OopsLocker ransomware / virus (Decryption Steps Included) - Virus Removal Guide
OopsLocker virus Removal Guide
What is OopsLocker ransomware virus?
OopsLocker – malware that demands 0.1 Bitcoin after file encryption
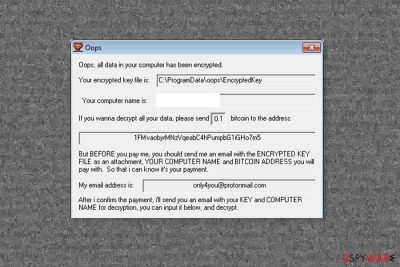
OopsLocker is a new variant of recently emerged Oops ransomware virus. Malware employs a combination of AES and RSA cryptography and appends .oops extension to each of the targeted files. According to the ransom note, delivered in the oops.exe file, victims need to pay 0.1 Bitcoin for the decryption.
| Name | OopsLocker |
| Type | Ransomware |
| Encryption method | AES + RSA |
| File extension | .oops appended to all personal files on the infected computer |
| Removal | Perform a full system scan with anti-malware software |
| System fix | Once malware is eliminated, we recommend scanning the device with FortectIntego repair tool that can fix virus damage to system files |
Usually, the virus arrives on the system with the help of malicious email attachments. When users open obfuscated Word documents and enable macros, ransomware executable is dropped on the system. Then it connects to its Command and Control (C&C) server and downloads new files to the affected system:
- oops.exe– decryption software,
- EncryptedFiles.txt – the list of encrypted files on the targeted computer.
The virus installs these files in a new folder called ProgramData in C disk. Here malware also creates EncryptedKey and KeyHash directories where it installs encrypted decryption key and the map of the encrypted files.
OopsLocker ransomware also sends particular information about the computer to the remote C&C server. This data includes:
- IP address,
- the version of Windows operating system,
- keyboard setup,
- information about computer’s protection and antivirus software.
Then malware settles in, it starts scanning the system looking for the targeted file extensions. The crypto-malware aims at more than 40 different files, including MS Office documents, various images, audio, video files, backups, etc. It locks the files with the .oops extension and runs a program window with data recovery options.
In order to decrypt locked files, users have to send an email to only4you@protonmail.com with their computer’s name, Bitcoin address where they have to pay the ransom and attach the “EncryptedKey” file. Then victims have to pay 0,1 Bitcoin in a week. Otherwise, the size of the ransom will double every single week.
However, following these instructions may not lead to data recovery. You might just waste more than $200 and sponsor further crook’s projects. There are many cases when cybercriminals did not keep their word and did not provide decryption tools after the payment.[1] Thus, we highly recommend spending your money on professional software that will help to remove OopsLocker from the device.
Only security software can assure safe and effective ransomware elimination. Trying to locate and delete all malicious files from the system might not end up good. Crypto-malware might affect legitimate processes or use names of real system files, so you can accidentally delete the wrong files. To avoid bigger damage, you should perform virus removal with SpyHunter 5Combo Cleaner or another malware removal program.
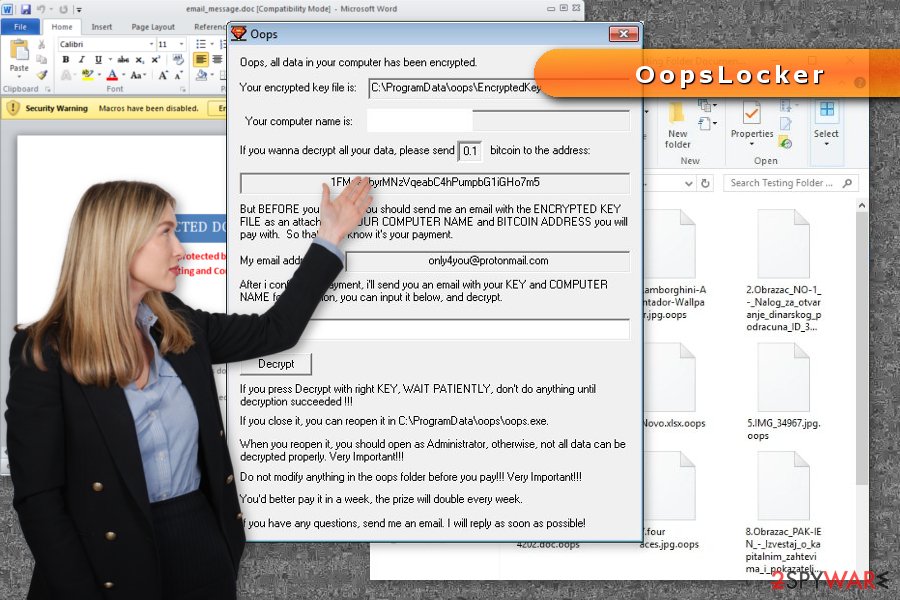
Malware enters the device with the help of obfuscated Word file
The main distribution method of ransomware is malicious spam emails. The executable of crypto-malware is camouflaged and attached to an email as a regular Word file. However, this file has malicious macro commands.
When a user opens this document, he or she receives an alert to enable macros to see the provided content. When a person does that, malicious commands are launched, and malware enters the system.
Keep in mind that dangerous letters might look like ordinary emails sent from governmental organizations, delivery services, or popular online shops, such as Amazon. However, before clicking provided documents, you have to make sure that it’s not a phishing email.[2]
However, security experts from No Virus[3] point out that crooks are getting better and better in social engineering. Thus, you should also be critical. If you do not expect to receive a statement from a bank or haven’t ordered any parcel, you should delete such emails immediately without checking what hides inside.
Withdrawal of the OopsLocker virus
As we have mentioned earlier, OopsLocker removal is achieved with the help of security software. We recommend to our readers to use SpyHunter 5Combo Cleaner or Malwarebytes to terminate the virus safely from the system. Also, FortectIntego can be used to fix virus damage and remediate Windows so it would run properly, without errors, afterward.
Ransomware might not allow the installation of security software or prevent it from installing or running it. If you have encountered one of these problems, you should check our instructions below. They will explain how to activate antivirus and remove malware automatically.
Getting rid of OopsLocker virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove OopsLocker using System Restore
System Restore also helps to disable the virus in order to delete it automatically.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of OopsLocker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove OopsLocker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by OopsLocker, you can use several methods to restore them:
Try Data Recovery Pro to set free files with .oops extension
This professional software helps to recover deleted, corrupted and some of the encrypted files. Users noticed that it's irreplaceable recovery tool after ransomware attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by OopsLocker ransomware;
- Restore them.
Windows Previous Versions feature allows copying individual files
If System Restore has been activated on your PC before ransomware attack, follow the steps to copy individual files:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer restores files from Shadow Volume Copies
Malware is not supposed to delete Shadow Volume Copies of the targeted files. Thus, you should be able to recover data using this tool:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
OopsLocker decryptor hasn't been released yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from OopsLocker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ David Glance. WannaCry hackers had no intention of giving users their files back even if they paid. The Conversation. In-depth analysis, research, news and ideas on various topics.
- ^ 7 Ways to Spot a Phishing Scam. ZoneAlarm Security Blog. News and information about internet security, online threats and safe web practices.
- ^ NoVirus. NoVirus. British site about computer viruses.





















