Lokibot virus (Removal Instructions) - 2020 update
Lokibot virus Removal Guide
What is Lokibot virus?
Lokibot is a Trojan malware that steals credentials, logs keystrokes, and can launch Jigsaw ransomware payload

LokiBot is an info stealer Trojan malware[1] that can leak usernames, passwords, banking information, and other credentials to remote servers managed by criminals. The virus has been first detected in 2015, while a closer investigation has been initiated in late 2017 by SfyLab (or ThreatFabric currently) security researchers[2]. It usually infiltrates devices using malicious phishing emails, which are massively sent by bots employed by hackers or can be downloaded as a fake app from third-party websites. The Trojan can attack Windows and Android users.
After a quiet period, cybersecurity researchers from Trend Micro[3] revealed a renewed malware campaign impersonating the launcher for multiplayer video game Fortnite. A massive malspam campaign has been spotted imitating the launcher for Epic Games, which after granting permission launches the #C code allowing to bypass security systems and the .NET file that opens the backdoor for data leaking.
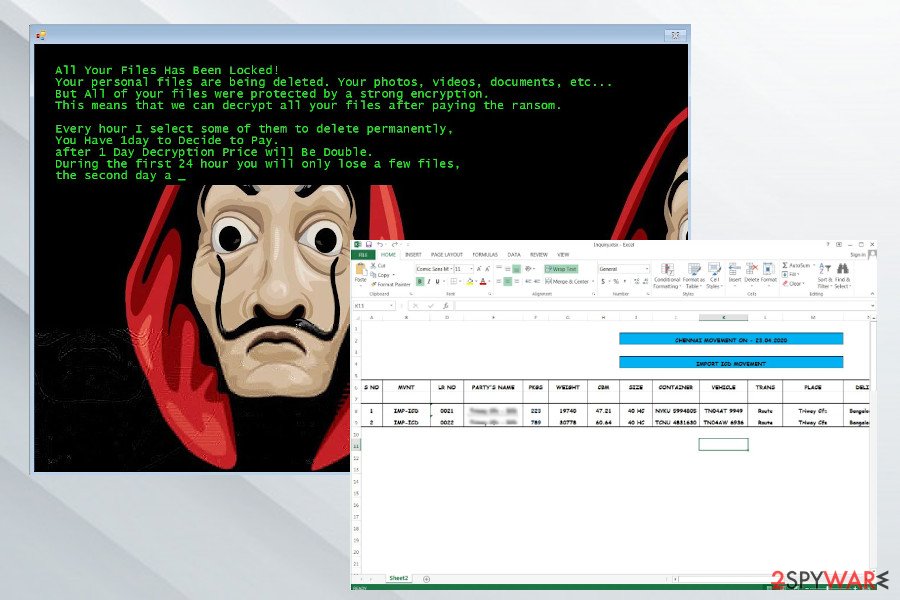
On May 1, 2020, news about the new LokiBot virus attack has started spreading. Attackers have started a phishing campaign introducing people with the fictitious invoices and bank transfers, which contain infected excel sheets named Swift.xlsx, Inquiry.xlsxorders.xlsx, or Invoice For Payment.xlsx. If the user opens the sheet, cjjjjjjjjjjjjjjjjjjj.exe[4] file, which stands for LokiBot, connects to remote servers and starts leaking credentials. Besides, it downloads a new variant of Jigsaw ransomware, which encrypts files using .zemblax extension. The most interesting feature of this malware is that it shifts into ransomware as soon as the victim attempts to get rid of the malicious application.
| SUMMARY | |
| Name | LokiBot |
| Type | Banking trojan with ransomware traits |
| Discovered by | SfyLab |
| Targets | Android devices, Windows systems |
| Distribution | Spam email attachments, malicious websites, third-party apps, social media links, etc. Typically, it disguises under malicious Excel spreadsheets that imitate official banking documents, invoices, or order details. The latest LokiBoit spam campaign misuses a game launcher of a popular game Fortnite |
| Executables | cjjjjjjjjjjjjjjjjjjj.exe, objectrecalcine.exe |
| Symptoms | Fake messages, pop-ups, fake bank interface, locked up files if the termination is implemented, files encrypted by Jigsaw or another ransomware (.zemblax extension) |
| Danger level | High. Stolen credentials can lead to money theft or identity fraud |
| Elimination | Eliminate the threat by entering Safe Mode and scanning the device with SpyHunter 5Combo Cleaner or Malwarebytes |
| Optimization required | This is a dangerous Trojan, which drops malicious objects all over the system. It can not only delete files, but also hijack registries, turn core processes idle, block anti-virus, and perform other tasks that are not restored after Trojan infection. For a full PC's optimization, we recommend using FortectIntego tool |
The primary goal of cybercriminals is obviously money. Thus, after the device gets infected with the virus, users can be presented with a simulated screen that looks identical to the online banking one. Victims are unaware of the presence of malware and merely enter their credentials into the banking app-look-alike. In the meantime, the virus sends all the information directly to hackers, allowing them to use this sensitive data.
Additionally, the virus is capable of mimicking other applications, such as Skype, Viber, WhatsApp, and even Outlook. Meaning, that all the data entered using these fake programs will be stolen as well; therefore, you need to be very careful. LokiBot removal should be your top priority. For that, you have to reboot your machine in Safe Mode, delete malware, and then scan it with SpyHunter 5Combo Cleaner or Malwarebytes to make sure all the traces are gone.
In addition to displaying a fake app interface and sending login information to hackers, the virus is also capable of the following:
- Initiating fake notifications that look identical to those from a bank;
- Making the smartphone vibrate when the messages pop up;
- Opening the browser and navigating to specific websites;
- Redirecting user's internet traffic through a proxy server;
- Sending malicious spam SMS messages to people on the contact list;
- Replying to incoming messages.
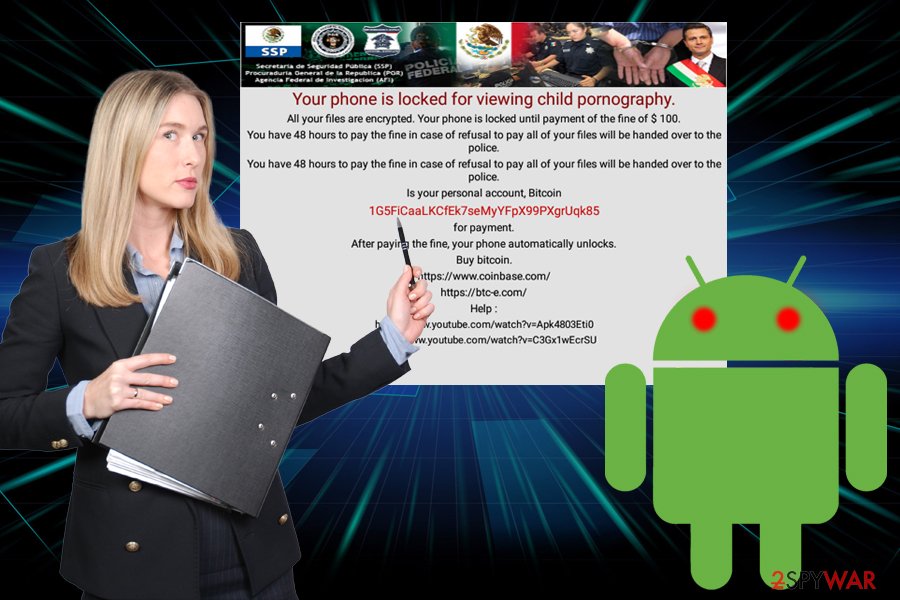
The banking trojan needs to have administrative rights to do all this, which it gains during the installation. Nevertheless, users are unaware of that at the start. Even if the attempt is made to deny admin rights, or if the user tries to remove LokiBot from their device, it instantaneously turns into ransomware[5] type virus.
Culprits earned a fortune from ransom payments
As soon as Lokibot shifts to ransomware, it reboots the device, locks-up the screen and displays a message to users, informing them that their machine was locked due to them viewing child pornography. These screen-locking viruses started appearing in 2010 and infected millions of devices worldwide (probably the most famous one is FBI virus).
Obviously, the claims are fake, and the device is locked by a virus. To redeem the full function of their phone or tablet, users are asked to pay ransom in Bitcoin cryptocurrency which usually ranges between $70 and $100 within 48 hours.
When researchers analyzed LokiBot's code, they discovered that the ransomware does not lock their files properly. It uses weak encryption and leaves copies of original files under different names, which is relatively easy to recover.
Unfortunately, not all users are aware of that, and they hurry to pay the ransom, as they are scared to lose the access to their device. This way, crooks earned over $1.5 million so far. Nevertheless, because the malware only costs around $2000 on the Dark Web, it is highly likely that it will continue to be spread by illegal money-craving cybercriminals.
Update 2020: Jigsaw ransomware under LokiBot payload
At the begging of 2020 this info stealer has renewed its malspam campaigns. According to Trend Micro, the campaign misuses the famous Epic Games launcher, which is widely used by Fortnite and other multiplayer video game lovers. The rogue launcher is being distributed by bots via spam emails, which once enabled runs two processes:
- #C source code, which blocks security software and prevents the malware from being eliminated;
- .NET executable, which runs the #C and enables LokiBot malware.
Once the malware grants access, it's primary goal is to trick the victim into giving away credentials, logins, banking information, and other personal information that subsequently allows hackers to steal money.
Jigsaw ransomware is one of the latest file-encrypting malware that the Lokibot trojan is programmed to launch. The latest malspam campaign, which started at the end of March 2020, tricks regular PC users into opening professionally developed Excel spreadsheets imitating invoices, bank transfers, order tracking details, and similar. According to experts, the spreadsheets can be named as follows:
- Swift.xlsx
- Orders.xlsx
- Invoice For Payment.xlsx
- Inquiry.xlsx
Each of them launches the cjjjjjjjjjjjjjjjjjjj.exe executable file, which starts exploiting for possibilities to leak saved logins credentials. It has an access to all web browsers, e-mails, remote control servers, and so on. However, it can not only steal data, but also download Jigsaw ransomware virus, which encrypts files with .zemblax file extension.
In the case of LokiBot and Jigsaw bundle attack, it's very important to disable the drpbx.exe process via Task Manager. Even though Jigsaw ransomware has been cracked down and can be decrypted quite easily, it is programmed to start damaging encrypted files progressively if the victim fails to pay the ransom on time. Thus, terminating the drpbx.exe is the only way to protect files from permanent loss. After that, ensure a full removal with a professional anti-virus program.
Protect yourself from dangerous trojans and other malware
Many users are not that tech-savvy, and cybercrooks are fast to abuse that fact. Thus, they employ various trickery to make victims install malware on their devices. The key here is information, and once you get to know how to protect yourself from viruses, you will not have to deal with the stress they can bring. Security researchers[6] advice to take these precaution steps:
- Never click on links that you are not sure are safe (note: even messages from your friends on social media may be malicious, as it is a case in the Facebook virus)
- Avoid shady websites and file-sharing (torrent) domains;
- Download apps only from trusted sources, like Google Play;
- Beware of spam emails with attachments or hyperlinks;
- Employ reputable security software.
Eliminate the virus and keep your credentials safe
If you suspect that a banking Trojan is hiding in your system or if your device was locked and you are accused of child pornography, do not panic and remove Lokibot virus from your device. You will have to eliminate the malware by entering Safe Mode on your machine in the following way:
- Press and hold Power button – the Power off the menu should show up;
- Then, press and hold Power off;
- The Turn on Safe Mode menu should appear;
- Press OK and wait for the device to reboot
After you enter safe mode, you have to strip the infected app of its administrative rights and eliminate malware.
If your Windows machine is infected with this cyber threat, you should take of Lokibot removal by following steps below. Do not forget you need to keep your computer protected at all times, so we recommend using anti-malware software with real-time protection feature.
If this trojan has successfully deployed Jigsaw ransomware payload, then take immediate actions to terminate the ransomware. Otherwise, it may start deleting the files in case the payment is late. You should:
- Open Task Manager (Ctrl + Alt + Delete).
- Select Task Manager and click on this option.
- Look for drpbx.exe, which stands for Jigsaw executable.
- Right-click on it and select End Task.
Right after that, restart your PC into Safe Mode with Networking and run a full system scan with a professional anti-malware program as explained below.
Getting rid of Lokibot virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Lokibot using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Lokibot. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Lokibot and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Banker Trojan. Investopedia. Financial content.
- ^ The first hybrid Android malware. ThreatFabric. Securit yresearchers.
- ^ LokiBot Impersonates Popular Game Launcher and Drops Compiled C# Code File. Trend Micro. Security News.
- ^ cjjjjjjjjjjjjjjjjjjj.exe. Virus Total. Free URL and file scanner.
- ^ Ransomware. Wikipedia. The Free Encyclopedia.
- ^ UsunWirusa. UsunWirusa. Polish cybersecurity site.





















