Gineaersifyo.top pop-up ads (spam) - fake
Gineaersifyo.top pop-up ads Removal Guide
What is Gineaersifyo.top pop-up ads?
Gineaersifyo.top – a site created to make money through pay-per-click advertising

There are plenty of fake websites created for the sole purpose of being a passive income source. Gineaersifyo.top is a fake page that tricks users into allowing it to send push notifications. If you give this site permission, you will start getting spammed with commercial content in pop-ups, banners, and redirects.
Creators fool people using social engineering tactics[1] that are commonly used to manipulate users online. In this case, a website shows a message “Download Is Ready click Allow to download your file.” But if you look at the bottom of the page, in smaller letters, it is written, “By continuing your navigation or clicking “Allow,” you accept our terms of use and privacy policy and agree to receive sponsored content.”
There is a page we have previously written about Todiscuassy.top that looks exactly the same and does same things. Usually, users do not stumble on sites like this by their own will. Most commonly, they get redirected from other shady websites. It is likely that users are this easily fooled because they were looking to download something for free that normally has to be paid for. For example, a person wants to watch a movie for free and finds an illegal streaming platform where they see a “Download” button.
Without realizing that the button is fake and actually an ad, a new tab opens where users get redirected to Gineaersifyo.top where they supposedly just have to click “Allow” to receive what they want. Of course, after clicking it, they do not get a movie because this website is completely unrelated to the one they were on. This is where they start experiencing erratic browser behavior and wonder what happened.
| NAME | Gineaersifyo.top |
| TYPE | Adware; PUP; push notification spam |
| DISTRIBUTION | Bundled software, redirects from untrustworthy websites |
| SYMPTOMS | Increase in commercial content, pop-up ads appearing even when the browser is closed |
| DANGERS | Ads shown can come from illegitimate sources and lead to other dangerous pages, which can lead to more serious problems |
| ELIMINATION | Usually, elimination is achieved easily by going to the browser settings |
| FURTHER STEPS | FortectIntego should be used to perform a system scan after removal. It can find any remaining issues left and try to repair the damage |
Learn to identify fake pages
Although in this day and age, fake websites and scam techniques have gotten more complicated and harder to recognize for an everyday user, there are still some basic things you can focus your attention on to try and avoid unwelcome intruders.
- Check the URL: unusual-looking URLs with rarely used extensions like .top, .xyz, .org, .io are indicators of a suspicious website. The reason for this is that domain names with .com are way more expensive. Of course, some scam websites do not want to spend money trying to make the site look legitimate.
- Look for a lock: the padlock next to a websites' links means that a site is secured by a TLS/SSL certificate that encrypts user data. You can look for the lock on the upper left of the address bar. Three types of TLS certificates will display a lock: Domain Validation, Organization Validation, and Extended Validation. Most browsers will display a “not secure” warning if a site does not have a lock.
- Research: read the privacy policy, look for contact information, inspect if the grammar and spelling on the website are correct. Look for additional information online, read the reviews.
- Use a website checker: if you have doubts, use a website checker[2] to verify the security. A secure website check can let you know any vulnerabilities on the site if it uses encryption and what level of verification a site has.

If you click on a fake site:
- Do not provide any sensitive information like financial details, a login and password, your name, and contact information.
- Do not click on random links from unfamiliar emails, online posts, or private messages.
- Please report it to Google Safe Browsing[3] and exit it right away.
Removing Gineaersifyo.top from your browser is quite easy if it is a simple “I clicked the “Allow” button” situation. You can do this manually by following the instructions provided below. After removal, it is recommended to use FortectIntego to automatically clear your browsers of anything that possibly was left by the program.
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
![Stop notifications on Chrome PC 1 Stop notifications on Chrome PC 1]()
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.
![Stop notifications on Mozilla Firefox 1 Stop notifications on Mozilla Firefox 1]()
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
![Stop notifications on Edge 1 Stop notifications on Edge 1]()
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
![Stop notifications on Edge 2 Stop notifications on Edge 2]()
MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right on the window.
- Select Internet options and go to Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
Websites track what moves you make online
Cookies are normally used to remember information about users. This information can be used to personalize web pages contents to make them more relevant. Cookies also track the browsing habits of users to identify their interests, hobbies. For this reason, you see ads of the same or similar things you search for in your spare time. If cookies are collected by legitimate and trustworthy sites, there is rarely something you should worry about, that is, of course, if you do not mind them tracking your behavior to make your experience personalized.
Problems arise when websites that belong to shady individuals get permission to track you. Gineaersifyo.top Privacy Policy, which seems to be just copied from another website, without changing a single word, says:
Celebsupdates may use third-party service providers who help Celebsupdates operate its business or administer activities on our behalf, such as sending out newsletters or surveys. Celebsupdates may share user's information with these third parties for those limited purposes provided that the user has given Celebsupdates user's permission. However Celebsupdates does not control such third parties practices and is not liable or responsible for any practices used by these third parties.
They can provide information about you to whoever they want, and they are not liable for anything negative you experience because of third-party activities.
We suggest implementing clearing browsers' cookies and cache in your routine. You can do this yourself. If you do not know how you can learn from our guide below:
Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Clear cookies and other browser data from MS Edge:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Clear cookies and site data on Mozilla Firefox:
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
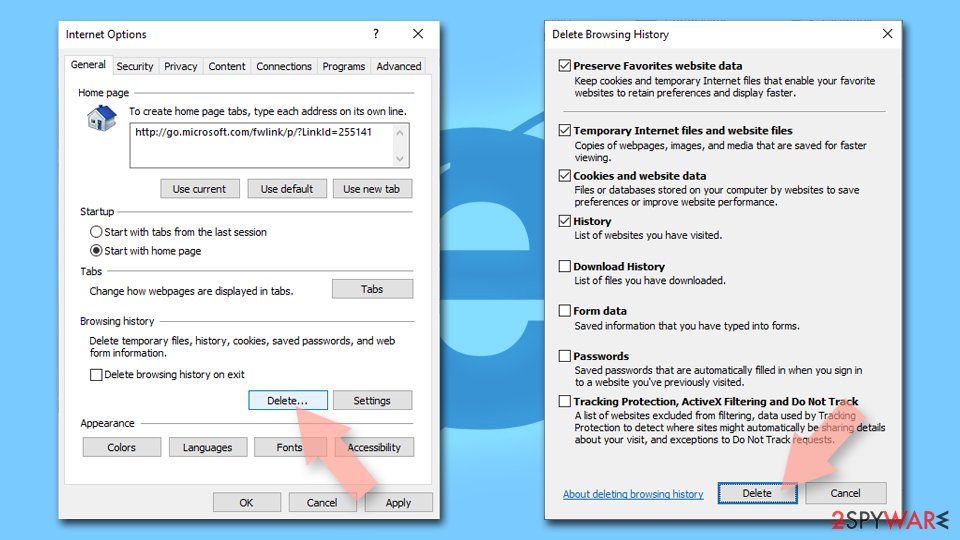
Delete temporary files from Internet Explorer:
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
![Clear temporary files from Internet Explorer Clear temporary files from Internet Explorer]()
Additional tips
If you were unsuccessful in deleting Gineaersifyo.top from your browsers' permissions, there might be adware operating in the background without your knowledge. Use SpyHunter 5Combo Cleaner or Malwarebytes professional security tools to scan your machine and try to detect which program is responsible for unwanted behavior.
Or, if you know what you are doing, you can remove the program manually. Look for instructions at the bottom of the page.
Getting rid of Gineaersifyo.top pop-up ads. Follow these steps
Uninstall from Windows
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Imperva. Social Engineering. Imperva. Learning Center.
- ^ Bureau of Internet Accessibility. How Do Automated Website Checkers Work?. BOIA. Internet Accessibility Blog.
- ^ Google. Send a Report to Google. Google. Report.