Hero-files.com ads (fake) - Free Instructions
Hero-files.com ads Removal Guide
What is Hero-files.com ads?
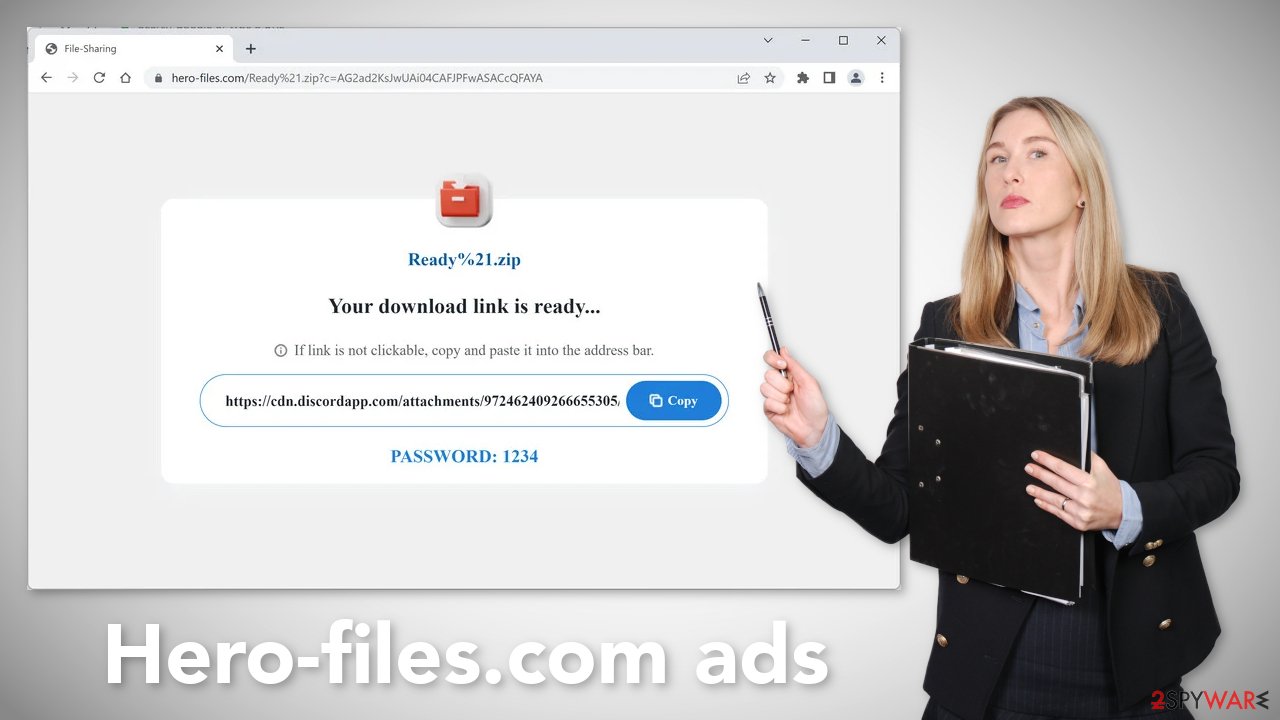
Hero-files.com is not a real download page and it might infect your PC with hijackers or malware
Hero-files.com is a dangerous website created by crooks to trick users into downloading PUPs (potentially unwanted programs)[1] or even malware. People may get infected by malicious browser extensions and experience erratic symptoms. The main settings of the browser, like the homepage, new tab address, and search engine might change. Fraudsters can force people to use only selected channels for browsing which raises many user privacy and security concerns.
A PUA may also cause an increased amount of commercial content on the machine, like pop-ups, banners, and redirects. The advertisements can be placed by rogue advertising networks[2] that lead users to other dangerous websites. Ultimately, this is just another bogus download page. It asks users to click on an unknown link that supposedly provides users with a file that they were looking for.
| NAME | Hero-files.com |
| TYPE | Phishing attempt; adware |
| SYMPTOMS | A page opens asking users to open an unknown URL to download a file |
| DISTRIBUTION | Shady websites; deceptive ads; sneaky redirects; bundled software |
| DANGERS | Users may be tricked into downloading potentially unwanted programs or malware |
| ELIMINATION | Scan your machine with anti-malware tools |
| FURTHER STEPS | Use a maintenance tool FortectIntego to clear your browsers |
Distribution methods
Usually, fake “Downloader” sites, like Hero-files.com, and Alternatesearches.com appear when users browse through torrent sites,[3] peer-to-peer file-sharing, or freeware distribution platforms. Specifically, they open after clicking on deceptive ads, and fake “Download” or “Play” buttons.
Do not try to install “cracked” software[4] because the risk of infection is very high. You can never know if a program you want to download is safe or a disguised virus. Even though it might get costly, it is best to use official web stores and developer sites.
Apps that get listed on digital marketplaces go through an extensive review process. Besides you can choose from free alternatives. It is not worth it to risk damaging your operating system and losing important files to watch a movie for free or install pirated software.
The site may have also opened automatically without any user input. This can happen if there is adware – advertising-supported software hiding on the machine. It can cause an increased amount of commercial content without any user knowledge.
How to avoid fake “Download” buttons?
When you are browsing the web and see a big, flashy “Download Now” or “Your Download Is Ready” button and you are not sure if it is real, hover your mouse over it. You should see a glimpse of the URL that it would take you to at the bottom or top of the screen. If it does not appear to include the file name that you want to download, the button is probably fake.
The hidden dangers of cookies
Almost every website you visit and every browser plugin uses cookies[5] to track your online behavior. Cookies are small data files that can store data such as your IP address, geolocation, links you click on, things you purchase online, etc. Normally, this information is used to personalize the user experience.
However, we notice that more and more often they are used to monetize user activity. The collected data can be sold to advertising networks or other third parties. There have also been instances when cookies were hijacked and used for malicious purposes.
That is why we recommend clearing your browsers regularly. You may use a maintenance tool like FortectIntego that can perform this task automatically. This powerful software can also fix various system errors, BSODs, corrupted files, and registry issues which is especially helpful after a virus infection.
Check your browser for unwanted extensions
Since you may be infected by a malicious browser plugin, find the list of extensions installed in your browser and remove them one by one to see if you notice any changes. You can follow the step-by-step instructions below:
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. IT Insights.
- ^ Christian Rigg. Are torrents actually dangerous?. Tomsguide. Tech Reviews.
- ^ Georgina Torbet. 5 Security Reasons Not to Download Cracked Software. Makeuseof. Security Blog.
- ^ Chris Maus. What Are Cookies and Are They Dangerous?. Qkey. Secure Online Payment Providers.
- ^ Jason Carreiro. The Hidden Dangers of Freeware and How You Can Avoid Them. Vircom. Security Services.










