MysteryBot virus (Removal Guide) - Tutorial
MysteryBot virus Removal Guide
What is MysteryBot virus?
MysteryBot – a mobile banking trojan that attacks Android 7 and 8 users

MysteryBot is a mobile virus that targets Android users. This advanced Android virus[1] seems to be related to LokiBot malware[2] which has been detected in 2017. However, the recent mobile malware is capable of stealing banking information, operating as a keylogger and contains a ransomware-type virus. The virus spreads as a fake Adobe Flash Player app and after infiltration gets administrative rights of the device. Since then it can perform its malicious activities.
| Summary of the cyber threat | |
|---|---|
| Name | MysteryBot |
| Type | Malware |
| Targeted OS | Android 7 and 8 |
| Features | Banking trojan, keylogger, ransomware |
| Relation | LokiBot malware |
| Distribution | Fake Adobe Flash Player app |
| Elimination | To uninstall MysteryBot, install FortectIntego and run a full system scan |
According to the research data,[3] MysteryBot virus uses the same Command and Control (C&C) server like LokiBot. Researchers assume that it might be an updated version of the latter malware or a brand new cyber threat created by the same hackers.
MysteryBot malware targets mobile devices that run on Android 7 and 8 operating system. The virus uses an advanced overlay attack and employs the Android PACKAGE_USAGE_STATS permission (commonly named Usage Access permission) to steal banking credentials. It also uses AccessibilityService that allows operating without user’s knowledge.
However, MysteryBot is not a regular banking trojan. It has an advanced functionality, and can perform the following tasks on the affected Android device:
- make, stop or forward phone calls;
- access contact list,
- copy, delete and send SMS messages,
- operates as keylogger and copies all used keystrokes;
- encrypt files;
- delete contact information;
- call USSD number;
- steal emails;
- give attackers remote access to the device.
This mobile banking trojan uses a sophisticated keylogging technique to get needed sensitive information. Instead of stealing keystrokes or making screenshots by exploiting Android Accessibility Service, MysteryBot can recognize device’s keyboard:
It considers that each key of the keyboard has a set location on the screen, on any given phone and regardless if the phone is in held horizontally or vertically, it also takes into consideration that each key has the same size and therefore is the same number of pixels away from the previous key. To summarize, it looks like this technique calculates the location for each row and places a View over each key. This view has a width and height of 0 pixels and due to the “FLAG_SECURE” setting used, the views are not visible in screenshots. Each view is then paired to a specific key in such a way that it can register the keys that have been pressed which are then saved for further use. [Source: ThreatFabric]
Researchers tell that this code is still in-dev mode. Therefore, malware might be still improved. In case of the attack, it’s important to remove MysteryBot as soon as possible to avoid serious privacy-related issues. However, this nasty cyber threat might be hard to get rid of. So, you should powerful professional tools like FortectIntego or Malwarebytes and get rid of it automatically.
After MysteryBot removal, it is recommended to change all your account passwords to protect your privacy and accounts from being hacked and used for malicious purposes. Moreover, you should monitor your banking transactions. If you notice some suspicious activity, report your bank immediately.

The MysteryBot virus can operate as ransomware
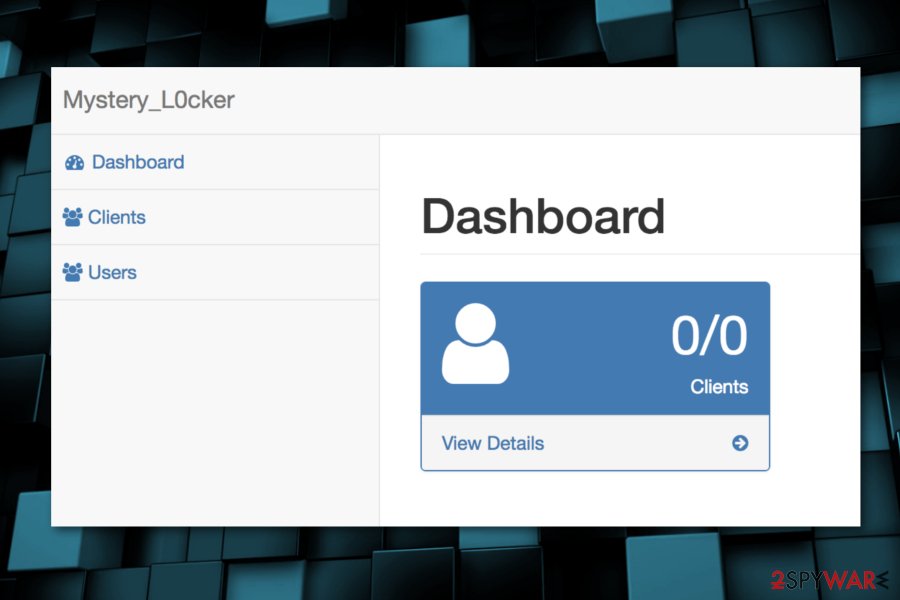
This Android malware has built-in ransomware virus. Dubbed as Mystery_L0cker, the file-encrypting virus starts scanning the system and looking for the targeted files as soon as it gets into the system. When it finds needed files, it places them the individual password-protected ZIP archives and then deletes original copies of the files.
Each victim receives a unique a unique password. However, researchers report that functionality of MysteryBot ransomware is not great. Due to some error during the encryption, some victims may not be able to recover their files.
However, following the encryption, malware delivers a message that the Android device is blocked because of accessing pornographic videos. However, the message tells that victims can restore their device and files by sending an email to googleprotect@mail.ru address and following their guidelines.
There’s no doubt that victims will be asked to pay a couple of hundred dollars in cryptocurrency in order to get back access to their files and device. However, security experts from LosVirus.es[4] note that such deal might end up with a money loss. As we have already mentioned, some victims may not be able to recover their files in general. Instead of risking to experience a bigger damage, remove MysteryBot malware form the device.
Android malware spreads as a fake Adobe Flash Player app
Android banking trojan gets into the system when people install fake Adobe Flash Player from third-party app stores or ads. Therefore, users are advised to stay away from suspicious stores and stick to the official Google Play Store.
Indeed, malware might bypass official store’s security too. However, chances to download malware from there is not that huge, especially, if you follow these security tips:
- Install apps only from trusted developers;
- Read app permissions and do not install apps that require administrative access to your device or other permissions that are unnecessary for its operation;
- Read terms of use, privacy policy and other provided information by the developers;
- Read user reviews outside the app store.
Eliminate MysteryBot malware from Android smartphones and tablets
In order to remove MysteryBot from the device, you have to uninstall fake Adobe Flash Player app and other malicious components from the Android OS. However, this sophisticated malware might block such attempts. For this reason, you may need to reboot your device to Safe Mode:
- Press and hold a power button for a couple of seconds until you see a menu.
- Tap and hold Power off.
- In the appeared prompt click OK to confirm to boot Android to Safe Mode.
If these steps did not help, just turn on and turn off your device. When try pressing and holding Menu, Volume Down, Volume Up (or Volume Down and Volume Up) simultaneously to see Safe Mode option.
When in Safe Mode, access App manager and uninstall malicious apps. However, we also recommend scanning the device with FortectIntego, Malwarebytes or another anti-malware that is compatible with your mobile device. Then you can be sure that MysteryBot removal is successful.
Once your device is virus free, change your account passwords and monitor banking transactions. If you notice something suspicious on your account, inform your bank. They will stop unknown transactions and offer the help you need.
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Ever-evolving Android virus poses new concerns. Virus Activity blog. News about viruses and cyber threats.
- ^ Bradley Barth. Malspam campaign delivers LokiBot by abusing Windows Installer. SC Magazine. Breaking news on cybersecurity, cybercrime, industry insight and security product reviews.
- ^ MysteryBot; a new Android banking Trojan ready for Android 7 and 8. ThreatFabric blog. Cyber security and malware news.
- ^ Los virus. Los virus. Spanish cyber security news.
