Routes adware (Free Instructions)
Routes adware Removal Guide
What is Routes adware?
Routes adware is a malicious program that spreads with software cracks

Routes adware can be installed accidentally or purposely, although its distribution methods are dubious, to say the least – just like its operation or purpose. The app can be found on various illegal torrent and software crack websites, where most users venture to download otherwise paid programs and video games for free.
Once installed, adware executes many files and starts running its own process known as “Routes tech Copyright© All rights reserved.” The main goal of malware is to ensure that users are exposed to a large flow of ads, including pop-ups, deals, offers, banners, in-text links, and similar intrusive advertisements.
Not only does Routes adware interfere with normal web browsing activities, but it might also cause one to click on malicious links. Consequently, people might end up on phishing, spoofing,[1] malware-laden, and similar websites where they could get infected with other parasites, disclose their personal information to cybercriminals, or spend money on useless services/subscriptions. It is also not recommended to enter any personal information while using the browser, as it might potentially be automatically stolen.
After the installation is complete, the virus also automatically installs a fake Google Translate extension, which applies the “Managed by your organization” setting to the browser. This makes the removal of the extension more complicated, although there are plenty of ways to be successful regardless. We provide all the elimination instructions in the below sections of the article.
| Name | Routes virus |
|---|---|
| Type | Adware |
| Distribution | Software cracks or bundlers, deceptive websites, fake ads |
| Symptoms | Redirects to suspicious websites that hold plenty of commercial or scam content; shows fake messages offer to download malicious software; malicious processes run in the background; installs a fake Google Translate extension |
| risks | Redirects to malicious websites can result in intrusive notifications, personal information disclosure to cybercriminals, financial losses, installation of other potentially unwanted programs/malware |
| removal | For the best results, you should check for unwanted browser extensions and programs that could be installed on the system level. Finally, you should scan your device with SpyHunter 5Combo Cleaner security software to ensure no malware is present |
| Other tips | Cleaning web browsers is one of the secondary things you should do after adware/malware removal to secure your privacy. You can use FortectIntego to do it quickly |
Effective adware and malware avoidance
Malware is always distributed in ways that would trick people into installing it in the first place. There are plenty of methods used by cybercriminals – software vulnerabilities, spam email attachments, fake updates, and many more.
However, software cracks and similar illegal installers remain the to-go method to spread the most common malware, such as adware, ransomware, and Trojans. One of the most widespread ransomware strains known as Djvu and its recent versions Avyu and Cuag is spread almost exclusively through software cracks.
This technique works so well because users themselves venture to high-risk websites to obtain free applications. Thus, many people are willing to risk it despite knowing about potential dangers. However, not only is it illegal to download cracked apps, but it can easily result in security issues.
Software cracks are always executable files, which are automatically flagged as malicious by most security vendors because of the initial program's design (it is programmed to interfere with the code of another program, hence most anti-malware would flag it as malicious by default. As a result, there is no effective way to check whether such a tool is actually malicious and would result in malware infiltration or not.
This is also why so many users tend to disable their security applications to install these software cracks. Keep in mind that security warnings should never be ignored, as they can save from a lot of issues arising from malware infections.
Therefore, you should ensure that your system is protected by a powerful anti-malware tool, and its warnings are never ignored. Likewise, we recommend staying away from pirated program websites, as these are one of the most common methods for Routes adware and similar malicious software infiltration.
First step: remove the malicious Routes program
It is evident that it is not recommended to keep potentially unwanted or malicious programs installed on the system. Therefore, below you will find all the information needed to eliminate the main program from the system and then take care of the browser extension thoroughly.
Uninstall from the system
First thing's first – you should get rid of the main application that is installed on the system level. This step may or may not be possible due to possible persistence techniques used by malware, but we recommend trying it anyways.
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Scan with anti-malware
Considering the deceptive distribution techniques of the virus, the fact that additional infections might be present on your system cant be excluded. Once a malicious executable is launched, it can initiate downloads of additional payloads, which could start recording keystrokes, harvesting sensitive information, corrupt system files, and much more.
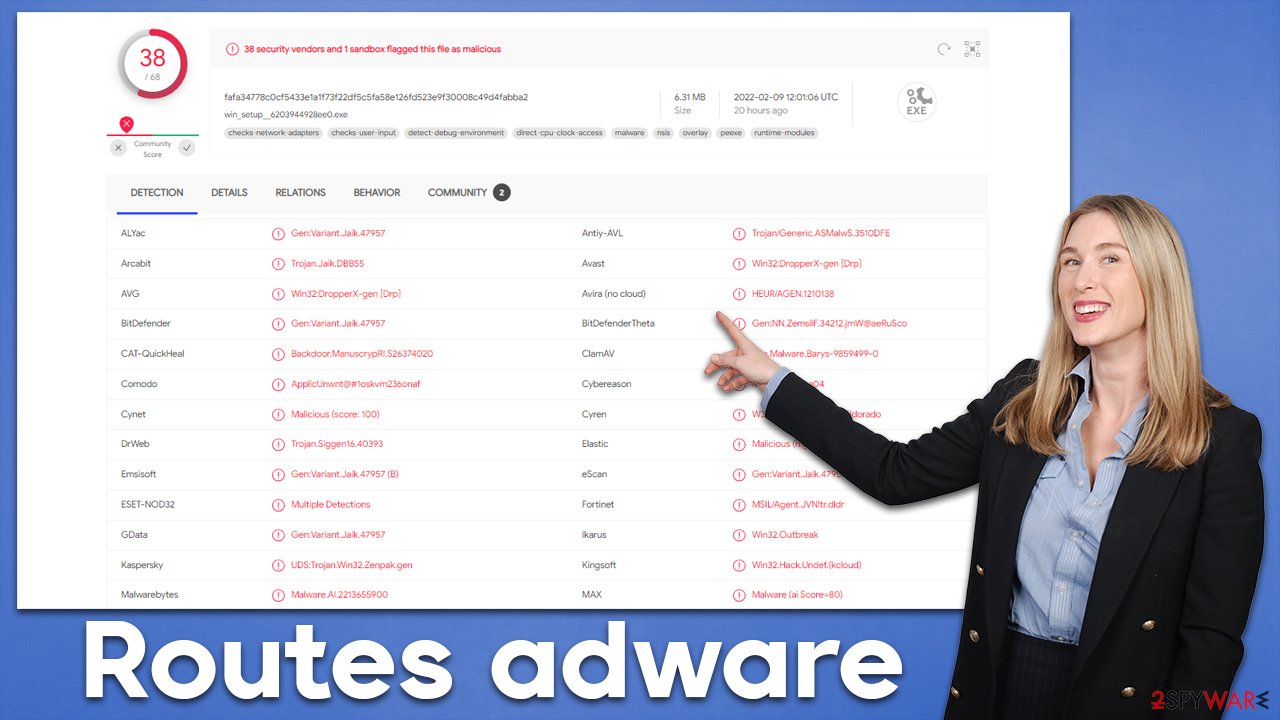
The Routes adware executable is detected by plenty of security applications, thus if you would not disable the detection, you can easily prevent its infiltration in the first place. Here are a few examples of how the installer is detected:[2]
- Trojan.Siggen16.40393
- BehavesLike.Win32.Generic.vc
- Win32:DropperX-gen [Drp]
- Trojan:MSIL/RedLineStealer.RPN!MTB
- Malware.AI.2213655900.
Evidently, this adware is commonly categorized as malware, and rightfully so. If you scan your system with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable security software, it can remove the Routes adware along with other underlying infections that could be running in the background.
Deal with the fake Google Translate extension
As mentioned before, Routes adware also installs a fake Google Translate extension on the browser. For this reason, you should make sure that not only the main program is removed from the system but also the extension as well. Otherwise, the unwanted ads and other malicious activities may continue.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
The next step is particularly important, as adware is commonly set up to track user information with the help of various trackers, such as cookies or web beacons.[3] These are stored locally and can remain present on the system for years (continuing their purpose) unless they are removed either by cleaning the web browser or resetting it.
Cleaning web browser caches is an overall recommended process that should be undertaken every so often, as it reduces the possibility of encountering various browser errors and suffering from a very dangerous session hijacking attack. You can refer to the instructions below or employ the FortectIntego repair tool, which can be used to also fix the damage done to the system due to the infection.
Google Chrome
- Click the Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
As we already mentioned, the “Managed by your organization” setting might make the removal of the fake Google Translate extension rather difficult. If you were unable to perform the aforementioned steps, we recommend resetting the browser altogether. You shouldn't lose any of your bookmarks and other details as long as you remember your Google account details that you can use to log in after.
Google Chrome
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.
![Reset Chrome 2 Reset Chrome 2]()
MS Edge
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.
![Reset Chromium Edge Reset Chromium Edge]()
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What is domain spoofing? | Website and email spoofing. Cloudflare. Application and data security.
- ^ win_setup__6203944928ee0.exe. Virus Total. File and URL analysis.
- ^ Web beacon. Wikipedia. The free encyclopedia.








