Advnotmoney.com ads (spam) - Free Instructions
Advnotmoney.com ads Removal Guide
What is Advnotmoney.com ads?
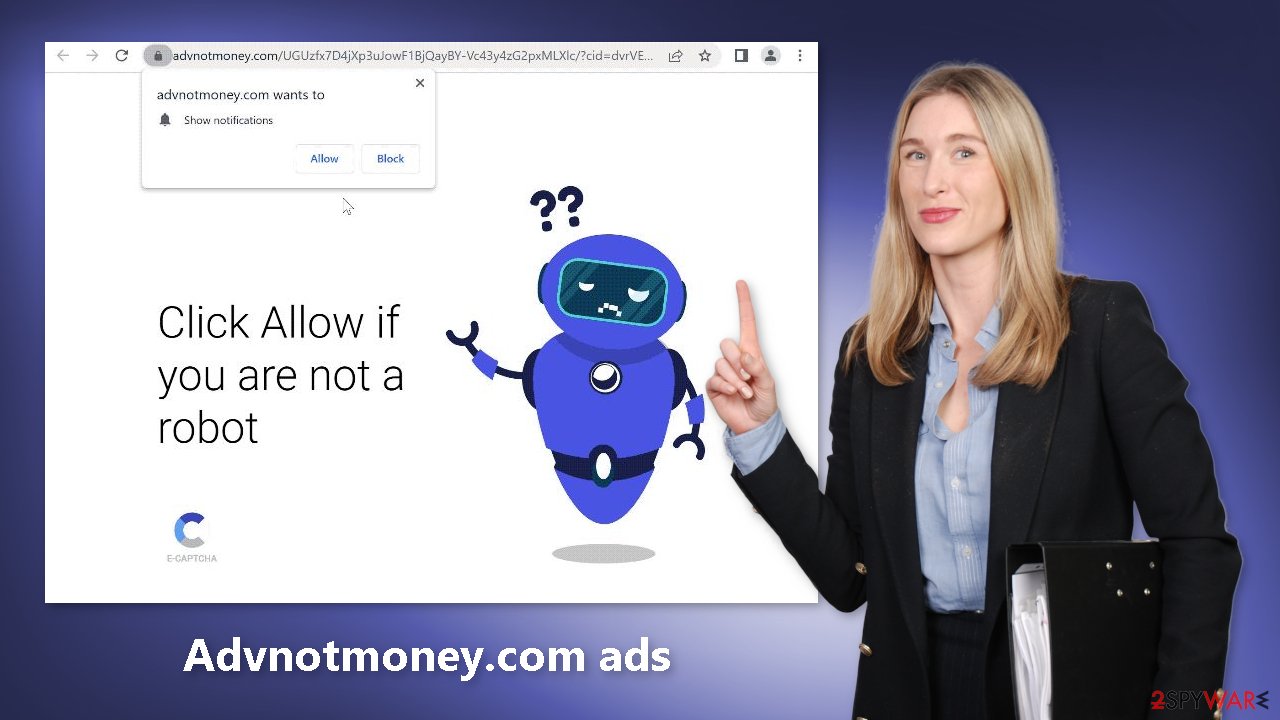
Advnotmoney.com causes pop-up ads that lead to harmful sites using social engineering

Scammers operate the website Advnotmoney.com. It uses social engineering[1] techniques to persuade people to subscribe to push notifications. To ensure that they are not robots, users are instructed to click the “Allow” button. However, as a result of this action, spam is generated.
Even if you close your web browser, those annoying pop-up ads can still appear on your screen. Unfortunately, scammers may employ rogue advertising networks to place advertisements that lead to dangerous websites. People may end up on pages that attempt to steal personal information and trick them into installing PUPs (potentially unwanted programs)[2] or even malware.
Users have reported seeing ads for adult websites, bogus antivirus offers, software deals, surveys, and freebies. As a result, it is critical to disable the advertisements as soon as possible, especially if other people are using the affected machine. All of the necessary instructions are provided below.
| NAME | Advnotmoney.com |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Pop-up ads start appearing in the corner of the screen sometimes even when the browser is closed |
| DISTRIBUTION | Shady websites; deceptive ads; bundled software |
| DANGERS | Links embedded in the pop-ups can lead to dangerous websites where people might get tricked into providing their personal information or downloading PUPs and malware |
| ELIMINATION | To disable push notifications go to your browser settings |
| FURTHER STEPS | Use FortectIntego to clear your browsers and fix performance issues |
Distribution methods
We previously discussed many other pop-up spam websites, such as Vantbox.com, Odestech.com, Link2captcha.top, and others. You're probably wondering where all of these push notification spam pages that seem to be popping up everywhere lately are coming from. They are usually concealed on other shady websites.
These websites are rife with shady ads and sneaky redirects. An example would be illegal streaming sites that display bogus “Download” and “Play” buttons that, in theory, should direct users to the desired content but instead redirect them to new pages that monetize user activity.
To avoid being taken advantage of, only visit websites that you are familiar with when browsing the internet. Do not click on links or advertisements from unknown sources because they could be bait used by crooks to trick you. To be safe, it is best to go straight to the source.
Block push notifications
Because push notifications are based on a subscription model, users need to disable them manually. If you do not know how, here are the instructions for Google Chrome, Mozilla Firefox, Safari, MS Edge:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
![Stop notifications on Chrome PC 1 Stop notifications on Chrome PC 1]()
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.
![Stop notifications on Mozilla Firefox 1 Stop notifications on Mozilla Firefox 1]()
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
![Stop notifications on Edge 2 Stop notifications on Edge 2]()
MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Cookies and cache
If you've noticed an increase in pop-up spam recently, it's probably because you visited some dubious websites that are still tracking your activity. Almost every website now requires visitors to accept cookies, so be cautious about which pages you visit in the future. Cookies save information like which websites you visit, which links you click on, your search history, and what you buy online.
Without your knowledge, this data may be sold to advertising networks or other third parties. To automatically clear your browser's cookies and cache, free up space on your device, repair corrupted files, and optimize performance, we recommend using a repair tool like FortectIntego.
Scan your system for adware
There may be a possibility that you are infected with adware[3] and that is why you are constantly bombarded with ads. Because there is no way of knowing which specific app is causing this annoying behavior, we always suggest our readers use professional security tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan their PCs.
Anti-malware tools can detect suspicious programs that are active in the background and eliminate them completely with all the related files. Manual removal may result in the renewal of infection as people often fail to eliminate all the related files and entries, however, if you still want to do this yourself, you can follow the guide below for Windows and Mac machines.
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Cynthia Gonzalez. Top 8 Social Engineering Techniques and How to Prevent Them [2022]. Exabeam. Information Security.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Adware. Malwarebytes. Cybersecurity Basics.













