Invisible Stealth Keylogger
Invisible Stealth Keylogger Removal Guide
What is Invisible Stealth Keylogger?
The publisher of Invisible Stealth Keylogger states that
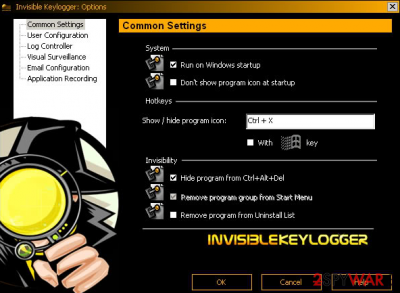
Invisible Stealth Keylogger is an extremely useful auditing and security tool. It runs silently in the background, records all of the machine's keyboard activities into a binary log file. The binary log file can later be viewed via included ''datview.exe'' utility […] Invisible KeyLogger Stealth for WindowsNT version 1.0 is the world's first keystroke recorder that can capture even NT's trusted logon (alt-ctrl-del logon). It runs silently in the background, records all of the NT machine's keyboard activities into a binary file. This binary file can later be viewed via the 'datview.exe' utility provided. The only file that is required for keystroke recording is the file ''iks.sys''. This file can be renamed to maximize stealth. The binary log file can also be renamed and be redirected to a different path. The primary purpose of this program is to provide network administrators with an effective means to monitor workstation usage in hostile environments. It is an equally effective tool for parental control, security audit and network penetration for the security professionals.
About Invisible Stealth Keylogger
The developers of this keylogger (which is also known as Invisible Keylogger) have released three versions of this keylogger: Invisible Stealth Keylogger 1.2d, Invisible Stealth Keylogger 2.0, Invisible Stealth Keylogger 2.1. Although the developers of this application claim that it is a very beneficial tool, you should also remember that it can be used not only for guiltless purposes. This program can also be used to collect private information about the PC user. Moreover, if someone installs this program to your PC, they might become able to see your credit card info, your passwords, and basically track every click that you perform on your keyboard. As a result, such stealth of personal information can lead to data leakage or even financial tear-off. Needless to say, no one wants to suffer because of the activity of hackers and data thieves.
How can Invisible Stealth Keylogger enter victim's computer?
Invisible Stealth Keylogger can infiltrate your computer if you:
- Tend to install freeware or shareware without paying attention to installation settings;
- Browse through unreliable websites and allow to install suspicious apps;
- Open e-mails from unknown senders and extract the e-mail attachments;
How to remove this keylogger?
You can remove Invisible Stealth Keylogger with a professional anti-malware program – FortectIntego. It can detect every malicious file and permanently eliminate it. You can also try to remove this program manually (we have provided removal instructions below), but this removal method is not as effective as the automatic one.
How to prevent from getting keyloggers
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
