LinkedIn virus versions explained
LinkedIn virus Removal Guide
What is LinkedIn virus?
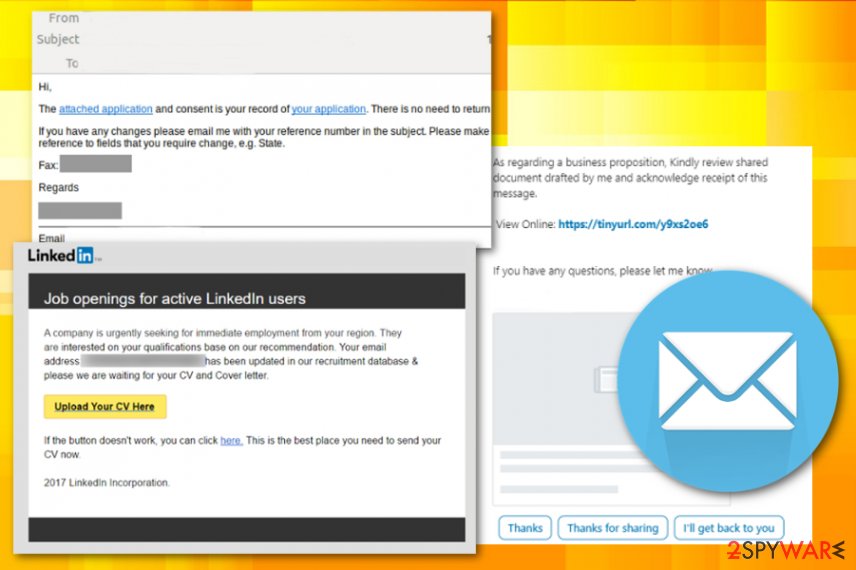
LinkedIn virus is a cyber threat which spreads via emails posing as legitimate messages from the social platform

LinkedIn virus is the email campaign that targets people all over the world with a fake message from the well-known network. The email poses as a business proposition email, job offer, or any other notification informing about the activity on the social platform. Unfortunately, this email campaign aims to trick users into opening the file attachment because this way, malware can be installed on the machine directly. Then, attackers can access any needed part of the computer and even gather personal information about the victim.
This virus started as a bug in LinkedIn messaging service back in 2017, and right now it is one of many email scams that can lead to the installation of dangerous malware or even lead to privacy issues and identity theft.[1] Actors learned how to disguise their files to pass as a real email from the service. The malicious code gets hidden in the malicious PowerShell Script and in the registry or added as a commonly found file. Once the PDF or DOC gets clicked and opened malicious installation launches and your PC gets infected.
| Name | LinkedIn virus |
|---|---|
| Type | Malware |
| Possible versions |
|
| Can be set to | Hijack browser with a PUP or gather information by installing malware directly to the machine |
| Danger level | High. Might steal private data, install other malware |
| Symptoms | Users receive legitimate-looking invitation letters which contain malicious links |
| Distribution | Spreads via malspam and phishing[2] campaigns targeting users worldwide |
| Removal | You can remove LinkedIn virus with the help of a professional anti-malware tool. We suggest using FortectIntego for eliminating virus damage |
LinkedIn scam is a sophisticated cyber threat which comes in the form of a fake invitation email. According to the research, the spam email looks exceptionally convincing as its design resembles the legitimate confirmation email by LinkedIn. Unfortunately, this malspam campaign is developed to infiltrate various malicious programs on the targeted computer and gather sensitive data either about a specific person or the company.
If you have received a message from LinkedIn virus think before you click on it. Experts warn that these fraudulent invitation emails contain malicious links which are designed to redirect you to malware distribution sources. Even though you think that by clicking on Confirm that you know XXX you will be redirected to the LinkedIn Message View page, experts warn you that this is a scam.
In fact, the innocent-looking button incorporated into LinkedIn virus email might directly trigger an automatic installation of the following cyber threats:
- Trojan horses[3];
- Keyloggers;
- Spyware;
- Ransomware;
- Etc.

Be aware that “Unsubscribe” and “Learn why we included this” links in this email do just the same! Likewise, by clicking any of these links provided by Linkedin invitation scam you risk exposing information which might personally identify you and lead to identity theft. Note that if the criminals manage to get sensitive data, they can sell it in the underground market and receive illegal profits.
If you fall for this scam, run a full system scan with updated anti-malware software right away. Keep in mind that any hesitations to remove LinkedIn virus might provide cybercriminals the necessary time to infect your system with more malicious programs or gather essential data.
We recommend using FortectIntego for LinkedIn virus removal. This security software will not only eliminate the malware but also fix virus damage after the infection and even restore needed Windows files from the database. Additional instructions on how to prepare your system for malware elimination listed below the article.
LinkedIn email scam possible versions
LinkedIn virus can have different purposes since this is not a new threat malicious actors managed to create different campaigns. Email scam campaign delivers various malware, and that depends on the malicious actor who is running the virus.
One message is targeting people and stating about the message from a particular person, poses as a notification from your friend or colleague. Linkedin invitation scam tricks people into clicking the link provided on the email which supposedly redirects you to the message gotten on the social platform. Unfortunately, the link is malicious and can lead to the installation of other malware programs.
Additionally, LinkedIn request scam is especially dangerous if the computer user is working in a large-scale organization. Attackers usually target employees to get into the network system of the firm and generate even more illegal profits. According to the security and social media professor Matthew Warren, employees should be extra vigilant[4]:
The most effective malware is the passive malware that just sits there and just monitors your activities <…> For particular organisations, it could mean capturing log ins that used on your computer.
LinkedIn request scam shows messages about business offers, job positions or open places for employment. Any active button with “Upload your CV here” or a hyperlink also redirects the victim to a malicious page or even automatically initiates a download of malicious program.
LinkedIn Share – suspicious browser extension
However, there is a malicious browser extension that uses lock-screen function and affects websites with unethical marketing practices that force users to install various in-browser content against their will. The LinkedIn share is a deceptive browser extension that reads and collects different information about the user and even can change the material on the websites you visit.
The browser extension locks the screen and restricts access to various functions. Then the pop-up appears that forces the victim to install shady extensions, tools, or toolbars. It even has the function of changing the homepage and new tab settings or alters startup preferences to run the needed programs on the browser and redirect your inline traffic to ad-supported sites so that the revenue can be generated.
This LinkedIn Share browser hijack redirects to shady pages to make a profit for its publisher since all the visits and website views can be monetized. Free browser attachment even gets promoted as a useful extension that suggests words based on things you type. However, this type of LinkedIn virus behaves intrusively as any PUP:
- delivers pop-up advertisements, banners;
- changes browser settings, appearance;
- redirect online traffic;
- makes PC running slow.
You need to get FortectIntego or SpyHunter 5Combo Cleaner and run a full system scan so any type of the LinkedIn virus gets eliminated. By cleaning your device entirely you can delete associated files, applications and fix any virus damage.
Email malware distribution techniques
As we have already mentioned, malware as such is distributed as a fraudulent invitation email or a similar notification. Commonly, hackers employ mailspam campaigns to spread their malicious programs online. Note that fake emails look exceptionally convincing. Likewise, people might fail to identify a scam.
Luckily our experts have prepared several useful tips to help you identify malicious spam emails:
- Do not open messages that reside in Junk or Spam inboxes;
- Avoid opening emails from unknown senders and especially electronic letters from member@linkedin.com or similar emails;
- If you have any doubts about the legitimacy of the message, contact the company directly for the confirmation of the email;
- Use a professional antivirus with real-time protection.
Email scam campaigns deliver various files with malicious payloads. The attachment on the mail can be in PDF, xlsx, or doc format. Documents often look safe enough to open, so people get tricked and unknowingly infects their devices with various malware, including one of the most dangerous types of cyber threats like ransomware or trojans.
LinkedIn virus elimination requires professional AV tools
Researchers[5] note that the malware installed during this email scam might simply reside on the system and stealthily monitor user's activity. Since it can operate in the background without any visible window, people fail to identify the infection. However, if you remember clicking on suspicious email content, you should consider LinkedIn virus removal.
Our experts recommend employing reliable security tools to remove LinkedIn virus automatically. This way, you can be sure that none of the malware-related components are left on your system. For that, pick FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and run a full system scan immediately.
Also, if you are receiving spam in your email or social networking site, do not hesitate to inform the support center of the sites included. This will help these sites to indicate the scammers more quickly and stop their further activities, so you don't need to worry about LinkedIn virus removal or any other threats.
Getting rid of LinkedIn virus. Follow these steps
Manual removal using Safe Mode
You might need to boot your computer into Safe Mode with Networking to download and use the security software properly because malware alters various preferences and can even disable functions or applications
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove LinkedIn using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of LinkedIn. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from LinkedIn and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Alex Hartman. Hackers hit your inbox: Malware through LinkedIn messenger. LinkedIn. Business and employment-oriented service.
- ^ Danny Palmer. What is phishing? Everything you need to know to protect yourself from scam emails and more. ZDNet. Technology news, analysis and reviews.
- ^ Trojan horse (computing). Wikipedia. The Free Encyclopedia.
- ^ Tom Snowdon. How that LinkedIn invitation may actually be a virus attack. News. Australia's #1 news site.
- ^ BedyNet. BedyNet. Security and Spyware News.





















