Dropbox virus. Scams/trojans/ransomware
Dropbox virus Removal Guide
What is Dropbox virus?
Dropbox virus – a series of different malware forms that occur while using the Dropbox application
Dropbox virus is a collection of various threats and dangerous infections that appear on Dropbox. Such threat series mostly cover different types of malicious threats that are distributed via email spam. Talking about the application itself, Dropbox provides file hosting features and has been founded by Dropbox Inc., in The United States, in 2007. Dropbox.exe is the executable which is responsible for the operating of this app, however, some users have reported that Malwarebytes detected this process as malware.[1] The reason for this might be some struggles in the software or maybe malware has been truly injected into this service.
| Name | Dropbox virus |
|---|---|
| Types | Scams, trojans, cryptoviruses |
| About Dropbox | Relates to dropbox.exe, founded in 2007, in the USA by Dropbox Inc. |
| Malware names | UPATRE, Trickbot, and other dangerous threats might be hiding behind the name of Dropbox app |
| Danger levels | Medium or high. Depends on the virus's operating principle |
| Distribution techniques | Email spam mostly |
| Detection purposes | Use FortectIntego to spot any possible malware traces in your operating system |
| Prevention | Install reputable antimalware for computer check-ups, manage all of your emails |
| Removal process | Get a reliable tool for virus elimination |
Due to the increasing popularity of Dropbox, Dropbox virus or Dropbox malware has become a popular term nowadays as more and more bad actors have been discovering ways to misuse the service for their own needs (distributing malicious software). Reports from users about malware detected in this app and questions about possible infections do not look like coming to an end.[2]
Someone wrote directly to Dropboxforum.com that he made a full system check-up and the antivirus software detected malicious components in the Dropbox application. The discovered content was Gen:Variant.Kazy 512414 and ~834b6cda.tmp and was found in the \.dropbox.cache directory.[3]
Due to the high level of infections and distribution of Dropbox virus, the company itself has provided useless information on avoiding malicious components from accessing their services and infiltrating the application. The organization offers to complete such simple steps for ensuring safety:[4]
Running anti-virus software
Exercising due caution when running unknown files from other computers
Furthermore, if you have been attacked by some type of malware related to this popular service, you should take quick actions to remove Dropbox virus from your computer system in order to prevent possible. That should be done by using reputable anti-malware software that is created for such advanced removal activities.
Additionally, before completing the Dropbox virus removal, you should download and install a tool such as FortectIntego or Malwarebytes and try detecting malicious software. When you find all infected locations and malware-laden objects, you will be able to get rid of them much easier and ensure that the entire system has been cured of the infection.
Different types of cyber threats that relate to Dropbox
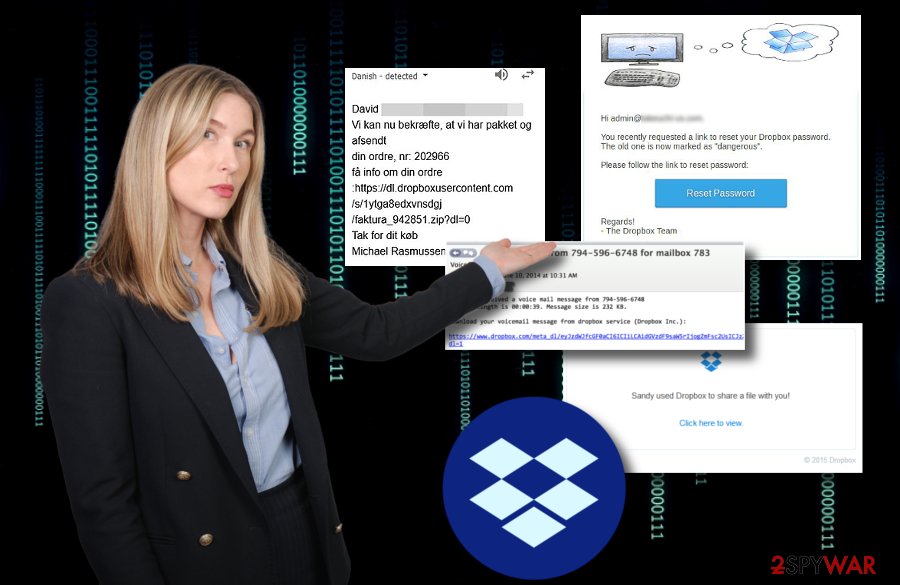
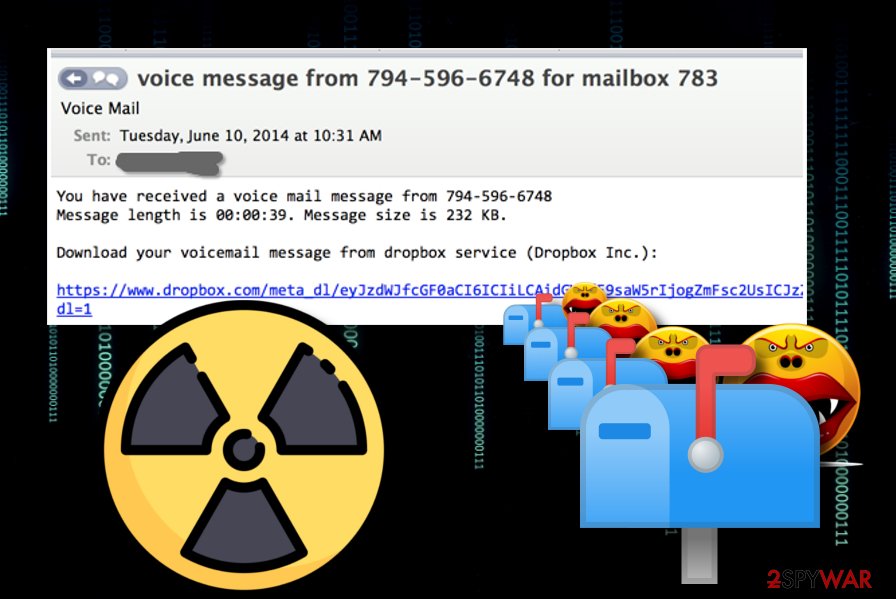
Cryptovirus delivered via fake Dropbox email message
It is known that ransomware infections are commonly spread via email spam pretending to come from well-known organizations. This time criminals decided to send Dropbox users and imitation of a voice mail message which includes a hyperlink (“provided by Dropbox Inc.) that truly is the malicious payload. DO NOT click on such content as it might relate in dangerous cryptovirus installation and encryption of your personal files.[5]
If ransomware catches your Dropbox files
Due to the increasing growth of ransomware-related cybercrimes, it is very important to know how to protect your files and documents on various platforms. Dropbox might also be a target by ransomware viruses and some files from this service might also be touched by the infection. Due to this reason, you should read the Intego helping guide on how to restore an individual Dropbox file.[6]
UPATRE malware spread through false Dropbox messages
Incoming Fax report email from Dropbox tricks users into installing UPATRE. Hackers insert a specific fax note in a link that users are provoked to click on. If you do that, you will start the download process of infectious .ZIP and .EXE files which are detected as the source of UPATRE malware that comes from the ZEUS family. Be aware of these malicious files as you might end up with a notorious virus on your computer system.[7]
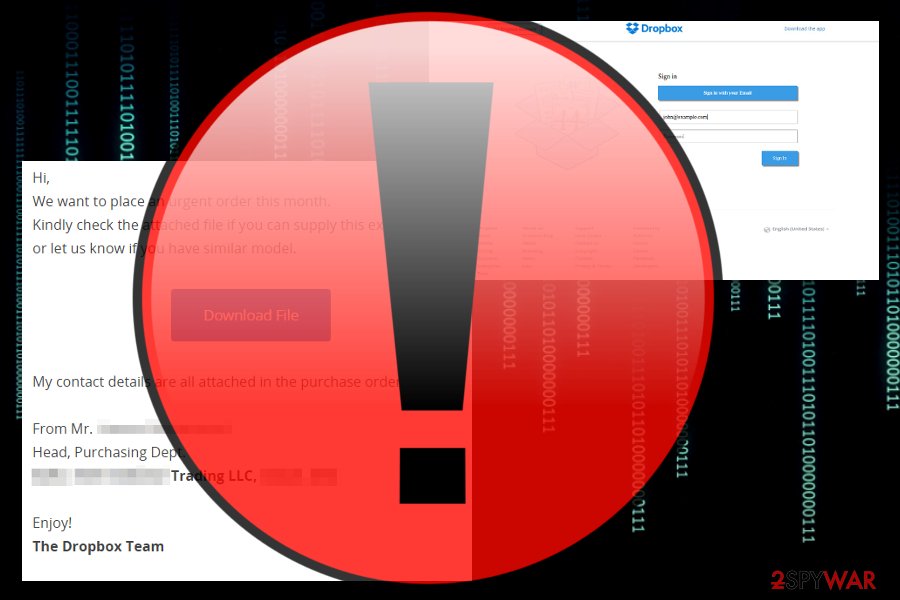
Dropbox phishing alert
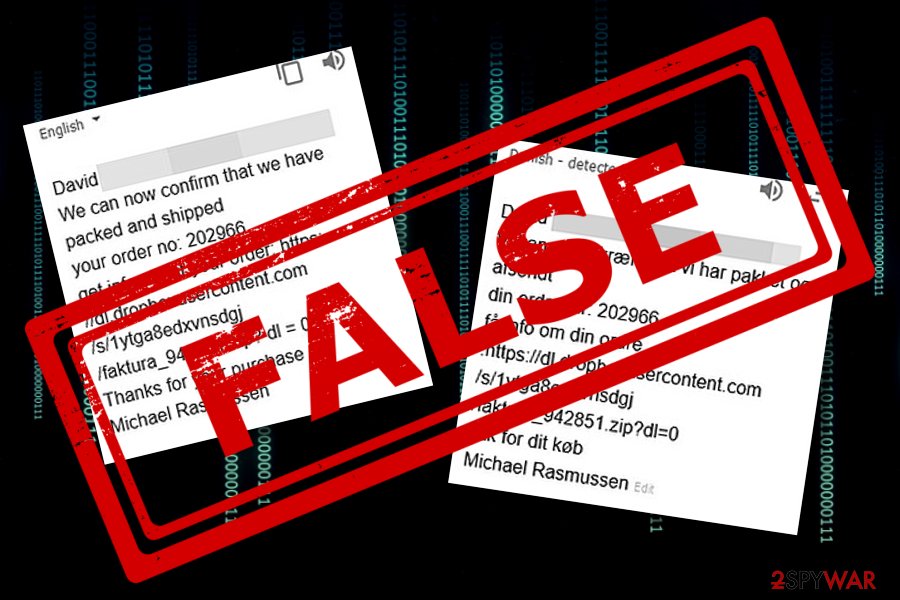
A phishing scam has also been targetting Dropbox by spreading fake email letters about urgent orders that need to be placed.[8] The scam message looks like this:
Hi,
We want to place an urgent order this month.
Kindly check the attached file if you can supply this exact product
or let us know if you have similar model.
If you decide to click on the “Download file” button which also is added in the rogue email message, you will supposedly be redirected to a fake but original-looking Dropbox login page. Be careful and do not provide any type of personal information or login details as they might easily be misused by bad actors.
Trojans misusing Dropbox for distributing threats
Malware was found pretending to be RealNetworks updater executable in order to infiltrate the computer system. Such component appears to be located in the %AppData%realupdate_ob directory and downloading malware-laden files from the well-known Dropbox service.[9] Researchers have discovered some malicious files that misuse well-known application names:
- utorrent.exe,
- Picasa3.exe,
- Skype.exe,
- Qttask.exe.
TrickBot pretends to be Dropbox staff
A dangerous form of malware, known as TrickBot, appears to be distributed via fake Dropbox email messages. This threat is known as a banking Trojan which has been launching malicious campaigns against big finance companies such as PayPal.[10] Bad actors send potential victims email letters which contain a security document that needs to be opened. As expected, it is the malicious payload.
Malware alert: random people sharing files with you
Another malware spam campaign has been released to the wild. Users who are targeted by this spam receive a message that a file has been shared by a random user name. If you select the “Click here to view” button, you will end up with the Amendment or the Agreement_09-11-2015.zip file on your system which downloads another malicious component Agreement_09-11-2015.scr.[11]
Distribution sources of malicious software and objects
According to Virusai.lt specialists, malware-laden components appear on the system by using stealth techniques and injecting themselves through legitimate-looking content. Crooks pretend to be from reputable organizations and send emails that imitate “very important purposes” for which a link needs to be clicked or a file downloaded.
Our suggestion would be to carefully manage all email letters that you receive. If some messages fall in the spam section, better eliminate them without even taking a look as reputable companies will not drop letters in such directories and will supposedly contact you directly via mobile phone or sending a letter to where you are located.
Furthermore, all attachments should be scanned with the help of an antimalware/antivirus program just for ensuring security. This might prevent malware infections from slipping into your computer system through legitimate-looking executables, Word documents, PDF files, and other similar components attached to email messages.
Removal tips for Dropbox malware forms
If you have been infected with some type of dangerous Dropbox malware form, the removal is necessary and should be performed immediately. We do not recommend trying to get rid of the cyber threat without any automatical software as you might accidentally cause even more damage to your computer system.
Automatical Dropbox virus removal is also a good choice for computer users who lack the required skills on the virus elimination field. Our recommendation would be to scan the entire system first with reputable computer software such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and find all possibly-infected locations on your machine.
Furthermore, you will see two system boot options below this text which will help you disable malicious activities before you remove Dropbox virus. Remember that all malicious components such as infectious executables, registry keys, and other types of files need to be gathered and removed from the system for a successful malware removal process.
Getting rid of Dropbox virus. Follow these steps
Manual removal using Safe Mode
Use these steps to reboot your computer system to Safe Mode with Networking. This is a way to prevent malicious activities from spreading further:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Dropbox using System Restore
Activating the System Restore feature on your Windows machine should allow disabling malware-laden components. Follow these guidelines to turn on this mode:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Dropbox. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Dropbox and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ LapinoBEL. Dropbox detected as malware. Malwarebytes forums. Topics.
- ^ Can computer viruses be transferred through Dropbox? How?. Quora.com. Relevant questions and answers.
- ^ dreemsnake. Antivirus detected malware in the Dropbox cache folder. Dropbox forum. Relevant information.
- ^ How Dropbox handles viruses and malicious software. Dropbox Help. Security measures.
- ^ Dropbox delivery of Crypto malware. Hour Computer Man.
- ^ Sarah Brown. How to Decrypt Dropbox Files Encrypted by Ransomware. Intego. Mac Security Blog.
- ^ Dropbox Used In Delivering UPATRE Malware. Trend Micro. Valuable Information.
- ^ SteveG. Fake Dropbox Email Phishing Scam Alert - April 2017. Spam Stops Here.
- ^ Blog Staff. Trojan Downloaders actively utilizing Dropbox for malware distribution. Webroot. Smarter Cybersecurity.
- ^ Olivia Morelli. Fake Dropbox emails spread updated Trickbot malware. 2-spyware.com. Spyware and security news .
- ^ Conrad Longmore. Malware spam: Random Name shared "Amendment or the Agreement_09-11-2015.zip" with you. Dynamoo.com. Tech blog.





















