Maze ransomware (Virus Removal Instructions) - Apr 2020 update
Maze virus Removal Guide
What is Maze ransomware?
Maze ransomware is a cryptocurrency-focused malware that is named by creators
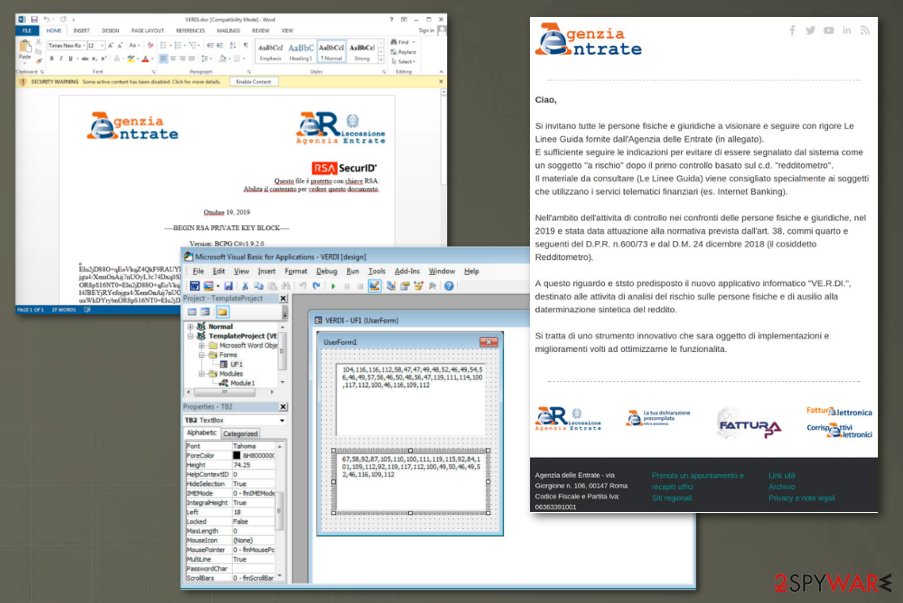
The ransomware is known to have sophisticated methods of distribution because it creates emails with false claims and imitates agencies or government institutions. One of the Maze ransomware campaigns against Italy[2] revealed that users got spam emails pretending to be sent from the Italian Revenue Agency and the Agenzia Delle Entrate that is responsible for taxes and revenue for the government.
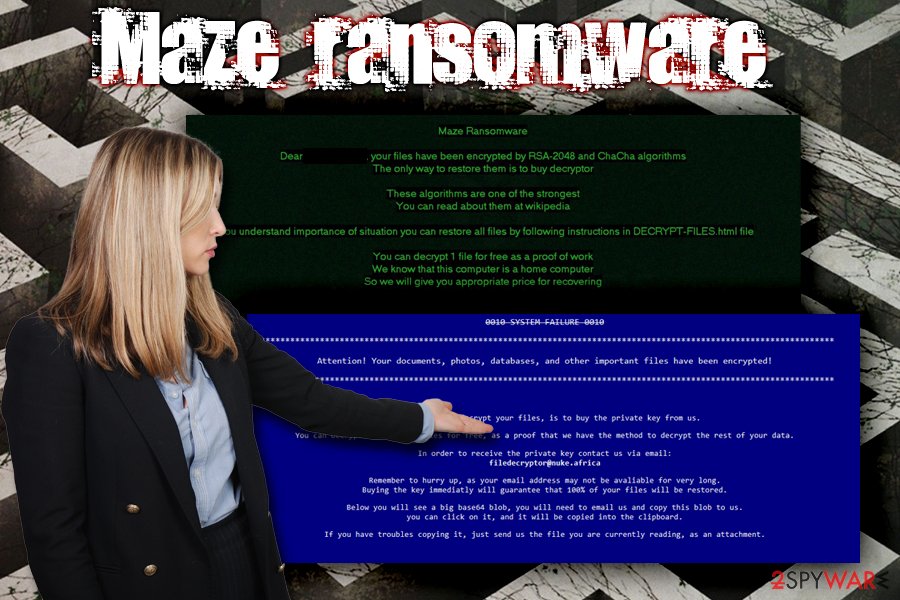
The virus is also known to be distributed via the help of a fake Abra site that hosts the Mobile Bitcoin Wallet app under the same name. Visitors who want to download the application will end up being redirected to a Fallout exploit kit,[3] which, under certain conditions, will implant the malicious payload without the users' interaction whatsoever. After encrypting files, the virus will drop a ransom note DECRYPT-FILES.html that asks victims to pay a ransom in BTC and contact bad actors via filedecryptor@nuke.africa. Additionally, the malware will also alter the background on the desktop, displaying another message from hackers.
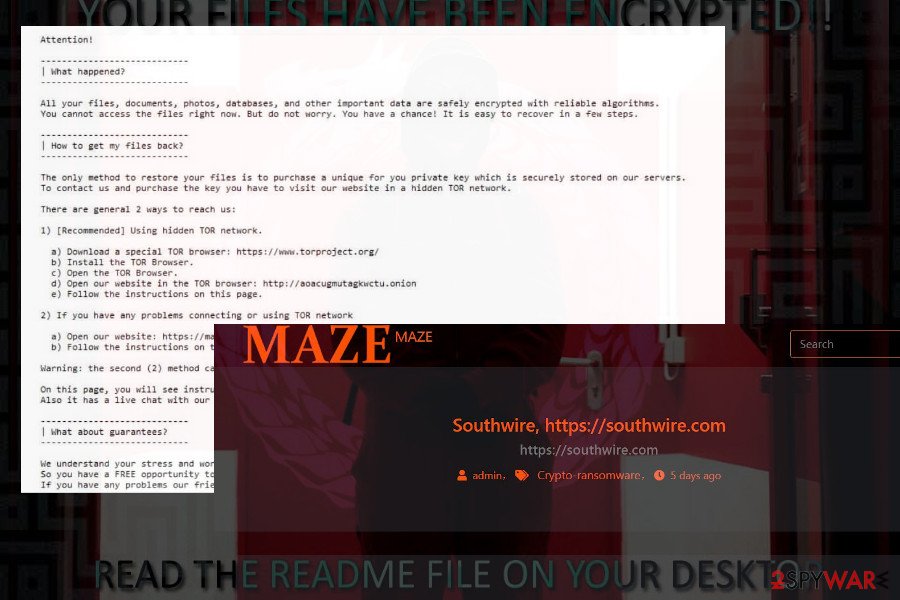
However, the latest Maze ransomware variant seems to switch its target from individual PCs and small businesses to giant companies that, obviously, can bring much greater earnings. Starting with an attack in 2019 over the Canadian insurance company Andrew Agencies, the criminals behind the file-locking virus has been reported for an attack over Cognizant[4] – one of the biggest IT managed service company in the world in April 2020. According to the cybersecurity experts, the ransomware made changes on IP addresses of servers and kepstl32.dll, memes.tmp, and maze.dll file hashes. Since this attack is currently under investigation, the exact damage caused to the company is yet to come. Nevertheless, experts share their presumptions that if Maze eventually manifested on the Cognizant server, it must have been there for an extended period of time to leak as many files and databases as possible. If the speculations will come true, the ransomware will be listed as a cause of a massive Cognizant data breach.
| Name | Maze file virus |
| Type | Ransomware |
| A variant of | ChaCha ransomware |
| Distribution | This malware strain is most commonly spread via the Fallout exploit kit. However, it also has a chance of showing through spam emails and their malicious attachments, fake updates, brute-forcing, and by employing other tactics. Recent campaigns were distributed via emails and infected word documents |
| Encryption algorithm | Bad actors use the RSA-2048 and ChaCha20 encryption algorithms to lock up all files and documents that are found on the targeted system |
| File extension | There is no accurate extension that is appended by the ransomware. Once the virus locks files, it adds a random 4-7 letter appendix to each filename |
| Related files | After successful infiltration, the file-locking virus brings the zprxqb.exe and Maze_Ransomware.exe files to the Windows computer system. The latest attack on Cognizant refers to file hashes of kepstl32.dll, memes.tmp, and maze.dll |
| Ransom note | Information about file encryption and ransom demands is placed in the DECRYPT-FILES.html which appears on the computer screen after data encryption |
| Contact | Criminals provide the filedecryptor@nuke.africa email address as a way to contact them and discuss all needed matters |
| New version | The virus developers have released a similar malware version that holds the exact same name. Even though the new variant also relies on successful encryption, the virus does not encrypt files if it finds the C:\hutchins.txt file in the computer system |
| Important | The ransomware exhibit a great success in attacking servers of big companies. If the criminals manage to insert malicious payload on the server, it starts leaking files, databases, and other encrypted information that is not encrypted to a remote server. The examples of attacks on Andrew Agencies and Cognizant prove the fact |
| Termination | Use a powerful anti-malware program to perform a thorough system checkup, detect all malicious strains, and remove the virus permanently |
| Decryption | File decryption is only possible via backups. However, third-party software might sometimes be helpful as well. We have provided and described three different tools at the end of this article |
| Fix virus damage | The virus causes damage to the infected system. It not only targets to lock targeted data, but also compromise Windows registry entries, startup processes, and some of the core system files. FortectIntego repair utility will help to fix such damage |
Interestingly, the latest variant of Maze ransomware shows a different wallpaper based on computer type (for example, home computer, backup server, server in a corporate network, primary domain controller, etc.), which essentially changes the decryptor price.
While there is no free decryption tool that would be able to retrieve your data, you should not pay the ransom and instead focus on Maze ransomware removal and alternative file recovery methods, instructions for which we provide below. Keep in mind that you might get easily scammed if you transfer the money to the crooks.

While the ransomware was spotted being distributed with the help of Fallout Exploit kit, it does not mean that hackers do not employ other tactics, such as:
- Spam emails;
- Unprotected RDP;
- Fake updates;
- Pirated software and its cracks;[5]
- Torrent sites;
- Web injects, etc.
Therefore, even if your software and the Windows OS are patched with the latest updates to prevent Fallout EK, you might still be at risk if you do not use adequate security measures. To make sure you are protected from future Maze ransomware infections, check the second part of this article.
Ransomware activity spotted in Italy
Independent researcher reported at the end of October 2019 that Maze virus released a campaign that targets Italy. The malicious malware attempted to infect systems with the help of a spam email campaign that delivers malicious word files and drops payload on the machine.
Emails came with legitimate-looking statements about new taxes, rules. The email is headlined “AGGIORNAMENTO: Attivita di contrasto all'evasione. Aggiornamento” and contains a word document called “VERDI.doc” which should involve the guidelines. However, the word document states about encryption of the content and then requires the reader to enable the content to read the text properly.
Once that is done, and the document is downloaded, opened on the machine, embedded macros get executed and downloads ransomware to the Temp folder on the system. Maze ransomware then gets launched and encrypts files, changes the wallpaper to an image with the guidelines on how to find a ransom note, and delivers a separate file DECRYPT-FILES.txt which includes instructions on contacting the virus developers.
The payment site that you should reach via the link provided in this ransom note shows the amount of ransom needed for the decryption key. It apparently differs from the type of device, the number of affected files, and other details about the victim. It can go up to $1200 or even more in Bitcoin. Unfortunately, decryption is not possible, paying is not an option, so you should remove the malware with an anti-malware tool and recover files using backups.
Once the payload of Maze ransomware is populated, it will contact 2 domains and 15 hosts, alter the Windows registry, delete Shadow volume snapshots to complicate the recovery process, and perform other malicious tasks required for its operation, for example, corrupting the Windows hosts file.
Ransomware viruses might seek to damage the hosts' file in order to prevent the victims from accessing security-related websites and forums where they could get valuable information on the malware's removal process. So, while you opt to remove the virus from your computer, make sure to delete the damaged file too.
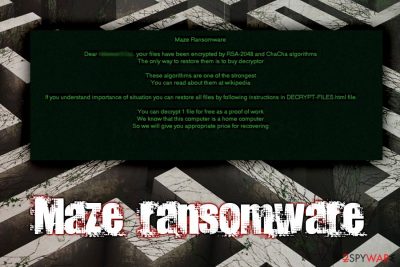
After establishing itself and locking the files, Maze ransomware will display the following note:
0010 SYSTEM FAILURE 0010
*********************************************************************************************************************
Attention! Your documents, photos, databases, and other important files have been encrypted!
*********************************************************************************************************************The only way to decrypt your files, is to buy the private key from us.
You can decrypt one of your files for free, as a proof that we have the method to decrypt the rest of your data.
In order to receive the private key contact us via email:
filedecryptor@nuke.africa
Remember to hurry up, as your email address may not be avaliable for very long.
Buying the key immediatly will guarantee that 100% of your files will be restored.
Below you will see a big base64 blob, you will need to email us and copy this blob to us.
you can click on it, and it will be copied into the clipboard.
If you have troubles copying it, just send us the file you are currently reading, as an attachment.
At the bottom of the note, victims can locate a Base64 string that includes such information and user's login name, Windows version, other technical data, and a private key. All this information is allegedly required for cybercriminals in order to decrypt files locked by the ransomware.
Speaking of malware removal, various AV vendors recognize the threat under such names as TR/Kryptik.ijmxi, or Ransom.Maze, but such things differ based on the particular virus database.[6] This is why we suggest using professional anti-malware tools to terminate the malware entirely.
However, make sure to choose reliable software. Note that manual elimination is not possible here as you risk damaging your system. You should remember that some system files get damaged too, FortectIntego may help you with those corrupted files after the file virus removal.
Once you delete Maze virus entirely, you can connect your backup device to retrieve your data. In case you have no backups prepared, there are very few chances of recovering files for free, although you should try third-party software. We provide all the instructions and download links to such tools below.
The new version includes the same Maze ransomware name
A very similar, almost identical version to the ransomware was found by nao_sec researcher.[7] This variant comes from the same family and even holds the same name “Maze”. The new variant also locks up data with a random appendix, however, there is one exception here.
The new variant of Maze ransomware looks for the C:\hutchins.txt file and if it is found on the infected system, data locking does not happen in this scenario. However, if the file is not found, the malware successfully proceeds with the encryption and drops the DECRYPT-FILES.txt ransom message.
Even though there is not much information given on the demanded price, cybercriminals often urge for a ransom between $200 and $2000. However, paying the money might only lure you into a scam and you will receive no decryption tool at all.
Additionally, it is known that the new Maze ransomware version appears through an exploit kit known as SpelevoEK. However, that does not deny the possibility that the malicious payload might be brought through malicious hyperlinks/ads, infectious macros, and p2p networks.
One of the biggest Maze victims in 2019 – Andrew Agencies insurance company
Apart from a massive malspam campaign initiating against Italian citizens, the ransomware extorted $1.1 million from a well-known Canadian insurance firm Andrew Agencies[8]. The malware has stolen 1.5 GB of information from the company's servers, including information of approximately 900 clients, more than 200 employees, and coded passwords of people's online accounts.
Prior to the encryption, Maze leaked the data to remote servers and then locked files on 245 computer systems using RSA-2048 and ChaCha20 encryption algorithms. Crooks demanded the Andrew Agencies heads to pay 150 BTC in exchange for not leaking data publicly.
The history remains silent if Andrew Agencies paid the ransom; though Dave Schioler, the vice president of the company, earlier claimed that they are not going to pay the redemption as there is no clear evidence that criminals behind the virus have leaked the files.
Ransomware prevention tips for individual users and companies
Hackers are sophisticated individuals who decided to put their knowledge for evil deeds. Therefore, they often employ a variety of advanced methods to distribute the payload of the malware, ensuring high infection rates among victims.
Nevertheless, those who are careless are by far the most vulnerable and prone to infections. While such threats like adware or other PUPs might not be devastating, ransomware can result in permanent data loss. What is more, those who decide to pay for the decryptor might also end up losing money as well.
Therefore, follow these tips from industry experts to avoid malware infections in the future:
- Install security patches for your operating system, as well as all the installed applications;
- Use reputable anti-malware software with real-time protection feature;
- Be aware that spam emails that carry attachments (such as .doc, .html, .pdf, etc.) or include hyperlinks might be infected with malware, including ransomware;
- Do not fall for believing in suspicious emails that claim to be from FedEx, DHL, or other reliable shipping companies even though you have not been waiting for an order to arrive lately;
- Ensure the safety of all your accounts by using password managing app and two-factor authentication;
- Use ad-blocker on high-risk sites, although do not forget to add exclusions for sites you want to support;
- Do now download pirated software or its cracks or keygens;
- Scan every unknown executable with tools like Virus Total or Hybrid Analysis;
- Use a VPN when using the Remote Desktop Protocol and ensure a strong password.
Finally, to negate the damage done by a ransomware infection, prepare backups regularly. For more accurate information, we want to inform users that ransomware developers are likely to hack RDP such as the TCP Port 3389 for secret malware infiltration. Additionally, exploit kits such as Fallout and SpelevoEK are widely used for distributing ransomware-related payload.
Terminate Maze ransomware virus by using powerful malware removal tools
You should not attempt to remove the ransomware manually, as such a method should only be used by IT professionals. Besides, cryptovirus can modify Windows system files and embed itself deep into the OS, so reverting these changes is almost impossible. According to experts from Virusai.lt,[9] it is very important not to skip any malicious objects, otherwise, the ransomware virus might boot itself automatically within the next PC startup process.
Instead of taking the risk in your own hands, employ reputable anti-malware software for Maze ransomware removal. We suggest you use anti-malware tools. You also should benefit from tools that may fix the damage and system files after the virus termination. Applications like SpyHunter 5Combo Cleaner, Malwarebytes, or other options are also available – choose the one that suits you the most.
Be aware that the Maze ransomware virus might prevent your security software from performing correctly. In such a case, you need to access Safe Mode, as it will temporarily stop malware's activities. Upon successful termination of the ransomware, fix the damage that it gas initiated against Windows OS. For that, we recommend using a repair tool FortectIntego.
Once you delete the virus, you can attempt to recover your data. Please follow the detailed instructions for this process below. We cannot assure you that all of the below-provided techniques will work perfectly but trying them is definitely a better thing to do than the risk to lose a huge amount of money while paying the cybercriminals.
Getting rid of Maze virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Maze using System Restore
You can also use System Restore to terminate the infection:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Maze. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Maze from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Maze, you can use several methods to restore them:
Data Recovery Pro might be able to recover at least some of your files
This tool is sometimes useful for ransomware victims.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Maze ransomware;
- Restore them.
Taking advantage of Windows Previous Versions feature
If you had System Restore enabled, this option might help you retrieve at least some individual files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer application might recover all your data
If the virus failed to remove Shadow Volume Copies, this solution might be the best for you.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Maze and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ RSA (cryptosystem). Wikipedia. The free encyclopedia.
- ^ David Bisson. Malspam Campaign Targeting Italian Users with Maze Ransomware. Tripwire. Security insights.
- ^ Fallout. NJCCIC. New Jersey Cybersecurity and Communications Integration Cell.
- ^ Julie Splinters. Newest Maze ransomware victim - IT giant Cognizant. 2-Spyware News.
- ^ Ransomware Can Make Installing Illegal Software More Risky. The Pickle. Technology Solutions.
- ^ e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684. Virus Total. URL and file scanning engine.
- ^ nao_sec tweets. Twitter. Social platform.
- ^ Howard Solomon. Manitoba insurance agency admits it was hit by ransomware. IT World Canada. Canadian online resource for IT professionals.
- ^ Virusai.lt. Virusai. Security and spyware news articles.





















