Baaa ransomware (virus) - Recovery Instructions Included
Baaa virus Removal Guide
What is Baaa ransomware?
Baaa ransomware – a dangerous computer virus that attempts to extort money from computer users
Baaa ransomware stands as a significant threat in the cybersecurity world, renowned for its powerful encryption techniques. It is a derivative of the infamous Djvu family of malware, employing a similar operational approach. The distinguishing feature of this malware is its method of renaming all affected files by adding “.baaa” to them and securing them with the RSA encryption algorithm. Once it infiltrates a system, Baaa ransomware wastes no time, quickly encrypting all accessible files, rendering them unusable for the user.
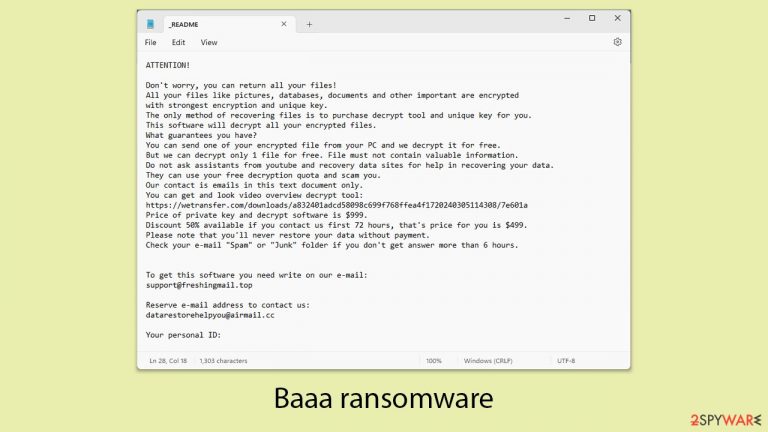
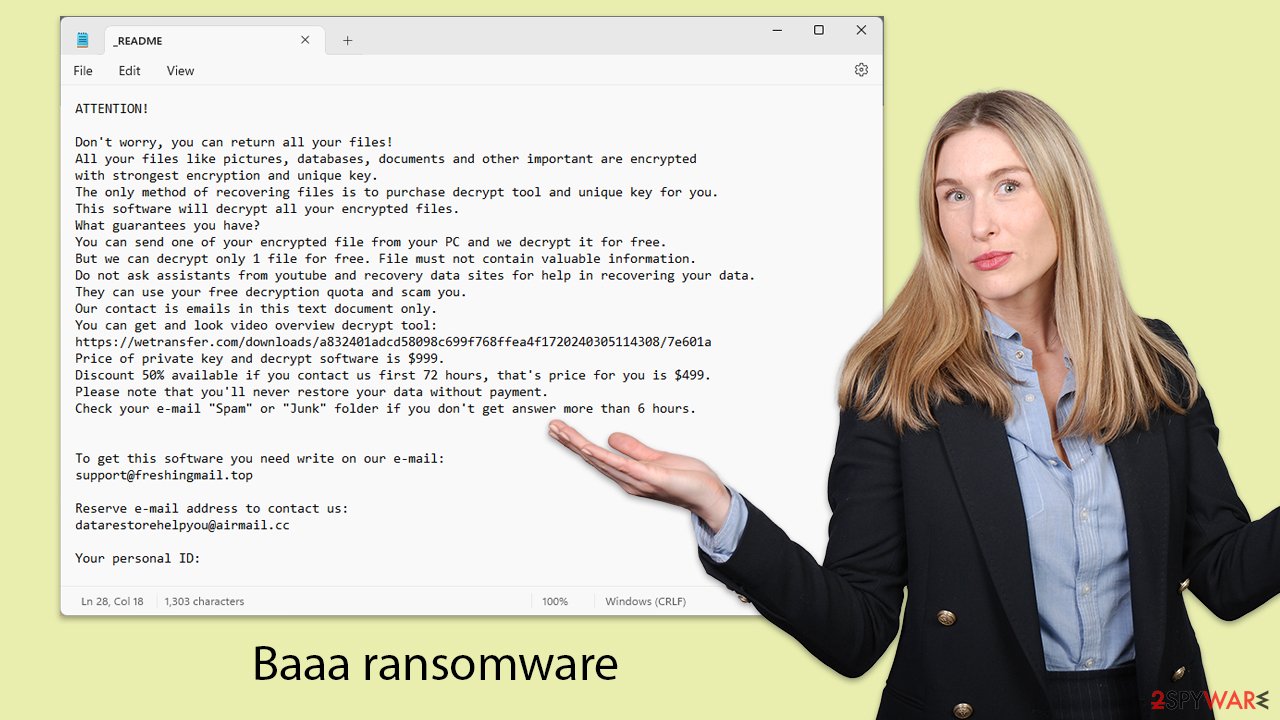
Following the encryption process, the Baaa virus leaves a “readme.txt” file in each affected folder. This note contains urgent messages and outlines the hackers' demands: a ransom of $999 for a decryption key that they claim will restore the encrypted files. However, the note also offers some hope – a 50% discount, lowering the ransom to $499, if the victims reach out within a specified timeframe. To facilitate communication, the ransom note provides two email addresses:
- support@helpmegetmyfilesback.com
- datarestorehelpyou@airmail.cc
This strategy of extorting money highlights a critical vulnerability and has prompted widespread concern among cybersecurity professionals. For further insights into Baaa ransomware, its removal methods, and possible ways to recover data, continue reading the information provided.
| NAME | Baaa virus |
| TYPE | File locker, crypto virus |
| FILE MARKER | .baaa |
| FAMILY | STOP file virus/ Djvu ransomware |
| CONTACT EMAILS | support@freshingmail.top or datarestorehelpyou@airmail.cc |
| RANSOM NOTE | _readme.txt |
| RANSOM AMOUNT | $999/$499 |
| THREAT REMOVAL | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| REPAIR | Upon installation, malware like ransomware can damage essential system files, leading to crashes and errors. To instantly mend such harm, FortectIntego PC repair, an automated solution, can be used. |
The ransom note and what to expect
Baaa ransomware, a member of the Djvu family, is engineered with precision to coerce victims into paying a ransom by encrypting various popular file types such as .jpg, .doc, and .pdf files. It cleverly avoids critical system files, especially executables, allowing the operating system of the affected device to continue functioning. This selective encryption strategy is deliberate, aiming to maintain the device's basic operations while still having a profound impact on the user's data.
Once Baaa ransomware completes its encryption process, it introduces a ransom note on the infected computer. This message is designed to inform the user about the demanded ransom and offers a possible way to recover the locked files. The note typically starts with a direct message to the victim, explaining the situation and the steps needed for potential file recovery. For example, part of such a ransom note could read:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted
with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
Do not ask assistants from youtube and recovery data sites for help in recovering your data.
They can use your free decryption quota and scam you.
Our contact is emails in this text document only.
You can get and look video overview decrypt tool:
https://…a832401adcd58098c699f768ffea4f1720240305114308/7e601a
Price of private key and decrypt software is $999.
Discount 50% available if you contact us first 72 hours, that's price for you is $499.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshingmail.topReserve e-mail address to contact us:
datarestorehelpyou@airmail.ccYour personal ID:
The perpetrators behind Baaa ransomware employ several manipulative strategies to compel victims to pay the ransom. They create a false urgency by promising a 50% discount on the ransom if the payment is made within the first 72 hours. Additionally, they attempt to demonstrate their ability to decrypt the data by offering to unlock one file for free, suggesting that paying the ransom is the sole avenue for full data recovery.
However, succumbing to their demands rarely ensures that the decryption tool provided will work as promised, and it may not lead to the recovery of all encrypted data. Moreover, paying the ransom further emboldens these cybercriminals, fueling the continued spread of ransomware attacks.
How to remove Baaa ransomware?
Discovering that your personal files have been locked by ransomware like Baaa can be extremely distressing. This ransomware targets a broad spectrum of personal data, from irreplaceable family photos to crucial work documents, exploiting the deep sentimental and practical importance these files hold for their owners. However, immediately giving in to the attackers’ demands is not advisable. Consider these steps for remediation instead.
Firstly, it’s essential to remove the ransomware from your system. While Baaa ransomware may self-delete after encrypting your files, it could have also installed additional malicious components that continue to pose a threat.
Use comprehensive anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes to thoroughly clean your system of ransomware and any hidden malicious traces that might have been overlooked. With FortectIntego, you can also repair any system damage that could have occurred, stopping any technical issues occurring post-malware removal.
Sometimes, certain types of malware can interfere with your security software. If you encounter this issue, try running your anti-malware software in Safe Mode. Safe Mode offers a controlled environment that minimizes potential disruptions during the malware removal process (instructions for entering Safe Mode are provided below).
How to recover .baaa files?
After removing the ransomware, you might still experience some system irregularities, such as frequent crashes or errors, due to the damage caused by the ransomware. To address these issues, consider using a reliable system repair tool. These tools can efficiently fix system inconsistencies, providing a simpler and quicker resolution than undertaking a complete reinstallation of your operating system.
Recovering your encrypted files without yielding to the demands of cybercriminals marks the final step in overcoming this cybersecurity ordeal. For those not well-versed in ransomware mechanics, it might seem that a simple antivirus scan could resolve the issue, or worse, that recovery of encrypted files is impossible. Both notions are incorrect.
Here are several effective methods for data recovery:
- Using backups to restore your files is the most dependable method, provided you have been maintaining up-to-date and regular backups.
- There are specialized tools designed to scan your hard drive for lost or damaged files, which may include those affected by the ransomware.
- While not always universally effective, specific decryption tools tailored for particular ransomware strains can be a valuable resource. Although originally designed for Djvu ransomware victims, similar tools for other strains may also exist and are worth exploring.
It's recommended to start with available decryption tools. Obtain the tool from a credible source, launch it, and follow the instructions provided. The primary function of this tool is to attempt file decryption. Depending on whether decryption keys are available and compatible with your encrypted files, you might experience complete success, receive a key unavailability error, or encounter issues due to files being encrypted with an online ID, which might make decryption challenging.
If decryption attempts are unsuccessful, do not lose hope. Turn to professional data recovery software. After installing such software, perform a thorough scan and follow the steps to attempt to recover your files.
Thanks to ongoing efforts by cybersecurity experts and law enforcement, new decryption tools often become available after the dismantling of ransomware campaigns. Regularly check official resources for updates on these tools to stay informed of new developments in decryption technology.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you need more detailed instructions on the mentioned recovery methods, please check out the information below.
Getting rid of Baaa virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
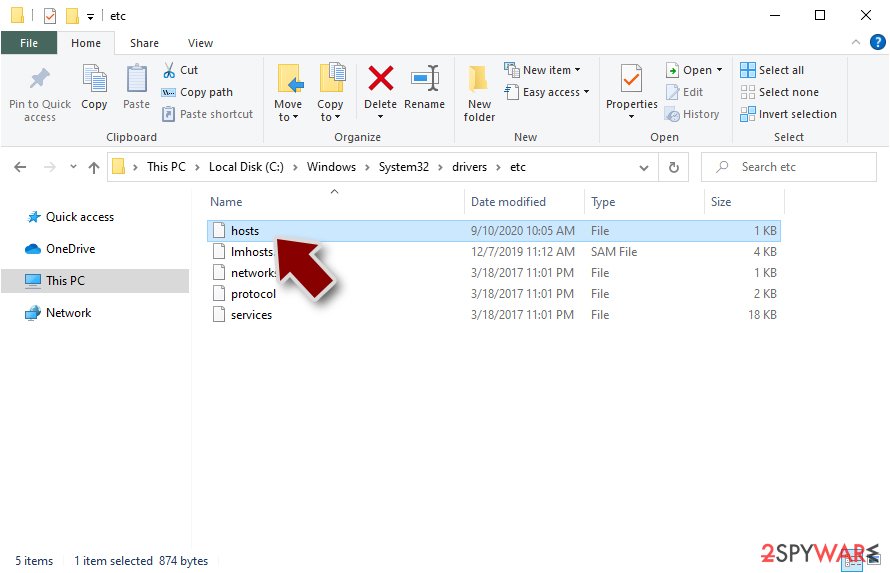
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
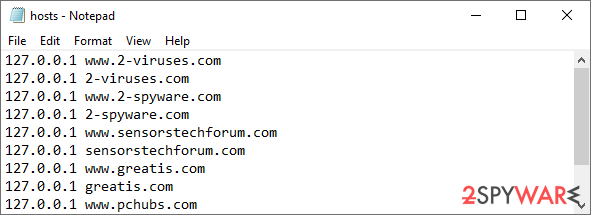
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Use Emsisoft decrytor for Djvu/STOP
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
