Zpww ransomware (virus) - Free Instructions
Zpww virus Removal Guide
What is Zpww ransomware?
Zpww – a dangerous ransomware-type virus that prevents access to all personal files
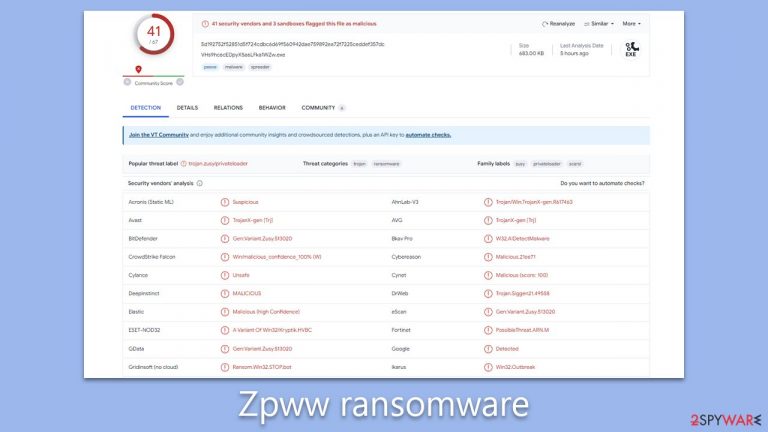
Zpww ransomware is malicious software designed to target and encrypt a wide range of personal files on infected computers, including but not limited to images, videos, and documents. Once encrypted, these files are essentially locked, identifiable by the “.zpww” extension, and lack their customary icons. Efforts to access these files result in a system error message, highlighting that the file is unrecognizable.
Driven by the robust RSA encryption algorithm, the decryption key needed to unlock the encrypted files is securely held on the cybercriminals' servers. Victims of this attack soon discover demands from the perpetrators, who seek payments ranging between $490 and $980 in Bitcoin. The assailants provide channels for negotiation or payment via specific email addresses: support@freshmail.top and datarestorehelp@airmail.cc.
Zpww is not an isolated threat; it stems from the extensive Djvu ransomware lineage, a family notorious for spawning over 600 distinct variants, including the likes of Itqw, Ttza, and Azop. This article will delve into strategies to address malware infection and explore avenues for possible file recovery without succumbing to the financial demands of cybercriminals.
| NAME | Zpww virus |
| TYPE | File locker, crypto virus |
| FILE MARKER | .zpww |
| FAMILY | STOP file virus/ Djvu ransomware |
| CONTACT EMAILS | support@freshmail.top and datarestorehelp@airmail.cc |
| RANSOM NOTE | _readme.txt |
| RANSOM AMOUNT | $490/$980 |
| THREAT REMOVAL | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner security program |
| REPAIR | Upon installation, malware like ransomware can damage essential system files, leading to crashes and errors. To instantly mend such harm, FortectIntego PC repair, an automated solution, can be used. |
Spreading mechanisms
The inception of the Zpww ransomware into computer systems primarily occurs through deceptive means. Often, an executable file, denoted as '.exe', acts as the vessel. This file might be located inside a ZIP folder, entrenched within a macro in Microsoft Office documents, or masquerading as a benign attachment. This is a calculated move by cybercriminals to ensure the widespread distribution of ransomware across diverse platforms and entities.
Another significant gateway for the ransomware is pirated software. Given that sources like torrent websites and peer-to-peer file-sharing platforms operate without stringent regulations, they become hotbeds for malicious distribution. Such unchecked and unaccountable environments pave the way for cybercriminals to seamlessly spread malware. Amongst the various ransomware distribution techniques, this method remains paramount for the creators of the Djvu ransomware family, of which Zpww is a member.
Moreover, the virus may also find its way onto systems via stealthy methods like trojan horses or worms, which can infiltrate silently. These covert invasions often go undetected, underscoring the importance of proactive defense. Employing robust anti-malware tools and comprehensive security applications can act as a formidable line of defense, scrutinizing email attachments and software installations for potential threats.
It's crucial to recognize that a large fraction of downloads carry malicious intent, often concealed in ways that defy easy detection, even by seasoned professionals. The malicious components are not always discernible through superficial inspections like checking file sizes. Thus, exercising extreme caution and meticulous scrutiny is vital to steer clear of threats akin to the Zpww ransomware.
Deciphering the Ransom Note
In the digital realm of ransomware attacks, the ransom note plays a crucial role. It's a message from the perpetrators, often elaborating on the nature of the attack and laying down terms for possible decryption. It serves as the cybercriminals' primary communication tool with the victim, conveying their demands and instructions.
Here is the ransom note typically received by victims of the Zpww ransomware:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-sD0OUYo1Pd
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
While the note might seem accommodating, offering a discount or a free decryption for a single file, it's essential to understand the risks involved. Cybercriminals are, by nature, untrustworthy. Complying with their demands offers no guarantees. Even if a victim decides to pay up, there's no assurance that they'll receive the decryption key. In some cases, victims have reported being targeted again, asked for additional payments, or left with files that remain encrypted despite having met the criminals' demands.
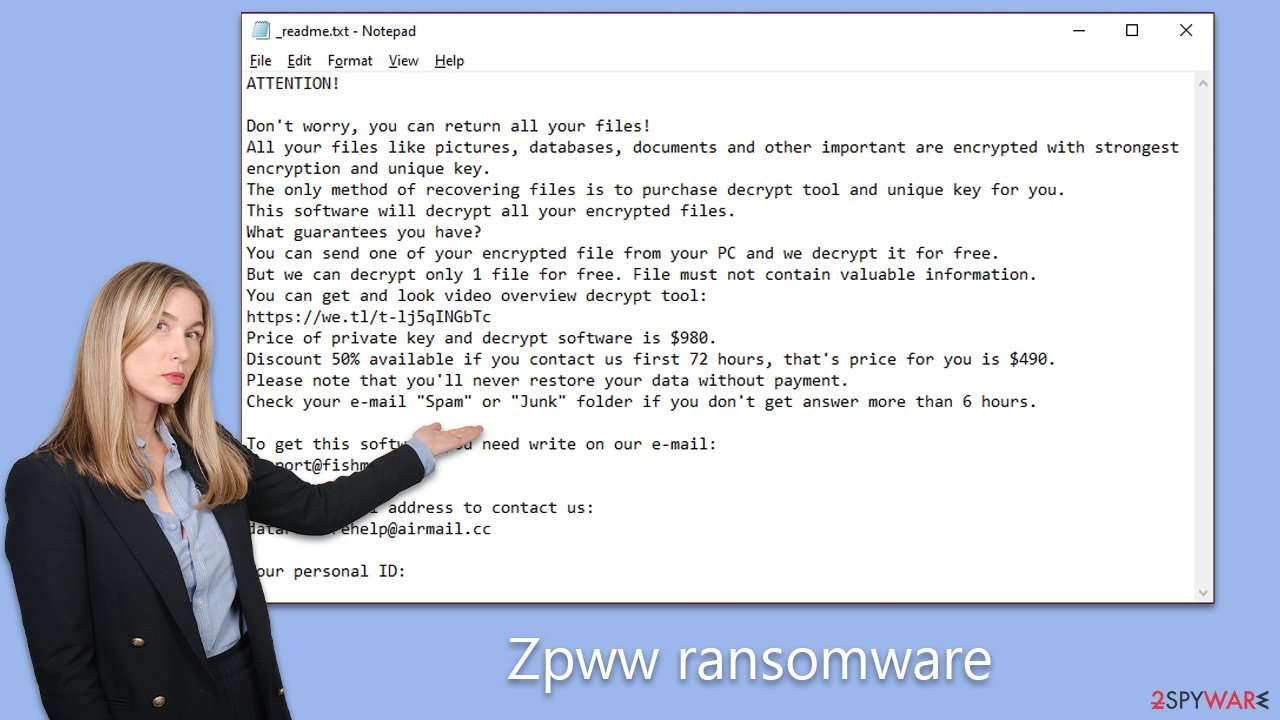
Furthermore, paying the ransom only funds these illicit activities, encouraging cybercriminals to continue and refine their attacks. Succumbing to the demands might seem like the quickest way out, but it perpetuates a vicious cycle of cybercrime. Victims should think long and hard before parting with their money, considering all available options and seeking expert advice where possible.
Effective removal of Zpww Ransomware
Realizing that your personal files have been encrypted by ransomware can be profoundly unsettling. Zpww ransomware is especially malicious, targeting a vast array of personal data, from irreplaceable photographs to essential documents. The attackers rely on the significant sentimental and pragmatic value these files possess for their victims. However, capitulating to these malefactors' demands should not be your immediate response. Instead, consider the following remedial measures.
The initial step is eradicating the ransomware from your system. While Zpww ransomware might self-terminate post the encryption process, it's possible it has dispersed other malevolent payloads or modules that persistently endanger your system. For a thorough cleanse, employ robust anti-malware tools such as SpyHunter 5Combo Cleaner or Malwarebytes. These tools are crafted to eliminate the ransomware and any concealed malevolent residues that might remain undetected.
On occasion, certain malware strains might disrupt the removal procedure by meddling with your protective software. Should you confront such an obstacle, consider initiating the scanning process in Safe Mode. This mode provides a more fortified setting ideal for addressing malware complications (guidance on entering Safe Mode is detailed below).
Post-eradication of the ransomware, you may find your system grappling with anomalies like unexpected crashes or system errors, stemming from the residual damage inflicted by the ransomware. As a remedy, leverage a dependable PC repair tool, such as FortectIntego. Utilizing such tools can seamlessly mend system discrepancies, offering a more streamlined solution compared to the intricate and prolonged process of a complete Windows reinstallation.
Steps for data recovery post ransomware attack
Recovering your encrypted files without succumbing to the demands of cybercriminals is the culminating phase in this cybersecurity challenge. For those unfamiliar with ransomware dynamics, it might seem that an elementary antivirus sweep might do the trick, or worse, that once encrypted, file recovery is a lost cause. Both assumptions are misguided.
There are several practical pathways for data recovery:
- Backup restoration: Retrieving files from a recent backup stands as the most reliable approach, but this hinges on maintaining current and regular backups.
- File Recovery Tools: There are specialized software available that can comb through your hard drive, aiming to reclaim deleted or compromised files, which could encompass those encrypted by the ransomware.
- Emsisoft's Decryption Solution: Developed especially for Djvu ransomware victims, this tool might not be a universal solution, but it's certainly worth an attempt.
Starting with the Emsisoft decryption tool is advisable. Secure the tool from Emsisoft's official portal, initiate the application, and adhere to the laid-out guidelines. The tool's core task is to try and decrypt the files. Depending on the availability of decryption keys and their alignment with your affected files, you may encounter one of three results: triumphant decryption, a key unavailability error, or a hurdle associated with an online ID making decryption unattainable.
In scenarios where decryption falters, don't get disheartened. Opt for dedicated data recovery solutions such as Data Recovery Pro. After downloading and setting it up, launch a comprehensive scan and navigate through the steps to reclaim your files.
Occasionally, thanks to the persistent endeavors of cybersecurity experts and judicial entities, decryption tools surface after ransomware infrastructure is apprehended and decryption algorithms are made public. Regularly check the stipulated links for any emerging updates on such tools:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you need more detailed instructions on the mentioned recovery methods, please check out the information below.
Getting rid of Zpww virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via the network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. NAS devices are commonly compromised via reused administrator credentials and remote access services, and attackers may also delete existing snapshots. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
In modern environments, ransomware often spreads using stolen credentials, remote management tools, VPN connections, and cloud synchronization services, not only through shared network drives.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. This does not disconnect wireless networks, VPN connections, or cloud services, which must also be disabled separately. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). In many organizations, devices are centrally managed, and network isolation is typically performed by IT or security teams using endpoint security or device management tools. The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
On modern Windows systems, network connections can also be disabled through the Settings app or automatically isolated using endpoint detection and response (EDR) tools.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead. Before reconnecting, credentials should be reset, persistence mechanisms checked, and backups verified to ensure reinfection does not occur.
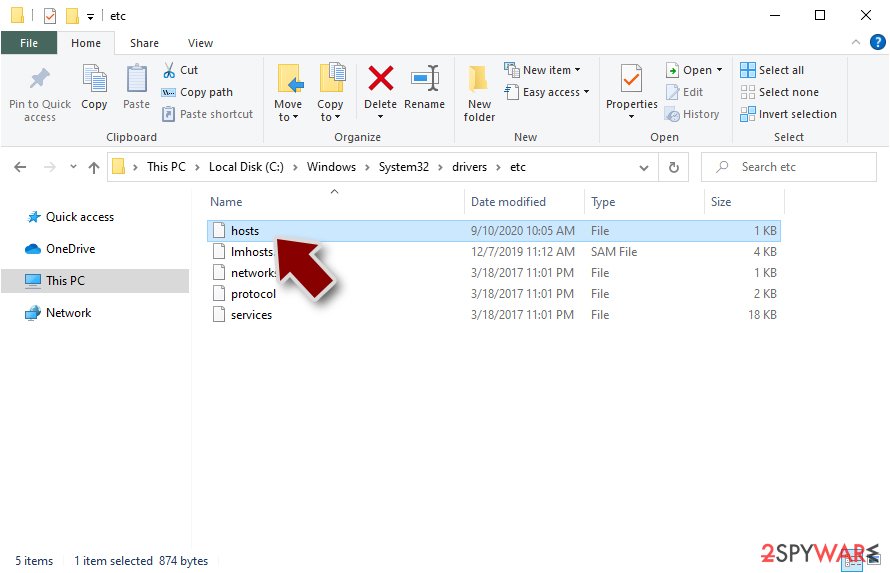
Restore Windows "hosts" file to its original state
Some ransomware might modify Windows hosts file in order to prevent users from accessing certain websites online. For example, Djvu ransomware variants add dozens of entries containing URLs of security-related websites, such as 2-spyware.com. Each of the entries means that users will not be able to access the listed web addresses and will receive an error instead.
Here's an example of “hosts” file entries that were injected by ransomware:
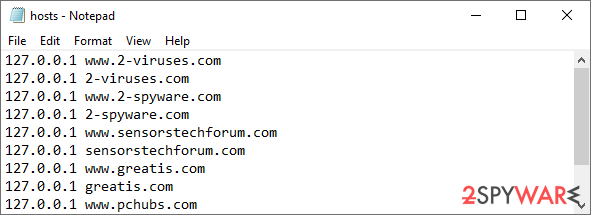
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\\Windows\\System32\\drivers\\etc\\
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Use Emsisoft decrytor for Djvu/STOP
If your computer got infected with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.

- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.

- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.

- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.

- Press Decrypt.

From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
