Koler ransomware / virus (Removal Guide) - Nov 2017 update
Koler virus Removal Guide
What is Koler ransomware virus?
Koler ransomware attacks Android users in USA to gain illegal profits
Koler virus is a dangerous ransomware with a screen-locking function. This Android virus version blocks the access of the target device and insists its owner on paying a ransom. To reset the tablet or phone to its primary stage, the fee must be paid via One Vanilla prepayment system.
Unfortunately, there is a significant increase in the distribution of this virus over the past several months in USA and other countries. You can encounter this mobile ransomware[1] masquerading as a Pornhub application which the visitors of adult-themed websites are offered to install when trying to view certain content.
Experts believe that Koler is merely an Android OS adaptation of the infamous Windows ransomware virus called Reveton which has been locking computers since 2014. Three years have passed since then but the virus creators are still hoping to catch their victims on the same bait.
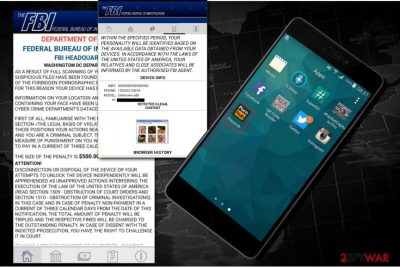
When the app is installed, it automatically takes over the administrative privileges to change the PIN code of the device and drops an official-looking lockscreen claiming that FBI blocked the device because of the illegal activity on the device.
The message is very similar to the one that Reveton was using back in 2014. The full message reads:
As a result of full scanning of your device, some suspicious files have been found and your attendance of the forbidden pornographic sites has been fixed. For this reason your device has been locked. Information on your location and snapshots containing your face have been uploaded on the FBI Cyber Crime Department’s data center.
First of all, familiarize with the positions stated in the section “The Legal Basis of Violations”. According to these positions your actions bear criminal character, and you are a criminal subject. The penalty as a base measure of punishment on you which you are obliged to pay in a current of three calendar days is opposed. The size of the penalty is $500
Attention! Disconnection of disposal of the device or your attempts to unlock the device independently will be apprehended as unapproved actions interfering the execution of the law of the United States of America (read section 1509 – obstruction of court orders and section 1510 – obstruction of criminal investigations).
In this case and in case of penalty non-payment in a current of tree calendar days from the date of this notification, the total amount of penalty will be tripled and the respective fines will be charged to the outstanding penalty. In case of dissent with the indicted prosecution, you have the right to challenge it in court. To make a penalty payment, go to section “Payment Penalties”.
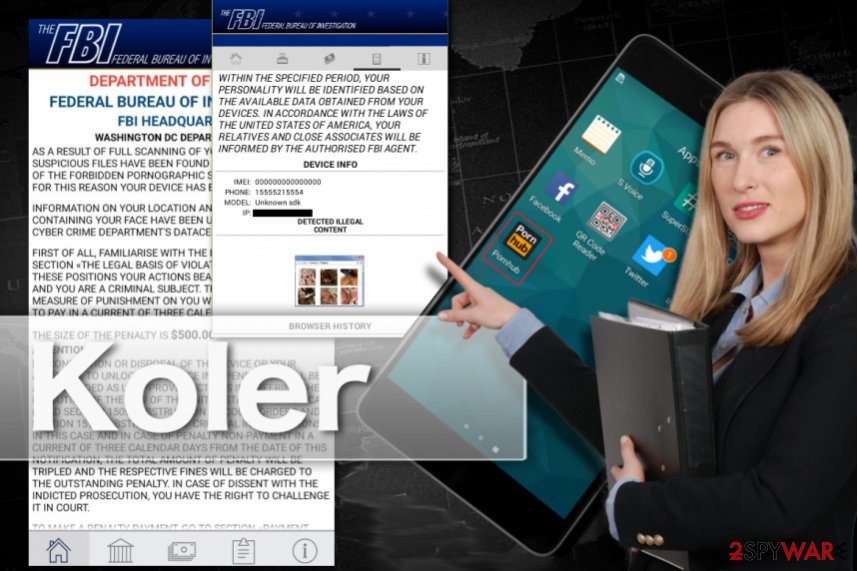
This message is a good example of malicious social engineering[2] used to scare the victim and prevent Koler removal from the system. The extortionists employ well made up scare tactics to make victims pay the 500 dollar ransom via One Vanilla card which doesn't require to submit personal details.
While Windows versions of this virus were aimed at individual countries and altered their ransom notes depending on PC's location[3], this malware seems to be aimed purely at US users, hence the FBI theme.
If you live in the US and have become a victim of clickjacking, make sure you remove Koler from PC without delay. After you perform the elimination with the help of mobile antivirus software like FortectIntego or manually, you should be able to access your files again.
Understanding methods used by this Android virus to spread around
As we have mentioned, researchers spotted Koler malware spreading as a fake PornHub app. Links to this app were spotted in adult-related sites. When dealign with this scam, Android users have no idea they are downloading a ransomware-laden Trojan on their devices. The first understanding that they are infected shakes them only after they start seeing the fake FBI alert on their screen.
Experts share the list of some links that have already been discovered to download Koler virus:
-
http://wywax7ljbf.privatehardvideohotgirl.pw/9/pornhub.apk;
-
http://wywaxweypv.greathardvideoblondegirl.pw/10/pornhub.apk;
-
http://wmwxwqgvhy.privatehardvideohotgirls.pw/9/pornhub.apk;
-
http://wycaq6ygea.greathardvideohotgirl.pw/9/pornhub.apk;
-
http://wmsqapmrdl.greathardvideohotgirls.site/9/pornhub.apk;
-
http://wmwqcabay6.privatehardvideohotgirl.site/9/pornhub.apk;
-
http://whsaalu7lt.greathardvideohotgirl.site/9/pornhub.apk;
-
http://whwqccw4gu.wonderfulhardvideohotgirl.pw/9/pornhub.apk;
-
http://cysqqoitia.greathardvideohotgirl.site/9/pornhub.apk;
-
http://chcxq6fq5n.excellenthardvideohotgirls.site/9/pornhub.apk;
-
http://wycxqkxspa.excellenthardvideohotgirl.pw/10/pornhub.apk;
-
http://wycxqkxspa.excellenthardvideohotgirl.pw/10/pornhub.apk;
-
http://wmwqq4uxtb.besthardvideohotgirls.pw/9/pornhub.apk;
-
http://wmwqwvxml6.beautifulhardvideoidealbrunettegirl.site/9/pornhub.apk;
-
http://wmsaq7seyx.greathardvideohotgirls.pw/9/pornhub.apk;
-
http://wmsaqpka4i.privatehardvideohotgirl.pw/9/pornhub.apk;
-
http://chcxxodmpp.excellenthardvideohotgirls.site/9/pornhub.apk;
-
http://smwaa7bhv6.greathardvideohotgirls.site/9/pornhub.apk;
- http://cmwawrkmmb.besthardvideoidealbrunettegirls.pw/9/pornhub.apk.
Experts have a few suggestions what can be changed to avoid similar incidents in the future
First of all, you should avoid visiting shady websites that may be potentially harmful to your PC. If you happen to land on such pages purposefully or by accident, you should not interact with any ads, links, pop-ups or similar content displayed there. Make sure you leave these sites immediately.
Also, DO NOT open .exe files if they get automatically downloaded on your PC or device. Put them into Trash without checking what's inside them.
And finally, make sure you always have the protective shields on and that your security software is running the latest version. If it is not updated automatically, make sure you download the latest updates every couple of days.
Do not hesitate to get rid of Koler virus
You can start Koler removal immediately — reboot your gadget to a Safe Mode and eliminate administrative right for suspicious applications that might be related to the virus. Afterwards, uninstall PornHub app from your device by putting it into Trash. Here is a step-by-step guide to help you with this task:
- Find the power button on your phone or tablet and press it for a couple of seconds until you see a menu. Tap the Power off.
- Once you see a dialog window that offers you to reboot your Android to Safe Mode, select this option and OK.
If this failed to work for you, just turn off your device and then turn it on. Once it becomes active, try pressing and holding Menu, Volume Down, Volume Up or Volume Down and Volume Up together to see Safe Mode.
When in Safe Mode, you should finish Koler ransomware removal by uninstalling the malicious app:
- Reboot your device into Safe Mode with the help of steps that are given above.
- When in Safe Mode, go to Settings. Once there, click on Apps or Application manager (this may differ depending on your device).
- Here, look malicious app (PornHub and other apps that look suspicious) and uninstall all of them.
We also recommend turning off the option allowing installing apps that belong to unknown sources. For that, go to Settings -> Security. Once there, turn off this option.
After you are done with these steps, Koler virus should be gone from your device. To make sure you won’t have to remove Koler in the future again, you should obtain a reputable mobile antivirus software. Just to be safe, you should also create backup copies of important files from your device.
Getting rid of Koler virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Koler using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Koler. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Koler and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Doros Hadjizenonos. Ransomware – not only file encryption. ITnewsAfrica. IT, news, Telecom news, Mobile news, Technology news, Gadgets news, analysis and reports.
- ^ Wendy Zamora . Hacking your head: how cybercriminals use social engineering. MalwarebytesLabs. The security blog from Malwarebytes.
- ^ Ioys. Ioys. Malware news, reviews and removal guides.





















