JSMiner-C (virus) - 2021 update
JSMiner-C Removal Guide
What is JSMiner-C?
JS:Miner-c is a dangerous cryptocurrency miner lurking in the cyberspace
JS:Miner-c is a term that is used by antivirus programs to identify a dangerous Trojan horse virus. This cyber threat possesses a wide range of capabilities, including secretly mining cryptocurrency (Monero, Bitcoin, etc.) on targeted machines, track and record personal and technical information, or even serve as a backdoor to various other malware. Experts categorize this infection as similar to Minergate virus as both of them can not only damage computer systems but infiltrate with other cyber threats as well. Thus, it vital to get rid of the infection promptly.
| Name | JS:Miner-C |
|---|---|
| Type | Trojan horse |
| Main activities | Mining of Monero and similar types of cryptocurrency |
| Symptoms | Extremely high CPU and GPU usage |
| Distribution | Spreads as malicious email attachments, or is disguised as legitimate software on P2P sites |
| Removal | You can get rid of the miner and similar cryptocurrency-focused threats with anti-malware tools |
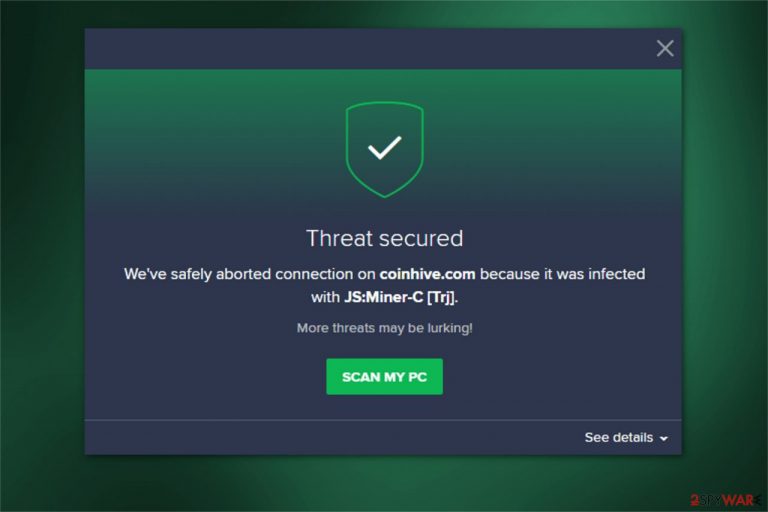
If you wonder what is JS:Miner-c, this is merely a name for the infection used by antivirus systems to warn users. At the moment, you can receive an alert with such a name from Avast. The term refers to the crypto-mining malware designed to redirect users to infected websites which are misusing the legitimate script from Coinhive — Monero JavaScript miner. According to Coinhive's Terms of Use, authors of the site MUST warn users about mining. However, it is more than obvious that hackers behind the trojan virus are not going to do that.
Have in mind that JS:Miner-c will never lead you to trustworthy sites. In fact, they cannot only use your computer's power to mine cryptocurrency but can also infect your system with the following potentially unwanted programs (PUPs) and other dangerous malware:[1]
- Browser hijackers;
- Adware-type applications;
- Ransomware;
- Trojan horses.
Note that once you enter a bogus website, it will use excessive amounts of CPU power while the page is open. The temporary way to stop the site from misusing your computer's resources is to close it immediately. However, this will not remove JS:Miner-c from your system which is the primary cause why you are redirected to such websites.

If you ignore JS:Miner-c Avast detection, there are numerous computer-related issues you may face. High CPU usage forces your computer to work at high temperatures for long periods of time. Likewise, after some time you will first notice a significant decrease in your PC performance, along with increased electricity bills.
Also, be aware that mining cryptocurrency usually takes up to 100% of CPU[2] and there are no resources left for performing other vital system processes. As a result, your programs will crash or it will take a lot of time for them to load. Moreover, you might face other issues related to the virus as well:
- Continuous freezes;
- Slowdowns;
- Sluggish system.
For all the reasons mentioned above, we strongly suggest you remove JS:Miner-c from both, Mac and Windows operating systems. You can employ professional security software, like SpyHunter 5Combo Cleaner or Malwarebytes.

Additionally, we would like to warn you that successful threat removal requires you to get rid of all its malicious components. Since this malware has adware-like features, it is vital to delete all suspicious entries from your browsers. Instructions on how to do that are also provided at the end of this article.
Beware of suspicious emails and dubious sites
One of the most prominent malware distribution methods is malicious attachments or links inside a phishing email. Bad actors often employ bots that are capable of sending thousands of emails to innocent users. Therefore, it is vital to recognize a scam email by the following signs:
- grammar or/and spelling mistakes present;
- the author presents himself as a representative of a high profile organization;
- the “From” address is not genuine (even if it might look so at first glance);
- attachments (such as .zip, .rar, .pdf, .doc, .html) or cleverly hidden hyperlinks present.
Thus, carefully check the message before proceeding with any actions. Another way to prevent malware would be scanning the attachment before opening it.
Furthermore, Monero miner can also be distributed via malware-laden ads which look incredibly genuine. Likewise, you must not only monitor the software installation procedure but also pay close attention when browsing the Internet.
We suggest you stay away from all types of ads you can encounter online. Note that developers aim to make them look genuine and trick credulous people into clicking on them (for example, the malicious pop-up might be disguised as fake update). Unfortunately, most of the time you might either fall into the trap of scammers who are offering fake and expensive products or manually infiltrate malware.
You can uninstall JS:Miner-c with an antivirus software
If you consider whether the removal is necessary, we can assure you that this is the only way to protect your computer's well-being. Note that this malware not only deteriorates it performance but it can also infiltrate the system with other potentially dangerous infections. Thus, get rid of it as soon as possible.
For that, we strongly recommend employing one of the antivirus tools mentioned below. They are designed to help you eliminate various potentially unwanted programs with a few clicks. Thus, this is the easiest way to get rid of JS:Miner-c virus. However, feel free to use any other malware removal tool of your choice.
LosVirus.es[3] team warns that users should remove the virus manually, at will most likely fail and can damage the compromised system even more. Rely on SpyHunter 5Combo Cleaner, Malwarebytes for the job. Also, trust FortectIntego fr the help of cleaning the system.
Getting rid of JSMiner-C. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove JSMiner-C using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of JSMiner-C. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from JSMiner-C and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. How-To Geek. We Explain Technology.
- ^ James Frew. What Is A CPU and What Does It Do?. MakeUseOf. Technology, Simplified.
- ^ LosVirus. LosVirus. Security and Spyware News.







