Newly designed ransomware starts spreading in Russian-speaking countries
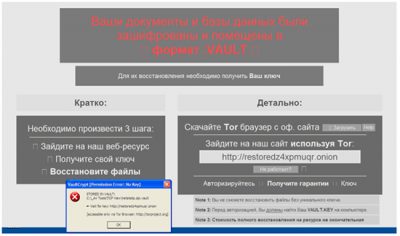
Normally, ransomware-type virus infiltrates computer, scans the system and then encrypts such files as documents, images and databases. For decrypting these files, victim has to enter a special key that can be received only by paying a ransom. However, several days ago researchers at Trend Micro have discovered a new type of crypto-ransomware, which is called CrypVault (see an image below).
This virus is clearly trying to reach new levels because it seems that it is trying to look like a legitimate antivirus software rather than a ransomware. Unfortunately, this is not the end. Another thing that you should remember about this threat is that it can also download info-stealer malware to your computer. Obviously, it can be used for stealing passwords and other personally identifiable information. How can you prevent this virus and what else should you keep in mind? Here is what you have to know about CrypVault virus:
Arrival:
It seems that CrypVault is spread just like other ransomwares – as a useful email attachment. Trying to be more precise we will say that security experts warn about a malicious Javascript file that is used to infect systems with additional malware. As soon as this Javascript file is downloaded, computer is infected with these files: the ransomware itself, SDelete (a tool that is capable of deleting files), GnuPG (encryption tool), and a GnuPG library file. These files are kept in the %User Temp% folder.
Functionality:
Differently from other ransomwares, CrypVault tries to create an image that it is a legitimate antivirus software that is quarantining victim’s files for trying to protect the system. However, it should be said that these files are encrypted, not quarantined. For that this ransomware is using the legitimate encryption tool called GnuPrivate Guard (also known as GnuPG) that adds a *.vault file extension to each of these doomed files. When trying to open any of affected files, a ransom note appears. Similarly to other ransomware threats, this virus is asking to pay a ransom of $500 or more. This should be done within a 72-hour period. That’s the amount of time that you can take if you don’t want to find your files destroyed. Here, we should warn you about one more thing – it seems that CrypVault is also capable of stealing passwords with a help of the Browser Password Dump tool that is downloaded to the system as soon as it infects it.
Prevention:
At the moment of writing it is known that this ransomware is mostly spread in Russian-speaking countries. However, there is no guarantee that hackers won’t start distributing this complicated threat in other world’s parts. For avoiding it, you should think about installing a reputable security solution on your computer.

