Scarabey ransomware (Free Instructions) - Decryption Steps Included
Scarabey virus Removal Guide
What is Scarabey ransomware?
Scarabey – ransomware targeting Russian computer users
Scarabey ransomware is yet another variant of the notorious Scarab virus which is currently targeting Russian computer users. This file-encrypting malware is written in Delphi and is used for encrypting files on victim's computer to make them inaccessible. Once it encodes the target files, Scarabey creates a .txt file named as Инструкция по расшифровке (Decryption instructions in English) and drops it on computer's desktop.
In contrast to its predecessor, Scarabey virus does not spread via Necurs botnet.[1] To drop the code and launch ransomware hackers have been misusing Microsoft's Remove Desktop Protocol (RDP). Besides, in some cases the virus can infect the system with the help of spam and ask you to use Support56@cock.lt to contact its developers.
Once the malicious code is executed onto the target computer, the virus scans the whole system and encrypts the most popular file formats, such as doc, .docb, .docm, .docx, .java, .jpeg, .jpg, .mp3, .mp4, .mpa, .pdf, .php, .rar, .raw, .txt, .vcf, .vob, .wav, .wma, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip, etc. Just like the previous version, it adds .scarab file extension to each of them and drops multiple files deep into the Windows OS to prevent easy removal of the malware.
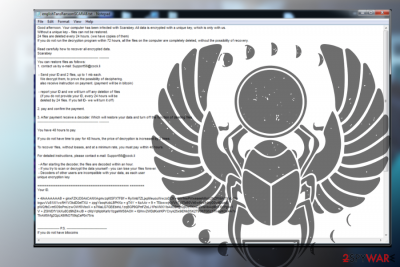
The ransom note of the Scarabey explains what procedures were initiated on victim's computer and what actions should him/her do to regain the access to locked files. The ransom note reads the following:
Good afternoon. Your computer has been infected with Scarabey. All data is encrypted with a unique key, which is available only to us.
Without the unique key – files can not be restored.
24 files are deleted every 24 hours. (we have copies of them)
If you do not run the decryption program within 72 hours, all the files on the computer are completely deleted, without the possibility of recovery.
Read carefully how to recover all encrypted data.
The virus uses strong cryptography, which, at the moment of writing, can be eliminated only by entering a unique decryption code which is help by hackers. In addition to locked files, the owner of the attacked PC can notice various system's changes and malfunctions, which is why Scarabey removal is the initial step we recommend taking. For that, use FortectIntego or similar anti-virus.
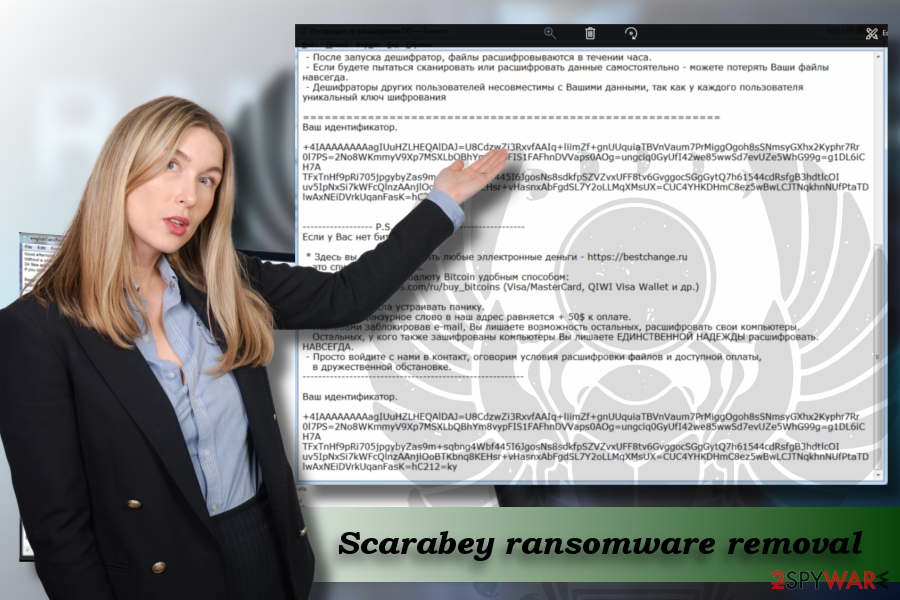
The only way to get the unique code is to contact the developer of the ransomware by email Support56@cock.lt and indicate the ID number to get further instructions.
However, we do NOT recommend that as this is a straight way into losing your money and files. No matter that crooks are promising to show the victim that they are capable of decrypting files locked by their ransomware, you should never follow their commands. Make sure you remove Scarabey from the system instead of sending two currently locked files (up to 1 MB) along with your ID. Then, proceed to our files' recovery section.
Do not pay the ransom, security experts warn
Although it's not yet clear how much money ransomware developers demand, based on the previous ransomware practice,[2] we can guess that the amount of money varies from 500 to 2500 USD.
The deadline for the payment ends within 72 hours and, furthermore, every 24 hours of hesitation will end up with a permanent loss of 24 personal files. Nevertheless, security experts recommend people to remove the virus using a professional anti-virus tool before it injects its code deep into a target system.
Remove Desktop Protocol (RDP) can be used for ransomware distribution
As we have already pointed out, this ransomware can be distributed via Remove Desktop Protocol (RDP).[3] With its help crooks may get access to people's PCs remotely and manually inject the malicious code. You should also be careful with spam emails, especially those from unknown senders and containing an attachment. Please, double check it before downloading it to your computer.
Finally, do not fall for clicking low-quality eye-catching ads and be careful with programs from third party sources, such as torrents or P2P networks. Such apps can also be bundled with malicious programs, including file-encryption virus, browser hijackers, etc.
A complete guide on how to uninstall Scarabey virus
If your personal files got locked because of the Scarabey ransomware, you have to decide immediately whether you are going to pay the ransom or not. Although you are locked from accessing your personal files, we would like to discourage you from hooking on the contact with cybercriminals.[4]
First of all, there's no guarantee that hackers will recover all your encrypted files. Second of all, by paying the ransom instead of eliminating ransomware from the system, people encourage cyber crooks for further attacks.
Once you remove Scarabey ransomware, you can try to decrypt files using a professional software decryption tool. However, we cannot guarantee that it will be capable of cracking a robust encryption code. We must add that Scarabey removal will damage Windows Shadow Volume Copies as well. People often use these copies for decrypting personal files, but this time hackers forestalled the possibility to use these copies by removing them.
Thus, before trying to recover encrypted files, get rid of Scarabey virus completely. For this purpose, you can use FortectIntego or SpyHunter 5Combo Cleaner.
Getting rid of Scarabey virus. Follow these steps
Manual removal using Safe Mode
To unblock your antivirus, which is blocked by ransomware, the guide on how to access Safe Mode with Networking will help you:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Scarabey using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Scarabey. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Scarabey from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Scarabey, you can use several methods to restore them:
Use Data Recovery Pro to get your files back
Data Recovery Pro is a professional application that was initially created for recovering data lost after unexpected system crash or accidental removal. Luckily, this tool is capable of recovering most of the files stored on your hard drive. To recover your files with Data Recovery Pro, please follow these steps:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Scarabey ransomware;
- Restore them.
You can recover files encrypted by Scarabey virus using the Windows Previous Versions feature
If Scarabey ransomware infected your PC and locked most of the files stored on it, you can try to decrypt the most important files using Windows Previous Versions feature. However, this method is applicable only if System Restore function was enabled before the virus hit your PC.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Scarabey decrypter is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Scarabey and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Julie Splinters. Necurs pushes spam emails infected with Scarab ransomware. 2-Spyware. The highest-quality information about malware and general security.
- ^ Jim Martin. Ransomware: to pay or not to pay to get your files back. Tech Advisor. the world’s leading technology media, data and marketing services company.
- ^ Mark Stockley. Ransomware-spreading hackers sneak in through RDP. Naked Security by Sophos.
- ^ Pierluigi Paganini. ybercriminals Stealing From Cybercriminals Ransomware Victims Left Stranded. Security Affairs. News, tips, tricks, and hacks.





















