JS/ScrInject.b (Easy Removal Guide)
JS/ScrInject.b Removal Guide
What is JS/ScrInject.b?
What should you know about JS/ScrInject.b virus?
JS/ScrInject.b virus is a new threat in the category of Trojan viruses. Similarly to other Trojans, such as Trojan.ZeroAccess or 12Trojan.Win32.Krepper.ab, this malicious program enters computers along with other malware programs. Of course, the JS/ScrInject.b hijack occurs stealthily, so the user has no idea about the infiltration. This way, the Trojan can secretly carry out its activities in the background of the system. The security experts warn that JS/ScrInject.b can bring serious damage to the infected computer by targeting its defense system. It goes without saying that this program should be terminated immediately. However, Trojans are usually very well hidden deep in the computer’s system, so there is little change you will be able to detect and remove JS/ScrInject.b by yourself. For this purpose, it is advisable to use professional antivirus software, such as FortectIntego, and run a thorough system scan with it.
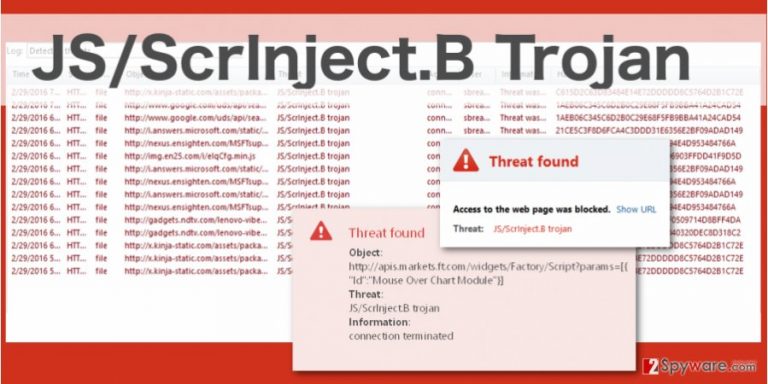
Essentially, JS/ScrInject.B Trojan works as a gateway for other viruses to enter the computer. It may install additional adware, browser hijackers and other viruses which significantly slow down the system’s performance, causing a variety of errors and malfunctions. Eventually, because of the heavy CPU and RAM load, the PC’s defense mechanisms will fail. If the Trojan manages to stay in the computer’s system long enough, it may redirect the infected computer to some remote server, easily handing down the access of your system to the online criminals. It is not surprising that these hackers will do their best to extort as much benefit out of this opportunity as possible. They may install cookies to track your online purchase information, login details used for e-banking and use this data for commercial purposes, or to steal your money. It is undeniable that JS/ScrInject.B removal is inevitable if you want to keep using your computer safely and uninterruptedly.
How can this Trojan infiltrate your computer?
As mentioned before, the JS/ScrInject.b Trojan can infiltrate the computers along with other malware. It can be achieved via deceptively spreading malicious programs in software packages together with popular and frequently obtained programs. Such infectious software packages can be encountered on obscure software download sites, downloaded by clicking on pop-up ads displayed on some untrusted sites and received as a file attached to a spam email. Since there are a lot of ways you can get infected with the JS/ScrInject.b virus, you have to take care of the thorough system protection. Obtaining reliable antivirus or anti-malware tools is the fundamental step towards a guaranteed system security. Also, it is worth reconsidering your browsing habits and make sure you stay away from suspicious content you may come across on the web.
JS/ScrInject.b Trojan. How to remove?
If you suspect your computer could have been infected with JS/ScrInject.b Trojan, you should get rid of it immediately. Your personally-identifiable information, system files, and computer’s security may be at stake if you do not do that in time. You may remember that manual JS/ScrInject.b removal is a rather difficult process as the virus is hidden deep in the computer’s system. Not to waste your time, we advise you to use reliable anti-malware software to remove JS/ScrInject.b virus from your device quickly and effectively.
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
