Abdoser.xyz ads (scam) - Free Instructions
Abdoser.xyz ads Removal Guide
What is Abdoser.xyz ads?
Abdoser.xyz is a fake website made to scam users

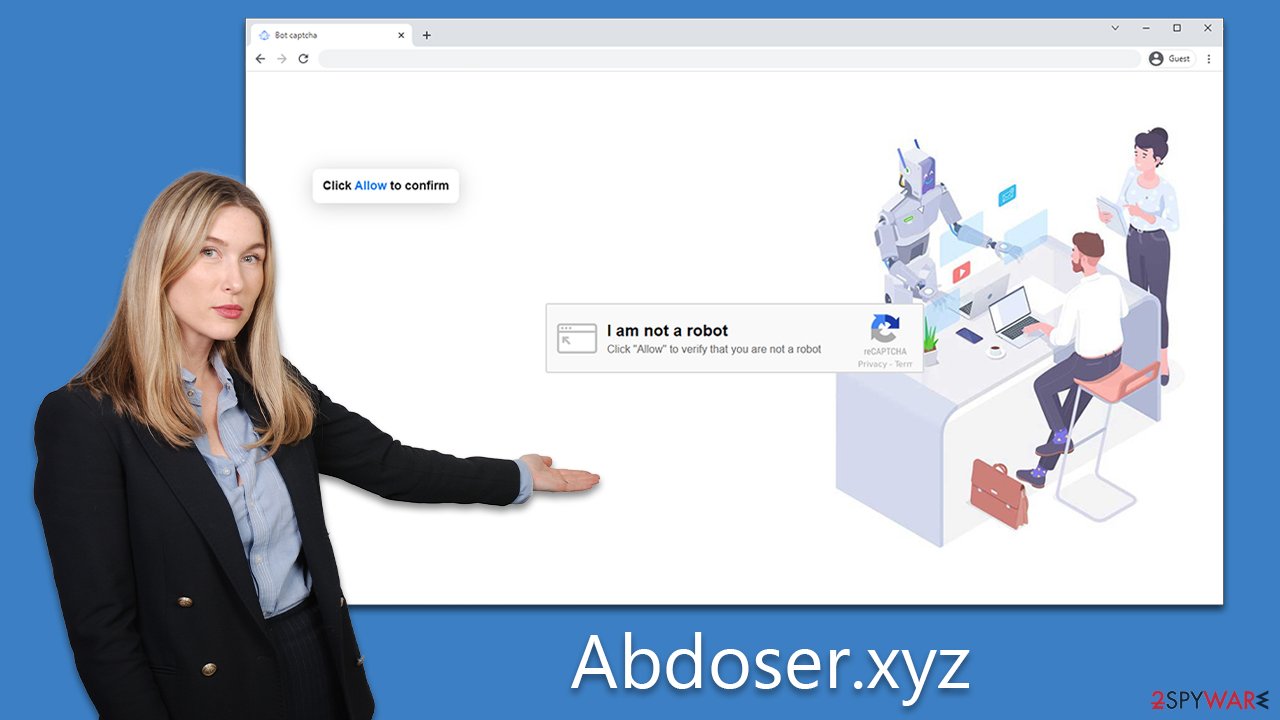
Abdoser.xyz is a push notification scam website that employs social engineering techniques to deceive users. Once users visit the site, they are asked to confirm that they are not robots and to click on misleading messages such as “Download Now.” Because these requests can be encountered almost anywhere, users tend to confirm them without giving it much thought, only to realize that the website has no value. They are then quickly redirected to another suspicious place.
Initially, nothing much happens, and users tend to forget about their visit to the sire. However, ads associated with Abdoser.xyz would start showing up consistently directly on their desktops. Users might be confused about why they see these ads. In reality, it is because they clicked the “Allow” button within the notification prompt, which allowed the website to deliver any kind of information via the built-in API.
Since Abdoser.xyz is a scam website, it is associated with rogue ad networks. The ads displayed on users' desktops are of poor quality and might expose them to get-rich-quick schemes or show fake virus infection alerts. As a result, people might be misled into installing malware on their systems or spending money on useless services.
| Name | Abdoser.xyz |
| Type | Ads, push notifications, pop-ups, scam |
| Distribution | Users allow push notifications after they click the “Allow” button within the prompt |
| Symptoms | Notifications show up at the bottom-right corner of the screen – these include fraudulent content and links to potentially dangerous websites |
| Risks | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Removal | To end intrusive push notifications, go to the Chrome menu and choose Settings. Then, to ensure that your system is not infected with adware or malware, scan it with SpyHunter 5Combo Cleaner |
| Other tips | Once you have removed all unwanted software, it is important to clean your web browsers and fix any corrupted system files. You can do that automatically by following the instructions here FortectIntego or referring to our manual guide |
Scam methods used
Few people willingly sign up for push notifications that will immediately bombard their computer screens with false or deceptive information. Scammers who utilize push notification frauds to understand this and often resort to using social engineering tactics to manipulate unsuspecting users into taking actions they would otherwise avoid.
These fraudulent websites often redirect users without warning, leaving them little time to react and process the situation. As a result, users may feel pressured to comply with the website's requests, even if they appear suspicious or untrustworthy. These requests may include entering personal information, downloading potentially harmful software, or making payments for fake services.
Scammers rely on social engineering tactics to exploit common human tendencies, such as the desire for instant gratification or the fear of missing out on an opportunity. By creating a sense of urgency or scarcity, these fraudsters can easily persuade users to perform actions that benefit the scammers' malicious intentions.
Here are a few examples of messages victims could encounter on the Abdoser.xyz scam site:
- If you are 18+, click Allow.
- Please tap Allow to continue.
- Click “Allow” to start downloading.
- Click “Allow” to win a prize and get it in our shop!
- Press “Allow” to verify, that you are not a robot.
- Can't play this video! Perhaps your browser doesn't allow video playback. Please click the Allow button to watch the video.
Please always pay attention to what is being asked of you because no legitimate website would hold the content lock behind a requirement to allow notifications. Nonetheless, even if you were tricked, you can always undo this change relatively easily by following the instructions below.
Removing intrusive Abdoser.xyz ads and checking the system for infections
Adware is a persistent issue that can result in various concerning behaviors, including pop-ups, redirects, and other unwanted changes to your browsing experience. If you notice any suspicious web addresses or experience frequent pop-ups, then it's possible that your device has been infected with adware. Additionally, you may find that your browser homepage or search provider has been changed without your permission.
To thoroughly investigate and clean your system of any potential threats, it's recommended that you scan your device using reliable security software like SpyHunter 5Combo Cleaner or Malwarebytes. This software can automatically detect and remove any potentially unwanted applications or malware that may have infected your system. It's also important to have effective anti-malware installed on your device to prevent dangerous attacks like ransomware, Trojans, and rootkits.
If the security scan detects any unwanted applications or malicious software, it's recommended that you take the time to clean your browsers. Regularly cleaning your browser caches can help to prevent errors and some security issues, but it's also important to remove cookies to prevent third-party tracking. You can use FortectIntego to perform this task and fix any system damage done by malware.
Finally, if you're experiencing intrusive pop-ups and exposure to malicious links or misleading messages, removing the adware responsible is crucial as soon as possible. To do this, you should access your browser settings and find the site settings, where you can block the URL from the “Allowed” list. By following these steps, you can ensure that your device is free from adware and can enjoy a safe and secure browsing experience.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
