Sorano Stealer virus (Free Guide) - Removal Instructions
Sorano Stealer virus Removal Guide
What is Sorano Stealer virus?
Sorano Stealer virus is the threat that can take data from the machine or make screenshots and send these details to the attacker remotely
Some relations with Russian hackers show that this can be the creation of a developer from Russia that makes a big effort to promote and distribute the threat in the wild with the help of such dark web sites and forums. The source code itself of this stealer is placed on the GitHub data, so anyone with more advanced skills can use this code, modify the functions, and spread it around for specific purposes.
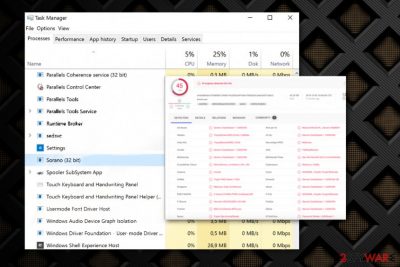
Unfortunately, Sorano Stealer utilizes a popular Russian messaging application to transfer data from the affected system to a remote server that is controlled by the attackers, so there can be many uses for the gathered information. It is not known what data this trojan is after, but there are many valuable details that malware can obtain from the computer directly and use other pieces of malware to get. Nevertheless, the virus runs in the background without displaying any symptoms or noticeable features, so the user of the affected machine is not aware of the infection until the suspicious process is noticed in Task Manager or the virus creates frustration due to speed and performance issues.
| Name | Sorano Stealer virus |
|---|---|
| Type | Information-stealer malware[2] |
| Symptoms | The virus is not displaying any symptoms besides the Sorano.exe file running in the background or other processes that cause high usage of CPU or speed and performance issues. Otherwise, the malware runs in the background without causing any symptoms and can be there unnoticed for a long time |
| Functions | Malware is set to steal data from the machine, gather information from social media platforms, messaging apps, exfiltrate data from sites and use keystroke loggers to steal passwords and logins, banking details |
| Danger | It can use the stolen information for blackmail, sell the information for third-party hackers and use it for money transfers or hacks of the machine itself |
| Distribution | Trojans and other more severe malware can land on the machine when the person opens a malicious file attachment from the email or visits hacked site, malicious domain. The infiltration happens silently and cannot be noticed by the user |
| Elimination | Sorano Stealer virus removal can be difficult when you are not seeing the threat and any symptoms, so you better get an anti-malware tool that runs on the system fully checking all the parts and can eliminate any traces of this or another intruder |
| Repair | For virus damage and system folder s affected by the malware, get FortectIntego or a similar system optimizer, PC repair tool that can indicate and possibly fix affected files or direct malware damage |
Sorano Stealer virus is the password-stealing virus that can gather banking details, credentials, and other information valuable for the hacker and other third-party attackers. This is the malware that can be purchased, and cybercriminals may buy the full-on trojan to spread for their own purpose of information gathering.
There is a version of this Sorano Stealer that can be obtained without paying but the publicly available version may not be up to date, so criminals still rely on paying the developers for the malicious program. Analyzing showed that this is a Russian hackers-related threat because it uses Telegram API and is distributed in Russian hacker forums and other sources. This makes the trojan even more dangerous since Russians are known for being notorious and especially malicious.[3]
Sorano Stealer virus acts like a typical malware focused on gathering information, so it can:
- collect information from Doscird, Steal, telegram sessions;
- take screenshots of the desktop at any point;
- execute commands without permission;
- obtain information from auto-fill forms;
- gather saved passwords;
- steal documents from the desktop directly;
- create processes and payloads that run in the background;
- expose the system to additional malware.

The worst feature of this Sorano Stealer is the fact that anything the trojan is set to do cannot be noticed by the user or quickly eliminated. The malware can run all the needed processes, gather information, and vanish without causing any symptoms. Luckily, some more cautious users can notice issues with the speed and performance of the system went his malware is affecting their device.
In cush cases, you may react sooner and remove Sorano Stealer virus in time before the disaster. If you spot any changes in the performance, notice the Sorano process running in the background or different file, process on the Task Manager, you need to react as soon as possible and scan the machine using proper AV tools. The detection rate[4] should help you with the proper tool selection.
Sorano Stealer virus removal is an important process that requires anti-malware tools because you need to find and terminate all the related files, programs, and applications that can potentially pose a danger or cause damage to your device. This is a product of cybercriminals you need to remember that and react as if your device has been affected by serious malware.
Since you cannot know how long the Sorano Stealer virus is running in the background, you are not aware of how damaged the system can already be. Anti-malware programs can find malicious software and files that are involved in the malware campaign, but you need additional help from FortectIntego or a similar optimizer software that locates and repair affected files or corrupted functions of the system. 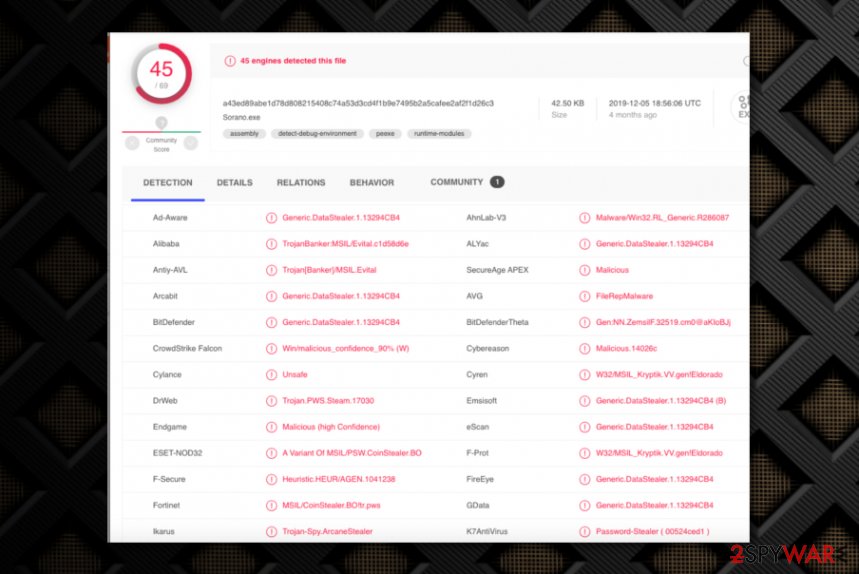
Malware programs run through malicious domains and hacked sites where scripts can get injected
You do not know when or how this malware got on your system because trojans and other malware like this spread around using malicious files and other methods involving scripts of the malware. Files with malware payload get attached to email notifications and included in the pirated software packages. When the user is not paying enough attention to such details like senders, sources, and additional files, the script is triggered directly on the machine.
If you want to avoid these installations, you need to take a closer look at emails you receive and the details that may become the red flag. Typos, grammar mistakes, and unknown senders should raise questions and encourage you to delete the received email instead of opening the message or downloading the file, clicking the link in the notification.
Sorano Stealer virus termination can be crucial in further infection avoidance
You should consider this malware as a serious danger to your privacy, system, and even security because anything gathered by this virus can lead to blackmail campaigns and damaged machines when the additional virus gets added after the trojan infection. Make sure to remove Sorano Stealer virus as soon as you notice issues with performance. If you check the system with SpyHunter 5Combo Cleaner or Malwarebytes more often you may terminate malware before it affects your machine.
Sorano Stealer virus removal is pretty quick if you choose the reliable program and run the full system scan during with AV detection engine can find and indicate any possible intruders for you. When this is done, you can see all the malicious programs and files, delete them with a few clicks and clean the system. After that, the only procedure left to do is FortectIntego that manages to fix virus damage and repair system files that create issues.
Getting rid of Sorano Stealer virus. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking and make sure to remove Sorano Stealer virus with anti-malware tool or a security program
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Sorano Stealer using System Restore
System Restore is the feature that can help with the affected device because it recovers the state of the computer in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Sorano Stealer. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Sorano Stealer and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Catalin Cimpanu. Docker servers targeted by new Kinsing malware campaign. ZDNet. Technology and security news.
- ^ Malware. Wikipedia. The free encyclopedia.
- ^ Matthew Rosenberg, Nicole Perlroth and David E. Sanger. ‘Chaos Is the Point’: Russian Hackers and Trolls Grow Stealthier in 2020. NYtimes. Breaking news.
- ^ Sorano file analysis. VirusTotal. Online malware scanner.





















