Al-Namrood ransomware / virus (updated Apr 2017) - Virus Removal Instructions
Al-Namrood virus Removal Guide
What is Al-Namrood ransomware virus?
New versions of Al-Namrood virus strike victims in 2017
When Al-Namrood virus appeared on the Internet, few might have expected that it will remain long in the competitive race among ransomware creators. Hackers tend to name ransomware according to their interests, and this time they chose to denominate their virus using Saudi-Arabian black metal music band’s name[1]. There have been already several cases of similar file-encrypting viruses: Batman_good@aol.com, NoobCrypt, or Jigsaw ransomware. Speaking of Al-Namrood ransomware origins, it is believed to be developed by the same ransomware gang that created all Apocalypse ransomware variants. There are a couple of versions that were originated from Al-Namrood initial version, for example, Al-Namrood 2.0, also versions that hardly differ from each other but provide different contact details. For example, one ransomware suggested contacting criminals via Jabber XMPP messaging service – cryptservice@jabber.ua, decryptgroup@xmpp.jp also email addresses – decryptioncompany@inbox.ru, fabianwosar@inbox.ru, decryptgroup@india.com. Therefore, each new ransomware possesses more complex features making the threat more invincible. However, if this cyber menace has befallen you, no need to panic as you can remove Al-Namrood quickly. We recommend speeding up the procedure with FortectIntego. Before you run any malware removal programs, check out Al-Namrood removal instructions given below this post.
Following the tradition of typical file-encrypting malware, the current virus is suspected of using the same channels of distribution. Once it successfully infiltrates the device [2], it starts sneakily looking for a broad range of files. It tends to corrupt files with these file extensions:
1cd, dbf, dt, cf, cfu, mxl, epf, kdbx, erf, vrp, grs, geo, st, pff, mft, efd, 3dm, 3ds, rib, ma, sldasm, sldprt, max, blend, lwo, lws, m3d, mb, obj, x, x3d, movie.byu, c4d, fbx, dgn, dwg, 4db, 4dl, 4mp, abs, accdb, accdc, accde, accdr, accdt, accdw, accft, adn, a3d, adp, aft, ahd, alf, ask, awdb, azz, bdb, bib, bnd, bok, btr, bak, backup, cdb, ckp dsk, dsn, dta, dtsx, dxl, eco, ecx, edb, emd, eql, fcd, fdb, fic, fid, fil, fm5, fmp, fmp12, fmpsl, fol, fp3, fp4, fp5, fp7, fpt, fpt, fzb, fzv, gdb, gwi, hdb, his, ib.
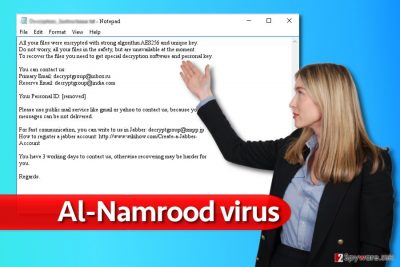
Therefore all your valuable documents, audio, video and image files are threatened by this virtual menace. With the help of traditionally employed AES encryption algorithm, the ransomware quietly encodes the files. As a result, you cannot access them, and you might spot that they bear one of the following extensions: .namrood, .access_denied, .unavailable, .disappeared. As usual in the ransom note, which can be dubbed Read_Me.txt or Decrypt_me.txt, cyber criminals instruct victims to pay the money in exchange of their locked data. However, we do not recommend paying any money to cyber criminals, at least not until you try Al-Namrood decryption tools created by malware analysts. Paying the ransom should be the very last option when dealing against ransomware attack, and only if losing the files lead to disastrous consequences at work or elsewhere. Remember that cybercriminals do not even have to provide you with the decryption software – it’s up to them, and the fact that you paid the ransom doesn’t really evoke sense of mercy for them.
Update December 2016: new version makes an appearance
Al-Namrood 2.0 ransomware virus struck the virtual world quite recently. It follows the manner of its predecessor to lock your personal data with AES-256 algorithm [3]. The essence of this encryption technique lies in running several cycles of block ciphers. Therefore, even a change of one number results in a completely different decryption key. Crooks take an advantage of this feature and threaten the victims to pay 10 BTC which equal to 6000 USD [4]. Such ridiculous demanded amount of money should ward off any considerations to transfer the money. The crooks indicate email – decryptgroup@xmpp.jp – for public communication purposes. However, it is futile to hope that you will return the files even if you dear to pay 10 bitcoints. Proceed to the elimination steps.
Update April 2017: Al-Namrood 2.0 virus uses different email, new attack vectors expected
Al-Namrood isn’t one of the most prominent viruses so far, however, it slowly evolves and every now an then we notice new versions of it. Recently, our experts spotted a ransomware that was dubbed Crypt32@mail.ru virus. Samples of this malware were spotted in April, and they were adding a long string to filenames of encrypted data. Here is an example of what the name of the encrypted file consists of [original_filename].ID-[8 random characters+victim’s country code[Crypt32@mail.ru].[14 random characters]. Apparently, the ransomware injects the contact email address in the new file extension and also corrupts the original filename. Just like the previous version, this one spreads via RDP attacks and spam. However, considering that ransomware distributors managed to hijack ad networks and push malware to victims via popular software such as Skype lately[5] (see – Skype virus), we strongly recommend users to be careful and not to click on suspicious ads that pop up in front of your eyes as you browse the Internet. Be extremely cautious and do not agree to install shady software updates, because that’s how ransomware distributors tricked dozens of victims into installing ransomware on their computers lately[6].
Ways of distribution
Al-Namrood malware follows the tradition of other notorious ransomware which confirmed their status in the cyber world, therefore it spreads using traditional techniques such as spam, malvertising, and others such as RDP attacks (it tends to target servers that have remote desktop services enabled). If you’re familiar with RDP services, make sure you use strong password for them, keep all your software up-to-date and ideally, create data backups every once in a while.
Speaking of spam, we must say that hackers might be using users‘ personal data acquired from fraudulent browser hijackers and adware to address victims directly. Clearly, spotting an email with your name mentioned in it instantly boosts up your curiosity. However, reviewing the infected attachment might open the Pandora box: you might accidentally activate not only Al-Namrood hijack but also allow various smaller viruses to enter the device. In this case, exercise caution and attention while surfing through your emails. You can always verify the sender on your own by calling the company that the email allegedly comes from, or look for information about the sender online using search engines.
How quickly can I get rid of Al-Namrood ransomware?
When it comes to this malware, we encourage victims to save time and shift to automatic Al-Namrood removal. You can perform it with the help of FortectIntego or Malwarebytes. Either one of another utility will help you battle the ransomware and completely eradicate it. Only when you remove Al-Namrood virus completely, you can think about the possible options of data recovery. In this regard, you can use our recommendations. Lastly, avoid using torrent sharing websites as they happen to be a frequent haven of file-encrypting malware. In addition, avoid opening the spam attachments if you are not sure if the email is fake or the real one. Reviewing new applications‘ reviews might come in handy before installing them as well.
Getting rid of Al-Namrood virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Al-Namrood using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Al-Namrood. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Al-Namrood from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Al-Namrood, you can use several methods to restore them:
The benefits of Data Recovery
You might use this tool to recover some of your files. It also comes in handy locating and repairing damaged files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Al-Namrood ransomware;
- Restore them.
How does Windows Previous Versions feature work?
This feature works only if System Restore is enabled [7]. After that, carefully go through each file and access the previous copy of your file.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Is Shadow Explorer an alternative?
It is not known whether the ransomware gets access to volume shadow copies. They are the copies of your files generated by the system. Therefore, the software helps to restore the files according to these patterns which were created by the operating system.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Use Al-Namrood decryption tool
Emsisoft researchers successfully cracked Al-Namrood ransomware and this decrypter helps to recover files locked by several Al-Namrood versions. You can find a guide on how to use it here.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Al-Namrood and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Al-Namrood. Wikipedia. The Free Encyclopedia.
- ^ Susmita Baral. How To Avoid Ransomware: Can It Infiltrate Your Life Outside Of Your Computer?. Ibtimes. International Business Times.
- ^ AES encryption. AES Encryption. Insights about encryption models.
- ^ What is Bitcoin?. CoinDesk.World leader in news about digital currencies.
- ^ Fake Flash Player ads on Skype push malware to users. eSolutions Blog. The Latest News about Computer Viruses.
- ^ David Bisson. Locky ransomware spreads through phony Flash update site. FightRansomware. Articles about Ransomware.
- ^ How to Use System Restore in Windows 7, 8, and 10. How-to-geek. A site for Geeks, Created by Geeks.





















