Html/rce.gen3 (Virus Removal Instructions) - Improved Guide
Html/rce.gen3 Removal Guide
What is Html/rce.gen3?
Html/rce.gen3 – a trojan that gets detected by antimalware every time when the user opens Internet Explorer
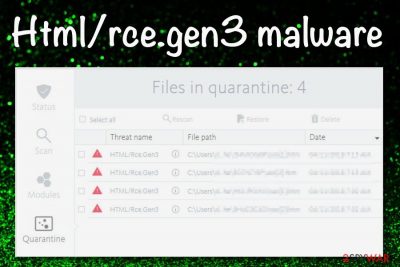
Html/rce.gen3 is reported to be a Trojan virus[1] that is detected by antivirus software when users open web browsers such as Google Chrome, Mozilla Firefox, Microsoft Edge, and Internet Explorer. A user has reported that Avira antivirus drops malware alerts related to this malicious product every time she launches Explorer.[2] The cyber threat targets Windows computer systems, can inject malware-laden code into web browser apps, install questionable processes, include malicious keys, and make a negative impact on the software and services that are running on the infected device. If you want to learn more about Html/rce.gen3 virus and what it is capable of, continue reading this article.
| Name | Html/rce.gen3 |
|---|---|
| Type | Trojan/malware |
| Danger level | High. Can install other malware and steal personal, banking information, include malicious code into web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer, and Microsoft Edge |
| Symptoms | Even though trojans show very little symptoms, some of the signs can still be spotted by accurate users. You might see a sudden overuse of your CPU's power, encounter unknown processes in your Windows Task Manager, find out that your programs and OS are running slower than before |
| Target | This Trojan virus is targetting users that are using computers running on the Windows operating system |
| Spreading | Trojans can be distributed by other malware and potentially unwanted programs. Furthermore, you can catch some type of infection while downloading products from torrenting networks, clicking on an infectious hyperlink or advertisement, opening a malicious email attachment |
| Removal | You should employ reliable antimalware software for the elimination of this cyber threat |
| Fix | If you have discovered any damaged areas on your device, try repairing them with FortectIntego |
Receiving a trojan infection such as Html/rce.gen3 is a really unpleasant thing, especially, when you know what types of consequences might be waiting for you. If you are a careless user and like visiting various torrenting networks, clicking on random ads, and opening spam emails, you slightly increase the risk of catching such type of malware infection.
However, trojans, including Html/rce.gen3, rarely come on their very own. If you have been attacked by this parasite, it might be because another infection, e.g. trojan, ransomware, worm might be hiding on your computer system. Nevertheless, potentially unwanted programs such as browser hijackers and ad-supported applications can also be used as intermediaries for distributing trojans and other malware.
Html/rce.gen3 can alter the Windows Registry and Task Manager sections by filling these places with unknown processes and keys. This way the trojan ensures that its malicious module is executed every time the user turns on the Windows PC. Furthermore, the malware might enable full recovery after partial removal to stay persistent even longer.
When Html/rce.gen3 appears on the device, it might not show any symptoms of infection at first. Trojans are known as hard threats to find when you are not expecting them. Even though these parasites try to hide every footprint, there still are some minor signs from which a skilled user can aim to spot that something is going wrong with his machine:
- A sudden increase in CPU[3] usage. The Trojan horse might start loading many programs at once or running multiple processes at a time that will start overusing the power of your CPU. The same can happen with the GPU too.
- Unexpected or doubled processes running in the Windows Task Manager. If you have found this section filled with new unknown tasks or you see almost identical executables running, this might be an accurate sign of a trojan.
- Your system and programs are failing. Finding your computer and software slowly launching or crashing in the middle of the process might also be a symptom of a dangerous malware infection.
Of course, if your antivirus software provides you with warnings that include the name of Html/rce.gen3, this is the most accurate sign that your computer is infected and you have to take some action. However, some times such infections might be evading antimalware detection and if you want to diminish this type of process, rebooting your computer in Safe Mode with Networking might do the thing.
Trojans such as Html/rce.gen3 can pose a lot of danger to your personal information and credentials. These parasites are able to record all the information that is hidden on the attacked device. If the trojan gets access to data that is related to your banking account, the malware might aim to connect to it and swindle all the money from that account.
Furthermore, if Html/rce.gen3 gets its hands on data that personally identifies you, the criminals might also misuse this type of information for legitimate purposes, e.g. identity theft. Nevertheless, hackers can put stolen details for sale on dark web markets that are accessible for all types of people worldwide.
If the hackers get remote access to your computer, Html/rce.gen3 can start installing what type of programs and files it wants. Sadly, this can relate to receiving more trojans or other dangerous infections such as ransomware viruses that result in total data encryption and often losses in valuable files as many people cannot restore them.
Some trojans, possibly Html/rce.gen3 too, can lead users to malware-laden websites that carry additional infections. Others might use your computer for delivering intrusive pop-up advertisements, scams for gathering monetary income. Additionally, there is also a variety of trojans that are named cryptocurrency mining malware and they use the device's resources for mining digital currency such as Bitcoin, Monero, Ethereum, Litecoin, etc.
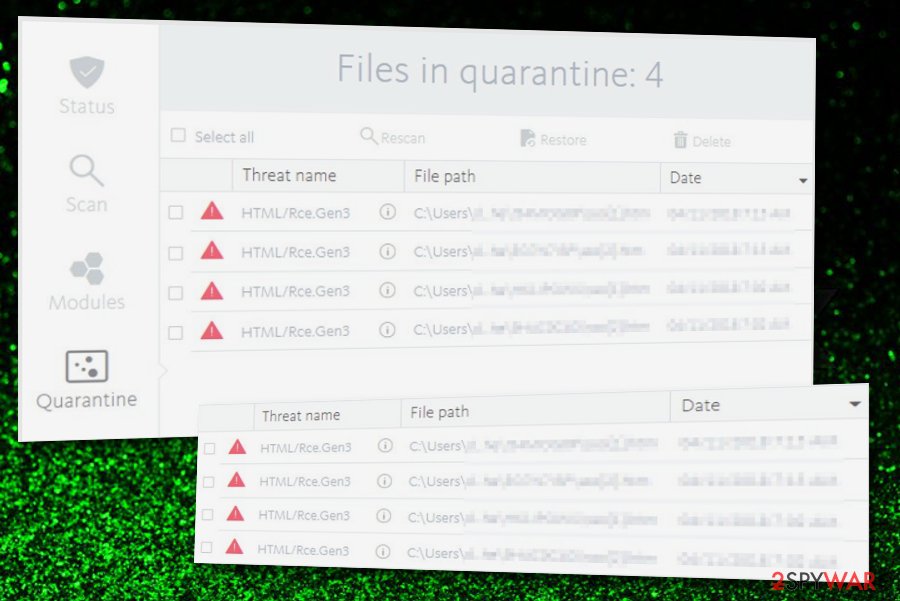
If you ever discover this Trojan horse on your Windows computer system, you should hurry up with Html/rce.gen3 removal before anything very bad happens. This type of process requires reliable antimalware software and manual elimination is not a possibility in this case as it can bring more damage or you might skip some crucial steps.
When you are ready to remove Html/rce.gen3 from Windows, make sure that your antimalware is capable of spotting this threat. If not, reboot your computer in Safe Mode with Networking to diminish malicious processes that are preventing you from eliminating the cyber threat. Afterward, if you have discovered any damaged locations on your device, you should try repairing them with the help of a tool such as FortectIntego.
Malware spreading through torrenting – a common attack vector
Malware researchers from Virusai.lt[4] state that various malware forms, including Trojan viruses are often distributed through pirating sources such as The Pirate Bay. Crooks use all types of software cracks such as key generators to disguise the malicious payload. The best way to keep yourself safe from such infections is to stop using secondary-downloading networks that are filled with cracked products.
Moreover, one malware form can bring another malicious product to the system and the virus delivery process executes in a chain module. The same can happen if you are infected with a potentially unwanted program. The adware or browser hijacker can act as an intermediary until the trojan reaches its destination.
To add, malicious infections can get downloaded from hazardous hyperlinks and malvertising advertisements that are also placed on unknown sources. Beware not to click on every component that you find while browsing online. Protect yourself automatically by downloading reliable antimalware software.
Furthermore, malware can be distributed via phishing email messages and the malicious attachments that come clipped to the letters. Crooks often pretend to be from reputable companies to convince users to open the attached file. DO NOT load any component without performing a full malware scan first.
Instructions on how to get rid of Html/rce.gen3 virus
If you have discovered the trojan on your Windows computer system, you have to take all actions possible to remove Html/rce.gen3. Keep in mind that you should not try eliminating the malware yourself as this can bring damage to your computer or you might skip some crucial steps while completing the process. Rather than taking such risks, employ reliable antimalware software for executing the task.
During the detection process of the malware, some antivirus programs might have problems to spot it. This might be due to the issue that the trojan is blocking your antimalware software from detecting it. Before completing proper Html/rce.gen3 removal, you should reboot your Windows computer in Safe Mode with Networking to diminish the malicious changes that have been included by the virus.
Note: virus elimination of Html/rce.gen3 has to be a full process. If you get rid of the malware only partially, it might be able to reconstruct itself and rise again the next time you boot your Windows device.
Getting rid of Html/rce.gen3. Follow these steps
Manual removal using Safe Mode
If you are looking for a way to deactivate malicious changes on your Windows computer and disable the virus, try launching Safe Mode with Networking as explained in the below-provided guidelines.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Html/rce.gen3 using System Restore
Reversing your computer back to its previous position is possible, you just have to use System Restore. If you do not know how to activate this feature, complete the following instructions.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Html/rce.gen3. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Html/rce.gen3 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ What is a Trojan Virus?. Kaspersky. Resource Center.
- ^ KathieReed. 'HTML/Rce.Gen3. Microsoft forums and answers. Community section.
- ^ CPU. Tech Terms. Definitions.
- ^ SAUGUMO IR VIRUSŲ NAUJIENOS. Virusai. Security and spyware news.





















