Nefilim ransomware (Easy Removal Guide) - Recovery Instructions Included
Nefilim virus Removal Guide
What is Nefilim ransomware?
Nefilim ransomware – a file locking malware that threatens to publish the data publicly
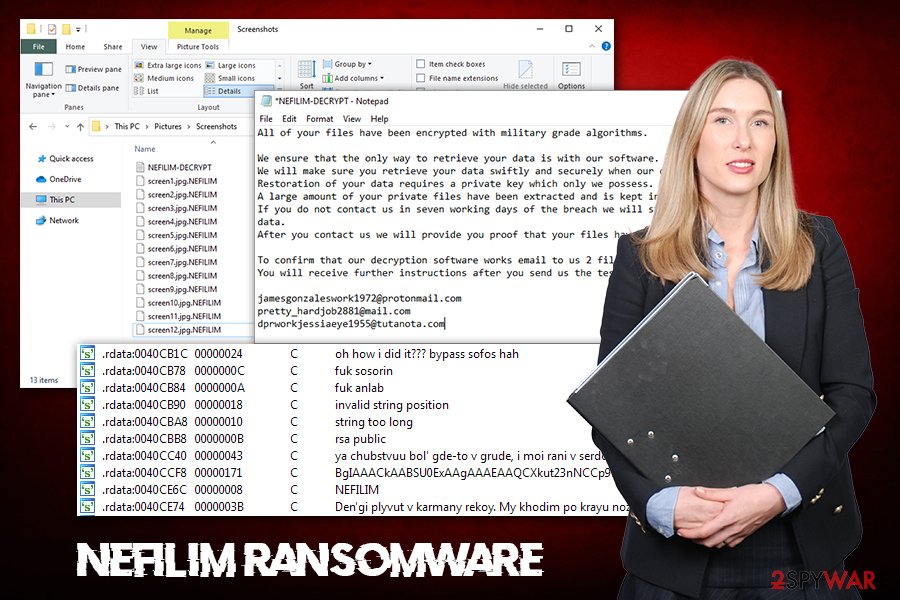
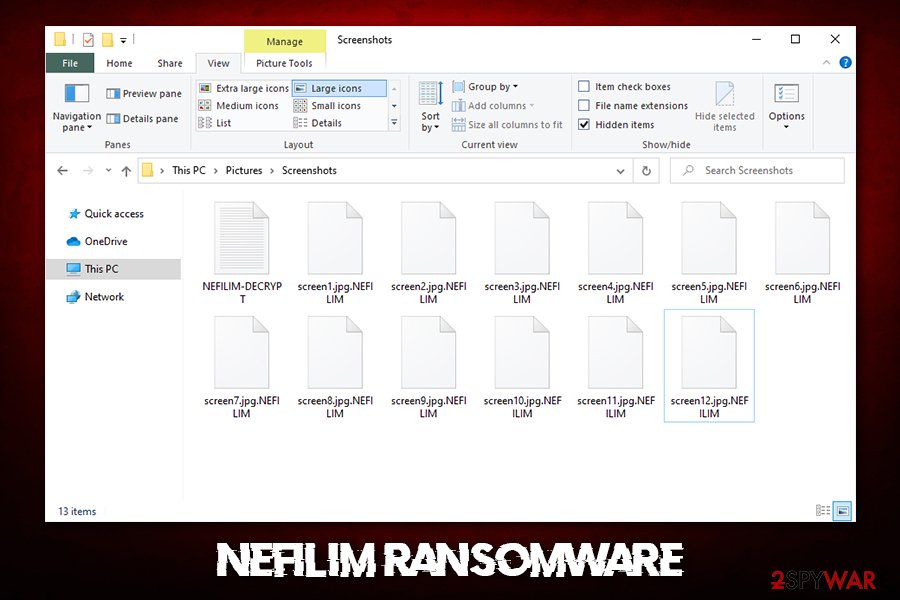
Nefilim ransomware is a data locker that uses extortion tactics in order to make you hand over the money to cybercriminals. Just like most other ransomware, this virus locks all personal files with the help of the RSA + AES encryption algorithm[1] and then demands a ransom payment in Bitcoin cryptocurrency. Each of such encrypted files receives a .NEFILIM extension and can no longer be accessed without the generated key that is stored on cybercriminals' C&C server.
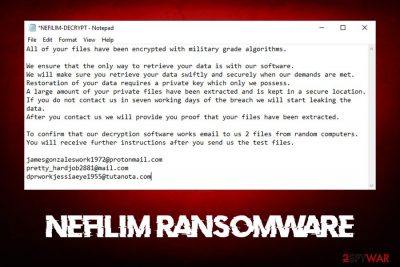
Additionally, the Nefilim virus also drops a ransom note NEFILIM-DECRYPT.txt, which explains what happened to the infected computer. In this note, crooks explain that they keep copies of all files on their servers. In case the ransom will not be paid within seven days, the data will be leaked and exposed online. This is a new tactic that increases the chances of a successful endeavor for cybercriminals.
For communication purposes, malicious actors ask victims to contact them via one of the following e-mails: jamesgonzaleswork1972@protonmail.com, pretty_hardjob2881@mail.com, or dprworkjessiaeye1955@tutanota.com. According to Nefilim ransomware developers, as soon as users send the email, they will be provided a proof cybercriminals indeed have copies of files.
| Name | Nefilim |
| Type | Ransomware, file locking virus |
| Encryption method | All local and networked files are encrypted with AES-128 + RSA-2048 cipher |
| A successor to | Nemty ransomware |
| File extension | All non-system and non-executable files are appended with .NEFILIM extension, e.g., a “picture.jpg” is turned into “picture.jpg.NEFILIM”. Another version of the ransomware uses .OFFWHITE! extension for encrypted data |
| Ransom note | NEFILIM-DECRYPT.txt or OFFWHITE-MANUAL.tx. Ransom note gets dropped into most folders located on the system, as well as the desktop |
| Contact | jamesgonzaleswork1972@protonmail.com, pretty_hardjob2881@mail.com or dprworkjessiaeye1955@tutanota.com, SamanthaKirbinron@protonmail.com, DenisUfliknam@protonmail.com, RobertGorgris@protonmail.com |
| Main executable | The file is signed by Sectigo RSA Code Signing CA |
| Demands | Cybercriminals threaten to publicly disclose all the encrypted files, which can be devastating for any business |
| Data recovery | As Nefilim ransomware is the newest version of Nemty, no decryption tool has yet been developed. Other methods include using third-party recovery software or built-in Windows tool to attempt to retrieve at least |
| Malware removal | Use reputable anti-malware software to scan your machine (access Safe Mode if required – we provide the instructions below) |
| System fix | If your computer seems to be unstable after you terminate the virus, you make use of FortectIntego in order to fix the damage done and recover the normal operation of the device |
Nefilim is a re-branded name of an already known strain – Nemty ransomware/Nemty Revenge 2.0, which mostly targeted high profile organizations and businesses, although regular users can be affected as well. It is yet unknown why the cybercriminal group decided to change the name, but they are using a similar pattern for file encryption and naming of the ransom note. Nevertheless, it is highly likely that malicious actors behind Nefilim ransomware changed the name due to a new scheme that they operate now
As of now, there are several tools that you could use for Nefilim ransomware removal, as over 40 engines detect the virus as follows:
- Win32:Malware-gen
- Ransom.NEFILIM!1.C3E7 (CLOUD)
- Ransom.Nefilim
- Win32/Filecoder.Nemty.D
- Mal/Generic-S
- Trojan-Ransom.Win32.JSWorm.d
Therefore, employ a sophisticated anti-malware software and perform a full system scan to remove Nefilim ransomware from your machine. Additionally, if your computer seems to lag, crash or suffer from similar stability issues after you get rid of malware, we suggest you repair it with FortectIntego.
Nefilim ransomware operation and data encryption
Nefilim ransomware authors are known to be sophisticated individuals who put their knowledge in coding for malicious deeds. The malware is spread by utilizing various exploits (RIG and Radio), fake websites, weakly protected RDP connections, as well as other methods – using several different attack vectors increases the chances of users being infected.
Security researchers previously noticed already that Nefilim virus' previous versions – Nemty – strangely used various clues hidden inside its code. For example, several references to experts were previously found within the written code – the new version now mentions SophosLabs and AhnLab in a particularly vulgar way.[2]
Another interesting feature of Nefilim ransomware is that the main executable used to infect the machine is signed by a valid certificate, which allows cybercriminals to prevent Windows from showing a warning about the file being potentially unsafe – this is another trick to avoid users from being suspicious during the initial infiltration process.
Once inside the system, Nefilim ransomware will implement the necessary changes to ensure that the encryption process would be successful. The virus performs the following:
- Exits if the keyboard language is set to one of the following: Russia, Belarus, Ukraine, Kazakhstan, Tajikistan, Azerbaijan, Armenia, Kyrgyzstan, and Moldova;
- Deletes all Shadow Volume Copies to prevent recovery;
- If available, it accesses backups and removes them;
- Gathers sensitive information about the company or the computer user;
- Modifies the Windows registry[3] for persistence, etc.
Once the necessary changes are complete, Nefilim ransomware begins the file encryption process, turning all normal data into inaccessible once – it targets the msot commonly-used files such as .jpg, .dat, .xlsx, gif, .pdf, and others, and appends each of them with .NEFILIM marker.
After that, malware drops the following ransom note:
All of your files have been encrypted with military grade algorithms.
We ensure that the only way to retrieve your data is with our software.
We will make sure you retrieve your data swiftly and securely when our demands are met.
Restoration of your data requires a private key which only we possess.
A large amount of your private files have been extracted and is kept in a secure location.
If you do not contact us in seven working days of the breach we will start leaking the data.
After you contact us we will provide you proof that your files have been extracted.To confirm that our decryption software works email to us 2 files from random computers.
You will receive further instructions after you send us the test files.jamesgonzaleswork1972@protonmail.com
pretty_hardjob2881@mail.com
dprworkjessiaeye1955@tutanota.com
As evident, crooks behind Nefilim ransomware are threatening to release the stolen data to the public, which can ultimately compromise any organization or business. However, this increases the chances of ransom payment to be made. If you decide to pay, keep in mind that hackers might never send you the required Nefilim ransomware decryptor, so you may up losing all your money, and they might still publish your data regardless.
Instead, we suggest you recover your data from backups and ensure that no future infections happen. For that, check the tips provided in the following section. Note that, if you did not have backups or they got encryption, you should copy all .Nefilim files over before trying to apply third-party software or using other methods.
Prevent your computer from being infected with ransomware
Nefilim ransomware developers use Ransomware-as-a-Service (RaaS) scheme in order to propagate the malware and receive profit from it. As a result, different cybercriminals who take on the task use different methods to infect users and companies worldwide. As mentioned above, various techniques were used, including exploit kits, web injects, drive-by downloads, unprotected Remote Desktop connections, etc.
If you are already infected, there is not much you can do apart from trying to remediate the situation. Nevertheless, you need to ensure that this devastating situation would not happen in the future. For that, you should:
- Employ sophisticated anti-malware software and keep it updated;
- Keep all the software and the operating system up to date at all times;
- Use strong passwords to protect your RDP connections and other accounts;
- Disable RDP as soon as it is not needed and use non-default port to establish the connection;
- Do not allow email attachments to run macro function (“Allow content”);
- Educate your staff about cybersecurity and safe computer handling practices;
- Enable Firewall and install ad-block on all web browsers;
- Do not download pirated software installers or software cracks.
Additionally, it is essential to keep backups separated from your computer and the network it is connected to. In such a case, you could restore all the files without paying cybercriminals, although they might still publish the stolen information online.
Nefilim ransomware elimination and data recovery
It is important to note that the infection of the computer or the network and data encryption are completely separate procedures, although it is possible to do the latter with the help of the former one only. Therefore, Nefilim ransomware removal will not retrieve access to your data – you need to use backups instead. If you had no backups, ensure that you make a copy of the encrypted data before you do anything, as further actions may permanently damage the files.
Then you need to remove Nefilim ransomware from the computer and the infected network. To do that, employ reputable anti-malware software and perform a full scan to ensure that all the malicious files are eliminated. If the procedure was unsuccessful, you can access Safe Mode with Networking as explained below and then initiate a scan – we provide the instructions on how to do that below.
Finally, after Nefilim virus elimination, you can attempt data redemption. For that, you can try third-party software like Data Recovery Pro or ShadowExplorer. If you were lucky enough, you could potentially recreate at least some of your files embedded in your hard drive. Note that security researchers created a decryptor for previous ransomware versions so that it might be possible for Nefilim ransomware as well.[4]
Getting rid of Nefilim virus. Follow these steps
Manual removal using Safe Mode
To get rid of Nefilim file virus, perform a full system scan in Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Nefilim using System Restore
System Restore can also be used to delete malware from your system:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Nefilim. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Nefilim from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Nefilim, you can use several methods to restore them:
Data Recovery Pro is one of the tools you can use for file recovery
If you did not use the computer much after the infection occurred, this method might be helpful.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Nefilim ransomware;
- Restore them.
Make use of Windows Previous Versions feature
This feature might help you recover files one-by-one if malware failed to delete Shadow Volume Copies, and you had System Restore enabled.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer may sometimes get all your files back
This tool may be successful in recovering all data in some cases.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Nefilim and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Encryption algorithm. Webopedia. Online Tech Dictionary for Students, Educators and IT Professionals.
- ^ MalwareHunterTeam. Nemty ransomware became "NEFILIM" ransomware.... Twitter. Social Network.
- ^ Windows Registry. Wikipedi. The free encyclopedia.
- ^ A decryptor for the Nemty ransomware based on analysis of its cryptography. Tesorion. Security research blog.





















