Back Orifice (Virus Removal Instructions) - Free Guide
Back Orifice Removal Guide
What is Back Orifice?
Back Orifice – remote administration software created by a member of Cult of the Dead Cow hacking organization
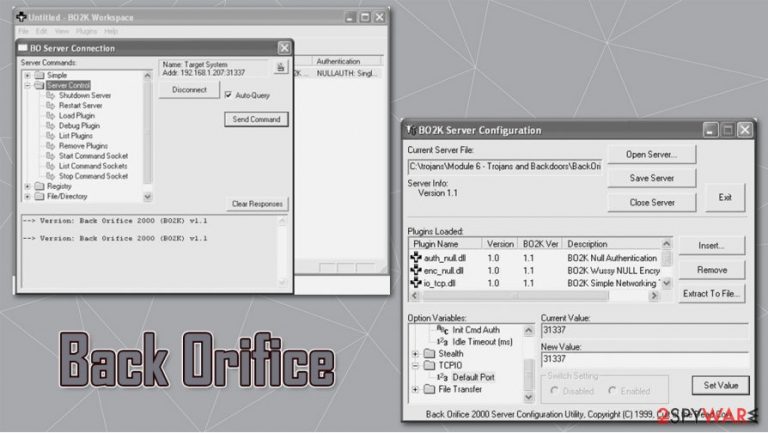
Back Orifice, later known as BackOrifice2K, is a remote administration application that was first introduced in 1998 by a hacking organization “Cult of the Dead Cow” member known as Sir Dystic. The developer named the software after Microsoft BlackOffice Server, which is meant to mock the tech giant and point out the flaws in then active MS Windows 9x operating systems. A year later, its next version was presented at the DEF CON 7 hacking convention in Las Vegas.
| Name | Back Orifice, BackOrifice2K |
| Type | Remote Administration Tool / Remote Access Trojan |
| Developer | Sir Dystic |
| Programming language | C++ |
| Infiltration | Insecure websites such as torrents, drive-by-download, malicious websites, fake updates, email spam, etc. |
| Capabilities | Since the RAT has backdoor and rootkit capacities, it would allow the attackers to take over the machine, send spam, proliferate other malware, steal sensitive information, etc. |
| Dangers | Personal data compromise, other malware infection, identity theft, monetary losses |
| Elimination | Download and install anti-malware software and perform a full system scan. Ensure that security tool is running the latest version. If needed, access Safe Mode with Networking to bypass persistence mechanisms – we explain how below |
| Further steps | To remediate your Windows machine after the infection is eliminated, we recommend using FortectIntego |
Written in C++ programming language,[1] its first versions emerged for Windows 95 and Windows 98, while the 2K version has expanded functionality and was also compatible with then-current versions of the OS – NT, Vista, and XP. Several different versions were released by the developers over the years, although each possesses a wide array of features we describe below.
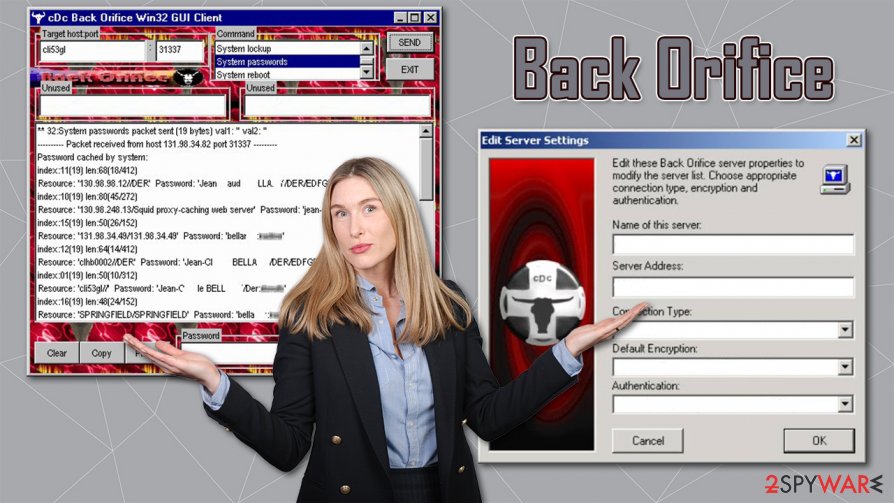
While initially Back Orifice can be used for remote administration legitimately, there has been plenty of abuse by cybercriminals. If installed without permission, it can serve as a Remote Access Trojan with backdoor and rootkit[2] capabilities. Malware would allow the attacker to take over the operating system with ease or monitor every action of the computer user.
Since the app would allow remote control, attackers could also use the infected computer as a bot[3] to spread spam or infect it with numerous other viruses, such as the treacherous ransomware. As a result, users could suffer from severe consequences, including monetary losses, credential leak, or even identity theft.
In other words, you should remove Back Orifice from your system as soon as possible if it arrived without permission, and security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, is preferred for it. Since malware has rootkit capabilities, it might be difficult to delete its remnants. Therefore, we recommend performing an additional scan with FortectIntego that could bring Windows back to a normal state after the elimination.
Back Orifice removal should not be delayed, although it is best not to get infected in the first place. Remember to stay away from high-risk websites, never open suspicious email attachments, patch all the software on the system on time, and ensure that a reputable anti-malware with real-time protection feature is running on the system at all times.
RAT capabilities
Back Orifice Remote Administration Tool is programmed to access computers remotely and then perform various diverse functions. To illustrate what abilities this application has, we will list some of its traits. Back Orifice Trojan can:
- Spawn a text-based application on a TCP port.
- Stop an application from listening for connections.
- List the applications currently listening for connections.
- Create a directory. Lists files and directory. You must specify a wildcard if you want more than one file to be listed. Removes a directory.
- Create an export on the server. Deletes an exports.
- List currently shared resources (name, drive, access, password).
- Log keystrokes on the server machine to a text file. Ends keyboard logging. To end keyboard logging from the text client, use “keylog stop.”
- Disconnect the server machine from a network resource. Connects the server machine to a network resource.
- View all network interfaces, domains, servers, and exports visible from the server machine.
- Ping the host machine.
- Return the machine name and the BO version number.
- Execute a Back Orifice plugin. Tell a specific plugin to shut down. List active plugins or the return value of a plugin that has existed.
- Redirect incoming TCP connections or UDP packets to another IP address. Stop a port redirection.
- Create a key in the registry. Delete a key from the registry. Delete a value from the registry, etc.
Back Orifice elimination steps
According to security experts,[2] it's not possible to know when Back Orifice virus attack is taking place, so it's very important to ensure a full system protection. Typically, cyber criminals who monitor this infection is spread via spam e-mails. Once a computer user clicks on the attachment, the virus is executed and roots deep into the system. Consequently, the machine can start working abnormally because hacked may start viewing and modifying the files and registries on your computer.
The Trojan can log your keystrokes, log files, take screen shots and send them to hackers or can simply crash the computer, so Back Orifice removal should not be delayed. It goes without saying that such a malicious application cannot be removed manually. Thus, if you suspect it to be hiding in your computer, our recommendation would be to check the system with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security software. After that,
Getting rid of Back Orifice. Follow these steps
Manual removal using Safe Mode
If the RAT on the system is too persistent, you can access Safe Mode with Networking to temporary disable its functionality:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Back Orifice and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting remote administration tools
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Programming language. Wikipedia. The free encyclopedia.
- ^ What is a Rootkit? How Can You Detect it?. Varonis. Security research.
- ^ What Is a Spam Bot? | How Spam Comments and Spam Messages Spread. Cloudflare. Online solutions.
