Qensvlcbymk ransomware (Virus Removal Guide) - Free Instructions
Qensvlcbymk virus Removal Guide
What is Qensvlcbymk ransomware?
Qensvlcbymk ransomware – dangerous file locking malware that targets organizations
Qensvlcbymk ransomware is a variant of Snatch malware and was first identified by a security researcher GrujaRS on Twitter in the middle of May 2020.[1] While the version might vary slightly from other malware of such type, its main goal is to extort money from victims. While ransomware strains like Djvu mainly target regular consumers, Qensvlcbymk ransomware mostly focuses on corporations and businesses for larger ransom sums.
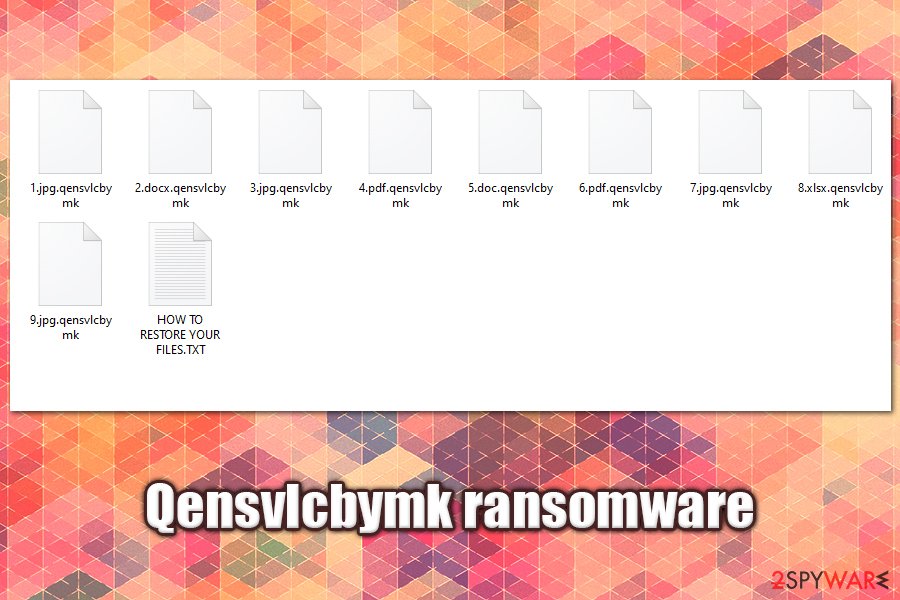
Once inside the system, the malware performs various checks and system changes before scanning for data to encrypt on local and networked drives (including NAS devices often used in corporations for data backups). It will encrypt most of the files with AES cipher, appending .qensvlcbymk extensions to each. The virus will also drop a ransom-demanding message (HOW TO RESTORE YOUR FILES.TXT) that asks users to email the attackers at support911@cock.li or xilttbg@tutanota.com and pay the ransom in cryptocurrency for Qensvlcbymk ransomware decryption tool.
| Name | Qensvlcbymk ransomware |
| Type | File locking virus, cryptomalware |
| Family | The virus belongs to Snatch ransomware family |
| File extension | Each of the non-system and non-executable files are appended with .qensvlcbymk extension and can no longer be accessed |
| Ransom note | HOW TO RESTORE YOUR FILES.TXT is dropped into each folder where the locked data is located |
| Contact | Users are asked to email the attackers via support911@cock.li or xilttbg@tutanota.com for negotiations about size of the ransom and data recovery process |
| Distribution method | Malware is highly likely to spread via weakly protected RDP connections, as its attacks are targeted |
| Main targets | Small to medium size businesses and organizations |
| Data restore |
Unfortunately, there is no secure method to recover Qensvlcbymk ransomware encrypted files if no backups were prepared or were also encrypted. Alternative methods include:
|
| Malware removal | To eliminate the infection, the infected computer or NAS device should be disconnected from the network and only then malware elimination performed with the help of powerful security software |
| System fix | To fix system damage after ransomware infection, employ repair tools like FortectIntego |
Snatch is a relatively established ransomware strain in the illegal crypto-extortion business since its first release back in December 2018. While it is not the most active cryptoviruses around, it released around a dozen variants (e.g., Jupstb, Egmwv, and others), targets of which are corporate networks.
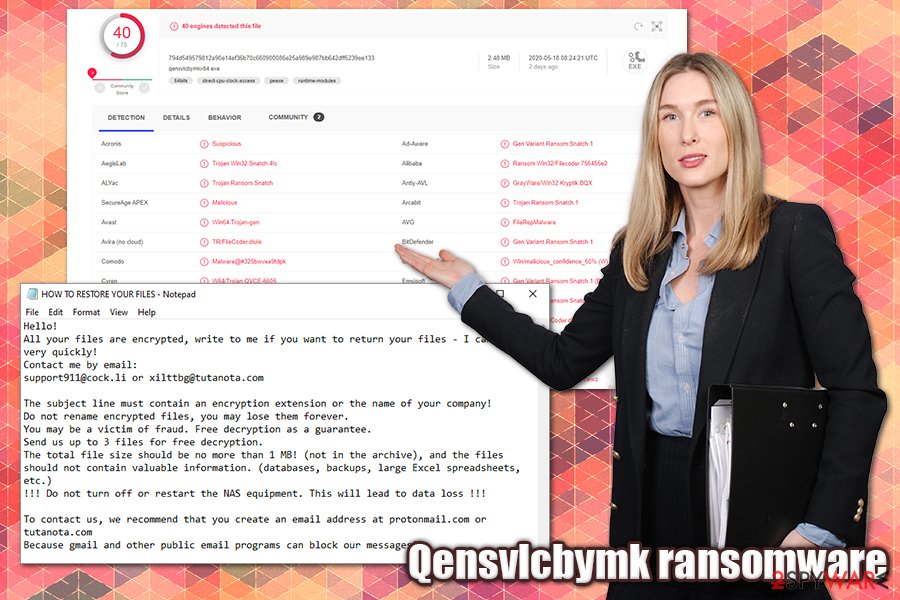
At the end of 2019, the malware has started rebooting Windows computers to avoid the detection of anti-malware software and performing data encryption without interruptions.[2] Due to this, victims might also struggle with Qensvlcbymk removal, although adequate security solutions like SpyHunter 5Combo Cleaner or Malwarebytes should be able to handle the infection. Additionally, the malware is detected under following names by security tools:[3]
- Win64:Trojan-gen
- Gen:Variant.Ransom.Snatch.1
- Ransom:Win64/Qensvl!MSR
- Ransom.Snatch.GO
- Trojan-Ransom.Win32.Gen.wwz
- Trojan.TR/FileCoder.diule
- W64/Trojan.QVCE-6605, etc.
Just as other crypto-malware of such kind, Qensvlcbymk ransomware mainly uses Remote Desktop connections to penetrate corporate networks. This happens when RDPs are exposed via the default port and are not protected with adequate measures, such as strong passwords.
Attackers typically infiltrate the networks to perform surveillance, remaining undetected for weeks before releasing Qensvlcbymk ransomware manually. Looking at the latest ransomware trends, they are highly likely to exfoliate sensitive information during this time, which they can later publish online if the victims declined to pay the ransom.[4]
Once malicious actors gain access to the network, they release the main executable such as qensvlcbymkx64.exe, which begins the infection routine and reboots Windows PC into Safe Mode. In this mode, most security solutions are non-functional, which would otherwise prevent Qensvlcbymk virus infection and file encryption.
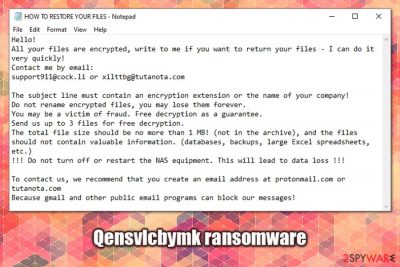
After data is locked, Qensvlcbymk ransomware boots in normal Windows mode and launches a ransom note titled as HOW TO RESTORE YOUR FILES.TXT, which reads:
Hello!
All your files are encrypted, write to me if you want to return your files – I can do it very quickly!
Contact me by email:
support911@cock.li or xilttbg@tutanota.comThe subject line must contain an encryption extension or the name of your company!
Do not rename encrypted files, you may lose them forever.
You may be a victim of fraud. Free decryption as a guarantee.
Send us up to 3 files for free decryption.
The total file size should be no more than 1 MB! (not in the archive), and the files should not contain valuable information. (databases, backups, large Excel spreadsheets, etc.)
!!! Do not turn off or restart the NAS equipment. This will lead to data loss !!!To contact us, we recommend that you create an email address at protonmail.com or tutanota.com
Because gmail and other public email programs can block our messages!
As evident, the attackers are asking for victims to include the name of the file extension (.qensvlcbymk, although this can vary) and the company name that the ransomware has infected for identification purposes. Snatch ransomware authors were previously seen asking for ransoms reaching 1-5 Bitcoin, although this can greatly vary depending on the size of the organization and the number of encrypted workstations/servers.
Crooks behind Qensvlcbymk ransomware are also offering free decryption of one file that is no larger than 1 MB, and should not contain any important information. This is a typical trick to make victims believe that they can trust the attackers and that they are guaranteed a Qensvlcbymk ransomware decryption tool as soon as the ransom is paid. However, there were several instances where attackers failed to fulfill their promise, or the tool simply did not work.
Before performing Qensvlcbymk ransomware removal, users should make a copy of all the important files and the registry database, as some relevant information might be stored in there. Also, the process would eliminate additional modules that the malware might install, such as publicly available test penetration tools and data-stealing components.
Once backups are prepared, the infected machine should be segregated from the infected network and then cleaned with anti-malware solutions. To restore normal functions of the Windows machine, we recommend using FortectIntego.
Companies should ensure a secure usage of Remote Desktop connections
Remote Desktop connections, otherwise known as RDPs, are very useful tools that allow remote access to a computer. Another reason why is RDP is so widely used is because it is built into Windows OS and can be used for free by, e.g., system administrators to reach the workstation of interest.
However, because the RDP is so popular and widely used (and also commonly poorly protected), it became one of the main attack vectors for malicious actors for surveillance and malware injection purposes. The attack is also often combined with brute-forcing – another technique that abuses weak passwords used to protect RDP connections.
The attackers typically spend weeks on the infected networks, all while gathering the necessary information and moving laterally via the network and accessing administrator accounts. After the malware is launched, the whole network should be considered compromised.
To protect your company from RDP attacks, practice the following precautionary measures:
- Never use a default TCP/UDP port 3389;
- Use a strong password fro connection and never reuse it for anything else;
- Enable Network Level Authentication (NLA) via System Properties;
- Employ a reputable VPN service for the computers that use RDP services;
- Limit the number of employees that can access the service;
- Disconnect from RDP as soon as it is not used for anything;
- Protect your network with endpoint security solutions.
Eliminate Qensvlcbymk ransomware correctly
Since the Qensvlcbymk virus is a part of Snatch ransomware, it may run a component called SuperBackupMan in Safe Mode (it is typically established during the infection routine). Thanks to this feature, rebooting the system into Safe Mode with not stop the malware from operating, although performing a full system scan with most up-to-date security software (we recommend using SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security tool) should help you perform Qensvlcbymk ransomware removal without problems.
However, before you remove Qensvlcbymk ransomware from the system, there are several steps that need to follow. First of all, all the affected machines should be disconnected from the infected network and a full backup of the hard drive performed (if important files are present). After that, you can use security software to terminate the infection, along with all the malicious files and modules that were inserted by the attackers.
The best way to recover encrypted files is by restoring them from backups. If you do not have backups ready, there are very few chances currently to recover data for free. Paying cybercriminals remains an option, although it is very risky and discouraged by most security researchers. Unfortunately, that might be the only choice in some cases.
Getting rid of Qensvlcbymk virus. Follow these steps
Manual removal using Safe Mode
If you need to access Safe Mode with Networking, perform the following steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Qensvlcbymk using System Restore
System Restore might also serve as an alternative method to eliminate the infection:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Qensvlcbymk. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Qensvlcbymk from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Qensvlcbymk, you can use several methods to restore them:
Try out Data Recovery Pro
The less you use the machine infected with Qensvlcbymk, the bigger chances you have for tools like Data Recovery Pro to work.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Qensvlcbymk ransomware;
- Restore them.
Make use of Windows Previous Versions feature
This method will only work if System Restore was enabled prior to the attack
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might save your files
If malware failed to delete Shadow Volume Copies, ShadowExplorer should be able to restore all your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Qensvlcbymk and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ GrujaRS. #Snatch #Ransomware extension .qensvlcbymk. Twitter. Social network.
- ^ Catalin Cimpanu. Snatch ransomware reboots PCs in Windows Safe Mode to bypass antivirus apps. ZDNet. Technology News, Analysis, Comments.
- ^ 794d549579812a90e14ef36b70c660900086e25a989e987bb642dff5239ee133. Virus Total. File and URL analysis.
- ^ Lien Van Herpe. Ransomware 2020: pay up or find your data online. Orange Cyberdefense. Cybersecurity solutions for companies.





















