McAfee Total Protection has expired scam (fake) - Free Guide
McAfee Total Protection has expired scam Removal Guide
What is McAfee Total Protection has expired scam?
McAfee Total Protection has expired scam is used to lure out personal information
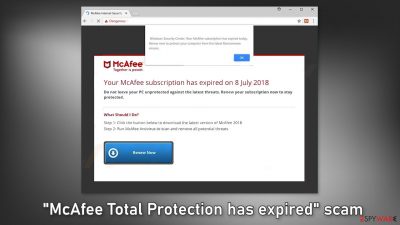
“McAfee Total Protection has expired” is a fake message delivered by scammers. They use the name of a well-known security brand to appear legitimate. Social engineering[1] techniques are used to trick people into thinking that their system is in danger. There are many variations of this scam and thousands of websites that are disguised as a security alert from McAfee. You may encounter messages such as:
Windows Security Center: Your McAfee subscription has expired today. Renew now to protect your computer from the latest Ransomware viruses.
Your McAfee subscription has expired on 8 July 2018
Do not leave your PC unprotected against the latest threats. Renew your subscription now to stay protected.
What Should I Do?
Step 1: Click the button below to download the latest version of McAfee 2018
Step 2: Run McAfee Antivirus to scan and remove all potential threats
These scams can cause PUP (potentially unwanted program),[2] and malware installations. Crooks also ask users to fill out their personal details, like their name, address, email, phone number, bank card details, etc. This can result in privacy issues, monetary losses, or even identity theft.
| NAME | McAfee Total Protection has expired |
| TYPE | Phishing scam; adware |
| SYMPTOMS | A page appears seemingly out of nowhere pushing users to install antivirus software |
| DISTRIBUTION | Compromised websites, deceptive ads, software bundling |
| DANGERS | Installation of PUPs or malware, sensitive information disclosure, monetary losses |
| ELIMINATION | Check your system for adware – you can either do it manually or perform a full system scan with antivirus for a quicker solution |
| FURTHER STEPS | Clean your web browsers quickly and fix virus damage automatically with FortectIntego repair tool |
Distribution methods
We previously wrote about many similar sites, like Datasecuritycentr.com, Systemsecuritys.com, and Totaldatasecuritycentr.com. They can rarely be found through search results. Most of them hide in other shady pages. Sites that engage in illegal activities are especially dangerous as they are unregulated and filled with deceptive ads and sneaky redirects.
“McAfee Total Protection has expired” scam can appear after clicking on a fake “Download” or “Play” button on an illegal streaming platform.[3] Even though Google promised to get rid of them, they still exist. Nowadays, there are plenty of streaming services to choose from, like Netflix, or Hulu. Users only need to pay a small subscription fee to be able to watch as much content as they want safely.
You should also beware of freeware distribution, peer-to-peer file-sharing platforms,[4] and torrent sites. They are breeding grounds for all kinds of malware and rogue advertising networks operate there actively so you can be easily redirected to a push notification spam page, or another scam site created to monetize user activity.
To minimize the risk of adware infection, be focused during software installation. Always choose the “Custom” or “Advanced” installation method. Read the Privacy Policy and Terms of Use to find out what the program will be able to do and what data it will collect. The last and most important part is to check the file list. Untick the boxes next to any additional programs that you did not choose to install.

Start the removal process
1. Look for suspicious browser extensions
You might be seeing the “McAfee Total Protection has expired” scam page because you have a malicious extension added to your browser, causing pop-ups, banners, redirects, and an overall increase of commercial content in your device. Even if you do not notice these symptoms we suggest investigating your browser.
The first thing you should do is go to your browser settings and check if you see any suspicious add-ons in the list. The best way to do this is by removing the extensions one by one and seeing if you notice any difference. You can follow our guide if you need help:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
2. Clear your browsers
Many websites use these tracking technologies to see the links you click on, things you purchase online, and other data like your IP address, geolocation, pages you visit, links you click on, and things you purchase online. Generally, this is not a bad thing as it helps websites and program developers to personalize the user experience.
But we see that more often, cookies[5] are used to generate revenue. They can be sold to advertising networks or other third parties and used to target you with ads even more. There have also been cases when cookies were hijacked and used for malicious purposes.
Security experts recommend clearing them regularly. It stops the tracking and deletes the collected data from your machine. This can become quite an annoying and lengthy process so you can use a maintenance tool like FortectIntego which will do this automatically with a click of a button. This powerful software can also fix various system errors, corrupted files, and registry issues which is especially helpful after virus infections.
3. Scan the system for adware
Scams like “McAfee Total Protection has expired” can also appear because of adware, so we strongly suggest using anti-malware tools like SpyHunter 5Combo Cleaner and Malwarebytes to scan your system. Adware is a type of program that generates commercial content like pop-ups, banners, and redirects on your machine to collect revenue.
Such PUPs (potentially unwanted programs) are mostly spread on freeware distribution sites. The owners of these platforms include additional programs in the installers without clearly disclosing this. Most people skip through the installation process and do not notice bundled software. That is why it is so important to have a tool that can detect these processes for you.
Professional security tools will scan your machine, eliminate intruders, and prevent such infections in the future by giving you a warning before a suspicious program can make any changes. Otherwise, you can use the guide below to remove the supposed antivirus if you have installed it or to try to identify any suspicious programs that should not be on your computer:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Josh Fruhlinger. Social engineering: Definition, examples, and techniques. Csoonline. Security Blog.
- ^ Potentially unwanted program. Wikipedia, the free encyclopedia.
- ^ Streaming online – know the risks. Crimestoppers-uk. Online Safety.
- ^ Francis Dinha. The Dangers Of P2P File-Sharing Sites. Forbes. Business Magazine.
- ^ Chris Maus. What Are Cookies and Are They Dangerous?. Qkey. Secure Online Payment Providers.








