Get-shields.com ads (Free Instructions)
Get-shields.com ads Removal Guide
What is Get-shields.com ads?
Get-shields.com shows fake messages that encourage users to download potentially unwanted applications
Get-shields.com is a malicious website designed by crooks. Most commonly, people do not enter it intentionally but are rerouted to it after clicking a link on some shady website or taking it by automatic scripts.[1] The important part here is that users do not expect the redirect to happen, hence why the hosted scam sees moderate success over time.
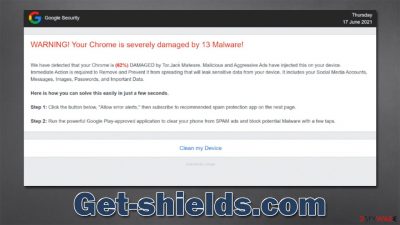
Once there, users are presented with the “WARNING! Your Chrome is severely damaged by 13 Malware!” scam message, which is meant to frighten them and try to convince them that their systems are infected – this is typical social engineering[2] technique operated by tech support scammers. Get-shields.com also pretends to represent “Google Security,” which is not at all true, as Google has nothing to do with this.
The main goal of scammers is to make users download questionable software – an activity that they financially profit from. We recommend not interacting with any of the links or other site components, as you risk making everything much worse, e.g., installing malware on your device. Instead, we recommend checking the below instructions on how to recover after visiting a scam site such as Get-shields.com.
| Name | Get-shields.com |
| Type | Scam, phishing, fraud, fake alert |
| Operation | Claims that Chrome browser has been damaged by malware. It then asks users to download a fake security tool to remove it |
| Risks | Fake messages usually aim for users to download potentially unwanted or malicious programs, steal their personal information or trick them into subscribing to useless services |
| Removal | You should not interact with the content shown by a scam website. Instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Other tips | You should remove caches and other web data to prevent data tracking – use the FortectIntego repair and maintenance tool. You can also repair damaged system components with it |
The scam message and what it means
Tech support scams are extremely effective because they attempt to abuse users who are not familiar with them and computing in general. When users are frightened, they become extremely worried about their computer security and personal safety, which can prompt them to make rash decisions. Get-shields.com tries to abuse this situation.
As soon as users enter the page, they are presented with one of the fake messages that the scammers host. Most commonly, people might be shown the following widespread scam:
WARNING! Your Chrome is severely damaged by 13 Malware!
We have detected that your Chrome is (62%) DAMAGED by Tor.Jack Malware. Malicious and Aggressive Ads have injected this on your device.
Immediate Action is required to Remove and Prevent it from spreading that will leak sensitive data from your device. It includes your Social Media Accounts, Messages, Images, Passwords, and Important Data.Here is how you can solve this easily in just a few seconds.
Step 1: Click the button below, “Allow error alerts,” then subscribe to recommended spam protection app on the next page.
Step 2: Run the powerful Google Play-approved application to clear your phone from SPAM ads and block potential Malware with a few taps.
In this example, crooks are claiming that the system was infected with so-called Tor.Jack malware, which actually does not exist, and the name is completely fabricated. Crooks prey on users who are not familiar with these technicalities, and their goal is to throw as much scary, confusing information as possible.
We recommend not clicking any links or downloading software from websites that say your system is infected, damaged, or missing something, as it usually means potentially unwanted applications or even malware are being spread.
Remediation steps and how to remove adware
Many users immediately assume they have been infected with a virus once they are redirected to Get-shields.com. While all the statements and messages on the page are fully fabricated, dismissing the possibility of infection completely is not advisable. Adware, for example, is one of the most common infections that users don't expect to find on their systems, as it is spread using deceptive distribution methods such as bundling[3] or fake updates.
Remove unwanted or malicious apps
Adware might be responsible for phishing, and other dangerous websites users encounter regularly. Therefore, we recommend you check your device thoroughly – the easiest way to do that is by scanning it with SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful security software. Alternatively, you can look for unwanted programs yourself as follows:
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
While moving apps into Trash is usually how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Don't forget to check for unwanted extensions – you can find them by accessing browser settings or clicking the “Extensions” button on the browser.
Clean your browsers to secure your privacy
To stop the unwanted tracking activities, you should remove cookies and other trackers from your computer. To do that, you should access browser settings or employ a powerful PC maintenance tool FortectIntego, which can also be used to fix any virus damage if such has occurred.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Josep Albors. Malicious scripts in compromised websites and how to protect yourself. WeLiveSecurity. ESET security blog.
- ^ Social Engineering. Imperva. Application and data security.
- ^ Bundled software. Computer Hope. Free computer help.







