Phmqdw ransomware (virus) - Recovery Instructions Included
Phmqdw virus Removal Guide
What is Phmqdw ransomware?
Phmqdw ransomware creators ask victims for payment in cryptocurrencies to get their files back
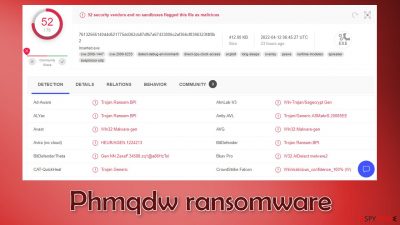
Recently, ransomware researchers detected a new strain of malicious programs called Phmqdw. It belongs to the Makop ransomware family and is a file locking malware. When it infiltrates the system, it immediately starts the encryption[1] process. After the encryption process is done, the malicious program appends a .phmqdw extension to every affected file, and the icons turn to white pages. Usually, this includes personal files, like photos, videos, and documents.
If a file was previously named picture.jpg, it would now look like picture.jpg.[victimID].phmqdw. This makes the files impossible to open, view, and use. Threat actors then generate a ransom note _readme.txt which informs victims about what has happened to their files.
| NAME | Phmqdw |
| TYPE | Ransomware, cryptovirus, data locking malware |
| MALWARE FAMILY | Makop |
| DISTRIBUTION | Infected email attachments, torrent sites, malicious ads, drive-by downloads |
| FILE EXTENSION | .phmqdw |
| RANSOM NOTE | _readme.txt |
| FILE RECOVERY | It is almost impossible to recover the files if you do not have backups; in this guide, you will find third-party options for file recovery |
| MALWARE REMOVAL | Scan your machine with anti-malware software to eliminate the malicious files |
| SYSTEM FIX | Windows reinstallation can be avoided with FortectIntego maintenance tool, which can fix damaged files |
The ransom note
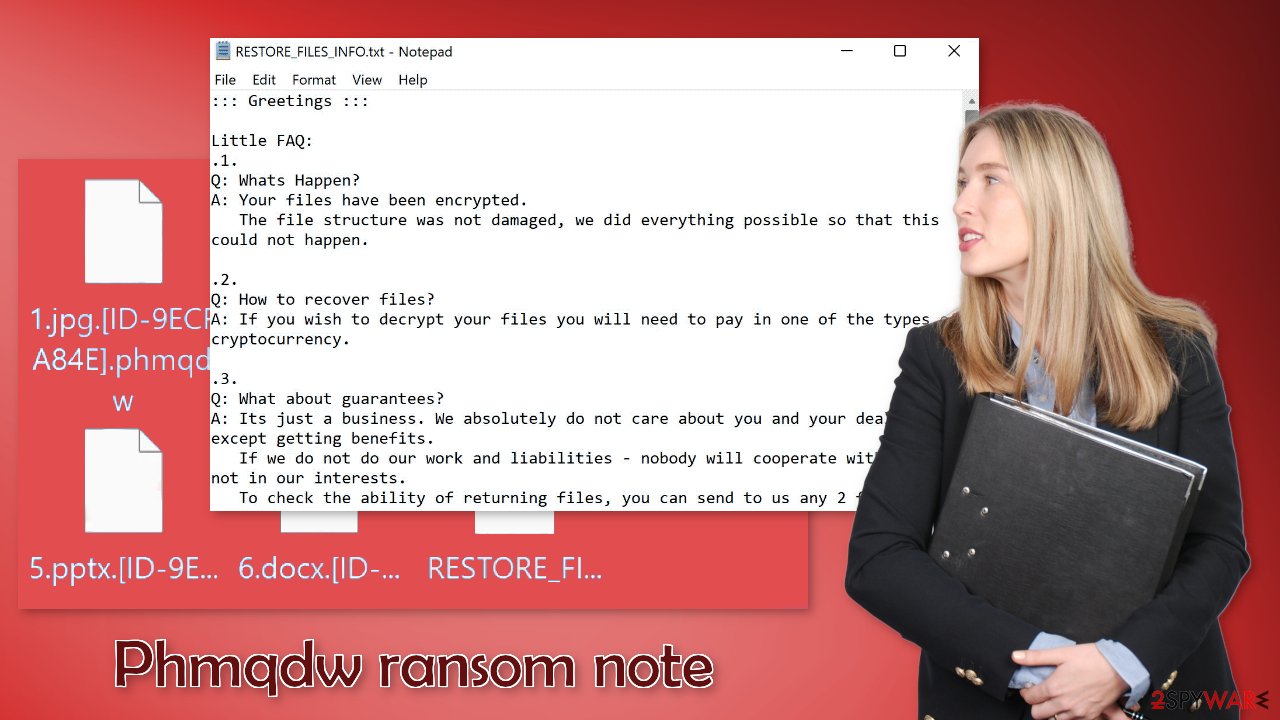
The full _readme.txt ransom note reads as follows:
::: Greetings :::
Little FAQ:
.1.
Q: Whats Happen?
A: Your files have been encrypted.
The file structure was not damaged, we did everything possible so that this could not happen..2.
Q: How to recover files?
A: If you wish to decrypt your files you will need to pay in one of the types of cryptocurrency..3.
Q: What about guarantees?
A: Its just a business. We absolutely do not care about you and your deals, except getting benefits.
If we do not do our work and liabilities – nobody will cooperate with us. Its not in our interests.
To check the ability of returning files, you can send to us any 2 files with SIMPLE extensions(jpg,doc, etc… not databases!)
and low sizes(max 1 mb), we will decrypt them and send back to you. That is our guarantee..4.
Q: How to contact with you?
A: Please, write us to our qTOX account: 32308809B05685C4B36DBD3230D3BBCEDB137 21C921353948C932B744274A3038E68BCCD1654
You can learn about this way of communication and download it here: hxxps://qtox.github.io/
Send us a friend request in the app and wait the support become online.
If you have not received an answer within 12 hours, use Bitmessage and write to our address: BM-NBurNHVRvKzmESPve8ZQz73m7AgyQyHV
You can learn about this way of communication and download it here: hxxps://wiki.bitmessage.org/
and here: hxxps://github.com/Bitmessage/PyBitmessage/releases/.5.
Q: How will the decryption process proceed after payment?
A: After payment we will send to you our scanner-decoder program and detailed instructions for use.
With this program you will be able to decrypt all your encrypted files.
After full decryption, we will point out your security problems and help you fix them..6.
Q: If I don’t want to pay bad people like you?
A: If you will not cooperate with our service – for us, it's does not matter. But you will lose your time and data, cause
only we have the private key. In practice – time is much more valuable than money.:::BEWARE:::
DON'T try to change encrypted files by yourself!
If you will try to use any third party software for restoring your data or antivirus solutions – please make a backup for all encrypted files!
Any changes in encrypted files may entail damage of the private key and, as result, the loss all data.Key Identifier:
–Number of files that were processed is: –
PC Hardware ID:
–
The note is full of grammar mistakes, which indicates that English is not the first language of these cybercriminals. Like many other ransomware developers, they ask for payment in cryptocurrencies[2] because it is anonymous. Unfortunately, the amount is not specified in the message, so it could be a matter of negotiations.
Threat actors also use scare tactics[3] to make victims contact them as soon as possible. We should stress that we do not recommend contacting the perpetrators. Many ransomware attack victims say that they never heard back after they sent the money to the criminals.
Since cryptocurrency transactions are irreversible, you should really think about if you are willing to take a risk of being scammed. Phmqdw ransomware creators say that only they have the decryption key, and that is true, so the only way to get your files back is to do what they ask. But you might be left without your files and your hard-earned money. In this guide, we will also cover a third-party recovery option that works for some people, so you should try that first.
Ransomware removal with anti-malware tools
If the machine is not located at your workplace but in your home, plugging out the ethernet cable is enough to disconnect from the network. You have to do this if other devices use the same network because they can be infected too.
After that, you have to remove the malicious files that are performing the tasks in the background. If you try to recover your data first, it can result in permanent loss. Also, the files can keep getting encrypted again and again until you eliminate the cause. It would be best if you did not try removing it yourself unless you have IT knowledge. Using anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system will give you the best chance of removal being complete. This security software should find all the related files and entries and remove them automatically for you.
If you cannot open security software, the code might be preventing the program from being able to function. Proceed with accessing Safe Mode, where you will be able to deploy the antivirus safely:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
File recovery using third-party software
Third-party programs cannot always decrypt the files, but you should at least try it. Before proceeding, you have to copy the corrupted files and place them in a USB flash drive or another storage. And remember – only do this if you have already removed Phmqdw ransomware.
It is devastating to know, but if you do not have backups, this might be your only chance at recovery because only hackers hold the decryption key, which can unlock your files.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Phmqdw ransomware Phmqdw ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
The operating system can be damaged after an attack
Performance, stability, and usability issues, to the point where a full Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files,[4] etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors,[5] freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Additional instructions are provided for corporate environments on isolating the infected machine and stopping the malicious program from affecting the entire network at the bottom of this post. You will also find information on where you can report your attack. Doing it will give you a better chance of having your perpetrators caught.
Getting rid of Phmqdw virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ What is encryption? Data encryption defined. Ibm. Security Blog.
- ^ Kate Ashford, John Schmidt. What Is Cryptocurrency?. Forbes. Investment Blog.
- ^ Ron Schlecht Jr.. DON’T FALL VICTIM TO CYBERSECURITY SCARE TACTICS. Btbsecurity. Proffesional IT Advice.
- ^ Dynamic-link library. Wikipedia, the free encyclopedia.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. Howtogeek. Technology Magazine.





















