Sekhmet ransomware (Removal Instructions) - Free Guide
Sekhmet virus Removal Guide
What is Sekhmet ransomware?
Sekhmet ransomware – crypto-malware that targets organizations and threatens to publish confidential information online
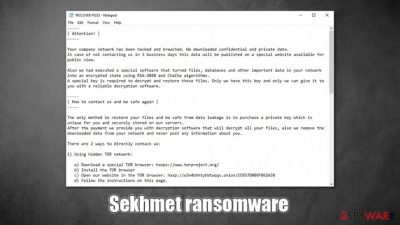
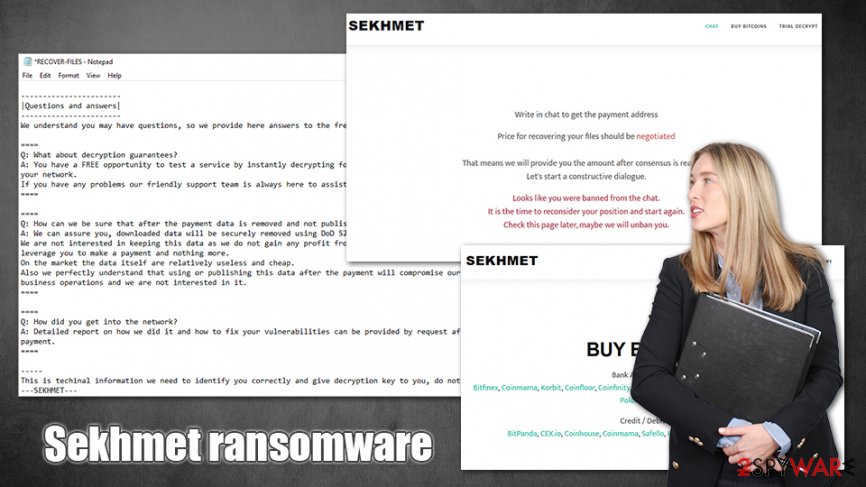
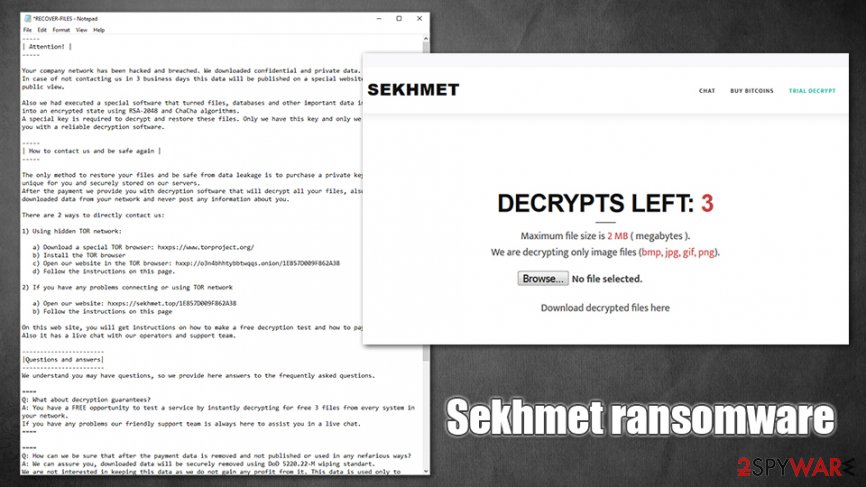
Sekhmet ransomware is a new crypto-locking virus strain that was first spotted by cybersecurity experts in late March 2020. Just like similar malware of such type, it uses a strong encryption algorithm (this time, a combination of RSA and ChaCha) to lock pictures, music, videos, documents, databases, and other files on local and networked drives for blackmail purposes. Each of the locked files is appended with a random extension (e.g., .WNgh, .DtiV) and can no longer be accessed, unless a ransom in Bitcoin from Sekhmet virus authors.The tactic has been developed by Maze ransomware authors and is now being adopted across other strains.
Threat actors behind the Sekhmet ransomware strain joined the terrifying trend among cybercriminals – they harvest sensitive information during the infection process and then threaten to publish it on a specific portal online, which would be accessible for everybody. Allegedly, victims only have three business days before that happens. To recover the Sekhmet ransomware decryption tool, users have to either visit a TOR site or visit a skhmet.top website. All this information is conveniently compiled into ransom RECOVER-FILES.txt, which is dropped on the infected machines' desktops.
| Name | Sekhmet ransomware |
| Type | File locking virus, crypto-malware |
| Related files | f55.dll, sekhmet.dll.exe, regsvr32.exe |
| Encryption method | All non-system files are encrypted with the help of RSA-2048 + ChaCha |
| File appendix | Unlike most ransomware, Sekhmet appends a random extension to each of the files on the same device. Example of two different files on the same system: picture1.jpg.WNgh and picture2.jpg.DtiV |
| Ransom note | RECOVER-FILES.txt |
| Contact | Malicious actors indicate two methods of contact: either by downloading a TOR client and visiting a provided link or by visiting sekhmet.top website |
| Threat | Hackers claim that they harvested sensitive information from the infected computers and will publish it if the ransom is not paid within three days |
| Data recovery | Without secure backups, retrieving data is almost impossible. Alternative ways for file recovery include using third-party software or trying to use built-in Windows backups. Paying cybercriminals might be the only choice in some cases (although it is not recommended) |
| Malware removal | To get rid of malware, users need to perform a network-wide scan with reputable anti-malware software |
| System fix | Malware can often damage Windows system files, resulting in crashes and other issues. To fix virus damage, employ repair tools like FortectIntego |
Since Sekhmet ransomware targets organizations mainly, it is clear that attack vectors do not include random targets. To perform a targeted attack, malware developers often choose to use spear-phishing[1] emails or insecure Remote Desktop connections. The latter can be reached simply by scanning the internet for all RDP connections that use a default TCP/UDP port 3389.
Due to the targeted nature of the attacks, threat actors behind Sekhmet virus could be able to disable implemented defenses, such as employed anti-malware tools. Nevertheless, most up-to-date security solutions might be the tools one needs to detect unauthorized access. There many AVs that detect malware under the following names:[2]
- Trojan.GenericKD.42872102
- Win32:Malware-gen
- Ransom.Win32.SEKHMET.A
- Win32.Trojan.Cryptor.Pgwr
- Trojan-Ransom.Win32.Cryptor.ddu
- Trojan.GenericKD.42872102 (B), etc.
Sekhmet ransomware removal can also be achieved with the help of anti-malware tools, although it could be possible that the infection neutralized itself after performing file encryption. Many ransomware is programmed to do so, although it is best to check the machine(s) with security software regardless. If you remove Sekhmet ransomware before backing up the encrypted data, it may get compromised for good, however.
Sekhmet ransomware does not immediately begin the file encryption process, as many system modifications need to be performed before that. For example, the Windows registry is modified, remote server connections established, malicious files dropped, Shadow Volume Copies, and multiple other files deleted, etc. For a startup, regsvr32.exe process is used – malware boots each time the Windows is started. These Sekhmet ransomware changes can sometimes damage the system, although it can be later reverted with tools like FortectIntego.
With the system preparations complete, the Sekhmet virus begins to look for files on local and networked drives. It targets the most commonly used types, such as .pdf, .jpg, .zip, .mkv, .doc, and many others. With the help of sophisticated encryption, the malware locks all data and appends a different extension to each file, making them unusable.
After that, a lengthy ransom note is dropped, which explains that Sekhmet ransomware encrypted all files and, allegedly, the only way to recover data is by paying cybercriminals. Here's an extract from the note:
| Attention! |
—–Your company network has been hacked and breached. We downloaded confidential and private data.
In case of not contacting us in 3 business days this data will be published on a special website available for public view.Also we had executed a special software that turned files, databases and other important data in your network into an encrypted state using RSA-2048 and ChaCha algorithms.
A special key is required to decrypt and restore these files. Only we have this key and only we can give it to you with a reliable decryption software.—–
| How to contact us and be safe again |
—–The only method to restore your files and be safe from data leakage is to purchase a private key which is unique for you and securely stored on our servers.
After the payment we provide you with decryption software that will decrypt all your files, also we remove the downloaded data from your network and never post any information about you.There are 2 ways to directly contact us:
1) Using hidden TOR network:
a) Download a special TOR browser: hxxps://www.torproject.org/
b) Install the TOR browser
c) Open our website in the TOR browser: hxxp://o3n4bhhtybbtwqqs.onion/1E857D009F862A38
d) Follow the instructions on this page.2) If you have any problems connecting or using TOR network
a) Open our website: hxxps://sekhmet.top/1E857D009F862A38
b) Follow the instructions on this pageOn this web site, you will get instructions on how to make a free decryption test and how to pay.
Also it has a live chat with our operators and support team.
It is yet unknown who is behind Sekhmet ransomware strain, but it seems like these criminals are serious about what they do. Looking at ransom note and the way communication system is established, it becomes clear that these people are not new in ransomware scene, and they are aiming to infect organizations and businesses for increased ransom payments.
Keeping that in mind, sensitive information disclosure becomes even more devastating than the loss of files, in some cases. For a company to have its secrets revealed possibly to other malicious actors or competitors might prove detrimental, resulting in the company shut down. This is why Sekhmet ransomware might be so efficient in collecting ransom payments, as business owners do not want to lose their source of income.
Ransomware prevention measures
It is currently unknown that type of distribution methods ransomware developers are using, although, considering the nature of the ransom note, they most likely rely on targeted attacks. In most cases, these are executed via unprotected RDP connections or phishing emails. Nevertheless, it does not mean that cybercriminals cannot use other methods, including:
- web injects
- fake updates
- exploits
- pirated software installers
- etc.
Therefore, to ensure the safety of the company, staff training and dedicated IT teams are essential for cybersecurity. It is especially important to secure remote desktop connections with the help of such tools like VPN, as well as strong passwords and correct settings.
Additionally, email attachments should never be allowed to run macro function, i.e., “Allow content.” Typically, PDF or .doc files, boobytrapped with malicious macros, are employed to execute commands and begin the infection routine. Also, with the help of spoofing techniques,[3] hackers might make it look that the email is coming from within the company, so caution should be practiced at all times.
Finally, comprehensive anti-malware software, regular backups, system patching, and other safety measures should always be practiced.
Get rid of Sekhmet ransomware and try to recover your data
It is up to you to decide whether you want to pay for Sekhmet ransomware decryptor, although keep in mind that it is very risky – cybercriminals behind the strain might simply ignore victims as soon as Bitcoins are transferred. Therefore, security experts advise against paying criminals, although the fact that they could disclose sensitive company information publicly is a considerable threat.
If you decide not to pay, you have to ensure that Sekhmet ransomware removal is performed correctly. Since malware drops a multitude of files across the system and changes various Windows settings, it is best to be done with the help of anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes
In case you have struggled when trying to remove Sekhmet ransomware, you can access Safe Mode with Networking and perform a full scan from there. Only then you should attempt to recover your data, although do not forget to backup the encrypted files first. Run FortectIntego for file alterations and PC repair before you recover files.
Getting rid of Sekhmet virus. Follow these steps
Manual removal using Safe Mode
To access Safe Mode with Networking, perform the following actions:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Sekhmet using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Sekhmet. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Sekhmet from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Sekhmet, you can use several methods to restore them:
Data Recovery Pro might be useful when trying to retrieve encrypted files
Data Recovery Pro might be able to reach healthy copies of at least some files located in the hard disk.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Sekhmet ransomware;
- Restore them.
Make use of Windows Previous Versions feature
This method will only work if you had System Restore enabled.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can sometimes help
In case the Sekhmet file virus failed to delete Shadow Volume Copies, ShadowExplorer can help you to retrieve the encrypted data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Sekhmet and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Dan Swinhoe. What is spear phishing? Why targeted email attacks are so difficult to stop. CSO Online. Security news, features and analysis about prevention.
- ^ f55.dll. Virus Total. File and URL analysis.
- ^ Email spoofing. Wikipedia. The free encyclopedia.





















