VapeV7 ransomware (virus) - Recovery Instructions Included
VapeV7 virus Removal Guide
What is VapeV7 ransomware?
VapeV7 ransomware can encrypt all your personal files like photos, videos, and documents

A new type of malicious software named VapeV7, identified by ransomware researchers, has been found to be a file-locking malware. Once VapeV7 infiltrates a system, it initiates the encryption process, which appends the .VapeV7 extension to files upon completion. For example, a file named picture.jpg would become picture.jpg.VapeV7.
As a result, these files are rendered inaccessible and appear as blank pages without icons. Ransomware typically targets personal files such as photos, videos, and documents for encryption. Following the encryption of the files, the attackers generate a ransom note via a pop-up window to inform the victim of the situation.
| NAME | VapeV7 |
| TYPE | Ransomware, cryptovirus, data locking malware |
| DISTRIBUTION | Infected email attachments, torrent sites, malicious ads, drive-by downloads |
| FILE EXTENSION | .VapeV7 |
| RANSOM NOTE | Pop-up window |
| RANSOM AMOUNT | $200 in Bitcoins |
| FILE RECOVERY | It is almost impossible to recover the files if you do not have backups; in this guide, you will find third-party options for file recovery |
| MALWARE REMOVAL | Scan your machine with anti-malware software to eliminate the malicious files |
| SYSTEM FIX | Windows reinstallation can be avoided with FortectIntego maintenance tool, which can fix damaged files |
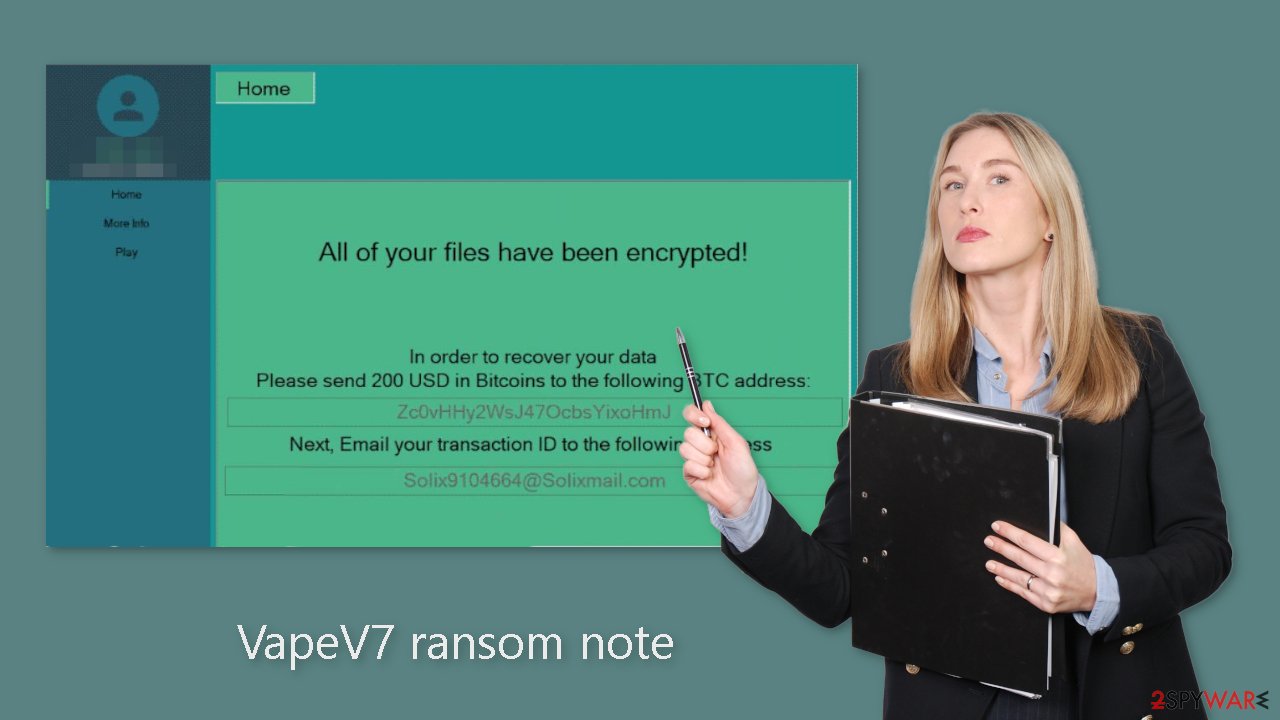
The ransom note
The ransom note in the pop-up windows reads as follows:
All of your files have been encrypted!
In order to recover your data
Please send 200 USD in Bitcoins to the following BTC address:
–Next, Email your transaction ID to the following address
–
The ransom note instructs the victim to send $200 in Bitcoin to a specific BTC address and email the transaction ID to a different address. Because Bitcoin, a cryptocurrency,[1] is difficult to trace, it is an appealing option for ransomware payments.
However, it is important to note that paying the ransom does not guarantee that the victim will regain access to their files. In fact, it is strongly discouraged to pay the ransom as it encourages cybercriminals to continue their illegal activities. Additionally, there is no guarantee that the criminals will decrypt the victim's files even after the payment has been made.
Distribution methods
While the exact method by which VapeV7 ransomware spreads on the internet is unknown, there are some general tactics that attackers employ when distributing malicious programs. Malware is frequently delivered via executable files (.exe), which can be hidden within a zip folder, disguised as a Microsoft Office document macro, or attached to another file.
Malicious files can also enter a system via “cracked” software[2] installations, which are frequently found on unregulated platforms that serve as breeding grounds for various types of malware. Unfortunately, even legitimate downloads may contain malicious files that are difficult to detect by the average user.
Another tactic used by cybercriminals to deliver ransomware is through email, where they embed malicious links or attachments. It is important to exercise caution and not open emails from unknown senders, and even if the email is from someone on your friend list, it is better to verify the attachment's authenticity with them through another platform.
Hackers may also use vulnerabilities in the operating system or software as a common distribution channel. Because software developers frequently release security updates to address newly discovered vulnerabilities, it is critical to keep all software and operating systems up to date. Failure to do so may expose you to ransomware attacks.
Ransomware removal with anti-malware tools
Disconnecting the machine from the network by unplugging the Ethernet cable is sufficient to isolate it from the workplace network if the device is located at home. This step is crucial if other devices share the same network since they may also be infected. After disconnecting, it is necessary to remove the malicious files that are running in the background. Trying to recover data before removing the malware may result in permanent data loss.
If the cause of the malware is not eliminated, the files may keep getting encrypted repeatedly. It is recommended not to attempt removing the malware unless you possess IT knowledge. The best approach is to use anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan the system thoroughly, ensuring the complete removal of all associated files and entries.
If you encounter difficulty opening the security software, the malware may be preventing it from functioning correctly. In such cases, accessing Safe Mode is advisable, where you can deploy the antivirus tool safely.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
File recovery using third-party software
Third-party programs cannot always decrypt the files, but you should at least try it. Before proceeding, you have to copy the corrupted files and place them in a USB flash drive or another storage. And remember – only do this if you have already removed VapeV7 ransomware.
It is devastating to know, but if you do not have backups, this might be your only chance at recovery because only hackers hold the decryption key, which can unlock your files.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![VapeV7 ransomware VapeV7 ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
The operating system can be damaged after an attack
Malware infections can cause a variety of issues that affect the performance, stability, and usability of a computer. These problems can progress to the point where a full Windows reinstall is the only option. Malware can alter the Windows registry database, corrupt or delete important DLL files, and do a variety of other things. Unfortunately, antivirus software cannot repair corrupted system files.
FortectIntego was created as a comprehensive maintenance tool to address these issues. It can repair a wide range of malware-related issues, including Blue Screen errors,[3] freezes, registry errors, and damaged DLLs. These problems can render a computer unusable, but Restoro can save you the trouble of reinstalling Windows.
It can identify and repair problems caused by malware infections by running a system scan. It can also improve system performance and stability. In many cases, it can restore a computer to its previous state, saving you the time and frustration of a full system reinstall. Restoro allows you to quickly and easily get your computer back up and running.
Additional resources
Additional instructions for corporate environments are provided at the bottom of this post, detailing how to isolate an infected machine and prevent the malicious program from spreading throughout the network. There is also information on where to report your attack. Reporting the attack increases the chances of apprehending those responsible.
Getting rid of VapeV7 virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Kate Ashford, John Schmidt. What Is Cryptocurrency?. Forbes. Investment Blog.
- ^ Georgina Torbet. 5 Security Reasons Not to Download Cracked Software. Makeuseof. Security Blog.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. Howtogeek. Technology Magazine.

















