Piiq ransomware (Recovery Instructions Included) - virus
Piiq virus Removal Guide
What is Piiq ransomware?
Piiq virus is a threat that aims to make a profit, so paying shouldn't be considered a solution
Piiq ransomware is the 307th version on the list of the dangerous cryptocurrency extortion-based threats. This is the particular file-encrypting virus that makes various changes on the computer once the system gets infected. The infiltration, in most cases, cannot be noticed because the virus spreads using various silent and stealthy methods.[1]
Users may download pirated software or cracks for licensed applications, games, cheatcodes for them. This is how the virus payload gets distributed around, so once such a file is opened on the machine, the activation is done. The encryption process starts right away alongside other functions that the cryptomalware has. Those include alterations in system folders and preferences.
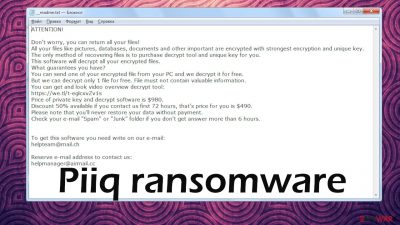
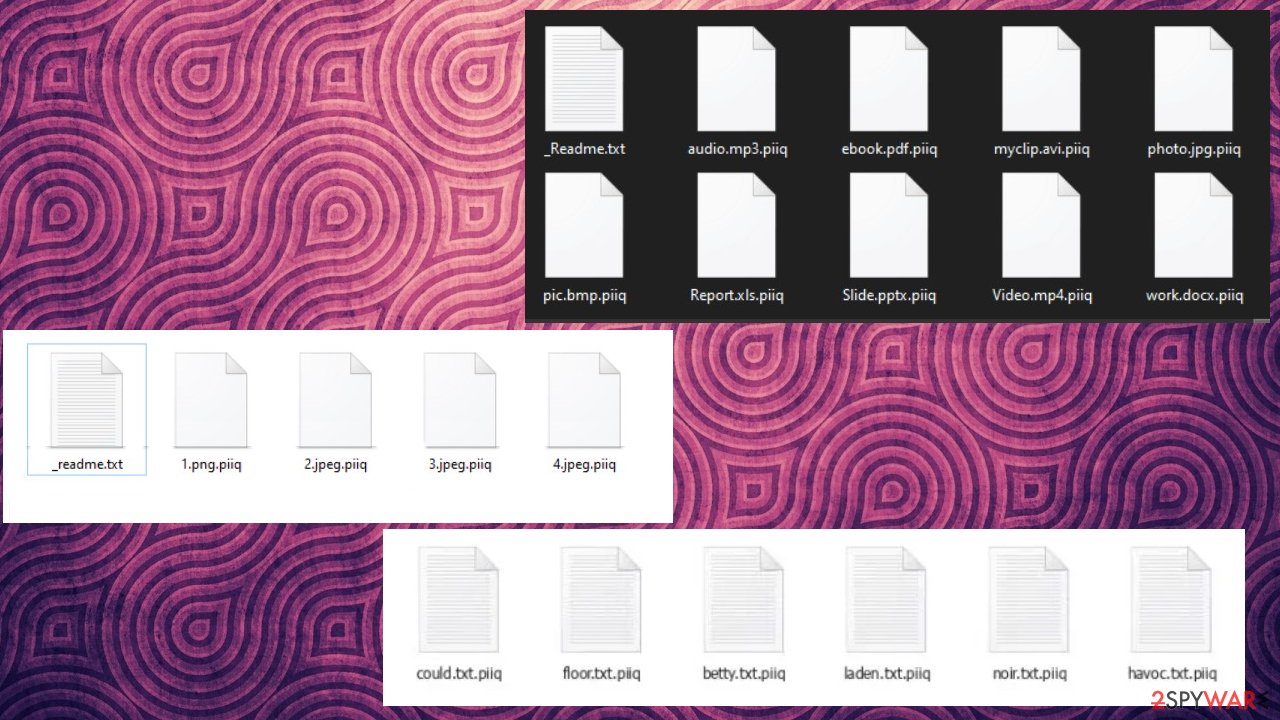
Once the encryption procedure is done, affected files get marked using .piiq appendix, hence the name of this virus. After that, the ransom note _readme.txt is delivered to the desktop and placed in other folders where the encoded data is. This message is an informational note from criminals who ask for payment while promising the recovery of files. Unfortunately, you cannot be sure that files get restored even after paying nearly 1000$ for the alleged software or decryption key.
Piiq virus can be exceptionally dangerous if you do not react as soon as possible. The demand for $980 or $490 in Bitcoin with the discount can look manageable when your files are valuable. However, you should never consider the payment as the best option for this infection and data recovery. Djvu family that this threat comes from is not known for the decryption options. The opposite. This threat is known for years now, and the main issue is that new versions come one after the other, often two a week. The latest threats: Ddsg virus and Sspq ransomware.
Do not fall for the misleading message that is the ransom note in that text file. Even though there are various mentions about possible decryption and the discount, trusting criminals is not the option.
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-9CYW99VhUR
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
helpteam@mail.chReserve e-mail address to contact us:
helpmanager@airmail.ccYour personal ID:
Even contacting people behind this threat can result in additional virus infiltration because these criminals aim for profit, that do not care about your valuables or feelings. Stay away from any interaction with the threat, its files, and the actors behind the infection. The first thing you need to do is to clear the machine.
File encryption and ransomware infection are two independent processes, but cryptocurrency extortion happens when there are files locked away, so threat actors have the option for blackmailing. However, it is important to understand that Piiq file malware performs various changes within a Windows operating system, fundamentally changing the way it works.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as a USB flash drive or SSD, and then disconnect them from your computer. Encrypted data does not hold any malicious code, so it is safe to transfer to other devices.
| name | Piiq ransomware |
|---|---|
| Type | File-locker, crypto virus |
| Family | Djvu ransomware/ STOP |
| Infection symptoms | Many non-system files like images, documents, video, audio files get renamed and rendered inaccessible; ransom demanding message appears on the desktop and in some affected folders as a text file; can't run security-related programs |
| Appended file extension | .piiq |
| Ransom note | _readme.txt – contains all the instructions for the payment and alleged recovery |
| Distribution | This family is known for spreading via pirated software platforms, game cheats, other pieces carrying the payload of the threat silently |
| Data recovery | Only possible with data backups, software that could restore affected files. The method is described in detail below. Decryption is limited to particular versions but possible |
| Elimination | Remove the cryptovirus by scanning your infected PC with reliable security software and anti-malware tools can remove the threat completely |
| System health | Malware additionally alters settings, so run system diagnostics with the FortectIntego repair software |
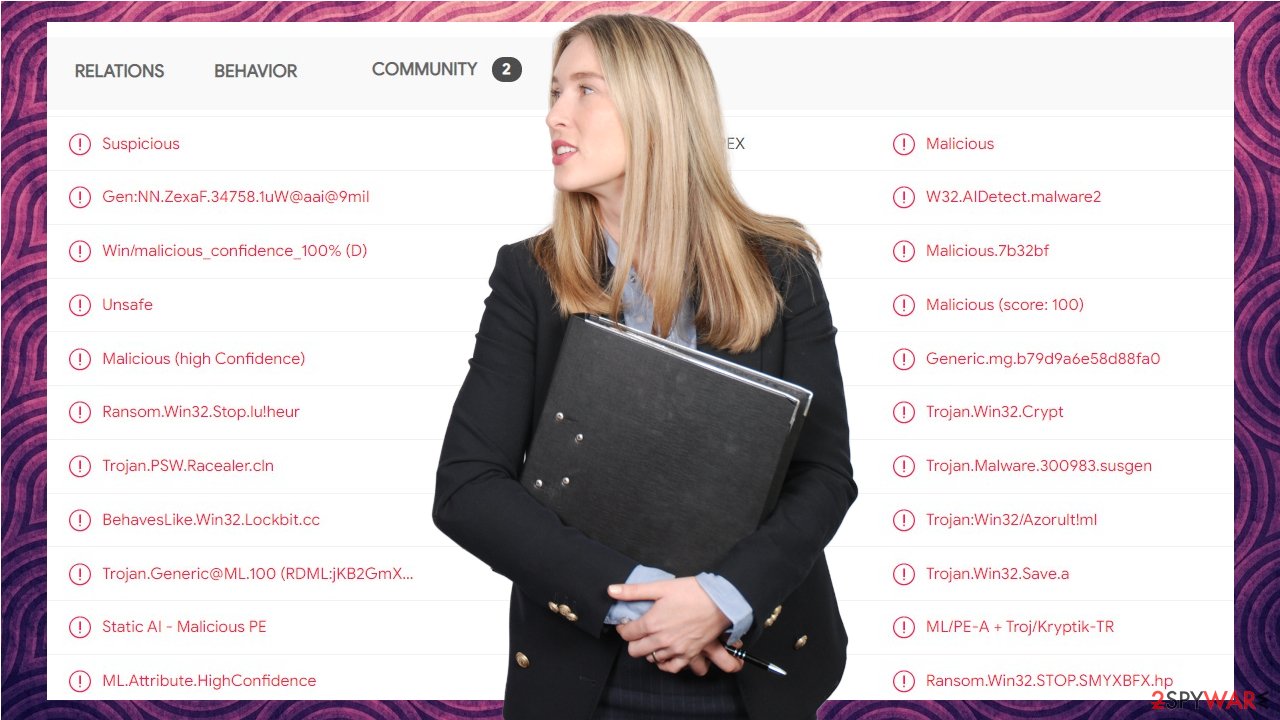
Even though previous versions in the same family had the decryption option, these newest variants are created with the impossible decryption opportunity. It is because of the offline ID vs. online ID when encoding data. Offline keys allow the recovery of files for all of the victims of this strain. At the same time, online keys are formed for each unique version of the particular strain. Unfortunately, the Piiq file virus is the more advanced version and cannot be easily decrypted.
The instructions below include the possible decryption option for versions when offline ids get used. The guide might initially seem overwhelming and complicated, but it is not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
Possible .piiq file decryption when offline keys get used in the encoding process
If you have infected your computer with one of the Djvu/STOP ransomware variants, you should try using Emsisoft decryptor. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.[2]
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. That can also happen when researchers obtain such keys from Piiq virus creators, but it is less likely that it can happen soon after the spreading of the particular version.
If you check your files and the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.
![Piiq ransomware Piiq ransomware]()
- After pressing the Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe, should show up – click it.
![Piiq ransomware Piiq ransomware]()
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Piiq ransomware Piiq ransomware]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
![Piiq ransomware Piiq ransomware]()
- Press Decrypt.
![Piiq ransomware Piiq ransomware]()
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt a file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID; decryption is impossible” – you are unable to decrypt files with this tool.
Possible Piiq file virus removal options
Such infections like the Piiq ransomware virus are not only encrypting data found on the system but also alters data placed in system folders, so functions and activities needed for the proper performance get altered and controlled by the attackers. If you want to get rid of the threat, you need to rely on tools like SpyHunter 5Combo Cleaner first. These anti-malware programs can help clear infections, terminate the cryptovirus properly.
Once the system is virus-free, it is possible to go through any data recovery options. However, always double-check since any leftover files can trigger issues with secondary encryption of malicious processes. Tools like Malwarebytes can scan the system fully and detect infection pieces,[3] so the ransomware is no longer active. The second step would be system cleaning and recovery.
Do not skip through this section because when Piiq ransomware is active, your device can get damaged significantly. If that is not taken care of, your computer can be damaged and stop working properly. There are no other options for cleaning the system and preparing it for file recovery. If you put your restored files on the infected machine – the PC can get damaged.
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstallation is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
This is the program that can help with various viruses and damage that cyber infections typically cause. If you run FortectIntego and there are many results of altered and damaged pieces – follow suggestions and fix them thoroughly. If that is not done, you may run into some issues when trying to recover files that the Piiq virus affected by encrypting.
Alternate option when decryption is not helpful
Since the decryption is only possible for some of the versions and not all people can access the decryption key and restore their files fully, users search for any available options. One of them – data recovery software. It is important for those who do not back up their files at all. People do not prepare proper data backups prior to being attacked by ransomware, so they might often lose access to their files permanently.
However, it is not the only option. Remember that paying is not considered to be a solution, especially when Piiq is the version of a well-known threat actor creation. You can still restore at least some of the data that got altered during this infection. Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Piiq ransomware Piiq ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ The four most popular methods hackers use to spread ransomware. Itproportal. Insights and reports.
- ^ Online Or Offline, Ransomware Will Find You. Darkreading. IT and security news.
- ^ Detection rate. VirusTotal. Online malware scanner.















