RadioDiskInput Mac virus (Free Guide) - Tutorial
RadioDiskInput Mac virus Removal Guide
What is RadioDiskInput Mac virus?
RadioDiskInput – a malicious Mac application that intercepts traffic and links to malicious websites

Adware remains the largest problem with macOS, and there are new attacks targeted at Macs every year. The RadioDiskInput malware belongs to the Adload adware family, which has been targeting macOS devices for several years with minimal changes between iterations. Although many of the strain's characteristics have not altered, the cybercriminals who designed it have been making modifications to increase the infection's longevity and propagation.
The primary goal of this rogue app, RadioDiskInput, is to maximize revenue from advertising. Following infection, users often encounter a variety of harmful content online, such as malicious links, phishing websites, and online scams. This is due to the strain's connections to a large number of other possibly undesirable programs and dangerous websites. It is true that not every pop-up or link is dangerous, but there is no way to know which ones are safe to click on.
| Name | RadioDiskInput |
| Type | Mac virus, adware, browser hijacker |
| Malware family | Adload |
| Distribution | Fake Flash Player installers or bundled software from malicious sources |
| Symptoms | Installs a new extension and application on the system; changes homepage and new tab of the browser; inserts ads and malicious links; tracks sensitive user data via extension |
| Removal | You can remove Mac malware with the help of powerful security tools, such as SpyHunter 5Combo Cleaner or Malwarebytes. We also provide manual removal steps below |
| Security tips | Potentially unwanted applications often leave traces within web browsers – cookies, for example, are used for tracking. You should get rid of these leftovers with FortectIntego or employ our manual guide |
How malware spreads and infects Mac users
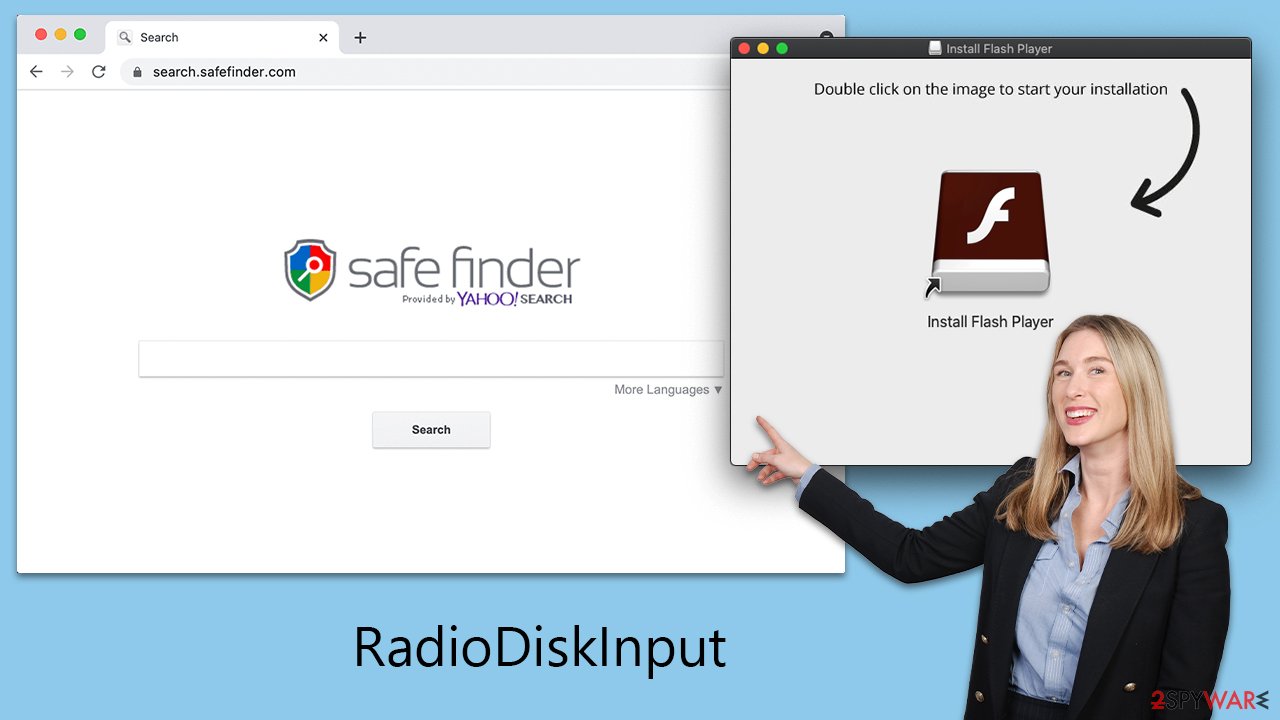
The two main ways that adload versions are distributed are through software cracks/pirated installers and fake Flash Player updates.
The most popular method used to propagate Adload versions is through bogus Flash Player updates. Operators fabricate phony websites that imitate the design of authentic Adobe webpages in an attempt to trick visitors into downloading a fake version of Flash Player. The user inadvertently downloads and installs the virus on their computer when they click the download button. This is one of the main reasons why Adobe had to terminate it and stop all support.
Software cracks and pirated software installers are two other ways that this virus is propagated. These techniques are frequently used to distribute software, which usually needs to be purchased legally. These illicit downloads might secretly contain the virus, which would cause the victim to install it without realizing it.
In order to protect Mac users from malware such as RadioDiskInput, users must follow security procedures. This entails only downloading software from reputable sites, avoiding questionable links, and not opening attachments from unreliable sources. Updating anti-virus software and implementing responsible surfing practices are essential for bolstering security against these kinds of online attacks.
Main characteristics of the virus
After infection, the virus instantly alters Mozilla Firefox, Google Chrome, or Safari; the most obvious change is to the homepage, which is done to monetize advertisements. It is typically swapped out for something else, such as Shlayer Trojan, another dangerous app exclusive to Mac users.
As a result, inquiries frequently go over several channels before reaching their intended destination. The search results are sometimes also not what visitors were expecting because a different default search provider (such as Bing or Yahoo) is utilized and a ton of advertisements are displayed at the top. It is risky to click on these links because RadioDiskInput might promote rogue websites that are infected with further viruses or try to sell memberships to services that aren't real.
Not only may the rogue app cause frustrating and perhaps harmful browser modifications, but it can also have a severe effect on a user's security and privacy. The malware deploys itself with elevated permissions during installation, enabling it to use AppleScript in any way it pleases. This fully evades the detection of XProtect and other built-in Mac defenses.
Malware can monitor users' browser activity and gather passwords, account information, and even credit card details with the use of enhanced permissions. As a result, it is advised against disclosing any sensitive information while the device is still infected as doing so could seriously jeopardize privacy.
How to remove the virus from the system?
Even though RadioDiskInput may not be considered extremely complex malware, Mac users are nevertheless at significant risk from it. Through its persistent tactics, it has proven its capacity to evade Mac systems' defenses, frequently outpacing Apple's security patches. As such, it may continue to function in the background of the system for extended periods of time if it is not successfully removed.
Users can use third-party security apps such as SpyHunter 5Combo Cleaner or Malwarebytes to remove malware more quickly. Owing to the virus's propensity to generate several files while infecting a computer, manual eradication can be difficult and demand advanced technical skills. The malware could resurface if you overlook even one file during the process.
However, exercise caution when working with browsers if you decide to manually remove the malware. For increased privacy, it's critical to remove cookies and other items from browser caches. As an alternative, you can remove the malware automatically without the need for human participation by using FortectIntego.
To uninstall an application on a Mac, you typically move it to the Trash. Before doing this, ensure that any background malware processes have been shut down:
- Open the Applications folder.
- Select Utilities.
- Double-click Activity Monitor.
- Look for any suspicious processes related to adware and use the Force Quit command to stop them.
- Return to the Applications folder.
- Find ExtendedService in the list and move it to the Trash.
![Uninstall from Mac 1 Uninstall from Mac 1]()
Upon infection, the malware might create new User profiles and Login items, making it difficult to remove the app or extension. Thus, you should remove these components as follows:
- Go to Preferences and select Accounts
- Click Login items and delete everything suspicious
- Next, pick System Preferences > Users & Groups
- Find Profiles and remove unwanted profiles from the list.
To remove the leftover configuration data and Launch Daemons of the malware:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any suspicious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and delete all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Your next task is to take care of your browsers. If you have removed the virus with security software, you can skip to the section for cache removal. Otherwise, you'll have to remove the extension first:
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
If you are unable to delete the extension, we strongly recommend resetting the web browser:
Safari
- Click Safari > Preferences…
- Go to the Advanced tab.
- Tick the Show Develop menu in the menu bar.
- From the menu bar, click Develop, and then select Empty Caches.
![Reset Safari Reset Safari]()
Google Chrome
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
Once you have completed the task, it is recommended that you clean all your web data and cookies to ensure your privacy. Follow the steps below in order to do this:
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.








