Fonix ransomware (Virus Removal Instructions) - Decryption Methods Included
Fonix virus Removal Guide
What is Fonix ransomware?
Fonix ransomware uses the extension pattern model that is similar to Ouroborus
Fonix ransomware (a.k.a. FonixCrypter) has been uncovered in early June 2020 by a famous ransomware researcher Micahel Gillespie[1]. The first sample of this deadly dangerous virus has been uploaded into the VirusTotal[2] scanner a day ago, which showed a high-detection rate – 54 out of 74 AV engines can quarantine the infection. However, having a powerful AV engine does not assure the block of the ransomware payload because it's initial expression may not be recognized as malicious.
Unfortunately, the Fonix ransomware payload can spread in camouflage with fake email messages or brute-forced into targeted PCs via unprotected RDPs. If the payload is launched, the ransomware unravels itself in three phases, i.e. infiltration, encryption, and emersion.
According to researchers, the pattern of encryption is reminiscent of the one used by Ouroboros ransomware. The ransomware locks files using a strong combination of Salsa20and RSA 4098 ciphers and appends .FONIX file extension to locked files. The email addresses for contacting the criminals behind this ransomware are fonix@tuta.io and fonix@mailfence.com, though the general information reaches victims in the form of a HowTo Decrypt Files.hta ransom note.
| Title | Fonix |
| Class | Ransomware |
| Encryption mechanism | Salsa20and RSA 4098 |
| Alternative name | FonixCrypter |
| Family | The pattern of extension points to Ouroborus ransomware family (not yet confirmed) |
| Email contacts | fonix@tuta.io or fonix@mailfence.com |
| Ransom notice | HowTo Decrypt Files.hta |
| Risks | The ransomware completely restricts user's access to personal files and urges to pay the ransom in exchange for a decryption key. Thus, people risk losing both data and money |
| Symptoms | It's not possible to pass over a ransomware attack. The main symptom – encrypted files, ransom note, and slow PC |
| Manual vs automatic removal | No manual Fonix removal is possible. One and the only way to get rid of file-encrypting viruses is to scan the machine thoroughly with the fully updated antivirus tool |
| Virus damage fix | FortectIntego is a repair utility that can restore system performance and settings |
Fonix virus is considered to be v6 variant of Ouroborus due to the similarities of the file extension patterning. However, such speculations haven't been confirmed yet since an unfamiliar footer of the encrypted files (x2 0x100 blobs as base64 ASCII w/ colon delims) has been spotted.
Disregarding the geology, the Fonix ransomware belongs to the group of crypto-malware, meaning that it's sole purpose to attack as many people as possible and extort money out of their pockets. The size of the redemption is not clarified, those it typically starts with $490 if the victim contacts criminals in less than 48hours and then gets doubled.
For more information on Fonix decryption possibilities, the victims are supposed to contact criminals via fonix@tuta.io or fonix@mailfence.com emails. However, experts from senzavirus.it[3] and others do not recommend contacting criminals at all and stress the fact that it's not an official contract that would grant that the payment will be followed by data decryption.
Instead of the payment, you should focus on a full Fonix ransomware removal. This malicious cyber infection is not very likely to refuse its position quite easily. When it uncovers the package of the malicious entries, they are scattered in various system's locations, including:
- C:Windows
- C:Program Files
- C:Users/[current user]/AppDataRoamingMicrosoft
- C:\Windows\System32
Finding and decontaminating malicious entries manually is not possible. The only way to remove Fonix ransomware completely is to scan the machine with SpyHunter 5Combo Cleaner, Malwarebytes, or another professional anti-malware tool. However, it's advisable to prepare cold storage for the files encrypted by this malicious crypto-virus. As we have already pointed out, this virus can successfully be quarantined by 53 AV tools out of 73 and the most common detections are as follows:
- Win32:Malware-gen
- TR/Diss.cxjcx
- A Variant Of Generik.IZSVMDG
- Trojan.Win32.Diss.suvbu
- Mal/VMProtBad-A
- Trojan.GenericKD.43207004
- Trojan.Encoder.31902
- Trojan.GenericKD.43207004 (B), etc.
In case AV engine flags any file running on your machine as malicious and report any of the above-listed names, take immediate actions to remove Fonix from the machine. Reboot the system into Safe Mode and set the antivirus to perform a thorough scan.
 Fonix is considered to be a version of Ouroborus ransomware
Fonix is considered to be a version of Ouroborus ransomware
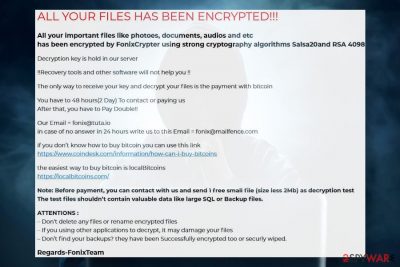
The .fonix file extension virus creators try to scare their victims into transferring the ransom using the intimidation strategy. They generate a ransom note HowTo Decrypt Files.hta on the machine's desktop and list the conditions and threatening not to try renaming or decrypting files manually because a permanent file loss is imminent.
While this may be true, we recommend making backups of the files locked with .fonix extension virus on an external HDD storage, get rid of the ransomware, and them render third-party data recovery software for data recovery.
ALL YOUR FILES HAS BEEN ENCRYPTED!!!
All your important files like photoes, documents, audios and etc has been encrypted by FonixCrypter using strong cryptography algorithms Salsa20and RSA 4098
Decryption key is hold in our server
!!Recovery tools and other software will not help you !!
The only way to receive your key and decrypt your files is the payment with bitcoin
You have to 48 hours(2 Day) To contact or paying usAfter that, you have to Pay Double!!
Our Email = fonix@tuta.io in case of no answer in 24 hours write us to this Email = fonix@mailfence.com if you don't know how to buy bitcoin you can use this link.
The easiest way to buy bitcoin is local Bitcoins.Note: Before payment, you can contact with us and send 1 free small file (size less 2Mb) as decryption test
The test files shouldn't contain valuable data like large SQL or Backup files.ATTENTIONS :Don't delete any files or rename encrypted files
– If you using other applications to decrypt, it may damage your files
– Don't find your backups? they have been Successfully encrypted too or securly wiped.Regards-FonixTeam
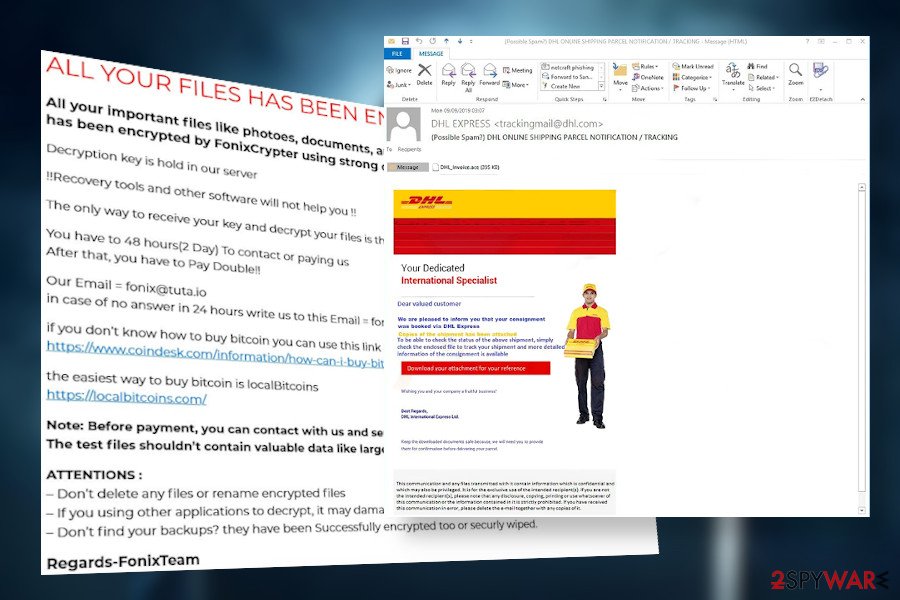
Spam email attachments carry malicious script in the disguise of the legitimate-looking files
The prevalence of the ransomware depends very much on the methods that their developers use for the distribution. Targetted attacks against the business sector are most frequently arranged in advance planning brute-force attacks via unprotected RDPs or other security gaps. Therefore, server administrators must take an obligation to take precautionary steps against cyber attacks by ensuring full update of the software, no vulnerabilities, the most powerful threat protection, strong password protected RDPs, etc.
However, even though criminals want easy money by attacking companies and demanding thousands in exchange for the decryption software, individual home users are no less endangered. Through the year of 2019, criminals managed to infect over 11.5 billion computers[4] and the most successful way for infecting PCs is spam.
Criminals launch spam emails impersonate legitimate companies and organizations. For example, people may get email messages from FedEx saying “See the order confirmation attached.” However, such and similar attachments contain malicious scripts that demand enabling macros. That's a catch since not a macros get enabled, but a ransomware payload.
Thus, if you see a suspicious message in your inbox, do not open its attachment. Analyze the email for grammar mistakes and double-check the sender. In case of any suspicions arise, send the email to spam to protect your machine and data from attacks.
 Fonix ransomware virus is usually spread via malicious spam email attachments
Fonix ransomware virus is usually spread via malicious spam email attachments
Fonix ransomware removal will not help to recover files but prevents downloads of other viruses
Fonix ransomware removal is a must. This intruder causes much damage to the machine by disabling some functions, such as security software, and increase vulnerabilities to open backdoor access to other cyber threats, such as Trojans or spyware. For that reason, you do not postpone ransomware elimination.
To remove Fonix ransomware virus from the Windows system once and for all, you need to launch the AV scanner while the system is booted in Safe Mode with Networking. However, before launching the scanner, make sure that the software is updated and has the latest virus definitions. Our recommended tools for that purpose are SpyHunter 5Combo Cleaner and Malwarebytes.
While the Fonix removal may not be a difficult task for the AV tool, the recovery of the system itself is a bit more intricate procedure that should be performed with a dedicated repair tool. Therefore, upon full virus decontamination, run a scan with FortectIntego to recover Windows Registries and other important files that could have been damaged.
Getting rid of Fonix virus. Follow these steps
Manual removal using Safe Mode
Safe Mode with Networking environment disables malicious processes and allows launching AV scanner for performing Fonix removal undisrupted.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Fonix using System Restore
Make the damage on the system reverse by restoring the computer to a previous point with System Restore feature
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Fonix. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Fonix from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Fonix, you can use several methods to restore them:
Data Recovery Pro is a tool that can save the day for those attacked by the .fonix file extension virus.
If you don't have data backups of the encrypted files, you can take advantage of the Data Recovery Pro tool, which may help to decrypt at least a part of your files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Fonix ransomware;
- Restore them.
Windows Previous Versions feature – yet another alternative data recovery tools
If you have already removed the ransomware, try to retrieve files locked by Fonix virus using this tutorial.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can recover encrypted files separately
You can try to unlock files encrypted by the ransomware with Volume Shadow Copies. Unfortunately, this option won't work if the virus has enabled the command to delete these copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
The official Fonix decryptor does not exists
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Fonix and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Michael Gillespie @demonslay335. Twitter. An American microblogging and social networking service.
- ^ Fonix ransomware sample. VirusTotal. The free URL and file scanner.
- ^ LE NOVITÀ SU SICUREZZA E SPYWARE. Senzavirus. Virus and spyware news.
- ^ Ransomware Facts, Trends & Statistics for 2020. Safety detectives. Cybersecurity news.





















