Video-watch1.com ads (Free Guide)
Video-watch1.com ads Removal Guide
What is Video-watch1.com ads?
Video-watch1.com ads may bring you to malware-laden websites

Like many other users, you might have been puzzled as to why Video-watch1.com ads started to show on your desktop all of a sudden. You see these pop-ups because you gave the website permission to deliver push notifications to your device. It's understandable if you can't recall granting consent because deceptive phishing[1] messages are frequently used to persuade unwary users to do so.
Users frequently have no idea where the suspicious activity is coming from because they were tricked into authorizing push notifications from Video-watch1.com. But as a result, these pop-ups could start appearing at any time, even while users are browsing completely unrelated websites or aren't even actively using their browsers.
The worst aspect of this activity is that Video-watch1.com ads might be harmful; they frequently contain links to dangerous websites, display fake virus infection warnings, or contain similar phishing information. If you click on these links, you run the risk of installing malware on your computer, giving crooks access to your personal information or subscribing to pointless services that will cost you money.
| Name | Video-watch1.com |
| Type | Push notifications, ads, scam |
| Distribution | Redirects could be caused by adware, although clicks on booby-trapped links on other malicious websites could be the reason for unwanted redirects as well |
| Symptoms | You may start seeing intrusive pop-ups on your desktop – clicking these may lead to insecure or even malicious websites |
| Risks | If you click on links provided by the website, you might end up infecting your system with malware/PUPs, disclosing your personal information to cybercriminals, or losing money for useless services |
| Removal | You can stop intrusive push notifications by blocking the website's URL in browser settings. It is also important to check the system for adware or other infections |
| Other tips | If you do not clean your browser from cookies and other web data, you see the unwanted ads return or data continue being tracked. Stop it with FortectIntego |
Distribution methods
Users don't purposefully go to websites like Video-watch1.com; if the URL were entered in the address box, nothing would happen. Instead, users are redirected there from various other websites, making the work of scammers much easier.
The most frequent cause of a redirect is clicking on a malicious link elsewhere. Peer-to-peer[2] networks, for instance, are well known for using fraudulent “Download” buttons and fake links that ultimately direct visitors to potentially harmful websites. High-risk websites occasionally also use automatic scripts to reroute visitors without requiring them to take any action.
Due to the fact that these websites are frequently infected with malware and may link to other harmful websites, we advise avoiding them. We advise utilizing a trustworthy ad-blocking tool in conjunction with security software that makes use of a web defense function for improved defense against compromised websites.
It is also important to note that adware may also be one of the culprits for redirects to suspicious sites. This software is typically bundled with freeware[3] downloaded from various third-party websites, so many people are not even aware that their systems are infected. To avoid this, make sure you download software carefully and never rush through steps – always pick Advanced instead of Recommended settings and remove ticks from pre-selected checkboxes.
Push notification scams: how do they work?
Making money from ads is the primary objective of deceptive and fraudulent websites. Unfortunately, dishonest people frequently turn to dishonest ad networks, leading to incredibly poor ad quality. This is one of the reasons why customers who sign up for push alerts from Video-watch1.com start seeing links that are harmful or misleading.
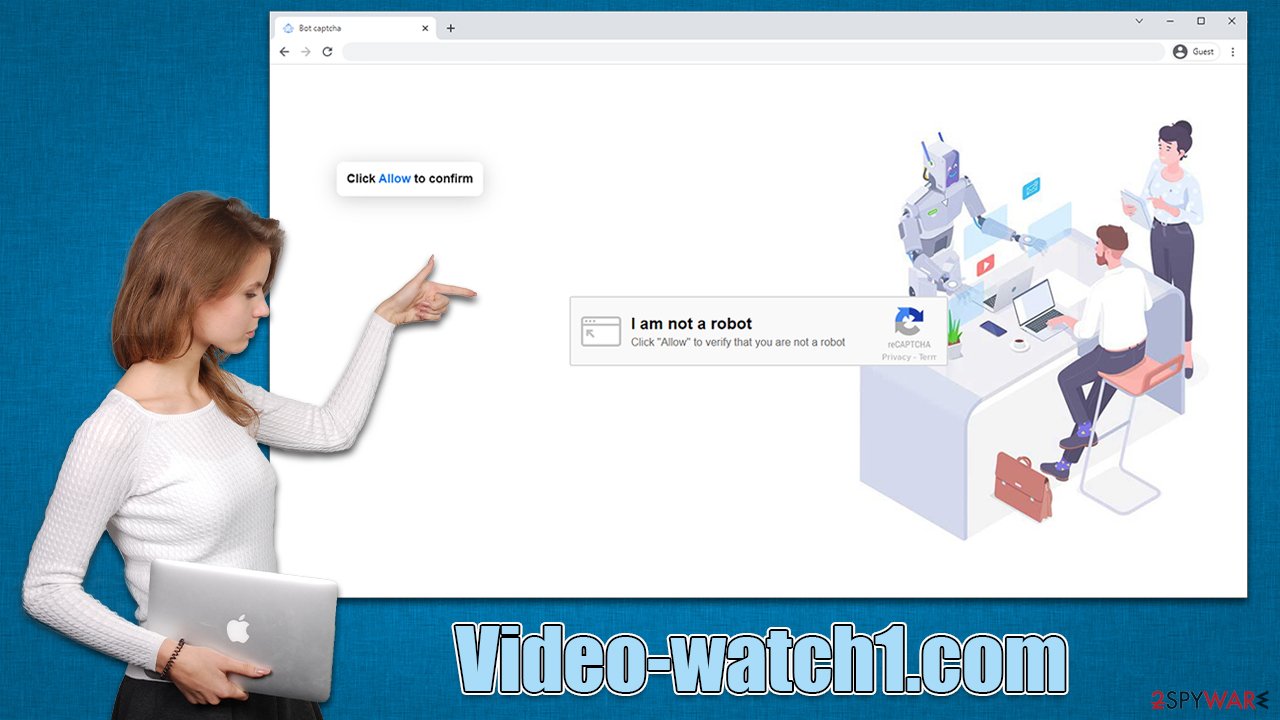
Scammers are encouraged to utilize these rogue ad networks since they pay well, thus, everyone benefits except the users themselves. Evidently, few individuals would willingly consent to have malicious ads delivered right to their screens. Therefore, scammers devise methods to make it happen. To be more specific, they are employing a few deceptive messages that should persuade individuals to enroll. Here are a few instances:
- Click Allow to start downloading
- If you are 18+, click Allow
- Click Allow to confirm that you are not a robot
- Click “Allow” to win the prize and get it in our shop!
- Press “Allow” to watch the video, etc.
All of these messages are made up and have no basis in reality. By displaying a push notification prompt along with the justification for pressing the “Allow” button, crooks are attempting to accustom users with familiar characteristics. Evidently, some people fall for tricks and just follow instructions without thinking, which is exactly when they permit undesirable activities to occur on their devices.
Removal of annoying push notifications and check for malware
Intrusive push notifications that originate from a scam scheme often confuse users about the source of the activity and what is causing it. Suspicious pop-ups frequently signify a virus infection, leading many people to believe their PCs are contaminated. They try to check their devices with security software to look for these infections, but they are unsuccessful. This is so that push notifications can only be manually disabled through browser settings.
But when dealing with suspicious activities, scanning the device is crucial because there can be an adware or other unwanted software running in the background without your permission. When downloading repacked software or viewing dangerous ads, malware may inadvertently download. You might not even be aware that your system is compromised because the entire process is quite cunning.
We advise scanning the system with robust security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, before moving further with the Video-watch1.com ads removal. Following that, you can use FortectIntego to delete browser caches, including cookies, and make sure that no data tracking is occurring.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ James Cope. What's a Peer-to-Peer (P2P) Network?. Computerworld. IT news, careers, business technology, reviews.
- ^ What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.






