Littleapsearch.com browser hijacker (virus) - Free Guide
Littleapsearch.com browser hijacker Removal Guide
What is Littleapsearch.com browser hijacker?
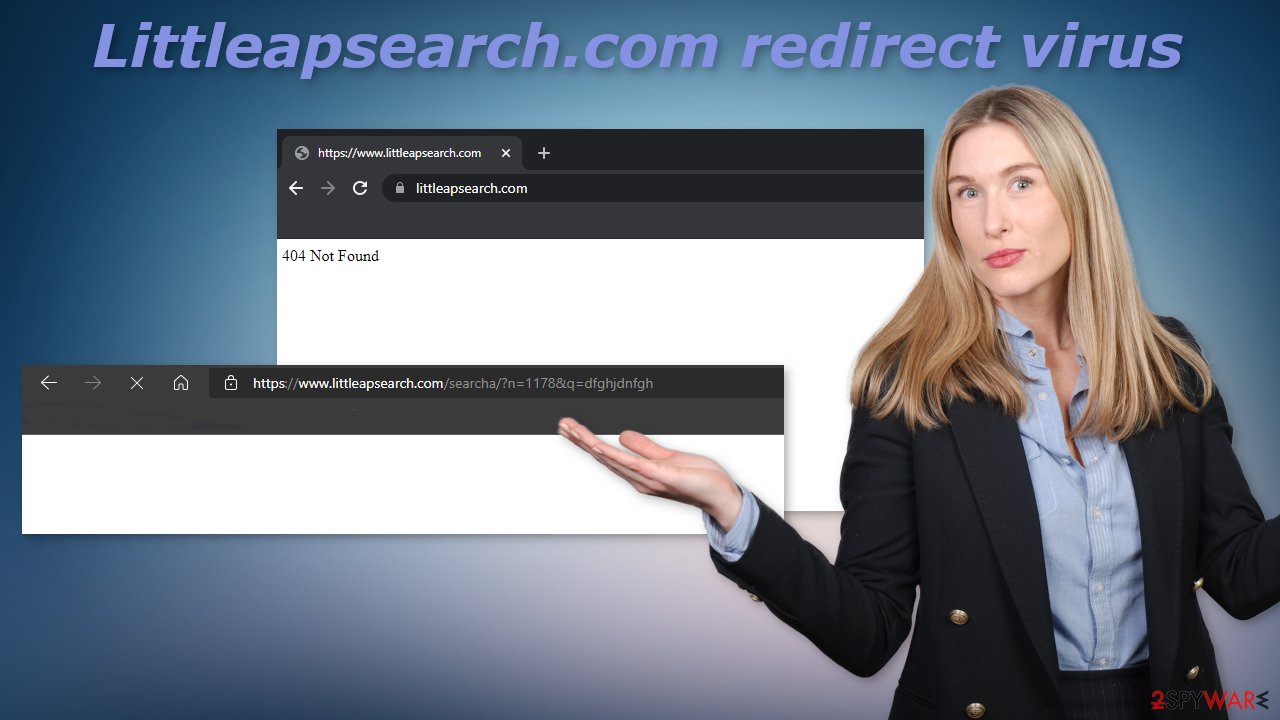
Littleapsearch.com appears when you use the search engine

Littleapsearch.com is an empty domain that redirects search queries when people use the Bing search engine with Microsoft Edge browser. It is classified as a browser hijacker but it can potentially perform some tasks that could be deemed as malicious according to user reports.
It is currently unknown what exactly causes the redirect. A lot of the times' users found out that this activity stopped when they removed third-party browser extensions. It is not known which extension exactly is causing the redirects as it seems to be a couple of them or even more. At first sight, there does not seem to be anything fishy going on, as the redirect appears just before people see what they searched for.
There is a possibility that companies that created the extensions in question code bases have been compromised or another piece of malware had compromised their plugin. Currently, very little information is available about the redirect so it is too early to make assumptions. If you recently noticed this unusual behavior while using Bing keep reading our guide to find out more.
| NAME | Littleapsearch.com |
| TYPE | Redirect virus, browser hijacker, keylogger, spyware |
| SYMPTOMS | Search queries get redirected through Littleapsearch.com |
| DISTRIBUTION | Browser extensions |
| DANGERS | The hijacker could possibly steal passwords, track browsing activity |
| ELIMINATION | Remove third-party extensions by going to your browser settings |
| FURTHER STEPS | FortectIntego can be used after you have successfully got rid of redirects to clear your browsers and optimize the device |
Littleapsearch.com in detail
When you search up the domain on your own, the page does not seem to be active. All you can see is the error “404 Not Found”. But when people see the redirect on Bing, it has some additional data like numbers and letters in the URL. As we mentioned before this activity seems to stop when users remove extensions from their browsers.
Some of the mentioned add-ons are “Quick Color Picker” and “Font Detector” which can both be found on the official Edge Add-ons app store but they are relatively small with little to no customer reviews. It is not clear how many people experience this. Right now, there are a couple of users who asked questions about it on the MS Answer boards.
The most worrying report is of a user, that after removal of third-party add-ons, the next day received a 2-FA[1] request for their Outlook account that they did not initiate and that originated from a foreign country. The password of this user was generated from 16 random characters so it seems that this redirect virus could have spyware[2] abilities and stole the password from auto-fill.[3]
This seems to be a so-called man-in-the-middle attack. Threat actors use it to exploit insecure applications by using automated software. The attackers interrupt the data transfer and pretend to be legitimate participants. This lets the individuals behind it intercept information and data from either party, send malicious links or other information to both participants, and remain undetected. In a MITM attack, the middle participant manipulates the conversation of the two legitimate participants without their knowledge, retrieves confidential information, and causes damage in other ways.
Remove suspicious extensions
Because users reported that the redirect disappeared when they removed third-party extensions they have installed, let's try and do just that. You have to do this manually by going to your browser settings:
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.
![Reset MS Edge Reset MS Edge]()
If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\Users\%username%\AppData\Local\Packages\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete
![Advanced MS Edge reset 1 Advanced MS Edge reset 1]()
- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\AppXManifest.xml” -Verbose
![Advanced MS Edge reset 2 Advanced MS Edge reset 2]()
After you successfully get rid of the redirect, we strongly suggest using FortectIntego to clear your browsers. The virus could have injected malicious links in the search results that you clicked on, so it would be a good idea to get rid of any cookies and cache. This repair tool can also optimize your device and improve performance, fix corrupted files, system errors.
You might not know about a PUA until it makes changes
As we said before, there is still very little known about this so users affected by Littleapsearch.com should take all the possible prevention techniques. We recommend using SpyHunter 5Combo Cleaner or Malwarebytes to check your machine for potentially unwanted programs and malware. Professional security tools can help detect applications that perform tasks in the background.
Of course, you can go through the program list yourself, and see if there are any suspicious apps in there that you did not install yourself:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
How to protect yourself from MITM attacks?
- Use a VPN – it masks your IP address by bouncing it through a private server. VPNs also encrypt the data being transmitted over the Internet. This does not make you fully resistant to MITM attacks, but this makes it much harder for crooks.
- Only visit HTTPS websites – HTTPS websites encrypt data and prevent attackers from intercepting communications. Also, look for a lock next to the URL in the browser and make sure it does not start with HTTP.[4]
- Avoid installing unpopular browser extensions – although official app stores are considered to distribute safe add-ons, some unknown ones can have weak security measures in place, and can be an easy target for threat actors who want to exploit them. Try to choose from those that have a lot of users and reviews.
- Use 2-FA authentication – if cybercriminals have your password, there is almost nothing stopping them from stealing your accounts, but if you use 2-FA authentication, they also have to get access to your mobile device that you use for authentication, which is very unlikely.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Littleapsearch.com browser hijacker. Follow these steps
Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Littleapsearch.com browser hijacker registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Multi-factor authentication. Wikipedia. The Free Encyclopedia.
- ^ What is Spyware?. Kaspersky. Home Security Blog.
- ^ Lindsey Murray. Major Security Flaw in Autofill Tool Means Your Info Can Be Stolen. GoodHouskeeping. Lifestyle Magazine.
- ^ Why is HTTP not secure? | HTTP vs. HTTPS. CloudFlare. Learning Center.


















