Js Miner (Removal Guide) - Free Instructions
Js Miner Removal Guide
What is Js Miner?
Js Miner is the tool used by cryptojackers who try to get money easily without directly involving victims
Js Miner is a crypto miner that can be used by website owners to monetize on visitor's computer power (CPU and GPU). It uses JavaScript[1] code to mine Monero whenever users visit the targeted website. Unfortunately, bad actors learned how to misuse coin mining codes and inject them into sites illegally, without letting users know. This can significantly impact anyone infected with a trojan[2] – slowdowns and crashes of the machine are common, as well as overall performance drops dramatically. The malware has multiple versions and mainly spreads via malicious websites.
| SUMMARY | |
| Name | Js Miner |
| Type | Trojan Horse, malware |
| Sub-type | Crypto-miner |
| Variants |
|
| Symptoms | Majorly increased CPU and GPU usage; slowdowns, crashes or freezes of the PC |
| Distribution | Malicious or infected websites, spam emails |
| Main dangers | Can lead to hardware wear and tear, other malware infections, stolen sensitive information |
| Elimination | Download and install an anti-malware tool that can provide a proper scan and system check |
| Repair | The system can be affected further, so it is required that you run FortectIntego for repair purposes and recover the performance |
Unlike legitimate coin miners, JS:Miner virus affects the machine every time it is booted. As soon as the malicious payload is executed on the targeted computer and files dropped into AppData, Temp, Windows and other folders, the virus performs modification of certain settings, as well starts to schedule tasks with administrative rights without your permission. Without a doubt, the proper virus removal is necessary, as prolonged functioning may destroy your computer hardware.
As soon as malware embeds itself onto the machine, it can emit the following symptoms:
- Highly increased CPU and GPU usage (over 70%);
- Constant freezes or/and crashes;
- Software malfunction;
- Low computer performance, etc.
It is essential to recognize these symptoms and not confuse them with hardware malfunction or computer aging. For that, you should perform a computer scan with Malwarebytes, SpyHunter 5Combo Cleaner, or other reputable anti-malware software. It can instantly determine if your machine is infected.

Money is the biggest motivator for any malicious actor
The primary interest of cybercriminals is to infect as many computers as possible – connecting all the infected machines into one mining pool.[3] As the number of affected computers increases, so does the generation of the desired cryptocurrency, resulting in more profits to hackers (more tokens are received into the same mining wallet in a shorter timeframe).
In some cases, the virus can operate on the targeted machine fileless, and use the browser instead. This increases malware's persistence and allows it to update itself automatically, or even create copies of itself. Thus, it can operate even if you delete JS Miner's main executable manually. That is why security software is so significant – it can detect all the components hiding deep within the system files.
Apart from mining digital currency, malware is also capable of stealing personal information (such as credentials), logging keystrokes, harvesting system, network, and software information, and even take screenshots of the desktop. Without a doubt, you should remove JS:Miner as soon as you notice anything suspicious, as hackers may steal your money or even identity, as well as destroy the operation of your machine.
Versions of the known miner
There many variants of the virus, but the most prominent ones are JS:Miner-C and JS/CoinMiner. So far, security experts have detected the following types:
- JS:MINER-A
- JS:MINER-B
- JS:MINER-C
- JS:MINER-D
- JS:MINER-E
- JS:MINER-F
- JS:MINER-G
- JS:MINER-H
- JS:MINER-I
- JS/CoinMiner
The main goal of all these viruses is to secretly mine cryptocurrency on the targeted machine. However, some variations have distinctive features.
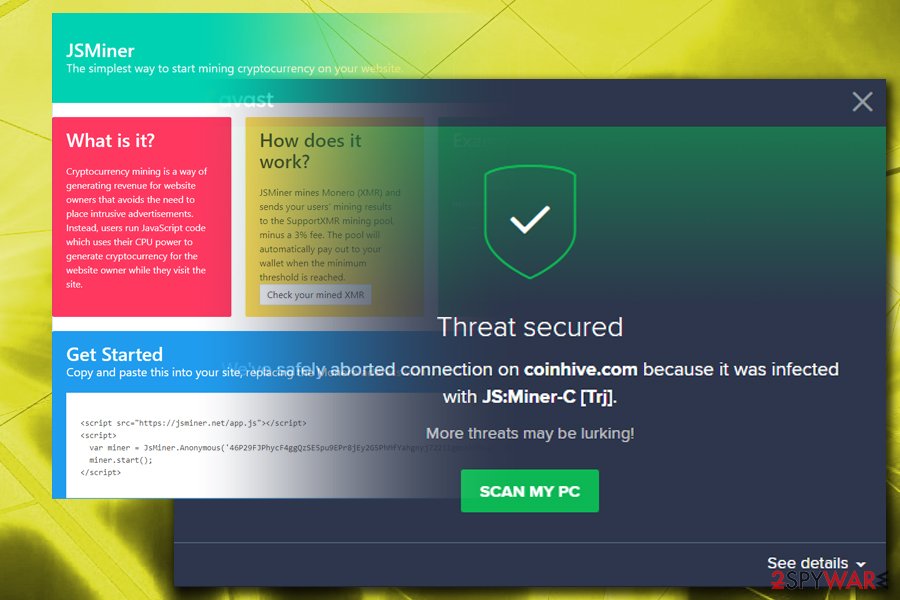
JSMiner-C
JSMiner-C is the most popular type that is injected into users' machines. The malware utilizes graphics cards and the central processing unit's power to run the crypto-mining activities. At the time of the operation, the fans on the PC run high, and it can become extremely hot. Unfortunately, it is sometimes impossible to determine the CPU usage as it is not shown in the Task Manager. We suggest users downloading and installing third-party software (Like CPU-Z or Core Temp) which is capable of detailing the workload on each hardware component.
JS/CoinMiner
This version also uses JavaScript to contaminate machines. It is relatively similar to other malware variants, except that it does not display other signs and symptoms, apart from increased CPU and GPU usage. JS/CoinMiner tries to avoid detection for as long as possible and mine crypto silently. Additionally, this variant can enable other viruses to enter computers unnoticed and conceal the infection deep within the system. The cure for this cyber threat is anti-malware tools, just as it is the case with other variants.
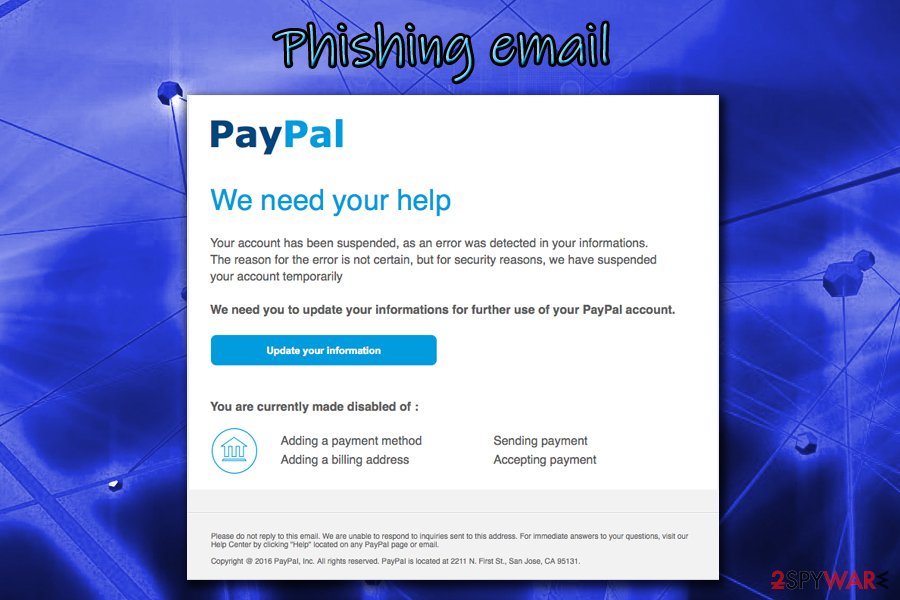
Infiltration techniques used by malware creators
Trojan horses are the sneaky type of viruses and have multiple distribution methods. One of the most prominent ones is via contaminated spam email attachments. If you are the one who opens every single email thrown at you – beware, you can infect your computer in just a few clicks. Especially if you open files attached to phishing emails, thinking it is legitimate. Please be careful, as cybercrooks use clever social engineering to trick victims and make them click on the contaminated link or malicious .txt, .pdf, .doc, or similar files. An example of a phishing email:
Claim Your Tax Refund Online
Dear Taxpayer,
We identified an error in the calculation of your tax from the last payment amounting to $319.95. In order for us to return excess payment, you need to create a e-Refund account after which the funds will be credited to your specific bank account.
Please click “Get Started” below to claim your refund:
Get Started
Always question every email, even if it looks legitimate. In most cases, your email provider will mark suspicious emails as spam, so do not ignore these warnings.
Additional ways trojans can get into your machine are:
- via suspicious or hacked websites;
- file-sharing or torrent sites;
- repacked or cracked software or any other executables;
- fraudulent links and malicious ads
- fake updates, etc.
Get rid of Js Miner using powerful security software
Trojan horses are particularly malicious and often use a complicated code (as we already mentioned, some variants can persist on the system even if the main executable is not present). Thus, trying to remove Js Miner virus manually is not a good idea and should only be performed by individuals with sufficient IT skills.
Therefore, cybersecurity experts[4] advise users to opt for automatic JS:Miner removal. Merely download Malwarebytes, SpyHunter 5Combo Cleaner or other reputable anti-malware software, bring it up to date and run a full system scan. As trojans may disable security programs from functioning normally, you should enter Safe Mode with Networking, as explained below.
Getting rid of Js Miner. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Js Miner using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Js Miner. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Js Miner and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Jay Sridhar. What Is JavaScript and How Does It Work?. MakeUseOf. Technology website.
- ^ Margaret Rouse. Trojan horse (computing). SearchSecurity. Cybersecurity information.
- ^ Anton Ivanov, Evgeny Lopatin. Mining is the new black. SecureList. Security researchers.
- ^ BedyNet. BedyNet. Russian cybersecurity site.





















