HawkEye virus (Free Instructions) - Virus Removal Guide
HawkEye virus Removal Guide
What is HawkEye virus?
HawkEye virus is the keylogger that is distributed online for cheap as a basic keystroke stealing tool for any hacker wannabe

HawkEye malware is dangerous because it manages to run in the background and affects the performance this way when the processes use resources of the PC. However, in many cases, this threat does not cause any symptoms and cannot be indicated at all. It even gathers data from the clipboard, monitor input to documents and information stored on the machine locally. The malware sends this information to remote C&C servers[2] that hackers control. Operating in the background without causing other issues allows the trojan to steal information unnoticed and leave the machine, so the victim cannot know that their data is at risk or stolen. Malware can make purchases and transactions or hack accounts on various platforms with those stolen logins and other credentials.
| Name | HawkEye virus |
|---|---|
| Type | Malware. This virus can be categorized as info-stealer, keylogger or banking/password-stealing trojan |
| Danger | The malware runs in the background and can gather various information from the machine directly, use keylogging techniques and record keystrokes to obtain credentials, passwords, logins and other valuable information from the victim |
| Tactics | Gather information related to financial sites, platforms like email or social media to hijack accounts or make fraudulent transactions and purchases using online banking data |
| Damage | Hacked accounts can be sued to scam people in the contacts, and people lose their money after the fund transferring to attackers; wallets and bank accounts. Malware can run or install additional viruses without any symptoms and damage the machine significantly |
| Versions | HawkEye Reborn v9 was released at the beginning of 2019. The update included particular license purchase for 90/180.365 days |
| Distribution | Hacker forums provide the tool for sale. The malware script gets included on emails or in pirated software packages, so people cannot notice or stop the infiltration[3] |
| Elimination | HawkEye virus removal process may be difficult since trojan hides in various places by using multiple files with code and associate programs, so AV tools are required for the proper system scanning and cleaning |
| Repair | Malware that affects particular functions of the system can inject scripts and alter settings on the machine that completely damage the computer. Run FortectIntego to repair any damage or indicate affected files and applications |
HawkEye virus is designed to steal information from devices it gets infected and can be used as malware dropper that leverages its botnets to fetch other malware and enable third-party actors to perform their crimes. It is capable of capturing keystrokes and screenshots or even steal credentials from various applications and from the system clipboard. All these activities cannot be tracked or noticed by the user since malware is not delivering any symptoms.
Harvested credentials from email clients and web browsers can get encrypted and sent to malware operators via email or the SMTP protocol, so HawkEye virus creators store such details for the later use in scams and targeted attacks. This particular trojan is one of the more interactive threats, and hackers use the tool for their criminal activities because sensitive information is extremely valuable.
HawkEye info-stealer is known for various campaigns throughout the years because it targeted victims since 2013 when it was started to be sold on hacker forums and other dark web sources as a cheap tool for criminals. It gets regular updates and includes new capabilities, functions with each newer release.
You should remove HawkEye virus as soon as possible because malware can get new functions like monitoring solutions and more advanced data exfiltration features. But since this is a threat that relies on various techniques, you need advanced options too. The best way to get rid of such malware would be anti-malware tools security software based on AV detection engine functionalities. 
HawkEye virus removal gets more and more difficult with each new update and improvement because detection is more difficult when the trojan is disguised as other files and programs. Anti-malware engines are designed to find malicious behavior-based threats and remove them. Now every tool can detect this trojan, so elimination is not performed in time.
HawkEye virus have been active across various platforms and will likely continue to be used in the future because developers can monetize the creation easily. This spying tool demonstrates that ongoing development and improvements helpt to move forward and affect the devices with even more dangerous versions like HawkEye Reborn v9 malware.
HawkEye virus can be spread with the use of spam email campaigns that disguise malicious code in files listed as financial information or order details, so the user falls for the trick. It is especially successful when emails state about a real company involvement, for example:
DHL Capability Tool
ATTN:
Your shipment has arrived!
Arrival Information
Your package has been arrived to your local DHL office and it’s ready for pick up.
——————————————
ARRIVAL NOTICE
——————————————DATE & TIME : 2018-04-19 at 11:40
STATUS : Shipment arrived************************
Please print the receipt that is attached to this email and visit DHL location indicated in the receipt
DHL WorldWide Delivery
©2018 DHL International
HawkEye virus can rely on payload droppers and act as one itself, there is a bigger possibility that malware is installed alongside other programs during the macro virus triggering, so your device is further affected. If you find any suspicious processes running in the background or find issues with the performance, check the machine with FortectIntego or a similar tool and repair any possible damage yourself in system folders and functions. 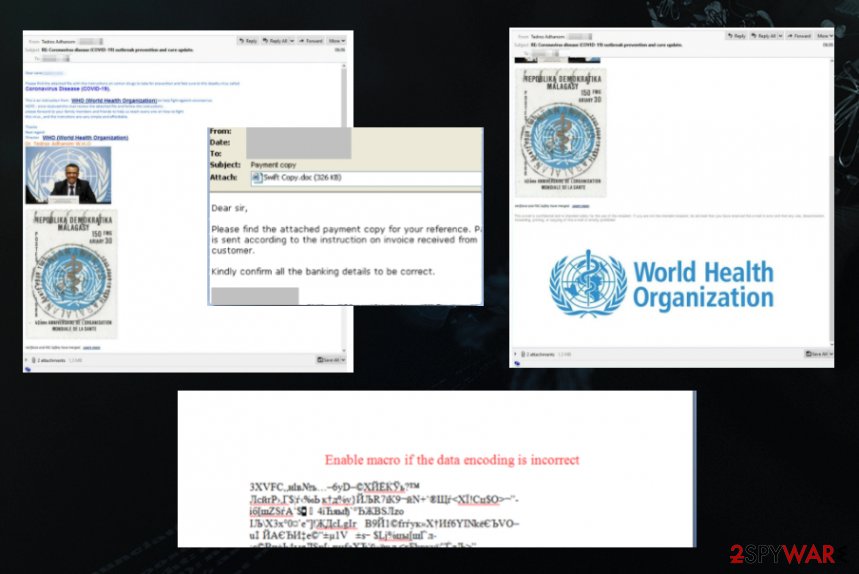
Spam email campaigns and remote access tools allow silent malware infiltration
Malware that can be proliferated without users' knowledge and intervention can be extremely dangerous. These methods involving spam campaigns and RATs can spread thousands of pieces of malware at once, so criminals achieve their goals pretty quickly.
Once the email is received and you can find the attachment as a document or executable, PDF, archive, you should immediately pay closer attention to other details. Once the document is opened malware gets introduced on the system, and remote access tools can be used. Those document attachments include malicious macros that get enabled by the user once the file is downloaded and opened.
In most cases, the attachment states about some kind of important information that users want to access, so not many of them pay attention to the button that triggers the content appearing on the screen. However, the same button releases the malware payload and allows the malware to run on the PC.
HawkEye malware termination includes full system scans and cleaning processes
Even though the HawkEye virus is not, so sophisticated threat and can be purchased online for cheap, the function remains dangerous and damaging. Updates to the functionality include processes similar to other spying software and detection avoidance. These changes increase the chance of getting machines successfully infected, so victims suffer data loss and account hacks without noticing the malware that gathered those details in the first place.
We should recommend getting a proper security tool for the HawkEye virus removal because any leftover files and malicious code that is running on the device can trigger damage and additional malware infections. If you leave anything related to the trojan on the system, your device may get permanently damaged. Rely on security tools(SpyHunter 5Combo Cleaner or Malwarebytes), and clear the system from virus-related data.
If you want to remove HawkEye virus quickly, you need to choose the proper AV tool that can possibly detect[4] the malware and terminate all the processes associated with the attack. Since versions of this malware category can proliferate using email spam campaigns and other stealthy methods, you can have more than one virus on the machine already. Make sure to check for the damage using FortectIntego.
Getting rid of HawkEye virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking to remove HawkEye virus suing proper AV tools
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove HawkEye using System Restore
You should try System Restore as an option for deleting the malware because it is the feature that allows recovering the system in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of HawkEye. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from HawkEye and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Tara Seals. Revamped HawkEye Keylogger Swoops in on Coronavirus Fears. Threatpost. News on threats and security.
- ^ Botnet. Wikipedia. The free encyclopedia.
- ^ Malicious spam campaigns proliferating. ZDNet. Technology and security news.
- ^ Malware detection rate. VirusTotal. Online malware scanner.





















