Motherfirstcopy.xyz ads (scam) - Free Guide
Motherfirstcopy.xyz ads Removal Guide
What is Motherfirstcopy.xyz ads?
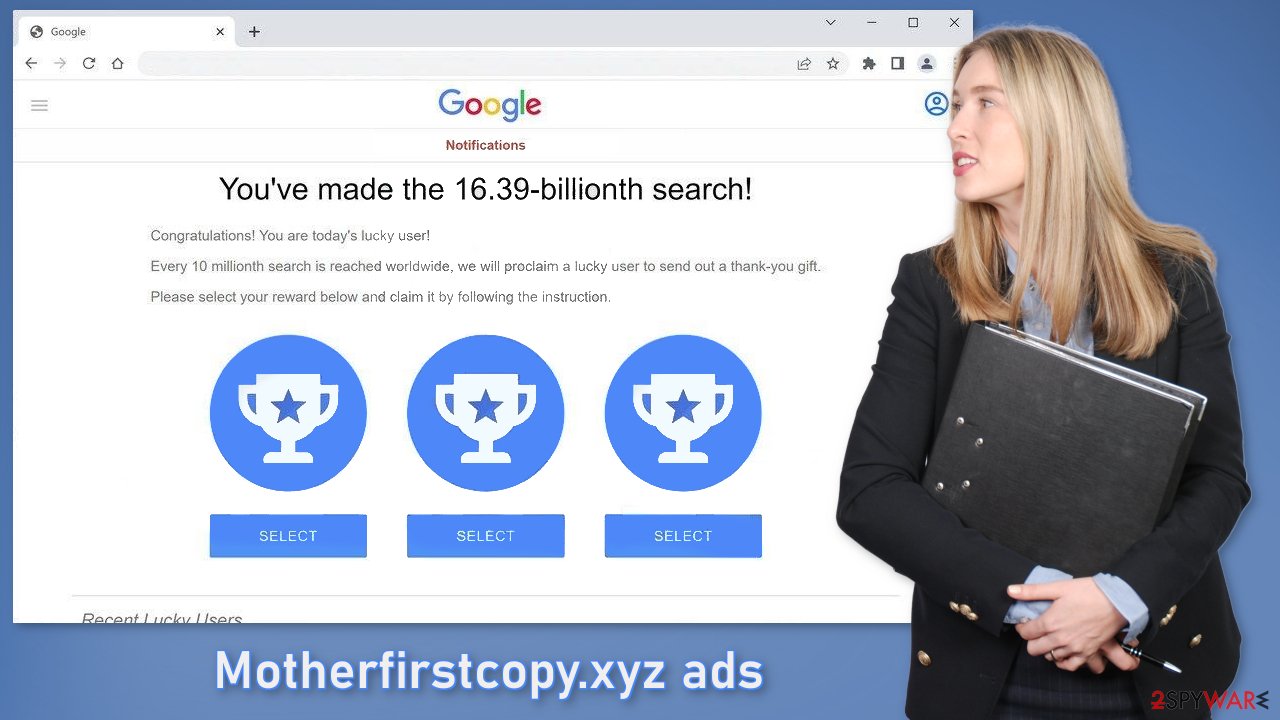
Motherfirstcopy.xyz uses Google's name to gain people's trust in a fake giveaway

Motherfirstcopy.xyz is a bogus website created by crooks to take advantage of Internet users. It displays a fake message to convince people that they have been chosen by Google as the lucky visitors. We previously discussed this phishing[1] attempt in “You’ve made the 16.39-billionth search!” scam article.
| NAME | Motherfirstcopy.xyz |
| TYPE | Phishing attempt; adware |
| SYMPTOMS | A page appears informing users that they have been supposedly chosen by Google as the lucky winners |
| DISTRIBUTION | Shady websites; deceptive ads; bundled software |
| DANGERS | Users could be tricked into providing personal information and suffer from monetary losses or even identity theft |
| ELIMINATION | Scan your system with professional security tools |
| FURTHER STEPS | Use a repair tool FortectIntego to optimize the machine and clear the browsers |
Motherfirstcopy.xyz in detail
The full message displayed by Motherfirstcopy.xyz reads as follows:
You've made the 16.39-billionth search!
Congratulations! You are today's lucky user!
Every 10 millionth search is reached worldwide, we will proclaim a lucky user to send out a thank-you gift.
Please select your reward below and claim it by following the instruction.
Crooks use social engineering[2] methods to trick users into thinking that they have been chosen by Google. The site may also ask people to fill out a form to supposedly be able to claim the gift. They could ask for the name, phone number, address, email, bank card details, etc.
This can result in monetary losses or even identity theft.[3] You should always be careful about giving out your personal details. Make sure to provide your data only to parties you absolutely trust. It is absolutely clear that Google has nothing to do with this fraudulent campaign and that crooks are only using their name to appear legitimate.
Fraudsters have done a decent job of making the website look like a notification from Google. At the bottom of the page, you may also see fake testimonies of people who supposedly claimed the gift successfully and are thanking Google for it. Always be wary of online giveaways that say you won an iPhone, a holiday on a cruise ship, a gift card, or anything else. If it is too good to be true – it probably is so think twice before entering very sensitive data onto a website you do not know.
Distribution methods
Usually, scam pages like Motherfirstcopy.xyz are not found in the search results. Most of the time, they hide in other shady pages. Websites that engage in illegal activities are unregulated and full of deceptive ads and sneaky redirects so there is a big chance that you clicked on the wrong link, ad, or a fake button that redirected you to the site.
Another possibility is that the page appeared without any user input. This could happen if there is a potentially unwanted program[4] hiding on the machine. That could be a malicious browser extension or adware – advertising-supported software. Some plugins are capable of hijacking the browser. They can start causing an increased amount of commercial content, like pop-ups, banners, and redirects.
Adware, on the other hand, can operate in the background of the machine without the users' knowledge. Generally, users download PUPs from unofficial pages that distribute freeware.[5] They include additional programs in the installers that monetize user activity. If users rush through the installation process and do not notice this, they install the PUA unknowingly.
To avoid this, next time go through all the installation steps. Choose the “Custom” or “Advanced” installation method, read the Terms of Use and the Privacy Policy. Most importantly, check the files up for installation. If you see any suspicious apps that look totally unrelated, untick the boxes next to their names.
Remove suspicious extensions
Because users reported that the redirect disappeared when they removed third-party extensions they have installed, let's try and do just that. You have to do this manually by going to your browser settings:
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ What Is Phishing?. Phishing. Scam Prevention.
- ^ Joe Pettit. 5 Social Engineering Attacks to Watch Out For. Tripwire. Security Insights.
- ^ Identity theft. Wikipedia, the free encyclopedia.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Tim Fisher. What Is Freeware?. Lifewire. Internet, Networking, and Security.














