Bluecodemc1.club ads (fake)
Bluecodemc1.club ads Removal Guide
What is Bluecodemc1.club ads?
Bluecodemc1.club is a fake website designed to make people download potentially dangerous software
Bluecodemc1.club is a website created with malicious intent by scammers. Usually, people encounter it accidentally when browsing the web – clicking links on high-risk websites is likely to cause redirects to it. In alternative scenarios, encounters with phishing websites are attributed to adware or malware infections.
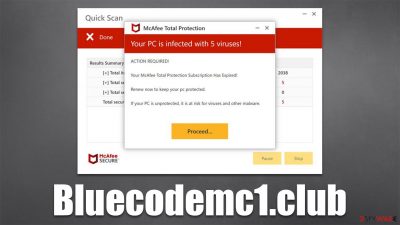
Upon entry, users might be misled to believe that McAfee – a popular antivirus maker, owns the website. However, Bluecodemc1.club has nothing to do with any legitimate company and is made to frighten people and make them believe that their systems are in danger. To be more precise, they are told that their machines have been infected with viruses, and the only way to remediate the situation is to download an alleged removal tool.
Do not interact with the scam, or you might lose money for fake deals or even install malware on your device inadvertently. While the claims of this scam page are fake, you should still check your system for infections and remove them as required. We explain the whole process below.
| Name | Bluecodemc1.club |
|---|---|
| Type | Scam, phishing, redirect, adware |
| Operation | Uses deceptive, misleading messages to make people install potentially unwanted or even malicious programs/extensions |
| Distribution | Redirects from other websites, adware |
| Symptoms | Redirects to suspicious websites that accommodate commercial or scam content; fake messages that offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Ads and links to sites displayed by the website might be dangerous: users might suffer from monetary losses, install malware or potentially unwanted programs on their systems, or disclose their sensitive data to cybercrooks |
| removal | Interacting with the scam might result in malware or PUP infection and pose privacy risks. Don't forget to check your system with reputable anti-malware |
| tips | After removal of unwanted software, make sure you clean your browsers from cookies and other trackers with FortectIntego |
More about Bluecodemc1.club
Browser-based scams are relatively common, and Bluecodemc1.club is not a unique site. Scammers usually rely on people's fear and lack of knowledge about the scheme – imitating legitimate security vendors has been done numerous times. For example, just recently, we covered Window-safe.com, Totaldatasecurityservice.com, and Defender-scan.xyz, which use precisely the same principle.
Upon website entry, users are typically shown what seems to be a virus scan by a reputable security vendor, for example, McAfee. After a short while, people are presented with alleged results, which claim that the system has been infected with multiple viruses and that the security software needs to be installed, updated, or subscribed to in order to remediate the situation. There are a few message variations, but here's one of the examples:
McAfee
Your PC is infected with 5 viruses!
ACTION REQUIRED!
Your Norton Subscription Has Expired!
Renew now to keep your pc protected.
If your PC is unprotected, it is at risk for viruses and other malware.
It is important to know that websites are not capable of detecting malware on your system – only an installed application can do that. Therefore, if, while browsing the web, you suddenly encounter a message which claims that your system is infected, you should disregard these claims completely, as they are fake.

What to do now?
After you encounter a scam site, it is very important to act correctly. The best-case scenario would be to shut down the Bluecodemc1.club tab immediately, without interacting with anything. Downloading software from this website might lead you to install potentially unwanted programs that would show you fake warnings, for example. Remember – everything that is advertised in a deceptive or misleading manner should be always ignored.
If you indeed have downloaded software, you should uninstall it as soon as possible – we provide all the necessary details for the process in the next section of the article. If you have disclosed your personal information, such as email, phone number, etc., expect to be targeted by scammers in the future, so be very wary.
In case you have provided a password you use somewhere else, immediately change it. Note that you shouldn't be reusing passwords in the first place, as it is a major security and privacy threat.[1]
If you are wondering if your personal or computer safety is in danger just because you have accessed the site – it is unlikely to be the case. The only way malware could get into your system is if it would host a particular exploit[2] that would correlate with vulnerable software installed on your device. To avoid this scenario, you should always ensure that all the programs on the system have all the security updates installed.
Check the device for infections
Checking the system for infections is vital regardless of whether or not you downloaded any programs from a phishing[3] site. Adware could be rather stealthy, so you might not even know it is running in the background. Malware, for example, might not have any active windows and could be invisible to regular computer users. To eliminate all the most dangerous threats, we recommend scanning the system with SpyHunter 5Combo Cleaner or Malwarebytes security software. Next, you should check the installed extensions on your browser:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
There is a chance that adware is installed on the system level, hence the unwanted activities won't go away unless it's removed. You can reach the Control Panel in Windows or Applications on Macs as follows:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Finally, you should clean your browsers from cookies and other trackers, or various third parties might continue tracking your visited websites, clicked links, timestamps, and a lot of other data. Cookies, for example, might remain in the affected system for years unless they are removed. Also, some ads may return if leftover files are not deleted after PUP removal. The easiest way to do this is by performing a scan with the FortectIntego utility, although the manual method can be used as follows:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Amer Owaida. People know reusing passwords is risky – then do it anyway. WeLiveSecurity. ESET blog.
- ^ Exploit kit. Wikipedia. The free encyclopedia.
- ^ Phishing attacks. Imperva. Application and data protection.











