Your personal files are encrypted virus (Removal Guide) - updated Nov 2019
Your personal files are encrypted virus Removal Guide
What is Your personal files are encrypted virus?
Your personal files are encrypted virus – a ransom-demanding virus that is identical to CTB-Locker malware
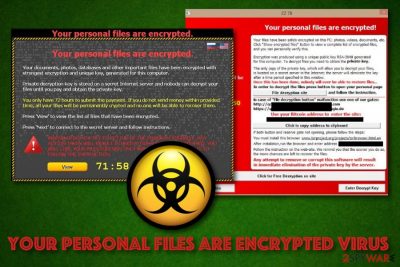
Your personal files are encrypted virus, also known as Your personal files are encrypted by CTB-Locker, is a ransom-demanding malware that locks photos, databases, and documents with the RSA-2048 algorithm,[1] adds the .ctbl appendix and requires a 3 BTC payment in exchange for data recovery. This ransomware is identical to CTB-Locker virus and targets a wide range of people, including users from the United States, Germany, France, and other countries. Your personal files are encrypted virus can appear on any type of Windows OS starting from the XP version and ending with the newest one. The malware brings DecryptAllFiles.txt, AllFilesAreLocked.bmp, and (multiple random letters).html ransom-demanding messages to the system and places a copy of each note to every folder that holds encrypted data.
| Name | Your personal files are encrypted virus |
|---|---|
| Type | Ransomware |
| Target | This malicious infection targets a big variety of countries worldwide, including the United States, France, Germany, and others |
| Identical to | CTB-Locker virus |
| Affected OS | This ransomware virus is able to infect various Windows computer systems such as Windows XP, Windows Vista, Windows 7, Windows 8, Windows 10 |
| Appendix | After the encryption process, the malware appends the .ctbl extension to each locked document, including photos, word documents, powerpoints, excel sheets, databases, etc. |
| Ransom note(s) | DecryptAllFiles.txt, AllFilesAreLocked.bmp, and (multiple random letters).html are the ransom-demanding messages that are provided by the ransomware virus |
| Elimination | Use only automatical software to complete the elimination process of the ransomware as manual step-by-step guidelines are not a solution here |
| Repairing | If the cyber threat has touched some system files of yours, you can try repairing them with FortectIntego |
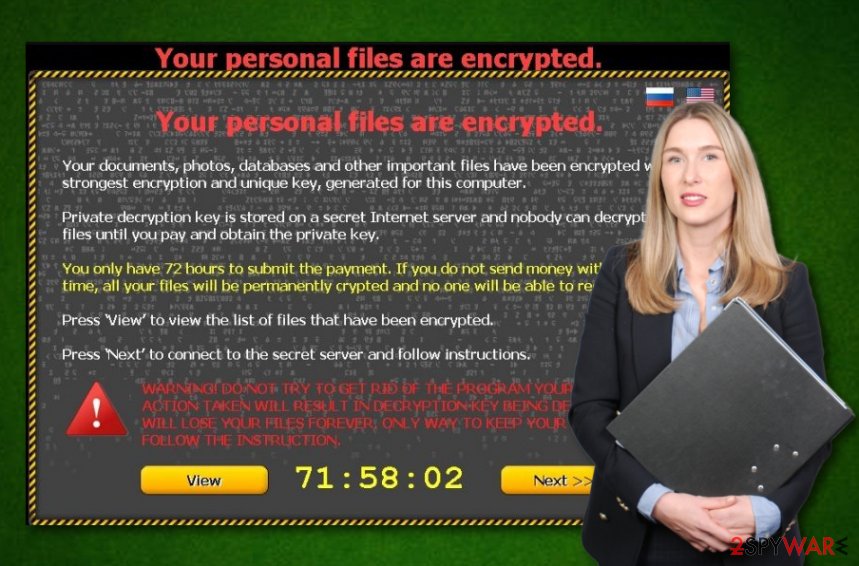
Your personal files are encrypted by ctb-locker developers urge for an inadequate ransom price (3 Bitcoins) that has to be paid within 96 hours by transferring money to the given Bitcoin wallet address. Continuously, if the victims want to decrypt their files with the received decryption tool they have to enter a specific URL via the Tor web browser:
Your documents, photos, databases and other important files have been encrypted with strongest encryption and unique key, generated for this computer. Private decryption key is stored on a secret Internet server and nobody can decrypt your files until you pay and obtain the private key. If you see the main locker window, follow the instructions on the locker. Otherwise, it's seems that you or your antivirus deleted the locker program. Now you have the last chance to decrypt your files.
1. Type the address hxxp://torproject.org in your Internet browser.
It opens the Tor site.2. Press 'Download Tor', then press 'DOWNLOAD Tor Browser Bundle',
install and run it.3. Now you have Tor Browser. In the Tor Browser open the hxxp://zaxseiufetlkwpeu.onion
Note that this server is available via Tor Browser only.
Retry in 1 hour if site is not reachable.4. Copy and paste the following public key in the input form on server. Avoid missprints.
436VPT-XI445Z-X4CFSL-MPOT6U-PQL2TK-74RNAQ-XYCCWO-ADYDL6
27UGA3-4YIAVP-IF3TTK-YGXGAI-3FATAX-SFK2XJ-VMELOS-YQNMI7
Q456FO-OVG476-FXKES2-TIAVXZ-ME2RLY-OWBKKV-L7EWNS-KYSWLB
5. Follow the instructions on the server.
Your personal files are encrypted virus also provides the users with the possibility to decrypt to small files for free as giving evidence of the decryption tool's existence. However, we recommend declining any offers to pay the demanded ransom price as you might easily get scammed by the hackers at the end and be left with an empty bank account and no decryption software in your hand.
If Your personal files are encrypted virus enters your Windows computer, it can easily encrypt each of these files: 3fr, accdb, ai, arw, bay, cdr, cer, cr2, crt, crw, dbf, dcr, der, dng, doc, docm, docx, dwg, dxf, dxg, eps, erf, indd, jpe, jpg, kdc, mdb, mdf, mef, mrw, nef, nrw, odb, odm, odp, ods, odt, orf, p12, p7b, p7c, pdd, pef, pem, pfx, ppt, pptm, pptx, psd, pst, ptx, r3d, raf, raw, rtf, rw2, rwl, srf, srw, wb2, wpd, wps, xlk, xls, xlsb, xlsm, xlsx, etc.
Afterward, both encryption and decryption keys are stored by Your personal files are encrypted virus developers on remote servers that are in reach only for the hackers themselves. This way the crooks try to decrease the chances for users of locking their files independently. However, you can try performing data recovery by yourself but you need to remove Your personal files are encrypted virus before that.
Your personal files are encrypted virus removal should be performed by employing reliable antimalware software that would be capable to deal with threats like this. Also, if the malware has corrupted some system files of yours, you can try repairing them with a program such as FortectIntego. Afterward, continue with the file restoring task. Even though no official decryption tool has been released yet, travel to the end of this article and take a look at all methods possible.
Your personal files are encrypted virus might be dangerous not only because of the encryption process that it performs but also because of the risk of additional malware infiltration. Ransomware infections are capable of bringing other cyber threats such as Trojan viruses, worms, cryptocurrency miners, and other dangerous malware to the system that can cause severe and unrepairable system damage.
In addition, Your personal files are encrypted virus might alter various entries in the Windows Registry or create malicious tasks and drop them in the Task Manager section. Keep in mind that each malicious component needs to be removed, otherwise, the dangerous infection might return easily.
Ransomware payload can get delivered in many ways
Experts from LosVirus.es[2] claim that ransomware developers think of various techniques on how to distribute the malicious payload. The most popular spreading locations of malware are:
- Software cracks. When malware camouflages as a program downloading link in unsecured networks such as The Pirate Bay, eMule, and similar p2p sites.[3]
- Email spam. Bad actors pretend to be from reliable organizations or companies and deliver malicious payload by presenting the clipped attachment as some type of “order shipment” information.
- Vulnerable RDP. Criminals target RDP configuration that holds weak security, for example, if it contains an easy-guessable password or no security code at all. The TCP port 3389 is known to be commonly targeted by hackers.
- Malicious updates. Sometimes crooks provide fake JavaScript or Adobe Flash Player updates as a way to infect users unknowingly. You might be flooded with urges to upgrade some of your software while browsing on unsafe networks.
The best way to protect yourself from possible ransomware attacks is to always pay attention while completing browsing and computing actions. First of all, make sure that all of your accounts and servers are secured with strong and reliable passwords. Continuously, always investigate your received emails (the sender, the content) and do not open any questionable-looking attachments without scanning them with antimalware software.
Furthermore, keep a fair distance from third-party downloading sources that produce cracked software. Do not click on any secondary downloading links or advertising content that is met on third-party websites. If you are ever provided with a dubious update, you should check the official developer's website and look for newly released upgrades. Last but not least, employ long-term antivirus protection that will announce about suspicious and malicious occurrences.
Remove “Your personal files are encrypted” virus
In order to remove Your personal files are encrypted virus that is providing you with inadequate ransom demands, you should use reputable antivirus software only as manual instructions are not the once you should rely on in this case. However, you can definitely use the below-provided guidelines on how to boot your computer system in Safe Mode with Networking or activate System restore to diminish malicious processes.
When you are ready for the Your personal files are encrypted virus removal process, you can also perform a full system checkup with a tool such as SpyHunter 5Combo Cleaner or Malwarebytes. Once you remove malicious files, check the system for virus damage as well. To repair altered system components, use FortectIntego. Once your computer is clean, go back to the part about ransomware prevention and memorize all avoiding steps once again.
Besides, do not forget to think about the file backup process in order not to get caught by malware such as Your personal files are encrypted ransomware the next time. You can use USB external hard drives, CDs, DVDs, Google Drive, Dropbox, Flickr, and other solutions. It is also recommended to make sure that all your open shares are available only for the necessary user groups or authenticated users.
Getting rid of Your personal files are encrypted virus. Follow these steps
Manual removal using Safe Mode
To diminish malicious changes on your Windows computer system and prevent them from continuing, you should boot your machine to Safe Mode with Networking
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Your personal files are encrypted using System Restore
To stop damaging processes from occurring newly and try reversing your Windows machine back to its previous position, opt for the System Restore feature
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Your personal files are encrypted. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Your personal files are encrypted from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Your personal files are encrypted, you can use several methods to restore them:
Employ Data Recovery Pro for file restoring tasks
Use this software if you are looking for a way to recover files and documents that have been touched by the ransomware virus
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Your personal files are encrypted ransomware;
- Restore them.
Windows Previous Versions feature might help you with data recovery goals
If you have booted your computer to System Restore recently, this method might appear helpful to you
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer for file recovery
If the ransomware virus did not touch Shadow Copies of encrypted data, you can try this technique. However, if the malware did affect these components, there might be various difficulties while using this tool
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor has been yet released
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Your personal files are encrypted and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ RSA (cryptosystem). Wikipedia. The free encyclopedia.
- ^ LosVirus.es. LosVirus.es. Security and spyware news.
- ^ P2P. Tech terms. Definitions.





















