OnlyFans malware (scam)
OnlyFans malware Removal Guide
What is OnlyFans malware?
OnlyFans malware uses social engineering techniques to get into people's computers

OnlyFans, an online platform that allows content creators to monetize their explicit material, has grown in popularity in recent years, revolutionizing the adult entertainment industry. However, as its user base has grown and the allure of exclusive paid content has grown, a new and sinister threat has emerged: OnlyFans malware. This insidious campaign uses deceptive techniques to prey on the desires of people looking for free access to premium content. Let us look into the specifics of this malicious phenomenon.
| NAME | OnlyFans |
| TYPE | Trojan, password-stealing virus, banking malware, spyware |
| SYMPTOMS | Symptoms may include, among other things, losing access to files or online accounts. |
| DISTRIBUTION | Infected email attachments, malicious online advertisements, social engineering, and “cracked” software installations |
| DANGERS | Stolen passwords and banking information, identity theft, computer inclusion in a botnet, data loss, financial loss, and other problems |
| ELIMINATION | Use professional security tools for complete malware removal |
| FURTHER STEPS | Fix damaged system files with a maintenance tool like FortectIntego |
VBScript loaders and DcRAT: unleashing chaos
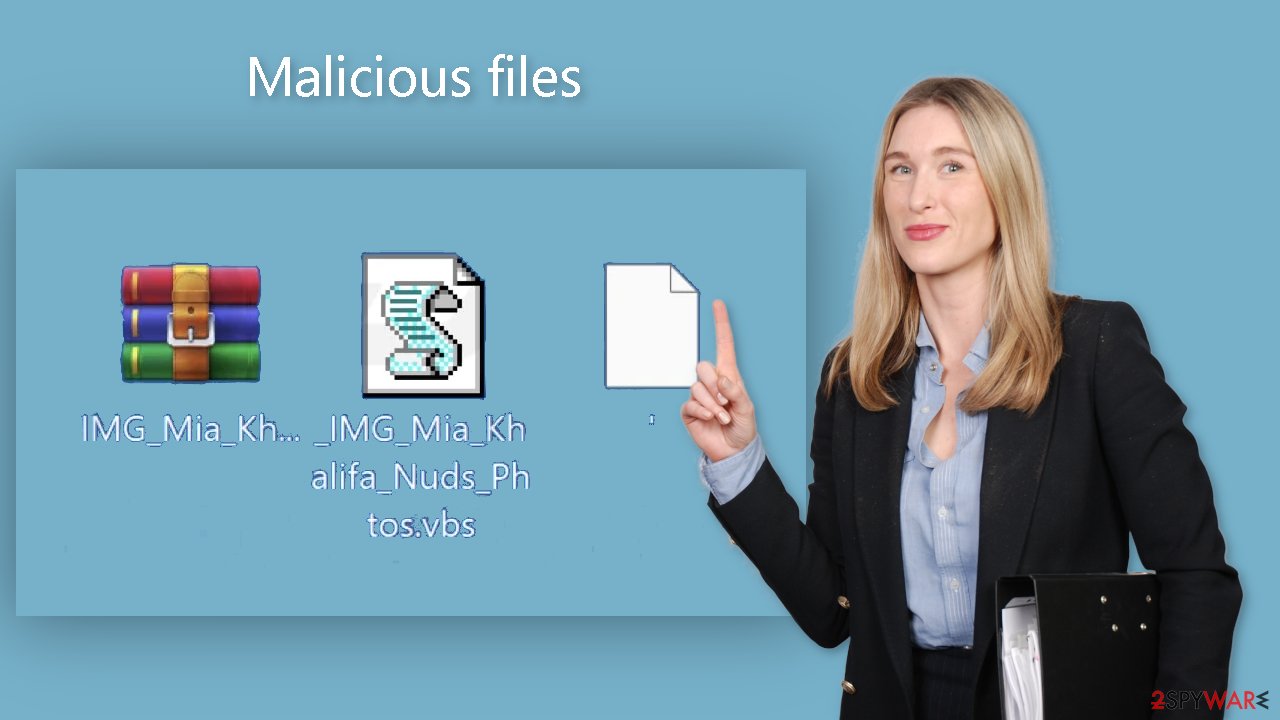
The distribution of ZIP files containing a VBScript loader disguised as highly coveted premium OnlyFans collections is at the heart of the OnlyFans malware campaign. Victims unknowingly execute these deceptive files after being enticed by the prospect of gaining access to explicit photos and content associated with various adult film actresses. While the exact method of infection is unknown, possible sources of infection include malicious forum posts, instant messages, malvertising, and Black SEO sites.
DcRAT, a Remote Access Trojan (RAT), is one of the prominent payloads observed in the OnlyFans malware campaign. This sophisticated malware has a wide range of malicious functionalities, making it a potent weapon in cybercriminals' hands. DcRAT's arsenal includes keylogging, webcam monitoring, file manipulation, and remote access to compromised systems.
DcRAT does not stop at invading privacy and security boundaries; it can also steal web browser credentials and cookies, seize Discord tokens, and even include a ransomware plugin. DcRAT collects sensitive information by keylogging and monitoring webcams, jeopardizing individuals' privacy. Theft of credentials and cookies can lead to unauthorized access to personal accounts, which can lead to identity theft and financial loss.
Unauthorized access to Discord accounts can also harm a user's reputation and facilitate further malicious activity. The ransomware plugin adds another layer of potential devastation by encrypting files and demanding ransom payments to unlock them. Such actions have the potential to cause significant disruption, resulting in data loss and severe consequences for victims.
Stay one step ahead
As the threat of OnlyFans malware grows, it is critical to take preventative measures to safeguard yourself and your digital assets. Here are some crucial steps to strengthen your defenses:
- Keep Your Systems Updated: regularly update your operating system and software with the latest security patches to minimize vulnerabilities.[1] Cybercriminals often exploit outdated software as an entry point into systems.
- Exercise Vigilance: exercise caution when handling email attachments or interacting with suspicious links, especially those originating from unfamiliar or untrusted sources. Beware of enticing offers for free access to premium content, as they might be traps laid by cybercriminals.
- Utilize Antivirus and Anti-Malware Software: install reputable antivirus and anti-malware software on your devices. Keep them updated[2] and conduct regular scans to identify and eliminate potential threats.
- Practice Safe Browsing Habits: avoid downloading files from untrusted websites and exercise caution when confronted with pop-up advertisements or deceptive download buttons. Stick to reputable sources and exercise skepticism when encountering unfamiliar or suspicious websites.
Removal of OnlyFans malware
The removal of remote-access trojans can be a difficult task. When such an infection enters a machine, it makes extensive changes to system files and settings in order to establish persistence, making it extremely difficult to detect. It is usually best to let antivirus or anti-malware programs do this automatically.
In some cases, however, malware may disable your anti-malware tools and disguise its processes as legitimate Windows tasks. If malware prevents you from using antivirus in normal mode, boot into Safe Mode and run a full system scan from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
Once in Safe Mode, you can run a reliable antivirus program. We recommend using trusted professional security tools SpyHunter 5Combo Cleaner or Malwarebytes. To remove malware and all of its malicious components, you should update the security program of your choice with the most recent definitions and run a full system scan.
A scan should detect all malicious files on your device, isolate them, and provide you with the option of removing them. Every person who spends at least a few minutes per day on the internet should have reliable anti-malware software. Cybercriminals are becoming more inventive in their methods of disseminating their dangerous creations. The primary means of defense are anti-malware tools.
Fix the damaged operating system
When a computer is infected with malware, its operating system is altered. An infection, for example, can alter the Windows registry database, harm vital bootup and other sections, delete or corrupt DLL files, and so on. When a system file is damaged by malware, antivirus software is powerless to repair it, leaving it in its current state. As a result, users may encounter performance, stability, and usability issues, necessitating a full Windows reinstallation.
As a result, we strongly advise using a one-of-a-kind, patented FortectIntego repair technology. It can not only repair virus damage after infection, but it can also remove malware that has already infiltrated the system, thanks to the program's various engines. Furthermore, the application can repair a variety of Windows-related issues that are not caused by malware infections, such as Blue Screen errors,[3] freezes, registry errors, damaged DLLs, and so on.
You won't have to worry about future computer problems if you use FortectIntego, because most of them can be resolved quickly by running a full system scan at any time. Most importantly, you can avoid the time-consuming process of reinstalling Windows if something goes horribly wrong for whatever reason.
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ The 25 most dangerous software vulnerabilities to watch out for. Zdnet. Computer Security.
- ^ Why is it Important to Update Security Patches?. Netcov. IT Support and Services.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. Howtogeek. Technology Magazine.







