Zrryzi.com (Virus Removal Instructions) - Free Guide
Zrryzi.com Removal Guide
What is Zrryzi.com?
Zrryzi.com is a potentially dangerous URL that promotes online scams
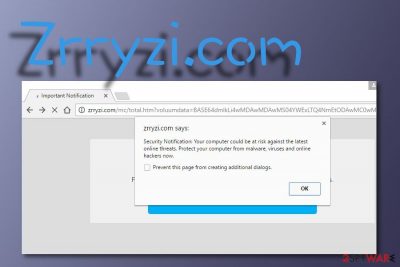
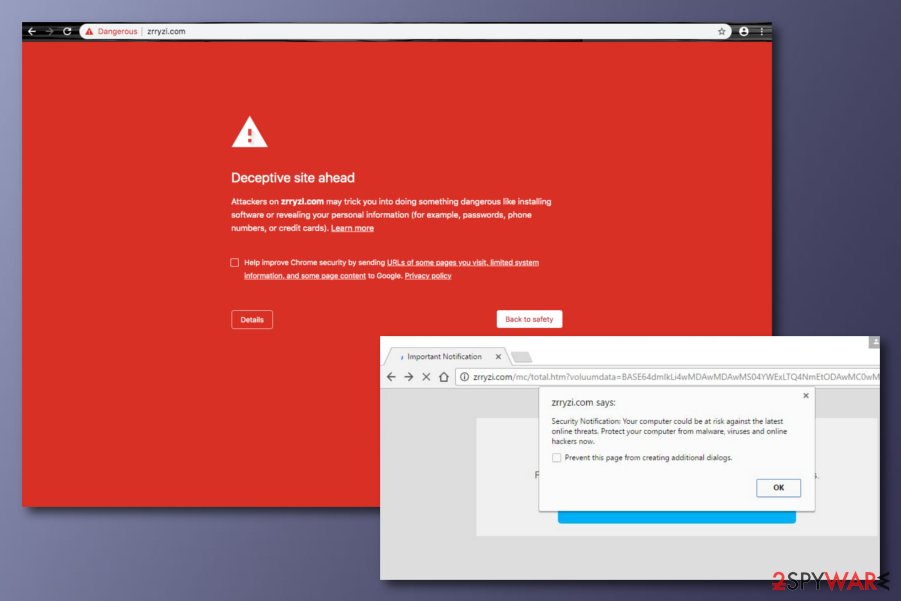
Zrryzi.com is a domain that drops a rogue notification claiming possible malware attacks. The suspicious pop-up urges users to protect their computers as they might be at risk of infection. We recommend not clicking anywhere on that message as you might get redirected to another website that promotes rogue security software and will try to sell the product for an inadequate price.
There is no substantial reason to believe these claims, as they come from a website that can not detect whether the level of your computer security is compromised. The authors' main goal is to collect as much income as possible, whether from the pay-per-click scheme[1] or forcibly taking you to affiliate domains and providing you with bogus offers.
| Name | Zrryzi.com |
|---|---|
| Type | Rogue website potentially related to adware |
| Activities | Redirects to suspicious websites and shows inadequate information to viewers |
| Main goal | The app aims to gather income from the pay-per-click scheme, redirecting the user to sponsored websites, and sharing non-personal data with other parties |
| Removal | You can get rid of the adware by using automatic software or by using the step-by-step guidelines that have been added to the end of this article |
| Fixing | If you have found some compromised components on your system, try repairing them with the help of FortectIntego |
While you may encounter this site by accident, it can also be a sign of an adware[2] infection if you keep experiencing redirects to this or another suspicious domain frequently. Regardless, this rogue domain tends to provide users with a suspicious Security Notification message about nonexistent threats. The note reads as follows:
Security Notification: Your computer could be at risk against the latest online threats.
Protect your computer from malware, viruses and online hackers now.
We recommend not paying attention to this message as it definitely is just a scam. It aims to threaten gullible users who do not know about the popularity of such scareware and fall for believing in these claims.
If Zrryzi.com asks you to subscribe to its page, you should not do that as you can easily end up installing suspicious programs on your system. The adware might infect web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, Safari and perform changes to their homepages or other settings.
Frequent redirecting is another feature related to adware and can easily interrupt your browsing sessions. It might start taking you to affiliate sources and promoting some type of third-party products or services. In some cases, you can even be sent to an infectious website and get attacked by malware.
Another unwanted activity is collection of non-personal information that relates to your browsing sessions, history, and habits. The developers can spy on data such as commonly visited websites, saved bookmarks, hyperlinks and adverts accessed, your IP address, geographic location, etc.
Later on, unknown parties might use the gathered data for involving you in targeted advertising campaigns or sharing the information with other parties for more income. Sometimes, the developers might get their hands on your email address. if this happens, be prepared to see the Spam section flooded with questionable deals and offers.
All this annoying activity will sooner or later affect your browsing quality and decrease the speed. For this not to happen or to prevent it from continuing, you have to remove Zrryzi.com from your web browser and get rid of all additional components such as extensions, plug-ins, and add-ons that the adware might have added.
The removal can be completed by employing reliable antimalware software or using the step-by-step guidelines that have been added to the end of this article. Besides, if the PUP has compromised some system objects on your machine, you can try repairing them by using system repair software such as FortectIntego.
Software bundling is the main way to distribute PUPs
Security experts from Virusai.lt[3] claim that adware programs come delivered by a deceptive marketing technique named “software bundling”. Bundling happens when the PUP is attached to an entire package of freeware and shareware. If the user has chosen the “Quick” mode as its installation settings, he/she has a big chance of receiving the adware.
Regarding this fact, you should choose only the “Advanced” configuration for completing your download and installations, otherwise, you might not be able to control all incoming downloads. Continuously, adware programs can get distributed via third-party advertisements and hyperlinks.
Due to such risk, we recommend keeping a fair distance from unknown websites and using antimalware protection that includes the safe browsing feature and will alert if something rogue or malicious is trying to get into the system while completing online sessions.
Zrryzi.com removal guidelines for all users
There are a few different ways you can approach PUP removal. The first method requires employing automatic software and leaving the entire work for the antimalware program. This technique is much easier and is suitable for even poorly-experienced users. The other method requires more of the user's involvement and is described at the bottom of this article.
If you want to remove Zrryzi.com by yourself, you can definitely do that, just measure your skills and capabilities first. Keep in mind that the adware might have added bogus products not only to your OS but also web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, and Safari that also need proper cleaning.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Zrryzi.com. Follow these steps
Uninstall from Windows
To delete bogus apps from Windows, use the following instructing steps.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
To eliminate suspicious components from Chrome, complete the following.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Zrryzi.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Pay-per-click. Wikipedia. The free encyclopedia.
- ^ Adware. Malwarebytes. Tech info.
- ^ Virusai.lt. Virusai. Spyware news.























