Watchsophisticatedextremelytheproduct.vip ads (Free Instructions)
Watchsophisticatedextremelytheproduct.vip ads Removal Guide
What is Watchsophisticatedextremelytheproduct.vip ads?
Watchsophisticatedextremelytheproduct.vip ads attempt to make you install potentially unwanted programs
Watchsophisticatedextremelytheproduct.vip might seem like a weird name for a website, but its main purpose is to spread misleading messages so that users would download and install browser hijackers and other potentially unwanted apps. Those who agree and install the extension or program would soon notice that their browsers have either changed homepage/new tab settings or that they encounter various intrusive advertisements and phishing content more often.
If you have noticed that you are being redirected to Watchsophisticatedextremelytheproduct.vip or similar websites often, there is a high chance that your system is infected with adware. Adware does not only promote suspicious links and shows intrusive ads but may also record user information, resulting in privacy risks. We recommend checking the device thoroughly, regardless of whether you have installed the promoted extensions or not.
| Name | Watchsophisticatedextremelytheproduct.vip |
| Type | Redirect, scam, phishing, adware |
| Distribution | Bundled software, third-party websites, redirects |
| Symptoms | Shows fake ads and promotes potentially unwanted applications |
| Risks | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| Removal | Do not interact with scam content; if you did, uninstall the unwanted browser extension and check your system for other infections with SpyHunter 5Combo Cleaner anti-malware |
| Other steps | After PUP elimination, make sure you clean your browsers to prevent data tracking. FortectIntego can significantly quicken this process |
Don't get tricked by a scam
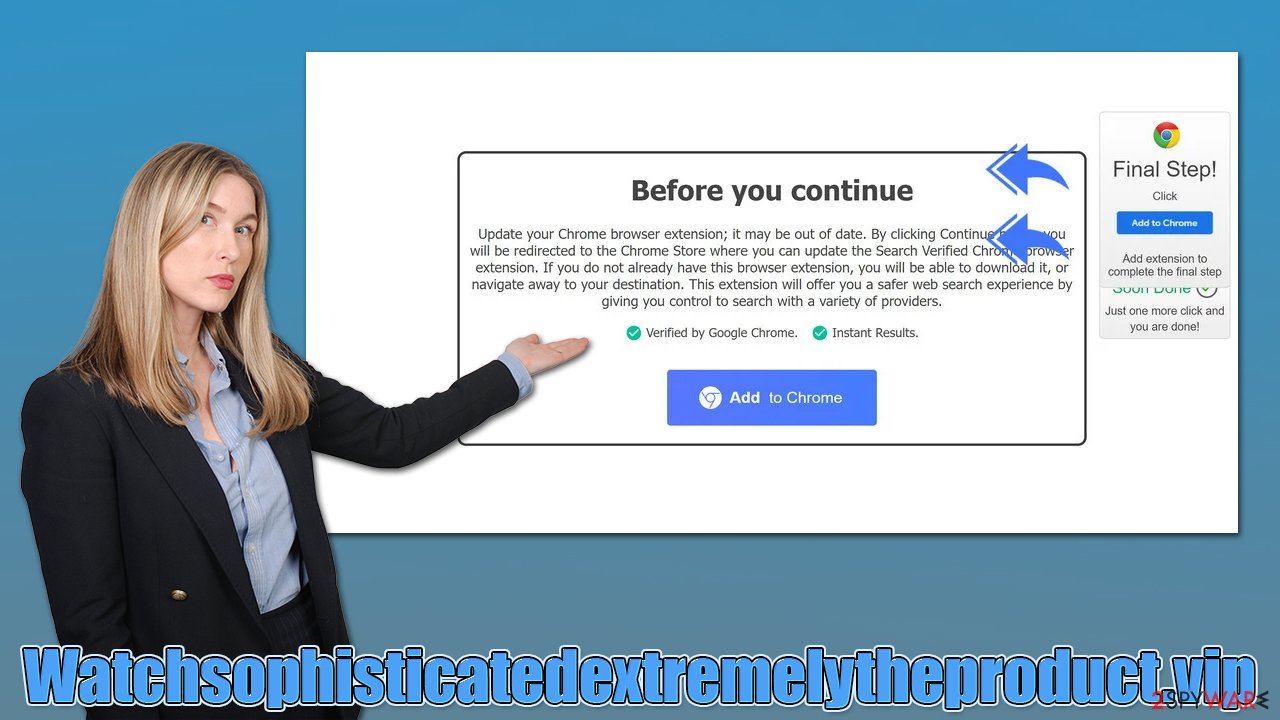
Watchsophisticatedextremelytheproduct.vip could host a variety of scam messages which are meant to convince users to download potentially unwanted software. It is overall advised not to download anything from websites that claim that something is missing or it needs to be installed in order to proceed. Flash Player – a plugin used for multimedia content for years – is now often being used by cybercriminals to spread malware, for example.
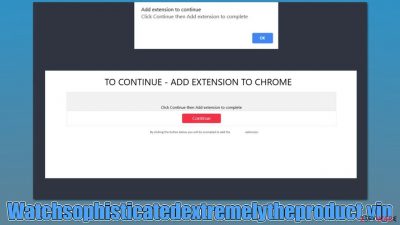
Here is one of the messages you might see once you enter the site:
Add extension to continue
Click Continue then Add extension to complete
According to this notification, users need to add the extension “to continue.” It is not explained where it leads to, or why do they need to install it. If you agree and click “Continue,” you might be redirected to a malicious site right after.
Also, other messages could be hosted on the site, so please do not interact with the content shown here – nothing good can come out of it. Instead, you should check your system for infections.
How does adware spread?
In most cases, users do not install adware intentionally but are rather tricked into doing so. Some people believe that the application they are about to install is useful in some way, as many PUPs boast their allegedly useful features.
For example, many fake ad-blockers can be found on scam sites – these would insert their own ads instead of blocking all of them, which completely negates the purpose of such an app. To avoid this, always pay close attention to the website which offers it to you, and especially how it is conveyed; as mentioned, if the message claims that something is missing or needs to be updated, disregard it immediately.
Another popular adware delivery method is software bundling.[1] It is usually applied by all third-party websites that distribute freeware and shareware. Always assume that the installer of the wanted application will offer you to install an additional app, and deceptive methods are used for that.
Thus, always make sure you select the Advanced or Custom installation method if prompted, read the fine print, untick the pre-ticked checkmarks, watch out for misplaced buttons and, most importantly, never rush through steps.
Uninstall suspicious programs from your system
Regardless of whether you downloaded something from Watchsophisticatedextremelytheproduct.vip or not, you should make some adware and malware checks.
Remove unwanted extensions
Browser extensions are the most common form of potentially unwanted software, such as adware or browser hijackers. They are easy to make and can be easily branded if such action is required. Therefore, we recommend accessing the browser settings and uninstalling everything suspicious as follows:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clean browser caches and scan for malware
If you haven't found anything in your device's extensions and applications section, we recommend you scan your system with security software SpyHunter 5Combo Cleaner or Malwarebytes. In fact, anti-malware can ensure that all the malicious components are removed all at once and that your device is safe again.
Additionally, take your time to clean your browsers, as if some components are not removed, it might result in privacy risks. For example, cookies[2] might be stolen by criminals in a so-called session hijacking[3] attack and personal accounts accessed. To avoid this, either rest your browser or remove caches, cookies, and other web data. You can use FortectIntego to make this process easier or refer to the following instructions:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Cookies and Web Beacons. NTT. NTT Communications.
- ^ Allie Johnson. Session hijacking: What is a session hijacking and how does it work?. Norton. Security research blog.








