Theamdads.com ads (scam) - Free Instructions
Theamdads.com ads Removal Guide
What is Theamdads.com ads?
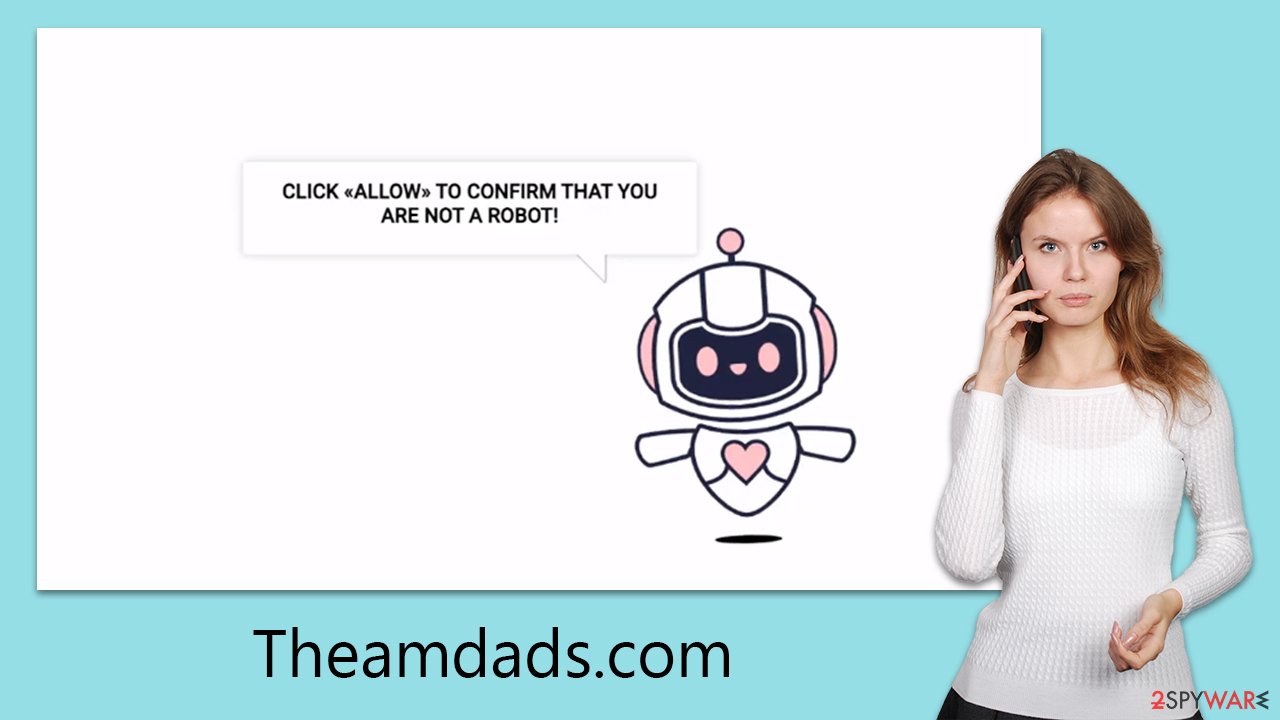
Theamdads.com is a fake site asking users to enable notifications in a deceptive manner

Theamdads.com is a website that employs push notification scams to deceive users. Despite its deceptive presentation as a legitimate site, it manipulates unsuspecting users into subscribing to its notifications. Typically, users are directed to this site through intrusive advertisements or potentially unwanted applications (PUAs). Once granted permission for push notifications, Theamdads.com inundates subscribers with misleading messages, including false virus infection alerts, as well as regular advertisements.
This intrusive behavior is not only a nuisance but also poses a potential risk to users' digital security. Subscribers may be led to believe that their device is infected with malware and be tricked into downloading more harmful applications or adware. Additionally, unwanted ads may flood their screens, disrupting normal browsing activities. If you are struggling with these unwanted notifications and suspect that your device may be compromised, the following sections of this article will provide essential guidance on how to eliminate these issues and safeguard your system from potential threats.
| Name | Theamdads.com |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | The only way the ads would start being shown is by users pressing the “Allow” button within the notification prompt |
| Symptoms | Push notifications show on the desktop at random time intervals – they show fake notices and push scams. Links can also lead to malware-laden sites |
| Dangers | Links from the site might cause you to go to harmful websites, which may result in malware infections, financial losses, or personal data exposure. |
| Removal | You can stop intrusive push notifications by blocking the website's URL in browser settings. It is also important to check the system for adware or other infections |
| Tips | You should remove caches and other web data after the elimination of adware to prevent data tracking with the FortectIntego repair and maintenance tool. You can also repair damaged system components with it |
The easy way to trick users
Users would obviously decline to intentionally receive push alerts from fraudulent websites. Knowing this, the scammers came up with a scheme to assist them in achieving their objectives: they fabricate phony websites, such as Theamdads.com, to lead victims into believing that clicking the “Allow” button is the appropriate course of action.
They employ a variety of social engineering techniques to do this. For instance, they may state that they must verify their age or humanity before proceeding or that the video cannot be played because the browser won't permit it.
- Click Allow to confirm that you are not a robot
- If you are 18+, click Allow
- Click Allow to start downloading
- Click “Allow” to win the prize and get it in our shop!
- Press “Allow” to watch the video, etc.
These messages are almost exactly the same as many others that are similar, such as those found on News-zobuti.cc or Tpwrldnws.com. The primary tactic used by scammers is to trick people into thinking that clicking the “Allow” button is a standard process they have already completed several times.
You will probably be sent to the same or a different website and asked to do the same task even if you choose to “Block” content. If you were to accept them, you would get more spam every time you opened your browser. Additionally, be cautious and make sure you don't connect with these pop-ups since they may contain links to phishing or malware-filled websites.
Users often fall into a trap by visiting suspicious websites
Cybercriminals are well aware that very few people would knowingly visit websites that might endanger their computers' security and well-being. In actuality, utilizing a search engine like Google or simply perusing websites that are considered reliable is rare (but not impossible) to come upon a dangerous website.
Issues arise when users visit websites whose origins cannot be independently confirmed. For instance, those who seek cracks to avoid paying for Windows or other software may visit phony websites and allow dangerous viruses, such as ransomware, to infiltrate their systems. This will seriously harm the victims by encrypting all personal files and then demanding cash to decode them.
Adware can be a real concern and the reason for redirects
Users may also be forced by adware to visit Theamdads.com or a similar website. Often at the expense of the app's usefulness, this kind of software focuses on advertising. People may be led as a result of websites that are deceptive or hazardous, such as those that specialize in push notification scams.
Adware may go unnoticed by many users as it is frequently installed on devices without the user's knowledge through software bundling and other deceptive techniques. Adware may be removed using both SpyHunter 5Combo Cleaner and Malwarebytes, but before using them, make sure your anti-malware program is up to date.
After uninstalling any malware, we advise running a computer scan using a repair and maintenance utility FortectIntego to assist in correcting any harm to the system and deleting any residual files. Additionally, the program may clean up system clutter and delete browser caches for increased privacy.
Get rid of the annoying Theamdads.com pop-ups
To stop receiving spam push notifications, go to your browser's settings and unsubscribe from them. Although the steps vary slightly depending on the browser, they usually entail going to the site settings and removing the notification privileges.
Please take note that the uninstallation method supplied below contains particular instructions for this operation that are suited to different browsers. You can successfully get rid of irritating push notifications and take back control of your online life by following these tips.
As always, the best defense against possible dangers to your digital life is keeping your security software up to date, using caution when surfing, and quickly resolving any indicators of infection.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.






