BugWare ransomware / virus (Virus Removal Guide) - Removal Guide
BugWare virus Removal Guide
What is BugWare ransomware virus?
BugWare ransom-demanding virus keeps evolving
BugWare virus functions as a new file-encrypting threat targeting Portuguese[1] or Spanish speakers as the ransom note is written in the Portuguese and is believed to have originated from Brazil[2]. The malicious software commonly provides slavic@secmail.pro email address in its ransom notes as well as in file extensions it appends to encrypted files. Typically, encrypted files get marked with an additional .[email] + .Bugware or .Criptografado file extension.
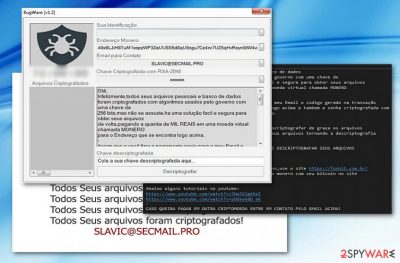
Besides the main ransom picture which includes the logo of the virus and the same line “Todos Seus arquivos foram criptografados!” in a text block, it also opens its GUI called BugWare [v1.2] which includes victims’ ID, the email address – slavic@secmail.pro – Bitcoin address, and the ransom text.
The latter prefers the ransom in Monero, though another cryptocurrency is also accepted. Following the manner of older crypto-malware, it gives victims 72 hours for the payment.
What is more, it also includes a couple of links to the Brazilian page about bitcoins. There are also Youtube page links, but at the moment, they do not function. The perpetrators urge victims to pay the ransom as their data is encrypted with RSA-2048 cipher.
Currently, the threat is detectable as Generic.Ransom.CloudSword.5DE49FDD or Generic.Ransom.CloudSword.5DE49FDD, though some anti-virus tools identify it as a sample of HiddenTear. Interestingly, the malware travels via doc_2017100200000-15.pdf.exe file. Therefore, you should be wary that Bugware virus spreads via spam emails.
The perpetrators attempt to deceive users with fake invoices in .doc or .pdf. If this misfortune has already settled on the computer and converted your records into useless .Bugware file extension files, then, make a haste to remove Bugware virus. FortectIntego or Malwarebytes helps you in this process. 
Versions of BugWare virus
.Criptografado file extension virus. Criptografado ransomware emerged on October 12 and quickly proved to be an updated version of BugWare virus. The new version has a slightly improved user interface, although it still provides the same email address for the victims – slavic@secmail.pro. While the previous version asked the payment in Monero currency, Criptografado virus asks for bitcoins.
What is interesting about the new variant is that it added exceptions for several countries including the following: Argentina, Bolivia, Brazil, Chile, Columbia, Ecuador, Guyana, French Guiana, Paraguay, Peru, Suriname, Uruguay, Venezuela, Portugal, Guinea-Bissau, Angola, Cape Verde, Mozambique, Timor-Leste, São Tomé and Príncipe, and finally Equatorial Guinea. Based on the victim's IP address, the Criptografado malware decides whether to encrypt data on the computer or not.
Experts say that currently files locked by this variant cannot be decrypted, so all that is left to do is to remove Criptografado file extension virus using proper malware removal tools.
Ways the virus reaches victims' computers
Regarding the fact that the malware functions via the executable file which disguises as .pdf or .doc file, most likely, BugWare malware developers engage in spam campaigns. They might pretend to be the representatives of a national tax company or post office.
Recently, cyber villains have developed technique how to foist ransomware by breaking into users’ ongoing email conversations. Therefore, double-check the identity of a sender before opening email attachments.
Lastly, beware that ransomware threats also spread via trojans or with the assistance of exploit kits[3]. In order to limit the risk of encountering the malware, install security tools and update them. Below you will find advice how to complete BugWare removal.
Remove BugWare ransomware now
In order to get rid of this threat, you will need the assistance of malware elimination tool. Since the virus may meddle with the system files, you may not be able to launch the program at the first attempt.
In case you encounter BugWare removal difficulties, restart the system in Safe Mode. Then, you should be able to launch the program and eliminate the virus from Windows operating system. Note that the elimination does not recover the data. You may find a few suggestions below to restore your data. This procedure should be done only when you remove BugWare virus completely.
Getting rid of BugWare virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove BugWare using System Restore
In case you find trouble launching Safe Mode, you might perform System Restore. It reverts the system to a last automatically saved restore point. In other words, this procedure should grant you access to a security tool to terminate BugWare threat.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of BugWare. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove BugWare from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by BugWare, you can use several methods to restore them:
Data Recovery Pro method
This program is created to assist people restoring damaged files. If you failed to backup your files in advance, this program might grant you a solution.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by BugWare ransomware;
- Restore them.
The benefits of ShadowExplorer
There is no information whether BugWare virus deletes shadow copies in advance. This program uses them to create the copies of your original files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from BugWare and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Get rid of computer threats. Semvirus. IT News and Malware Removal Guides in Portuguese.
- ^ MalwareHunterTeam. A Brazilian ransomware: BugWare. Sample. Twitter. Source for News and Communication.
- ^ Ajay Kumar. The change in hacker tactics – and security technologies to thwart them. CSO. Security news, features and analysis.





















