Verify.safeadd.com scam (fake) - Free Guide
Verify.safeadd.com scam Removal Guide
What is Verify.safeadd.com scam?
Verify.safeadd.com uses scam techniques to trick users into downloading software

Verify.safeadd.com is an unauthorized website involved in a misleading scheme that presents fabricated virus infection notifications, ostensibly from reputable cybersecurity brands like McAfee. The site capitalizes on this contrived danger to persuade users to purchase its alleged antivirus software. It's imperative to understand that these virus infection notifications are wholly fictitious and only emulate the design of a genuine security scan.
Although the virus scans presented by Verify.safeadd.com are devoid of any real merit, one should not disregard the potential presence of adware on their system. Adware, which can often be the source of such counterfeit alerts, can expose your system to a myriad of cybersecurity vulnerabilities if left untreated.
In the following segments of this article, we will delve into the specifics of the Verify.safeadd.com deception and provide thorough guidance on identifying and eliminating potential adware from your device. Achieving a deep comprehension and vigilance regarding these matters is paramount in defending your online space against such predatory tactics.
| Name | Verify.safeadd.com |
| Type | Scam, phishing, redirect, fraud, fake alert |
| Scam content | Claims that the antivirus software license has expired and that the computer is exposed to various malware |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Loss of finances due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | You should not interact with any links or ads shown on the scam page and shut it down immediately. Then, perform a full scan with SpyHunter 5Combo Cleaner security software as a precautionary measure |
| Other tips | We recommend scanning the system with FortectIntego to clean browser caches and repair virus damage automatically after eliminating PUPs and malware |
Possible adware infection
Online fraud remains a pervasive threat in the digital realm, though its impact and frequency are often contingent upon users' online behaviors and choices. One such behavior that greatly increases the chances of encountering scam websites like Verify.safeadd.com is navigating to inherently high-risk domains. Torrent sites, known for hosting a plethora of files from various unverified sources, are hotbeds for these scams. Users seeking free or pirated content may inadvertently stumble upon links that redirect to malicious sites.
Similarly, compromised websites pose another significant risk. A legitimate site that has been hacked may have malicious scripts or redirects implanted by attackers. Unsuspecting visitors, believing they are on a trusted platform, can be stealthily rerouted to scam sites, becoming potential victims. The credibility of the original site often lends an air of legitimacy to these redirects, making the scam more convincing.
A second major avenue through which users find themselves on malicious sites is due to adware infections. Adware is a type of malicious software that inundates a user's device with unwanted ads. These ads are not just annoying; they are often designed to mislead. By clicking on them, users may be transported to a scam site like Verify.safeadd.com. Adware typically capitalizes on users' trust, displaying ads that seem relevant or enticing, only to redirect them to sites with malicious intent.
It's imperative to emphasize that once on a scam site, the best course of action is non-interaction. Engaging with such sites, whether by clicking links, downloading files, or providing personal information, can have detrimental effects on one's cybersecurity and personal data integrity.
In the upcoming section, we'll delve deeper into the nuances of recognizing phishing sites, equipping readers with the knowledge to stay safe and informed in an ever-evolving online landscape.
Fake messages are designed to exploit users' fears
Understanding the modus operandi of online scammers is crucial in defending oneself against their deceitful tactics. When users are redirected to sites like Verify.safeadd.com, they are often greeted with alarming messages meant to incite panic and prompt hurried action. For instance:
Scan results: 2023_TROJAN virus, password_SPY, AdSwitcher detected
- Trojan found on this PC will most likely copy and delete all data from hard drives.
- Spyware will attempt to collect logins, passwords, and banking details.
- Adware usually replaces search results with false and scammy websites.
It is highly recommended to use an antivirus immediately!
Such messages are meticulously crafted to appear authentic and urgent. Let's dissect the tactics employed and the red flags that users should be wary of:
- Specific naming and date stamping. Using terms like “2023_TROJAN” gives the illusion of a recent, thus more menacing, threat. This specificity can cause the user to believe it's a genuine, up-to-date virus detection.
- Dire consequences. The warning that a Trojan will “copy and delete all data” and that spyware will “collect logins, passwords, and banking details” is designed to invoke immediate fear. The stakes are set high to urge quick, often irrational, actions.
- AdSwitcher mention. By listing the consequences of each “threat,” scammers make it seem like they are providing helpful information. The mention of adware redirecting to “false and scammy websites” ironically plays on the user's fears of being scammed, while they are, in fact, on a scam site.
- Immediate action required. The closing line, recommending the use of an antivirus immediately, is a classic tactic. By pushing users to act swiftly, scammers hope to bypass their logical thinking processes, making them more susceptible to the scam.
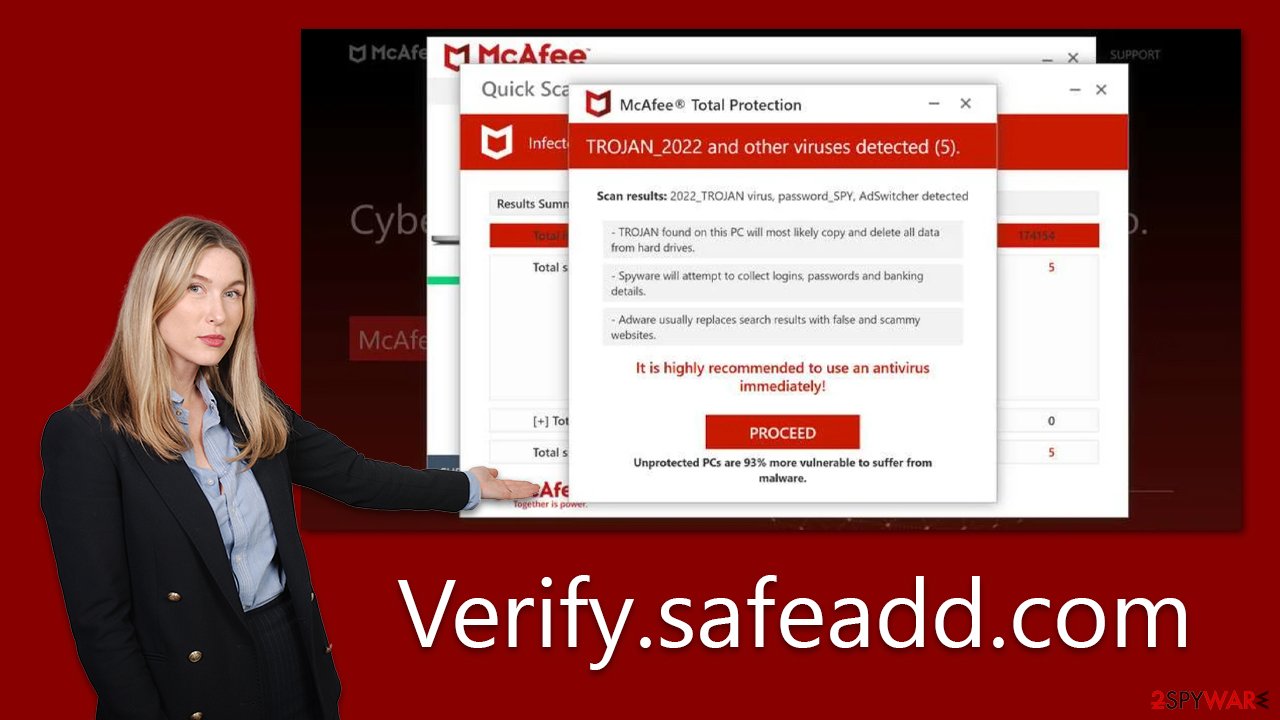
In essence, the design of these scam alerts leverages a mix of perceived authenticity, induced panic, and a push for hurried solutions. Recognizing these red flags and responding with caution is the first step in avoiding the pitfalls of such deceptive tactics.
Checking the system for infections
When confronted with sites like Verify.safeadd.com, it becomes crucial to scrutinize your system for genuine threats. The very presence of such a site could be an indication of underlying problems, such as an adware infection. In light of this, it's prudent to initiate a comprehensive system scan with credible security solutions like SpyHunter 5Combo Cleaner or Malwarebytes. Renowned for their efficacy, these tools are adept at detecting and neutralizing an array of threats, fortifying your device's defenses.
Following the neutralization of potential threats, it's a sound practice to employ tools like FortectIntego to purge your browser of residual cache. While residual data from scam sites might not pose an immediate threat, over time, this accumulated data could degrade system performance or even be leveraged by malevolent actors for further attacks. It not only expunges superfluous data but also rectifies any damage inflicted by malware. This dual action ensures both improved system efficiency and bolstered security. For those who prefer a hands-on approach, the subsequent section outlines steps to clear browser caches manually:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.




