KEYPASS ransomware (Removal Guide) - Updated Guide
KEYPASS virus Removal Guide
What is KEYPASS ransomware?
KEYPASS ransomware – a dangerous cryptovirus that infiltrates systems via fake software installers

KEYPASS ransomware is a dangerous cryptovirus that belongs to the family of STOP ransomware. Once installed, it makes changes to the Windows Registry to gain boot persistence. That makes its removal a bit more difficult but possible with proper anti-malware software.
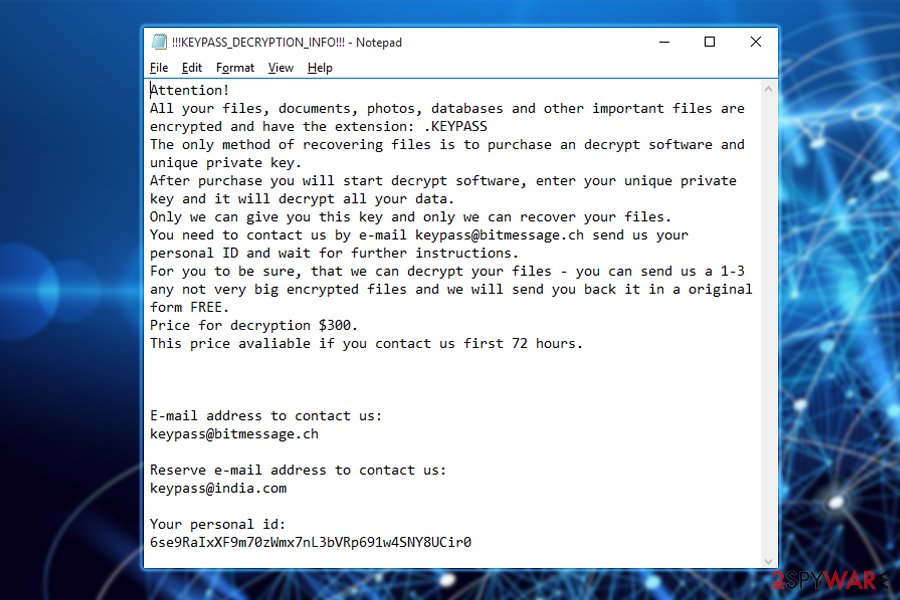
The malware uses AES-256 cipher to encrypt files and adds a .keypass extension. Additionally, the virus connects to its C&C servers to receive the encryption key and make user's files useless without it. Victims are informed about this attack via the !!!KEYPASS_DECRYPTION_INFO!!!.txt ransom note that requires a $300 ransom in Bitcoin in exchange for the decryptor for the locked data.
The victim receives 72 hours to pay this fee. For that, users need to contact the cybercriminals using a provided email address (keypass@bitmessage.ch). Note that this cryptovirus has nothing to do with the well-known KeePass password management software.
| NAME | KEYPASS |
|---|---|
| TYPE | Ransomware, file-locker |
| RANSOM note | “!!!KEYPASS_DECRYPTION_INFO!!!.txt” |
| Ransom amount | $300 in Bitcoin has to be paid in 72 hours |
| other features | Manual control. Used to customize the ransom note and change the ransom amount, email address, victim ID, etc. |
| DISTRIBUTION WAYS | Spam emails, questionable sources, file-sharing platforms |
| ELIMINATION | Remove any computer virus by performing a full system scan with a trustworthy anti-malware tool |
| System fix | Revert any changes this infection has made to the Registry and other core system settings and files by using the time-proven FortectIntego system repair tool |
KeyPass ransomware was first discovered by Kaspersky Lab experts on the 8th of August,[1] and infection submissions came from over 20 countries across the globe, with Brazil and Vietnam being hit the most. As of now, security experts are not sure about how the virus spreads, but several users reported that it appeared after they installed the Windows hacking tool KMSpico. In contrast, others stated that no changes were made before the infection occurred.
This file-locking parasite comes with a hidden feature called “Manual control”. It can only be activated by using a specific key combination that allows hackers to take manual control[2] of the virus. This allows them to modify the victim's ID, file extension, encryption key, and several other preferences related to the file encryption process.
Security experts also noticed that in the Command & Control server is not reachable or the infected device is not connected to the internet, the malware uses a hard-coded key, which makes the ransomware removal and file retrieval a much easier task.
However, if the computer is connected to the network, the virus does not only encrypts your regular personal files like pictures, databases, documents, and similar but instead skips a few folders on the machine, allowing the system to boot properly. After the encryption process is complete, most of the files become inaccessible, leaving the device in a complete mess.

The ransom note that is retrieved from the C&C server after the file encryption states the following:
Attention!
All your files, documents, photos, databases and other important files are encrypted and have the extension: .KEYPASS
The only method of recovering files is to purchase an decrypt software and unique private key.
After purchase you will start decrypt software, enter your unique private key and it will decrypt all your data.
Only we can give you this key and only we can recover your files.
You need to contact us by e-mail keypass@bitmessage.ch send us your personal ID and wait for further instructions.
For you to be sure, that we can decrypt your files – you can send us a 1-3 any not very big encrypted files and we will send you back it in a original form FREE.
Price for decryption $300.
This price avaliable if you contact us first 72 hours.
E-mail address to contact us:
keypass@bitmessage.ch
Reserve e-mail address to contact us:
keypass@india.com
Your personal id: –
While the ransomware virus developers demand a $300 ransom, the payment type is not mentioned. However, hackers usually rely on digital currency (Bitcoin, Monero, Litecoin, etc.) for all the transactions. This way, money transfers remain anonymous and prevent law enforcement from tracking and punishing scammers.
Nevertheless, we do not recommend contacting cyber criminals, as the chance of retrieving the key is quite low. Additionally, it might encourage bad actors to improve the malware code and increase the number of infections. Thus, better take care of the ransomware by using anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes, and then recover your files from a backup.

Unfortunately, this malware can also be used as a backdoor for other infections, such as banking trojans and other malware forms[3]. We recommend you not to wait and get rid of the virus as soon as possible, as the infection chance increases the longer you wait.
Remember, your computer and data safety is in your own hands. Better prepare for such attacks in advance – keep important files safe and on a USB stick or an external HDD. If you are already infected with Keypass ransomware and have no backups ready, you could try third-party software that could help you to recover your data. See instructions below.
But before proceeding with file recovery, either from backups or by using recovery software, users should take care of their device's overall health. This ransomware causes havoc on system files, which can lead to various abnormal behavior. Use the FortectIntego system repair tool to take care of all system inconsistencies automatically.
Keep your PC safe from ransomware by following safety tips
According to UdenVirus.dk specialists[4], ransomware usually has one main distribution source – spam emails. Cybercriminals take action and send numerous phishing messages to accidental users. Once received, such messages can be found in the Spam section (however, phishing emails might slip through the built-in scanners and get into your Inbox instead). If you encounter this type of content – better eliminate it permanently to avoid severe computer infections.
We advise increasing your PC safety by running an antivirus program[5] on your computer. If you do not already have one, you should consider downloading a trustworthy one. Such anti-malware software will keep your machine secured from various infections if kept up-to-date as required.
Get rid of the dangerous infection with the help of our removal guides
To remove this hazardous virus, you need to run a full system scan with a reliable anti-malware program and get rid of every component of this ransomware. Experts recommend using such tools as SpyHunter 5Combo Cleaner or Malwarebytes. Of course, you can pick another trustworthy anti-virus of your liking, but make sure it is up-to-date.
The elimination might take a while, but it is critical to get rid of the cyber threat as fast as possible to avoid further damage. Afterward, to complete the removal process by restoring your Registry, host files, and other essential system files, it's highly recommended to use the FortectIntego system repair tool.
Unfortunately, neither the security software nor the repair tools that we recommend recover data encrypted by KEYPASS ransomware. For that, you should follow the tips given below this article. Finally, to protect yourself from ransomware attacks in the future, keep backups of your most valuable files. For that, use cloud services or external drives.
Getting rid of KEYPASS virus. Follow these steps
Important steps to take before you begin malware removal
File encryption and ransomware infection are two independent processes (although the latter would not be possible without the former). However, it is important to understand that malware performs various changes within a Windows operating system, fundamentally changing the way it works.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. Encrypted data does not hold any malicious code, so it is safe to transfer to other devices.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Repair damaged system components
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstall is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
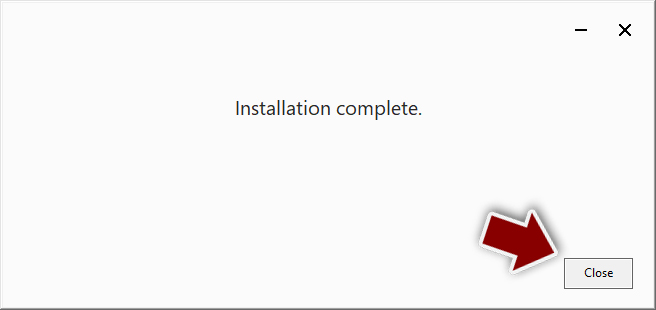
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing FortectIntego, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
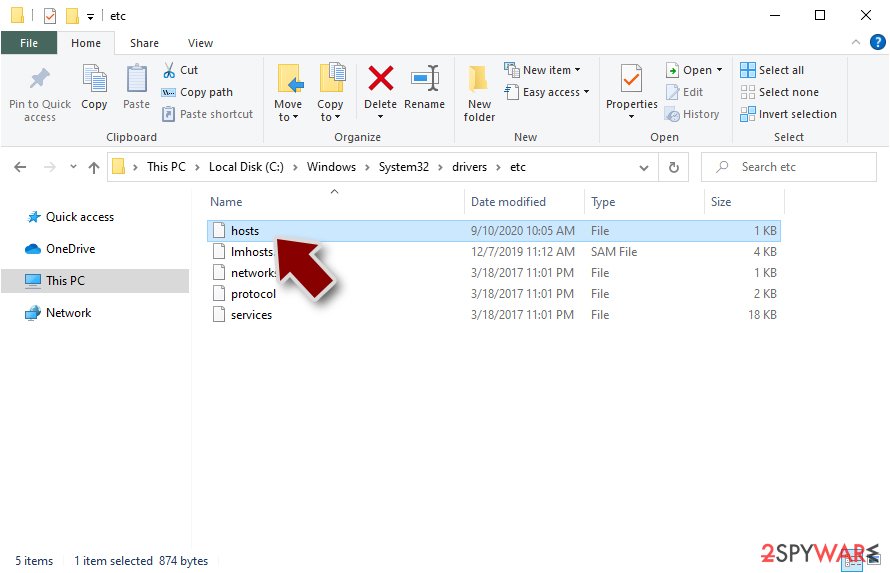
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
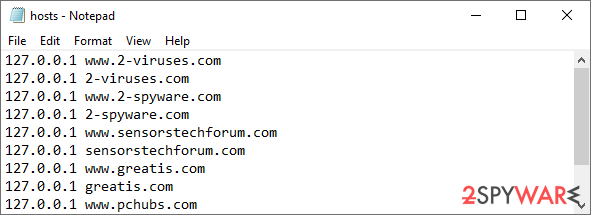
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
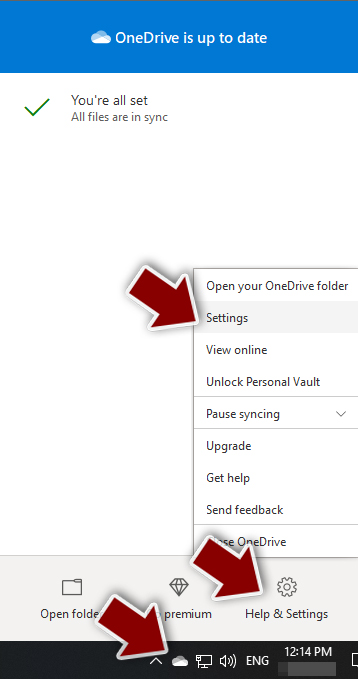
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.

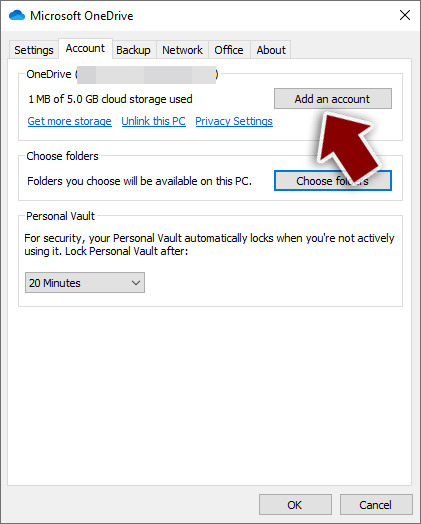
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.

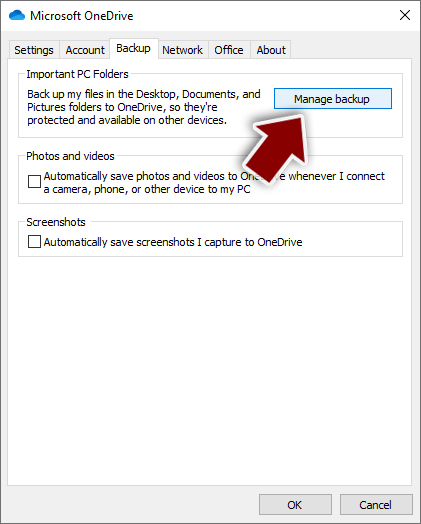
- Once done, move to the Backup tab and click Manage backup.

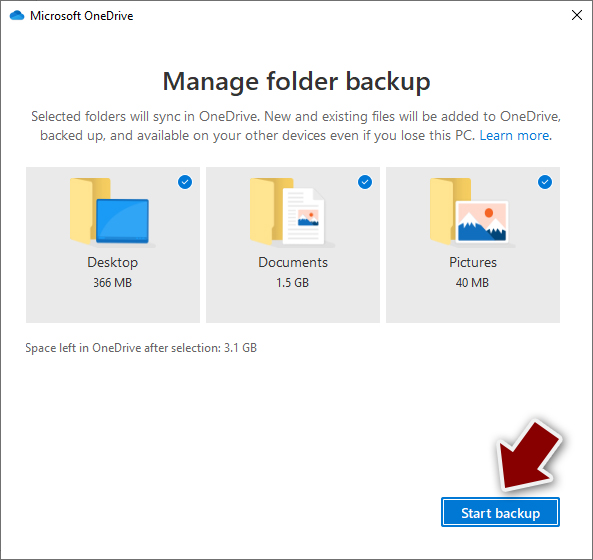
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.

After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
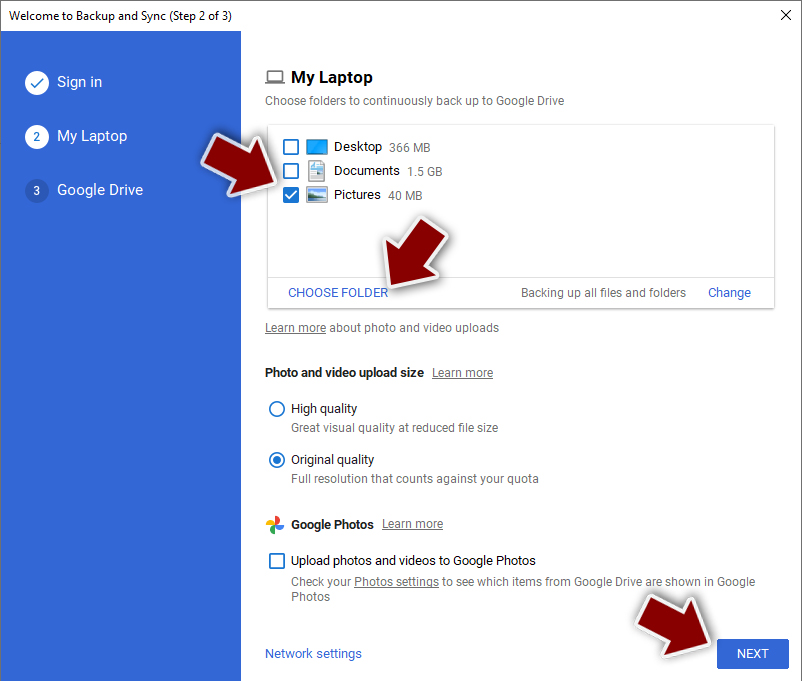
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
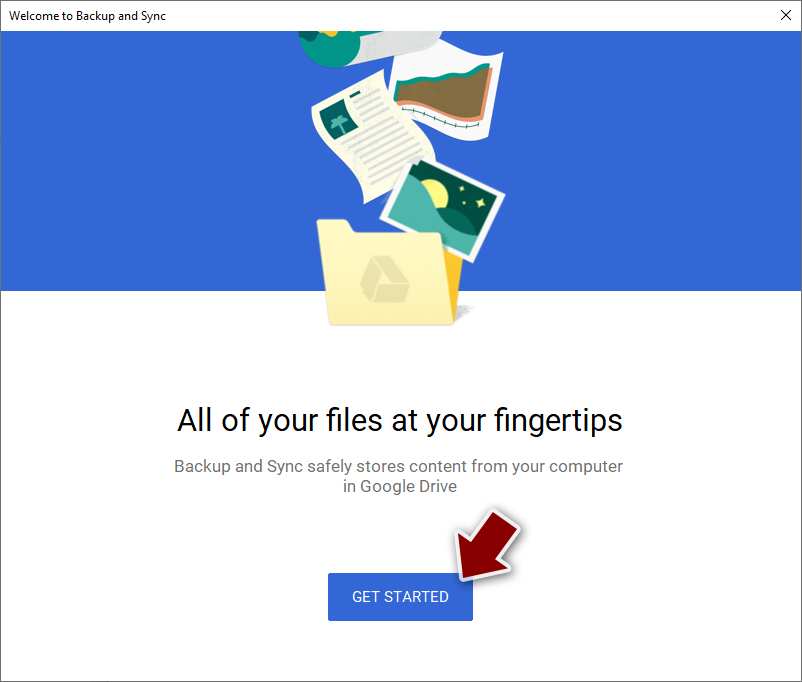
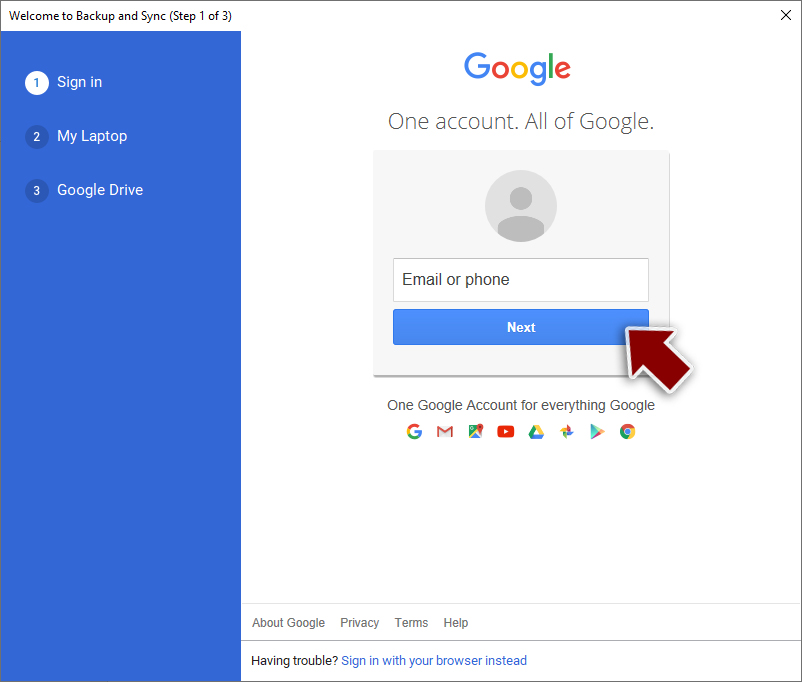
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.

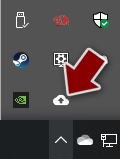
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.

- Click Get Started.

- Enter all the required information – your email/phone, and password.

- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.

- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from KEYPASS and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Orkhan Mamedov, Fedor Sinitsyn. KeyPass ransomware. SecureList. Kaspersky's security blog.
- ^ Lucia Danes. Hackers employ KeyPass ransomware for manual attacks. 2-Spyware. Cybersecurity news and articles.
- ^ Roger A. Grimes. 8 types of malware and how to recognize them. CSO. From IDG.
- ^ UdenVirus. UdenVirus. Removal guide.
- ^ Antivirus software. Wikipedia. The free encyclopedia.