WindowsEncapsulate Mac virus (Tutorial)
WindowsEncapsulate Mac virus Removal Guide
What is WindowsEncapsulate Mac virus?
WindowsEncapsulate is a malicious Mac application stemming from one of the more common Mac malware family

WindowsEncapsulate is a formidable variant of the well-known Adload malware, specifically targeting Mac systems. This pernicious virus is engineered to take control of web browsers, reroute users to harmful websites, and clandestinely extract sensitive personal information. Such information is often exploited for nefarious purposes, including sale on covert online marketplaces.
Due to its intricate design, the elimination of the virus presents significant challenges. The virus comprises multiple components and employs a variety of methods to avoid detection and removal. In cases where it is not thoroughly eliminated, WindowsEncapsulate has the potential to re-emerge, perpetuating its damaging influence and further compromising the integrity of the affected system.
For those seeking to defend their computer and secure their personal data, prompt and decisive action is essential in removing WindowsEncapsulate. Recognizing the complexity of this task, we offer comprehensive guidance to effectively address this threat.
| Name | WindowsEncapsulate |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Third-party websites distributing pirated software, software bundles, fake Flash Player updates |
| Symptoms | A new extension is installed on the browser, along with an application of the same name; search and browsing settings altered to an alternative search provider; new profiles and login items set up on the account; intrusive ads and redirects |
| Removal | Although not recommended to novice users, manual elimination of Mac malware is possible. We recommend performing a full system scan with SpyHunter 5Combo Cleaner and removing all the malicious components automatically |
| System optimization | After you terminate the infection with all its associated components, we recommend you also scan your device with FortectIntego to clean your browsers and other leftover files from the virus |
Malware spreading techniques
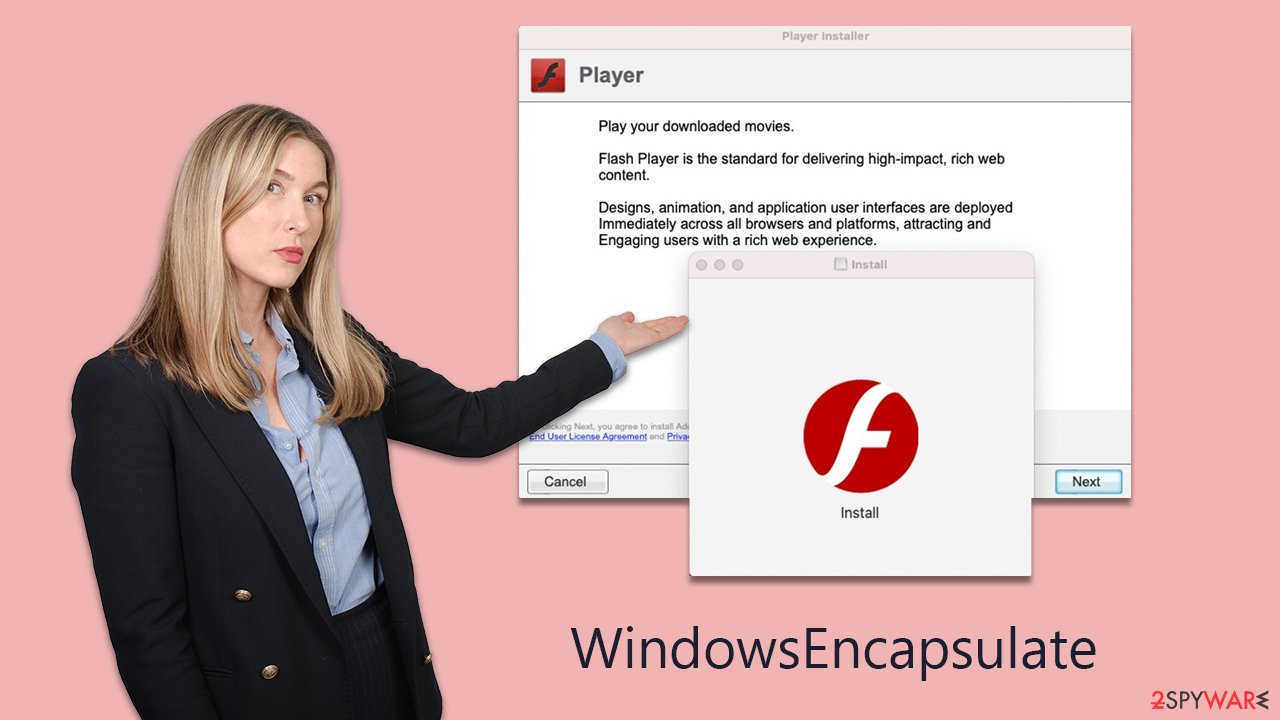
WindowsEncapsulate virus propagates through several deceptive methods, most notably fake Flash Player updates and downloads from unauthorized sources.
A primary tactic involves counterfeit Flash Player updates. Cybercriminals ingeniously craft websites that impersonate legitimate Adobe platforms, luring users into downloading what appears to be a necessary update. This deceptive download, however, is the virus itself, covertly installing WindowsEncapsulate onto the user's Mac.
The design of these fraudulent websites is meticulously crafted to mirror the authentic Adobe site, complete with convincing logos and graphics. These sites often employ alarmist tactics, warning users of potential security breaches or restricted access to content if the update is not installed. Tragically, many users are duped by these schemes, leading to the inadvertent installation of the virus.
Another prevalent method of distribution is through the downloading of software from non-official sources. Cybercriminals frequently distribute pirated versions of well-known software, including Adobe products, VPNs, and security applications. These pirated versions, touted as free alternatives, are, in reality, carriers of all kinds of malware.
Users drawn to these pirated versions often seek to avoid the costs or official acquisition channels for the software. Nonetheless, such practices expose them to significant security vulnerabilities. Alongside WindowsEncapsulate, they risk inadvertently introducing other malicious software, including trojans and spyware, onto their systems.
Adload family traits
Adload malware family, a notorious group of adware strains, increasingly targets Mac systems. Despite the common belief in the robust security of Macs, they are becoming more vulnerable to aggressive adware, partly due to their rising popularity. Notably, adware aimed at Macs often exhibits a more aggressive nature compared to its Windows-targeted counterparts.
WindowsEncapsulate belongs to this Adload family and is recognizable by its distinct icon, often featuring a magnifying glass on backgrounds of blue, teal, green, or gray. Upon installation, it alters browser settings in various ways, depending on the specific malware version. These alterations can include changing the homepage to unsecured sites, redirecting web traffic, substituting default search engines, and displaying intrusive advertisements in search results and other areas.
A characteristic feature of WindowsEncapsulate and similar Adload variants is their ability to circumvent Apple's security measures. They often leverage AppleScript for installing browser extensions with elevated privileges and for extracting sensitive data like credit card numbers and login credentials. This poses a serious threat to both user privacy and system security, emphasizing the need for immediate action to remove the infection and caution against entering personal information while the system is compromised.
Given the aggressive and evolving nature of the Adload malware family, including WindowsEncapsulate, Mac users should adopt proactive security practices. This includes using trusted antivirus solutions, exercising vigilance when downloading software or updates from unverified sources, and responding swiftly to any indicators of adware infection. Such measures are vital for maintaining the security and integrity of their Mac systems.
Elimination of malicious software
Removing standard applications from a Mac is usually a simple process, involving just dragging them to the Trash, leaving no residual files or issues. However, this ease does not apply to prominent malware, including an Adload variant. These infections are deliberately engineered to resist easy removal, as their prolonged presence on a device increases profitability for cybercriminals.
The urgency to eliminate WindowsEncapsulate stems from its potential for extensive damage and its pervasive nature. Traditional removal techniques might prove inadequate against such stubborn malware. For this reason, we strongly recommend the use of reliable security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, ensuring it is regularly updated. Conducting a comprehensive system scan with such software can efficiently identify and eradicate the WindowsEncapsulate infection.
For those who prefer manual removal, detailed instructions are provided. However, it is crucial to remember that, irrespective of the chosen method, clearing the caches of affected browsers, like Safari, is necessary to guarantee the thorough elimination of any malware traces. This step is vital for fully securing your system from the impacts of the infection, and FortectIntego can easily help you with this step.
Manual removal
Malware often operates through background processes, executing tasks as programmed by its creators. Thus, when dealing with malware, it's essential to first identify and terminate these background activities to prevent them from obstructing the removal process. On a Mac, this can be accomplished using the Activity Monitor. The steps to access Activity Monitor and halt these processes are as follows:
- Open the Applications folder and go to Utilities
- Double-click the Activity Monitor and shut down all the suspicious processes.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
![Uninstall from Mac 1 Uninstall from Mac 1]()
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
Your next task is to remove all the virus-related Login items and new Profiles that could be used by it.
- Go to Preferences and pick Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
Small configuration files known as PLIST can hold various settings information. They might prevent the virus from being removed properly.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Finally, you need not forget that the extension might still be present in the system, so you need to make sure to remove it. If you are unsuccessful while trying to eliminate it because it is grayed out, you can always resort to security software doing the deed, or you can also reset the browser. Check out the detailed instructions on how to do that below.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of WindowsEncapsulate Mac virus. Follow these steps
Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of WindowsEncapsulate Mac registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.












