NetProcess Mac virus (Tutorial)
NetProcess Mac virus Removal Guide
What is NetProcess Mac virus?
Found a NetProcess extension on Safari? You have a dangerous Adload malware on your device
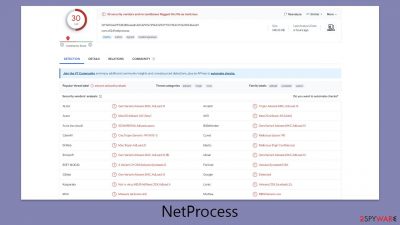
NetProcess is a malicious application targeting Mac computers, designed to compromise web browsers, display intrusive advertisements, and resist straightforward removal methods. This application is part of the expansive Adload malware family, notorious for its creators releasing numerous variants endowed with harmful capabilities.
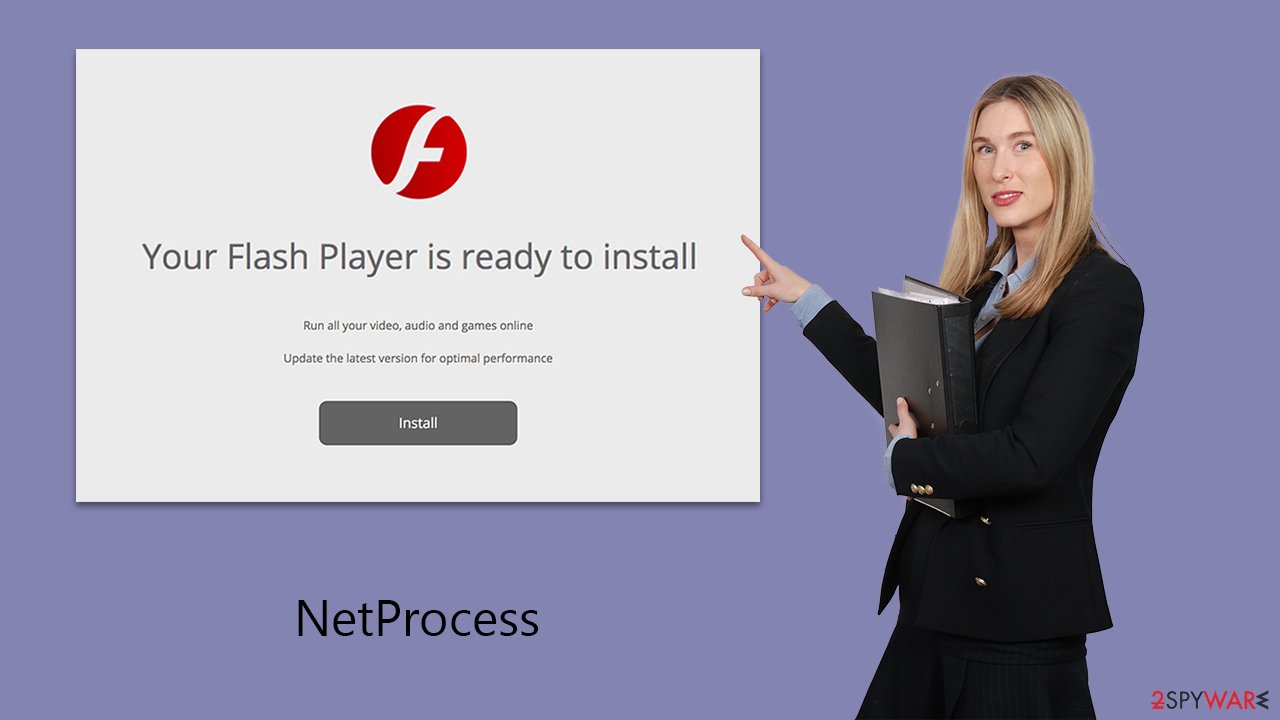
The dissemination of NetProcess and its kin often involves unsophisticated yet efficient vectors, including the use of cracked software installers and counterfeit updates for obsolete software like Adobe Flash Player. Despite the simplicity of these methods, they are alarmingly effective, leading to the widespread infection of numerous users daily.
Once active on a system, NetProcess exposes the user to a variety of online hazards. These include deceptive alerts about malware infections, fraudulent promotional offers, and dubious schemes promising quick financial gains. Moreover, it aggressively bombards the user with a slew of advertisements, such as pop-ups, autoplay videos, and banner ads, during their web sessions across different browsers like Safari, Chrome, and Firefox, which have been compromised by this malware.
| Name | NetProcess |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Malware can be downloaded along with pirated software installers or via fake Flash Player updates |
| Symptoms | Installs a new extension and application on the system; changes homepage and new tab of the browser; inserts ads and malicious links; tracks sensitive user data via extension |
| Removal | Although not recommended to novice users, manual elimination of Mac malware is possible. We recommend performing a full system scan with SpyHunter 5Combo Cleaner and removing all the malicious components automatically |
| System optimization | Malware and adware can meddle with your system, reducing its performance. If you want to quickly fix various issues, we recommend you try using automated tools like FortectIntego |
Distribution tactics explained
The distribution mechanism of NetProcess, a malicious software under the Adload malware family umbrella, relies heavily on exploiting the guise of Adobe Flash Player installers, with “Player.app” frequently employed as a deceptive package name. This method leverages deceptive advertisements suggesting that the Flash plugin is out-of-date and necessitates an immediate update to access multimedia content on certain web pages.
Given Flash's extensive history and its ultimate discontinuation due to significant security vulnerabilities, any prompt suggesting a Flash update should be immediately regarded as a scam aimed at infiltrating Mac computers with this harmful software.
Moreover, the spread of NetProcess is not limited to counterfeit Flash updates. It also encompasses the distribution through software cracks and pirated software installers. These avenues, inherently illegal, significantly amplify the susceptibility of users to malware threats.
Individuals exploring peer-to-peer (P2P) networks and other similar environments for software acquisition face a heightened risk of encountering and inadvertently installing malicious applications like NetProcess. In light of these risks, it is imperative for users to practice caution and avoid these channels. Adhering to legitimate sources for software downloads and updates is a critical preventive measure against the infiltration of malware.
Characteristics and what to look out for
Adload malware has been compromising Mac systems since 2017. Despite being among numerous iterations released over time, it stands out for its widespread impact on users worldwide. The creators of NetProcess are unknown, yet its connection to other prominent Mac malware, such as the Shlayer Trojan, suggests its involvement in a larger scheme of malicious operations.
The fundamental objective of the virus is to monetize its presence on infected devices by injecting unsolicited advertisements into users' browsers. These advertisements often originate from disreputable ad networks, leading to the display of low-quality content. This strategy extends beyond mere nuisance, potentially steering users towards unsafe websites and dubious advertising materials.
A particularly stealthy aspect of the NetProcess virus is its deployment of a man-in-the-middle proxy, which reroutes internet traffic through servers under the control of cybercriminals. This redirection not only facilitates financial gain for the attackers through manipulated web traffic but also heightens the risk of users encountering malicious online content.
Moreover, the malware secures extensive permissions during its installation process, enabling the associated browser extension to harvest sensitive personal information. This data collection spans credit card details to login credentials, exposing users to significant risks such as financial loss and identity theft.
NetProcess represents a multifaceted threat to Mac users, encompassing everything from irritating advertisements to profound privacy breaches and financial harm. Its enduring presence, links to a broader malware network, and multifarious harmful functionalities underscore the critical threat level it poses, necessitating ongoing vigilance from users.
How to remove the NetProcess virus
The presence of multiple Adload variants, including NetProcess, RadioDiskInput, ResourceActivity, and HelperFraction, on a single device is not uncommon. The concurrent operation of several versions indicates a broader infiltration of malicious files within the system, complicating the removal process. Managing these threats manually can prove to be particularly challenging, given the complexity and resilience of each variant.
In light of this, leveraging robust security software like SpyHunter 5Combo Cleaner or Malwarebytes becomes crucial. Such applications are designed to be unaffected by the malware's defensive mechanisms, ensuring the automatic detection and removal of these malicious entities. An important component of the cleanup process also involves purging the web browsers affected by these variants. Malware can leave behind residual files that continue to track data and cause additional privacy concerns.
For those preferring or necessitating manual removal, it is essential to meticulously follow a comprehensive guide tailored to address all malware variants. This methodical approach is vital for thoroughly eliminating the malware and mitigating the risks associated with their presence on the device. Alternatively, follow the steps provided below:
Remove the main app components
Malware would launch background processes as soon as it was installed to continue operating. Therefore, you should check Activity Monitor and end any dependent processes before moving further with the primary app's uninstallation.
- Open Applications folder
- Select Utilities
- Double-click Activity Monitor
- Here, look for suspicious processes related to the virus and use the Force Quit command to shut them down
- Go back to the Applications folder
- Find the malicious app in the list and move it to Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
While Profiles takes care of various account settings, Login items are in charge of running the malicious program as soon as the machine turns on. To remove these malware-related components, do the following:
- Go to Preferences and pick Accounts.
- Click Login items and delete everything suspicious.
- Next, pick System Preferences > Users & Groups.
- Find Profiles and remove unwanted profiles from the list.
Finally, you need to remove any Launch Daemons and other configuration files that malware may have left behind.
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Cleaning your browser
If you have chosen a manual method of removal, you should take care of the OperativeIndexer extension, which is attached to your web browser. Keep in mind that it's used to read personal information such as account details or passwords, so make sure you don't leave it behind. If this step is not possible, proceed with the next one.
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
If you were unable to remove malware from your web browser, you might reset it as we describe below. You won't lose your bookmarks or other settings.
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
If you successfully removed the extension traditionally, you should also clear your browser caches to stop any more data from being tracked. This can be done either manually or with tools like FortectIntego.
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Getting rid of NetProcess Mac virus. Follow these steps
Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.












