4rw5w ransomware / virus (Removal Guide) - Recovery Instructions Included
4rw5w virus Removal Guide
What is 4rw5w ransomware virus?
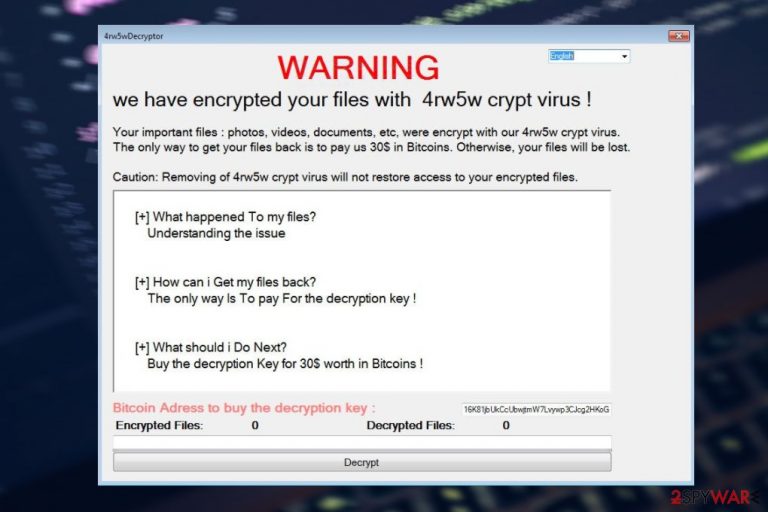
4rw5w ransomware asks for bitcoins in exchange for a decryption tool
4rw5w virus is a crypto-ransomware[1] that was first seen in the first half of 2017. Using a combination of AES and DES encryption algorithms, the malware locks all personal data located on the host machine and prevents victims from accessing it. The modified (not corrupted!) files are all appended with the .4rwcry4w extension and also lose their original icons.
After this process, ransomware delivers a ransom note in the form of a pop-up window titled 4rw5wDecryptor, which explains users the situation and asks to pay $30USD worth of Bitcoin to the provided wallet. Do not pay these novice attackers, as they did not manage to reach success. Instead, you can check for tips below to find effective ways to restore your files to their original form.
| Name | 4rw5w ransomware |
| Type | File locking virus, crypto-malware |
| Encryption | AES + DES |
| File extension | .4rwcry4w appended to all personal files on a Windows computer |
| Ransom | $30 to be paid in bitcoin cryptocurrency |
| Malware removal | Manual malware elimination is possible but is not recommended; instead, employ SpyHunter 5Combo Cleaner or another security |
| System fix | After you get rid of all ransomware-related files, use FortectIntego to fix virus damage done to system files automatically |
It looks like malware creators’ attempt to jump on the WannaCry's bandwagon in hopes of receiving similar success as this infamous parasite did a few years back. As evident, the copycat malware came nowhere near what the latter has achieved.
Fortunately, this malware is still at a very low distribution stage, so there is really no need to panic. At least for now. Nevertheless, if this malware does invade your computer somehow, it is unlikely that you will avoid the destructive consequences it brings.
If the system infiltration goes successfully, the virus will then start looking for 22 types of file extensions, including:
.avi, .dll, .DOC, .DOCX, .DOT, .dotm, .exe, .jpg, .lnk, .mp3, .mp4, .NEF, .ODT, .PDF,. pif, .png, _en.png, .rar, .txt, .url, .wav and .zip.
To keep these files safe from decryption, extortionists have programmed the virus to encrypt the AES encryption key with the DES algorithm [2]. Such double encryption is virtually impossible to crack; thus, the ransomware victims either have to pay the criminals or use alternative methods for data recovery.
. Unfortunately, these might not always be successful. Despite this, we strongly recommend you do not contact cybercriminals, as they might not fulfill their promises even after you pay them.
4rw4w.exe and 4rw5wDecryptor.exe are the main files associated with this virus, so make sure you delete them from your computer. Applying FortectIntego or similar virus detection software for the elimination is a smart choice if you want to get rid of the malware quicker.
.4rwcry4w extension virus is not only as widespread as WannaCry, but it also seems to be quite different in its design. Lockscreen that displays the ransom note is very basic and does not feature additional details such as a timer that counts down the time until data destruction. It only features the language selection option, a fill-in box with a decrypt button next to it, and a brief message that goes like this:
WARNING
we have encrypted your files with 4rw5w crypt virus !
Your important files : photos, videos, documents, etc, were encrypt with our 4rw5w crypt virus.
The only way to get your files back is to pay us 30$ in Bitcoins. Otherwise, your files will be lost.
Caution: Removing of 4rw5w crypt virus will not restore access to your encrypted files.
[+] What happened To my files?
Understanding the issue
[+] How can i Get my files back?
The only way Is To pay For the decryption key !
[+] What should i Do Next?
Buy the decryption Key for 30$ worth in Bitcoins !
Bitcoin Adress to buy the decryption key : [Bitcoin address]
The typos and grammar mistakes suggest that the criminals behind this virus are not really taking this program seriously. Perhaps it’s just a test drive to see if the ransomware works before starting more widespread distribution. Either way, you should not follow the instructions in this note and head straight to the virus removal instead.
The obscure ways of ransomware distribution
Malware investigators have not come across a specific source of malware distribution yet. This is probably because the program’s prevalence, in general, is very low. What we can presume, though, is that the extortionists may be distributing the malware themselves and not relying on major botnets such as Necurs to disseminate it like the majority of ransomware viruses.
This makes it almost impossible to determine where and how this virus may hit. Nevertheless, we know that typically, ransomware is distributed via email spam, so it would be smart to pay more attention to what emails you are receiving and especially what attachments you are downloading. Besides, to be completely sure your data is safe, you should create backups of your files and keep them safe.
Eliminate ransomware and then try alternative data recovery options
It goes without saying that ransomware is not the type of malware you can mess around with. This means that you should not even try to remove the virus from your computer manually. You should only rely on professional anti-malware software to carry out this task.
Security tools can be used to protect your device from malware, potentially unwanted programs, and viruses. So, make sure you invest in a powerful utility with strong real-time protection.
Once you eliminate all the malicious files, you should also check the data recovery techniques we provide below. Keep in mind that you should transfer the encrypted files over to another medium before restoring them.
Getting rid of 4rw5w virus. Follow these steps
Important steps to take before you begin malware removal
File encryption is one component of a ransomware infection, which may also include credential theft, persistence mechanisms, and lateral movement. However, it is important to understand that malware may perform various changes within a Windows operating system, including persistence, scheduled tasks, registry modifications, and security feature tampering.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. The storage device should remain disconnected after copying to prevent accidental modification or deletion. Encrypted data itself does not contain active malicious code, but only the encrypted files—not executables or scripts—should be transferred.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Repair damaged system components
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstall is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing FortectIntego, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Find a working decryptor for your files
File encryption is a process that is similar to applying a password to a particular file or folder. However, from a technical point of view, encryption is fundamentally different due to its complexity. By using encryption, threat actors use a unique set of alphanumeric characters as a password that can not easily be deciphered if the process is performed correctly.
There are several algorithms that can be used to lock data (whether for good or bad reasons); for example, AES uses the symmetric method of encryption, meaning that the key used to lock and unlock files is the same. Unfortunately, it is only accessible to the attackers who hold it on a remote server – they ask for a payment in exchange for it. This simple principle is what allows ransomware authors to prosper in this illegal business.
While many high-profile ransomware strains such as Djvu or Dharma use immaculate encryption methods, there are plenty of failures that can be observed within the code of some novice malware developers. For example, the keys could be stored locally, which would allow users to regain access to their files without paying. In some cases, ransomware does not even encrypt files due to bugs, although victims might believe the opposite due to the ransom note that shows up right after the infection and data encryption is completed.
Therefore, regardless of which crypto-malware affects your files, you should try to find the relevant decryptor if such exists. Security researchers are in a constant battle against cybercriminals. In some cases, they manage to create a working decryption tool that would allow victims to recover files for free.
Once you have identified which ransomware you are affected by, you should check the following links for a decryptor:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

If you can't find a decryptor that works for you, you should try the alternative methods we list below. Additionally, it is worth mentioning that it sometimes takes years for a working decryption tool to be developed, so there are always hopes for the future.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from 4rw5w and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ A guide to avoid being a crypto-ransomware victim. Webroot. The Webroot Communities Discuss. Contribute. Learn. Read..
- ^ Data Encryption Standard. Wikipedia. The free encyclopedia.
